Taking advantage of DIY spamming tools and harvested databases of user names, cybercriminals have been systematically abusing multiple instant messaging services in an attempt to trick as many users as possible into interacting with their malicious campaign.
In this post, I’ll profile a newly released DIY Skype spamming tool, discuss its main features, and whether or not it can lead to an increase in the overall spam levels affecting Microsoft’s Skype.
More details:
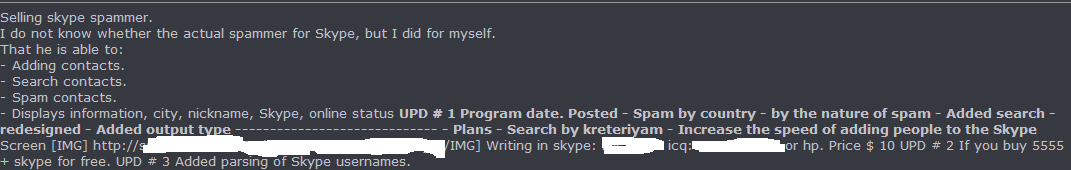
Screenshot of the forum posting advertising the sale of the Skype spamming tool:
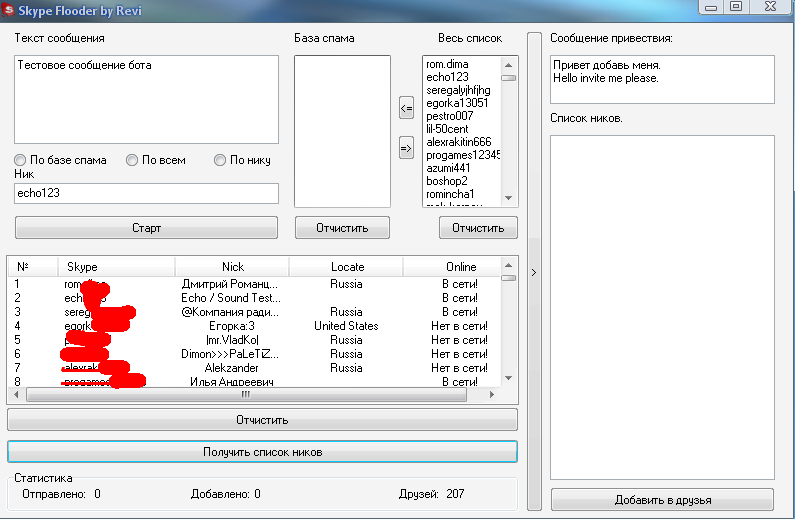
Screenshot of version 1.0 of the Skype spamming tool:
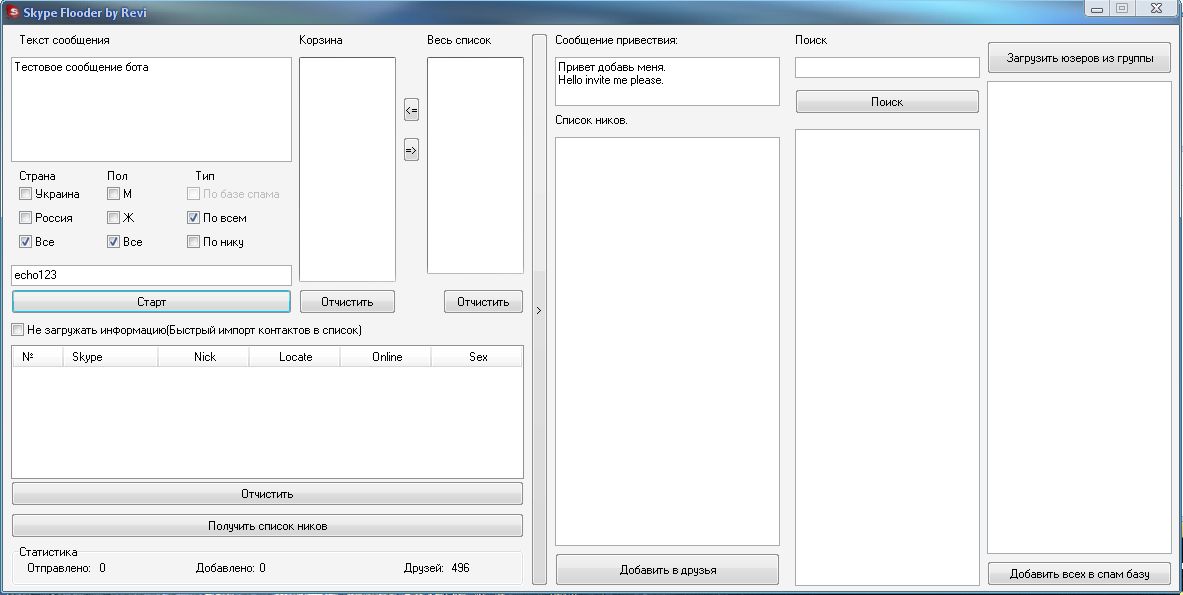
Screenshot of the latest 2.0 version of the Skype spamming tool:
The DIY Skype spamming tool is capable of harvesting Skype user names based a particular country, gender, and it can also check whether the user is online or not. Next to these features, the latest version also supports parsing of log files. The price? For $10 anyone can have access to the tool. Those who purchase the tool will automatically receive 5000 already harvested Skype user names.
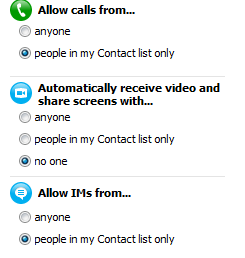
Since the tool is only capable of spreading a particular message to those who give authorization to the spammer’s account, as well as the fact that it doesn’t support multiple spam accounts and proxies, it doesn’t represent a scalable threat . Instead, it primarily relies on social engineering. Although the tool is capable of segmenting the targeted population for better conversion rate, the user still has to authorize the spammer in order to receive messages from him.
How you can protect yourself from this DIY Skype spammer? Pretty simple. Just ensure that only users on your contact list can send you IMs, or initiate a call with you.
We’ll continue monitoring the development of the tool.
You can find more about Dancho Danchev at his LinkedIn Profile. You can also follow him on Twitter.







This article is very nice & more informative.I gain much information in this article.I guess they do get to some blogs. It is a bit like email spam.Anyway, great content as always.