Who needs automated bots solving CAPTCHAs, when you have teams of low-waged humans recognizing them for pennies?
In an underground cybercrime ecosystem dominated by managed services and countless outsourcing opportunities, it’s fairly logical to assume that Google’s reCAPTCHA is under constant fire.
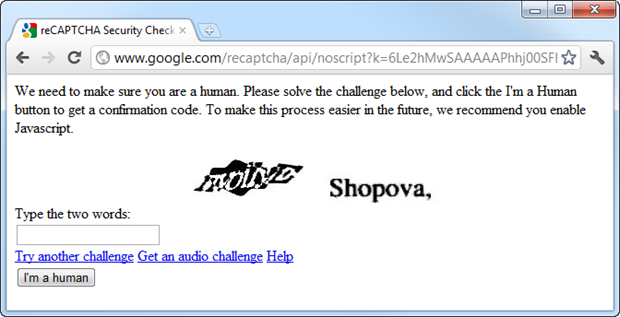
Just how easy is it to recognize reCAPTCHA images for malicious account registration and service abuse purposes? Let’s find out.
According to newly published research, it easier than it should be. From professional CAPTCHA solving teams, to services offering API keys for the integration in third-party software and automatic account registration purposes, the entire CAPATCHA solving process is easy to outsource.
The research details the process of hiring dedicated CAPTCHA solving teams, and affiliate networks offering CAPTCHA solving services, next to issuing API keys for the purpose of third-party integration.
More details on the affiliate networks involved:
Looking at the API, the process basically goes like this:
- Send the CAPTCHA and API key via an HTTP POST request
- A response is returned with an ID
- Wait 10 seconds then send the ID back in another request
- A response with either the resolved text or a “not ready” status is sent back
- If it’s not ready, wait 5 seconds then ask for the status again (rinse, lather, repeat)
It seems like a very good use case for long polling. Never mind, the API is straightforward; the interesting bit will be the success rate achieved.
Before we move onto the crux of this post – actually “breaking” CAPTCHA – there’s one more useful service provided by Antigate and that’s the ability to get a quick health check on the status of the operators. Actually, you can load this yourself without authenticating and you should see something similar to this:
Total of 1,230 CAPTCHAs were sent off to Antigate and only 77 were not solved correctly, hence causing the registration process to fail. That’s a 94% success rate.
In the past, independent research has confirmed numerous weaknesses in Google’s reCAPTCHA:
In a newly released report, a security researcher claims that Google’s reCAPTCHA, one of the most widely adopted free CAPTCHA services, contains weaknesses that would allow a 10,000 infected hosts botnet the ability to achieve 10 recognition successes every second, allowing it to register 864,000 new accounts per day.
In response, a Google spokesman stated that the report relies on data collected in early 2008, and doesn’t take into consideration the effectiveness of the current technology used against machine solvers.
Moreover, Microsoft’s CAPTCHA has been under fire from phishers and spammers as well:
Jeff Yan and Ahmad Salah El Ahmad, at the School of Computing Science, Newcastle University, England recently published a research paper entitled “A Low-cost Attack on a Microsoft CAPTCHA“, demonstrating how they’ve managed to attack the Microsoft’s CAPTCHA used on several of their online services such as Hotmail and Windows Live, with over 92% recognition rate.
Malicious attackers outsource the CAPTCHA solving process to vendors of CAPTCHA solving services, in order to automatically abuse a particular Web service that requires CAPTCHA verification in order for the account registration process to take place.
Yahoo!’s and Hotmail’s CAPTCHA’s have been under fire in the past, resulting in hundreds of thousands of automatically registered email accounts used for sending spam and phishing emails. Independent research has also confirmed that spam from legitimate Web-based email providers is increasing.
With low-waged humans solving CAPTCHAs for pennies, CAPTCHA as a layered authentication mechanism is definitely flawed, thanks to the constant and automatic abuse by scammers and malicious attackers who want to take advantage of the clean IP reputation of free Web -ased email service providers.
You can find more about Dancho Danchev at his LinkedIn Profile. You can also follow him on Twitter.







Interesting blog, it’s not just humans but some services use CAPTCHA that is inherently weak at the moment like Yahoo, we wrote about it recently:
http://community.websense.com/blogs/securitylabs/archive/2012/01/30/trojan-caught-on-camera-shows-captcha-is-still-a-security-issue.aspx