Cybercriminals are currently mass mailing hundreds of thousands of emails impersonating Citi, using two different professionally looking email templates. Upon clicking on any of the links found in the malicious emails, users are exposed to the client-side exploits served by the latest version of the Black Hole Exploit Kit.
More details:
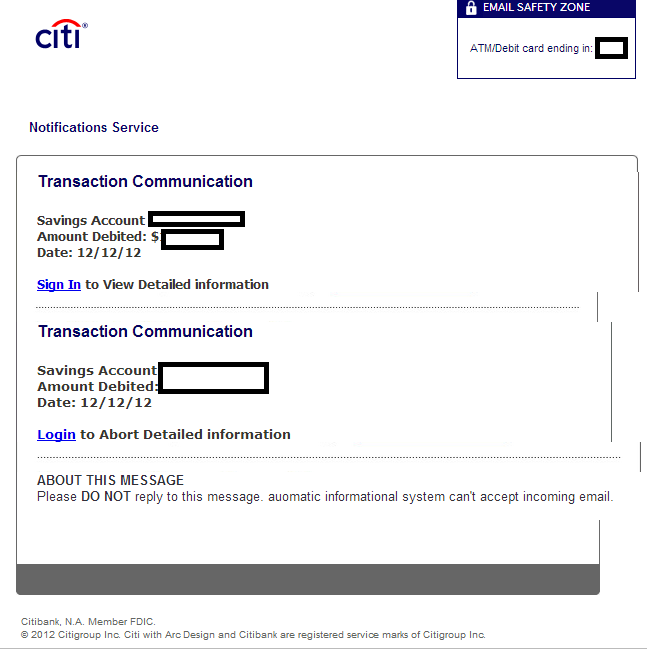
Sample screenshot of the first spamvertised template:
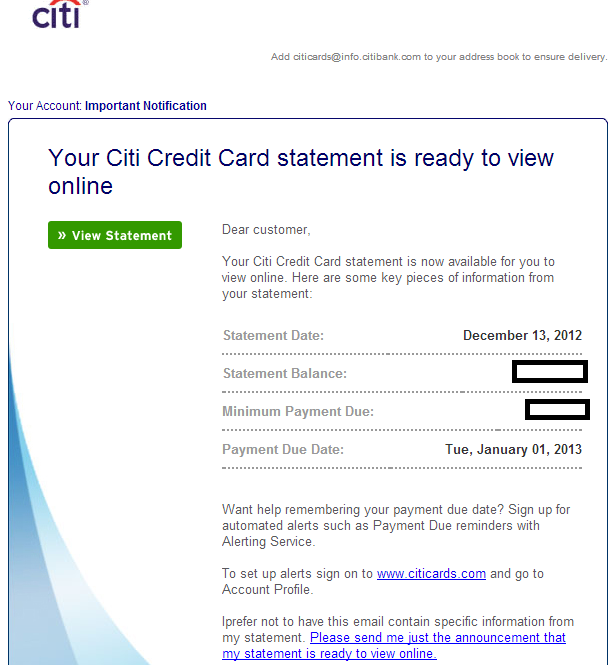
Sample screenshot of the second spamvertised template:
Sample spamvertised compromised URLS used in the campaign:
hxxp://franctelnetwork.com/components/com_ag_google_analytics2/citialertservice.html
hxxp://ghostdeal.com/components/com_ag_google_analytics2/citialertservice.html
hxxp://thesmsway.com/components/com_ag_google_analytics2/citialertservice.html
hxxp://911pcs.com/components/com_ag_google_analytics2/alert-service-citibank.html
hxxp://rjewelryd.com/components/com_ag_google_analytics2/alert-service-citibank.html
hxxp://softwarehit.com/components/com_ag_google_analytics2/alert-service-citi-sign_in.html
hxxp://ceipfernandogavilan.com/components/com_ag_google_analytics2/alert-service-citi-sign_in.html
hxxp://troubleshootersacademy.com/components/com_ag_google_analytics2/citialert-sign_in.html
Sample client-side exploits serving URLs:
hxxp://eaglepointecondo.biz/detects/operation_alert_login.php – 59.57.247.185
Name Server: NS1.AMISHSHOPPE.NET – 209.140.18.37 – Email: solaradvent@yahoo.com
Name Server: NS2.AMISHSHOPPE.NET – 211.27.42.138 – Email: solaradvent@yahoo.com
hxxp://platinumbristol.net/detects/alert-service.php – 59.57.247.185
Name Server: NS1.AMISHSHOPPE.NET – 209.140.18.37 – Email: solaradvent@yahoo.com
Name Server: NS2.AMISHSHOPPE.NET – 211.27.42.138 – Email: solaradvent@yahoo.com
Upon successful client-side exploitation, the campaign drops MD5: b360fec7652688dc9215fd366530d40c – detected by 28 out of 45 antivirus scanners as Worm:Win32/Cridex.E.
