Security researchers from Webroot have intercepted a currently active, client-side exploits-serving malicious campaign that has already managed to infect 18,544 computers across the globe, through the BlackHole web malware exploitation kit.
More details:
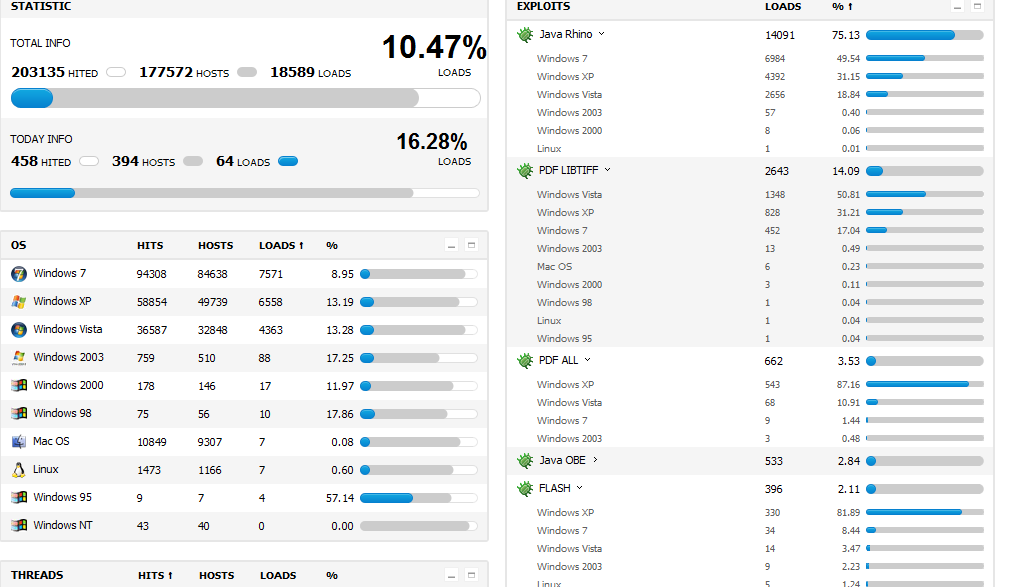
The BlackHole Web malware exploitation kit is currently serving the following exploits: Java Rhino; Java OBE; MDA; PDF ALL; PDF LIBTIFF; HCP; FLASH.
As you can seen in the attached screenshot, the cybercriminals managed to infect 14091 hosts using the Java Rhino exploit, 2643 hosts using the PDF LIBTIFF exploit, 662 hosts using the PDF ALL Exploit, 533 hosts using the Java OBE exploit, and 396 hosts using the FLASH exploit. The campaign alsos managed to infect 7571 Windows 7 hosts, 6558 Windows XP hosts, and 4363 Windows Vista hosts, next to 7 Mac OS X hosts.
The campaign is relying on traffic redirected through multiple campaigns which usually take place using traffic exchange networks. In these networks, cybercriminals will exchange traffic that they have aggregated using, for instance, black hat search engine optimization tactics, or directly embed client-side exploits serving iFrames within bogus adult web sites.
Client-side exploits are served from the following URLs:
hxxp://176.31.245.175/main.php
hxxp://176.31.245.175/main.php?page=b0d770efba902f4d
hxxp://176.31.245.175/main.php?page=41daaa37bd31588f
hxxp://176.31.245.175/main.php?page=ca56ea46b85905c8
hxxp://176.31.245.175/main.php?page=b556c61cbc0a973d
hxxp://176.31.245.175/main.php?page=5d50b58e2c650bb1
hxxp://176.31.245.175/main.php?page=bde782aaab4733f5
hxxp://176.31.245.175/main.php?page=09cd2cae1be568e1
hxxp://176.31.245.175/main.php?page=0f901be3c1f396a0
hxxp://176.31.245.175/main.php?page=6f56cd0f4e82bd69
hxxp://176.31.245.175/main.php?page=e9c8657855ca6126
hxxp://176.31.245.175/main.php?page=0058ca317c5afa83
hxxp://176.31.245.175/main.php?page=8790bb3deeb48533
hxxp://176.31.245.175/main.php?page=bb6227d3a4bb9474
hxxp://176.31.245.175/main.php?page=3831657f7eea6b07
hxxp://176.31.245.175/main.php?page=37c1318db6a8c63b
hxxp://176.31.245.175/main.php?page=37c1318db6a8c63b
hxxp://176.31.245.175/main.php?page=64a2d67411c0b080
hxxp://176.31.245.175/main.php?page=43a3824339b73b31
IP Information for 176.31.245.175:
IP Location: France Paris Ovh Systems
ASN: AS16276
Resolve Host: ks386835.kimsufi.com
The following malicious executables, have been detected as participating in the malicious campaign:
MD5’s participating in the malicious campaign:
921914ae92f6e650289db252605304a1
857bf35df69ebb16b492b767021a5743
42c6422d4815f48b19097363347aad02
4794576b3776b0d3989ff0c06e10fd7c
0274d65f4ee68b1fb425357c713cf8bd
7a9b6a40ef47cf7c43bfcebf0348ecd4
b8dd1c9f712d95514fbc892c2530af6c
45f715d409446da3a6f5ad5923087193
f2d593dfda4f38a967cd43f4c3cf0683
0150b4c48d8ddd5e6e4a1fdbb0f9616e
708f2ce2fc6600bd309448b80e0c266d
5077020c65ed2e152848c0eb651c2e62
056a34283fc185f50dfe5d6b9262028d
Multiple independent reports are confirming that client-side exploits remain the most lucrative end and corporate user exploitation tactic, thanks to the fact that end users aren’t patching their third-party applications and browser plugins.
Users are advised to ensure that you’re not running any outdated software, next to browser plugins.
You can find more about Dancho Danchev at his LinkedIn Profile. You can also follow him on Twitter.







Thank you for the news.
Dancho Danchev is one of the very, very, few people who consistantly gets it right.
I’ve got an insta click for his stuff, even if it’s about stuff I know inside and out, he seems so far ahead of the pack and definately ahead of the curve that it’s almost, well, supernatural (Santana grabs guitar…I got this Man!).
L8R