Earlier this month, we profiled and exposed a newly launched underground service offering access to tens of thousands of malware-infected hosts, with an emphasis on the fact that U.S.-based hosts were relatively more expensive to acquire, largely due to the fact that U.S.-based users are known to have a higher online purchasing power. How much does it cost to buy 10,000 U.S.-based malware-infected hosts? Let’s find out.
In this post, I’ll profile yet another service offering access to malware-infected hosts internationally, that’s been operating since the middle of 2012, and despite the fact that it’s official Web site is currently offline, remains in operation until present day.
More details:
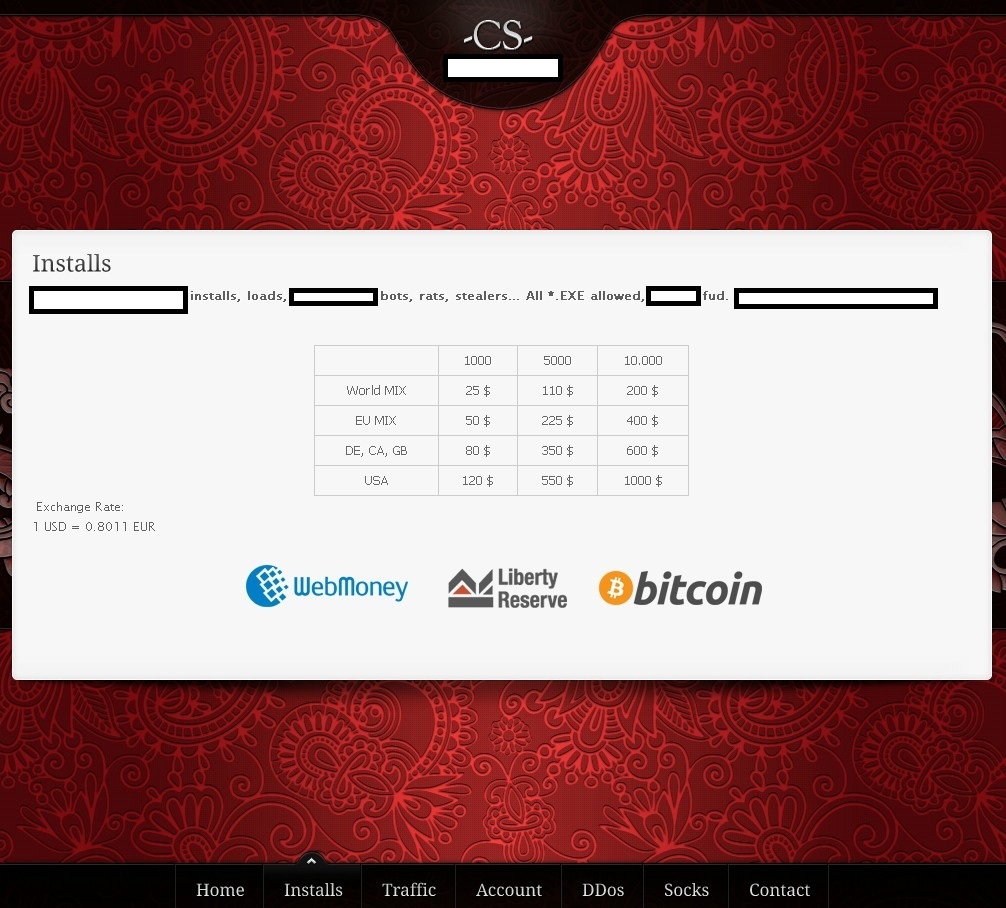
Sample screenshot of the underground E-shop selling access to malware-infected hosts:
The service is yet another example of a trend that’s been evident since the early days of the first Malware-as-a-Service underground market offerings, namely, the segmentation and use of perceived pricing schemes when it comes to U.S.-based malware-infected hosts. Naturally, purchasing access to U.S.-based malware-infected hosts is more expensive than, for instance, purchasing access to hosts based in Germany, Canada or the U.K., largely thanks to the fact that a U.S.-based user has a higher online purchasing power compared to the rest of the world.
If a potential cybercriminal wants to spread his fully undetectable piece of malware online, all he has to do is purchase access to the malware-infected hosts offered by such services, allowing virtually anyone access to “managed malware propagation” capabilities. The service that I’m profiling in this post is also attempting to “vertically integrate” within the cybercrime ecosystem by offering related “value added” services such as access to Socks5 servers, which are in reality malware-hosts converted to be used as anonymization proxies.
The prices are as follows:
- 1,000 hosts World Mix go for $25, 5,000 hosts World Mix go for $110, and 10,000 hosts World Mix go for $200
- 1,000 hosts EU Mix go for $50, 5,000 hosts EU Mix go for $225, and 10,000 hosts EU Mix go for $400
- 1,000 hosts DE, CA and GB, go for $80, 5,000 hosts go for $350, and 10,000 hosts go for $600
- Naturally, access to a U.S.-based host is more expensive compared to the rest of the world. A 1,000 U.S. hosts go for $120, 5,000 U.S. hosts go for $550 and 10,000 U.S hosts go for $1,000
Thanks to the rise of DIY (do it yourself) underground market propositions, as well as managed services allowing novice cybercriminals to outsource the entire host acquisition, retention through QA (Quality Assurance), and dissemination of malicious campaigns to third-parties offering these capabilities as a service, we expect to see more of these services offering access to malware-infected hosts.
You can find more about Dancho Danchev at his LinkedIn Profile. You can also follow him on Twitter.







The domain that you are talking about is hxxp://cheapshop[.]su