Cybercriminals are masters of multi-tasking. For instance, whenever a web server gets compromised, they will not only use its clean IP reputation to host phishing, spam and malware samples on it, they will also sell access to the shell allowing other cybercriminals the opportunity to engage in related malicious activities such as, mass scanning of remotely exploitable web application vulnerabilities.
Today, I intercepted a currently active phishing campaign that’s a good example of a popular tactic used by cybercriminal known as ‘campaign optimization’. The reason this campaign is well optimized it due to the fact that as it simultaneously targets Gmail, Yahoo, AOL and Windows Hotmail email users.
More details:
Sample screenshot of the spamvertised phishing email:
Spamvertised URL hosted on a compromised Web server: tanitechnology.com/fb/includes/examples/properties/index.htm – the URL is currently not detected by any of the 28 phishing URL scanning services used by the VirusTotal service.
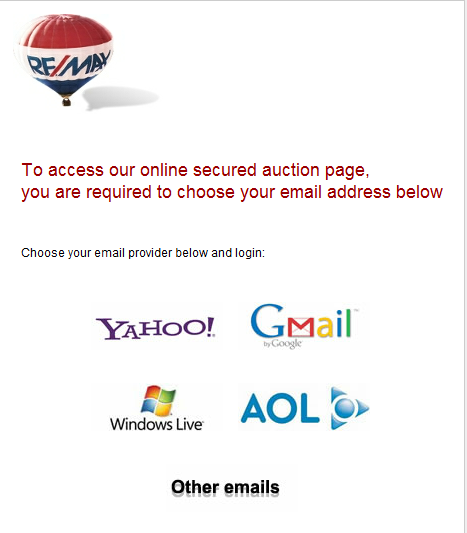
Sample screenshot of the landing phishing page affecting multiple free email service providers:
What makes an impression is the poor level of English applied to the campaign’s marketing creative. Moreover, it’s rather awkward to see that the landing phishing page is themed using the Online Real Estate brand Remax, a brand that has nothing to do with the enforcement of a particular marketing message related to the phishing campaign.
Users are advised to avoid interacting with similar pages, and to always ensure that they’re on the right login page before entering their accounting data.
You can find more about Dancho Danchev at his LinkedIn Profile. You can also follow him on Twitter.








Is webroot secure anywhere complete taking care of this new virus????
is webroot secure complete taking care of the virus “Troj/Redir-O fox news”
Yes, the URL being used in the scam is blocked by Webroot SecureAnywhere.