 Annoying as they are, the spam emails circulating that supposedly come from Facebook don’t merely lead the recipient to one of those so-called Canadian Pharmacy pill-vendor websites. They now come with a bonus: An infection, courtesy of a malicious iframe which attempts a series of exploits against the browser, Adobe Reader, and Adobe Flash in an attempt to push a drive-by download down to the victim’s PC.
Annoying as they are, the spam emails circulating that supposedly come from Facebook don’t merely lead the recipient to one of those so-called Canadian Pharmacy pill-vendor websites. They now come with a bonus: An infection, courtesy of a malicious iframe which attempts a series of exploits against the browser, Adobe Reader, and Adobe Flash in an attempt to push a drive-by download down to the victim’s PC.
The messages, which say they come from a service called Facebook Notify (or, sometimes, just Facebook Service) inform the recipient that they’ve received a message. In order to read the message, the recipient is encouraged to click a link in the email that looks like it leads to Facebook.
It’s a sham: The spammers have hotlinked a Facebook URL so it points to another Web site. That Web site redirects the browser to the Canadian Pharmacy page, but that’s not all: In a few cases, while checking out what happens when one visits the page, I found that the test PC was infected afterwards.
As it turns out, a script embedded within the Canadian Pharmacy page loads an iframe that points to yet another site. And that iframe runs through a number of tricks to push down a Trojan installer we classify to Trojan-PWS-Daonol.
 Daonol is an obnoxious thief, because in addition to stealing passwords, the Trojan also prevents the browser from loading certain Web sites; redirects the browser to sites other than the one the user clicks in search result pages on Google, Bing, and Yahoo; and prevents Windows from running some applications.
Daonol is an obnoxious thief, because in addition to stealing passwords, the Trojan also prevents the browser from loading certain Web sites; redirects the browser to sites other than the one the user clicks in search result pages on Google, Bing, and Yahoo; and prevents Windows from running some applications.
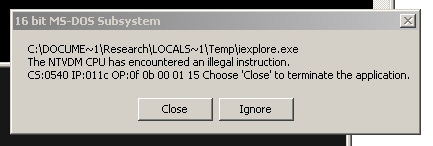
In Daonol infections dating back as long as 11 months ago, the malware prevented the user from running Regedit or cmd.exe. I found that I was able to run both of those programs with this latest infection, but other programs installed on my testbed — including the text editor UltraEdit, the rootkit-removal tool GMER, or the system utilities Filemon, RegMon, Sam Spade, or ShexView — would quit or crash as soon as I ran them on an infected system. (Daonol hides the registry keys it uses to load itself using rootkit techniques.)
Of course, other utilities commonly used to research or remediate infections, such as Process Explorer, HijackThis, or OllyDbg worked just fine. So it’s anyone’s guess what the creator of Daonol is trying to do, here; Obviously, he’s a few neck-bolts short of a Frankenstein.
For recipients of these email messages, the only safe action to take is to avoid clicking the links in the messages. We can clean up the Daonol infection, but it’s better to avoid it in the first place.
It pays to look closely at the To: address where the spam message was sent; In this case, the messages came through a spam account set up long before Facebook was even a twinkle in someone-who-told-Mark-Zuckerberg-about-his-idea’s eye. Real messages always include This message was intended for (and the email address you used to register your Facebook account) but this message moronically says This message was intended for you. Well, duh.
And I have yet to see an email message from another Facebook user which didn’t actually include not only the name of the sender (not just Facebook Service) but the text of the message as well. When in doubt, just open your browser and type facebook.com into the address bar, then click the link to read your messages. If the message is real, it should appear there, too.





















Boy, this a already a year old… and i never read about it before!
I’ve been having that trouble: Very careful about downloads – even leaving them in quarantine for 2 or 3 Antivirus-updates. Ad yet every now and then, i had positive findings i couldn’t explain. Most of them in the temp-folder.
So now i know: Yes i looked at those ‘pharmacy’ things every now and then!
Thanks a lot!
i guess, Viagra is the word which consider as the spam word,