Bank of America (BofA) customers, watch what you click on!
A currently ongoing malicious spam campaigns is attempting to entice BofA customers into clicking on the client-side exploit serving URLs found in legitimate looking ‘Statement of Expenses’ themed emails. Once users with outdated third-party applications and browser plugins click on the link, an infection is installed that automatically converts their PC’s into zombies under the control of the botnet operated by the cybercriminal/gang of cybercriminals behind the campaign.
More details:
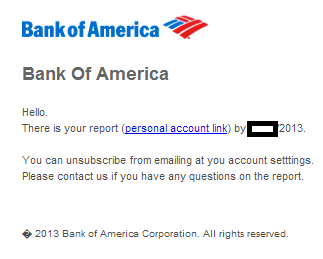
Sample screenshot of the spamvertised email:
Sample redirection chain: hxxp://medikalgorus.com/7k4lsdc.html -> hxxp://nutnet.ir/dl/nnnew.txt -> hxxp://emotiontag.net/cp/nnnew.txt -> hxxp://aurummulier.pl/nnnew.txt -> hxxp://drstephenlwolman.com/topic/sessions-folk-binds.php
Client-side exploits serving URL: hxxp://drstephenlwolman.com:80/topic/sessions-folk-binds.php?csgDjSDzgnivUPJ=OqhBlPjQNTGtUEj&nwuILeihO=zlCYepniDHdPh
Detection rate for a sampled JAR archive – MD5: 733d2db8f7e88b79fab66e80e97a42a3 – detected by 1 out of 45 as UDS:DangerousObject.Multi.Generic.
Upon successful client-side exploitation, the campaign drops MD5: 5facf6703483704fd04245f65662a8e5 – detected by 7 out of 46 as PWS:Win32/Zbot.gen!AM.
Once executed, the sample starts listening on port 5748.
It also creates the following Mutexes:
Local{B0B9FAFD-CA9C-4B54-DBC9-BE58FA349D4A}
Local{B0B9FAFC-CA9D-4B54-DBC9-BE58FA349D4A}
Local{D15F4CEE-7C8F-2AB2-DBC9-BE58FA349D4A}
Local{D15F4CE9-7C88-2AB2-DBC9-BE58FA349D4A}
Local{0BB5ADEF-9D8E-F058-DBC9-BE58FA349D4A}
Local{911F9FCD-AFAC-6AF2-DBC9-BE58FA349D4A}
Global{2E06BA86-8AE7-D5EB-DBC9-BE58FA349D4A}
Global{B0B9FAFD-CA9C-4B54-DBC9-BE58FA349D4A}
Global{B0B9FAFC-CA9D-4B54-DBC9-BE58FA349D4A}
Global{D15F4CEE-7C8F-2AB2-DBC9-BE58FA349D4A}
Global{D15F4CE9-7C88-2AB2-DBC9-BE58FA349D4A}
Global{0BB5ADEF-9D8E-F058-DBC9-BE58FA349D4A}
Global{BB67AFC4-9FA5-408A-DBC9-BE58FA349D4A}
Global{D30C91FE-A19F-28E1-11EB-B06D3016937F}
Global{D30C91FE-A19F-28E1-75EA-B06D5417937F}
Global{D30C91FE-A19F-28E1-4DE9-B06D6C14937F}
Global{D30C91FE-A19F-28E1-65E9-B06D4414937F}
Global{D30C91FE-A19F-28E1-89E9-B06DA814937F}
Global{D30C91FE-A19F-28E1-BDE9-B06D9C14937F}
Global{D30C91FE-A19F-28E1-51E8-B06D7015937F}
Global{D30C91FE-A19F-28E1-81E8-B06DA015937F}
Global{D30C91FE-A19F-28E1-FDE8-B06DDC15937F}
Global{D30C91FE-A19F-28E1-0DEF-B06D2C12937F}
Global{D30C91FE-A19F-28E1-5DEF-B06D7C12937F}
Global{D30C91FE-A19F-28E1-95EE-B06DB413937F}
Global{D30C91FE-A19F-28E1-F1EE-B06DD013937F}
Global{D30C91FE-A19F-28E1-89EB-B06DA816937F}
Global{D30C91FE-A19F-28E1-F9EF-B06DD812937F}
Global{D30C91FE-A19F-28E1-E5EF-B06DC412937F}
Global{D30C91FE-A19F-28E1-0DEE-B06D2C13937F}