Once executed, the sample performs the following activities:
- Accesses Firefox’s Password Manager local database
- Creates a thread in a remote process
- Installs a program to run automatically at logon
It creates the following Registry Keys:
HKEY_CURRENT_USERSoftwareMicrosoftWindows NTCFBDC89D4
HKEY_CURRENT_USERSoftwareMicrosoftWindows NTS25BC2D7B
With the following value:
[HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun]
KB00121600.exe = “”%AppData%KB00121600.exe””
It then creates the following Mutexes:
LocalXMM000003F8
LocalXMI000003F8
LocalXMRFB119394
LocalXMM000005E4
LocalXMI000005E4
LocalXMM0000009C
LocalXMI0000009C
LocalXMM000000C8
LocalXMI000000C8
It also drops the following MD5s:
MD5: 9e7577dc5d0d95e2511f65734249eba9
MD5: 61bb88526ff6275f1c820aac4cd0dbe9
MD5: b360fec7652688dc9215fd366530d40c
MD5: f6ee1fcaf7b87d23f09748cbcf5b3af5
MD5: d7a950fefd60dbaa01df2d85fefb3862
MD5: ed662e73f697c92cd99b3431d5d72091
It then phones back to 209.51.221.247/AJtw/UCyqrDAA/Ud+asDAA.
We’ve already seen the same command and control server used in the following previously profiled malicious campaigns:
- Malicious ‘Security Update for Banking Accounts’ emails lead to Black Hole Exploit Kit
- Bogus Facebook ‘pending notifications’ themed emails serve client-side exploits and malware
- Cybercriminals spamvertise bogus ‘Microsoft License Orders’ serve client-side exploits and malware
- ‘Copies of Missing EPLI Policies’ themed emails lead to Black Hole Exploit Kit
- Fake ‘Flight Reservation Confirmations’ themed emails lead to Black Hole Exploit Kit
- ‘Fwd: Scan from a Xerox W. Pro’ themed emails lead to Black Hole Exploit Kit
- Malicious ‘Sendspace File Delivery Notifications’ lead to Black Hole Exploit Kit
The same email (solaradvent@yahoo.com) that was used to register the name server domains in this campaign, is also known to have registered the following domains:
AFRICANBEAT.NET
ALEGRECAMPO.NET
GAUGE-MASTER.NET
TOMOLLALLAMAFARM.NET
Responding to 59.57.247.185 are also the following malicious domains:
eaglepointecondo.org
sessionid0147239047829578349578239077.pl
pleansantwille.com
ibertomoralles.com
eaglepointecondo.co
eaglepointecondo.biz
ansncm.org
canbmn.org
hfeitu.net
labpr.com
namelesscorn.net
platinumbristol.net
porkystory.net
robertokarlosskiy.su
romoviebabenki.ru
seldomname.com
winterskyserf.ru
Webroot SecureAnywhere users are proactively protected from these threats.
You can find more about Dancho Danchev at his LinkedIn Profile. You can also follow him on Twitter.