How are cybercriminals most commonly abusing legitimate Web traffic?
On the majority of occasions, some will either directly embed malicious iFrames on as many legitimate Web sites as possible, target server farms and the thousands of customers that they offer services to, or generate and upload invisible doorways on legitimate, high pagerank-ed Web properties, in an attempt to monetize the hijacked search traffic.
In this post I’ll profile a DIY blackhat SEO doorway generator, that surprisingly, has a built-in module allowing the cybercriminal using it to detect and remove 21 known Web backdoors (shells) from the legitimate Web site about to be abused, just in case a fellow cybercriminal has already managed to compromise the same site.
Are turf wars back in (the cybercrime) business? Let’s find out.
More details:
The newly introduced feature appears to have been recommended to the developer of the tool by one of its users. What we’ve got here is a great example of how cybercriminals apply QA by taking into consideration the concept of customerization.
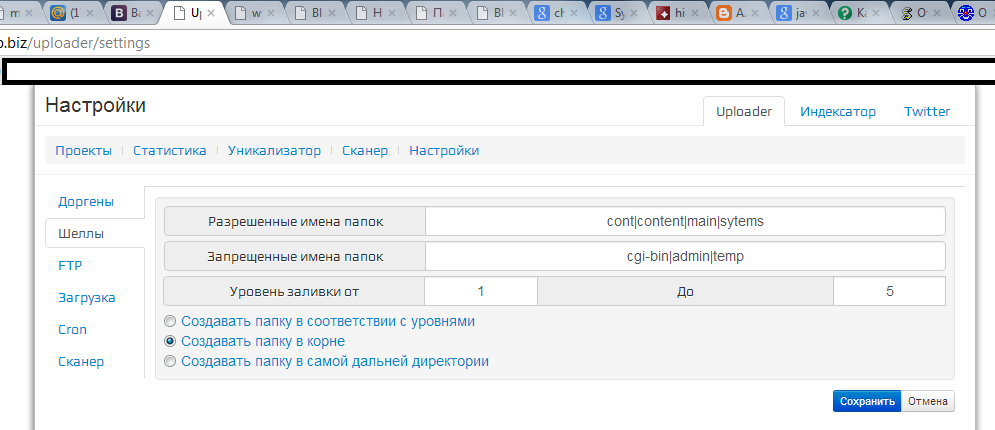
Sample screenshots of the DIY doorway generator in action:
As you can seen in the screenshot above, the developer has added support for 21 of the most popular Web backdoors (shells).
As you can seen in the screenshot above, the tool appears to have detected a competing shell and is presenting the output to the user to investigate and eventually clean the site of the competitors backdoor.
- Related research – “What’s the ROI on Going to a Virtual Blackhat SEO School?”
Does the newly introduced feature signal an upcoming turf war on the blackhat SEO front, the way we’ve seen it with Bagle, Netsky and MyDoom, SpyEye’s ‘Kill ZeuS’ feature, or Storm Worm vs Srizbi? Not necessarily, at least not in this particular case since for a turf war to take place, we need to have an exchange of virtual ‘shots’ between all the market leading — or least one to act as a provoker — blackhat SEO platforms. And this is something we aren’t seeing, at least for the time being.
As always, we’ll keep an eye on any future updates introduced by the developer of this DIY doorway generator.
You can find more about Dancho Danchev at his LinkedIn Profile. You can also follow him on Twitter.