Global{D30C91FE-A19F-28E1-09ED-B06D2810937F}
Global{D30C91FE-A19F-28E1-51EF-B06D7012937F}
Global{D30C91FE-A19F-28E1-35EC-B06D1411937F}
Global{D30C91FE-A19F-28E1-55EF-B06D7412937F}
Global{DDB39BDC-ABBD-265E-DBC9-BE58FA349D4A}
Global{2E1C200D-106C-D5F1-DBC9-BE58FA349D4A}
MPSWabDataAccessMutex
MPSWABOlkStoreNotifyMutex
It then phones back to the following C&C servers:
213.123.186.173
88.68.122.74
68.22.158.150
130.251.186.103
220.255.230.41
95.104.124.51
62.1.222.171
174.96.27.128
75.32.154.102
174.6.141.85
108.197.50.249
108.60.184.54
107.193.222.108
71.43.167.82
216.21.197.54
203.81.192.36
217.114.113.148
99.0.126.100
108.227.104.254
74.95.239.117
95.224.253.62
174.141.40.194
99.1.206.145
67.78.107.130
87.146.141.56
95.104.16.83
68.117.10.58
188.121.218.120
93.177.136.143
97.78.65.201
212.58.125.106
151.66.147.254
66.128.168.151
190.167.163.155
122.174.206.2
222.173.101.226
124.104.159.14
We’re also aware of the following malicious MD5s that have phoned back to the same C&C IPs, over the past month:
MD5: 92f7472d55b74161fe1cbdc7b74579ee
MD5: 5b7dfd54792235b6d5fb7263befca803
MD5: 856ceaffd52b043c429a5e96208118c1
MD5: bc852222b67fcf145f4e1c3027e1e76a
MD5: 1b15467c4bc1809f464efbac71a840eb
MD5: f5c1521d15abbe4f42ced730e6b03f6f
MD5: 0c17a2c9baec309c2795363c54d4d1a1
MD5: 8dab06b40ff79d7e09b61bd62b190833
MD5: bc561a4c2fceee57e11894a64410e4c8
MD5: 5286979a90b77b3387db7a3aaf15d065
MD5: 93cb982f40b0f6501ded641401c39171
MD5: 8d6ac22d6cb874d072d54ce537329400
MD5: 08a0a0d21a6cf4575e95ec4db16b5ad8
MD5: 99e8ccecde4cba2452c757f123e08cef
MD5: 52357c2539a2953443260e84a40ae5ad
MD5: 867802b2b074a9e38af7fc2e44fa738b
MD5: 3567fa4afb087510ba0f50129ea44f58
MD5: 0dc200ee9c98c4d22f1e4de9ab897225
MD5: fdd5b409d466085257798f85de7ab6c2
MD5: c381a97c1b4cc51b476e64e4a3d67007
MD5: ba66cb6330fb27e009a9bdae6bb6dd36
MD5: 80b0eaf741c1c67ae002826564b16a3d
MD5: b45f1417811ac9caa4a4f683b8483c3b
MD5: 211d2b3db3f7832f92adb5c5c7946cc5
MD5: 7a9c0baf18053636aa102f2cd9a7f55f
MD5: ca718ed4fc614a7fa6cde31d8c476e7b
MD5: afc4b0650e594824885faa950e5b5f71
MD5: e188446962d4a87e2dc0fdbe80f1c9be
MD5: b3eeb6006dfc3016252c1cac8b9878da
MD5: 085ee57d389316c0b4887169f0cec239
MD5: 257f407f8de807879dee0e49e6a38a66
MD5: 70b93f41f724bc3a485175be65952be4
MD5: 085ee57d389316c0b4887169f0cec239
MD5: 257f407f8de807879dee0e49e6a38a66
MD5: 70b93f41f724bc3a485175be65952be4
And we’ve already seen some of these C&C servers (213.123.186.173; 107.193.222.108) in malicious campaigns.
Webroot SecureAnywhere users are proactively protected from these threats.
You can follow Dancho Danchev on Twitter.







there’s malicious software on facebook that can steal your information be careful of clicking on photos that send you to another link in order to look at them this is not a normal routing.