By Joe McManus
Last week Adobe announced that they would no longer be supporting Flash for Android. Adobe will be removing Flash from the Android Marketplace and users should be wary of fake Flash apps for their Android Devices. Now to be fair to Adobe, they are not taking flash away from the Android platform but are focusing on the Adobe AIR cross platform runtime environment http://www.adobe.com/products/air.html. The reason Adobe is switching to AIR is to allow app developers to write one program for use on iOS and Android devices.
Let’s look at some of the fake Flash apps for Android that we have seen and what they do. This is just a small sampling; there are too many to highlight them all.
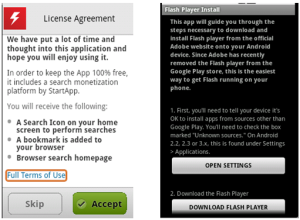
This first app we’ll look at is one of hundreds of premium SMS Trojans being distributed on third party markets that are fake installers for legitimate applications. What they really do is charge for what may or may not be a download of an already free app. The scam works when the user agrees to their ‘Terms’ and the app will send out three SMS messages containing SMS short codes that come with a fee. These messages go to a premium service setup by the malware author and will appear as charges on you phone bill. The charges vary depending on the user’s location but range around $8-12.
This has appeared many times as Flash Player 11, Flash Payer 10, FlashPlayer, etc. Webroot detects them as Android.FakeInst and has been tracking these type of fake installer for over a year; here, here and here.
Our next example is another scam of sorts. It doesn’t charge for anything but will install a bunch of aggressive advertising SDKs that are known to create ad-related notifications, shortcuts and bookmarks. This app requests 24 Android OS and device-specific permissions when, at most, it would need the INTERNET and WRITE_EXTERNAL_STORAGE permissions. The additional 22 permissions are for the ad SDKs. Webroot detects one of the ad SDKs bundled with the app as a Potentially Unwanted Application (PUA) and labels it Android.Ads.Plankton.B.
Although it does download Adobe Flash for Android after agreeing to their License Agreement it does come with the cost of a bunch of other non-flash related stuff.
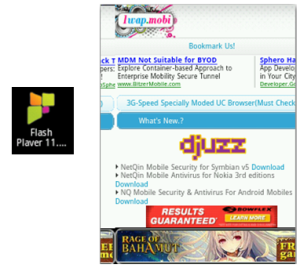
This final example is for an app that claims to be Flash Player but really installs an Adobe Flash Icon, that merely opens a browser window full of advertisements. These types of apps are annoying and really are meant to drive web traffic to sites so the developer can receive pay-per-click revenue, and in this case they deceive the customer into thinking they’re getting a known productive app. Like the previous example, this app isn’t malicious, but it’s more deceptive and doesn’t deliver on what it claims, for that Webroot detects Android.DreamStepFlash as a PUA.
Malicious and untrustworthy apps come in many different flavors, and as you can see, Adobe Flash is one that is used to lure unsuspecting users to install. Adobe will continue to release security updates for Adobe Flash and suggests you uninstall if your device is able to upgrade to Android 4.1.
Remember, always choose your apps wisely and download from a trusted source. Check reviews, research the developer and verify permissions requested before downloading.








What the heck is Google doing about this. I bought my android phone on the pretext that Google was going to police android apps to the point where they get uninstalled automatically or zapped remotely if ever a bad one cropped up. This was the hype anyway at the time that Android was first about to be released.