Since its inception in 1996, Alexa has positioned itself as primary Web metrics data portal, empowering Web masters, potential investors, and marketers with access to free analytics based on data gathered from toolbars installed on millions of PCs across the world. Successfully establishing itself as the most popular, publicly accessible Web site performance benchmarking tool, throughout the years, the Alexa PageRank has acted as a key indicator for the measurement of a Web site’s popularity, growth and overall performance, often used in presentations, competitive intelligence campaigns, and comparative reviews measuring the performance/popularity of particular Web sites.
Operating in a world dominated by millions of malware-infected hosts, converted to Socks4/Socks5 for, both, integration within automatic account registration tools, DoS tools, in between acting as anonymization ‘stepping-stones’, cybercriminals continue utilizing this legitimate, clean IPs-based infrastructure for purely malicious and fraudulent purposes. Their latest target? Utilizing the never-ending supply of malware-infected hosts to influence Alexa’s PageRank system. A newly released, commercially available, DIY tool is pitching itself as being capable of boosting a given domain/list of domains on Alexa’s PageRank, relying on the syndication of Socks4/Socks5 malware-infected/compromised hosts through a popular Russian service.
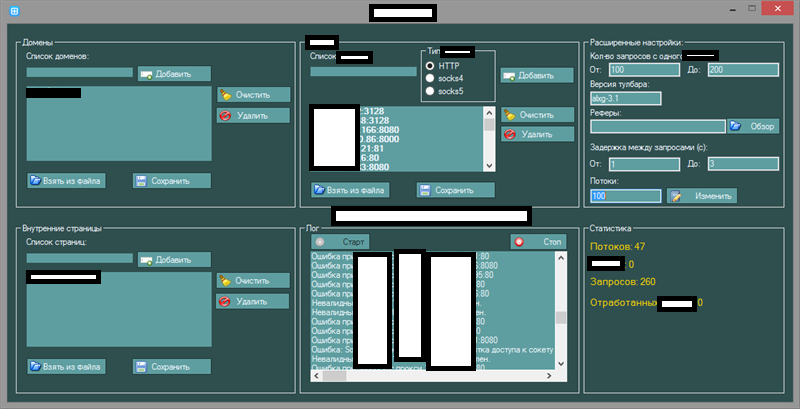
Sample screenshot of the tool:
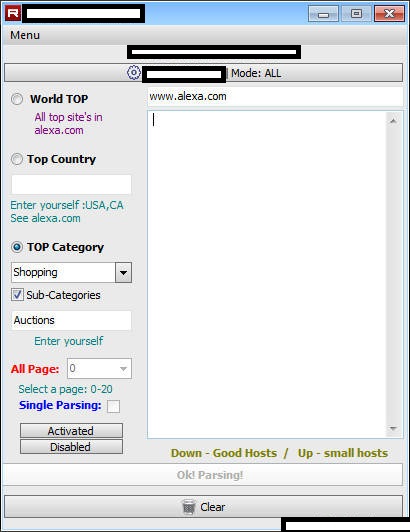
The multi-threaded tool, pitched at $100, is capable of supporting HTTP/Socks4/Socks5 malware-infected hosts, and also has the ability to validate the active/non-active state of the proxy in question. Due to Alexa’s popularity, and vast database of domain related data, for years cybercriminals, and spammers in particular, have been abusing the Web site in an attempt to harvest domain lists — which they didn’t manage to obtain through good old school fashioned zone transfer techniques — to later on attempt to launch dictionary harvest attacks in an effort to build spam hitlists.
Sample screenshot of a tool used to harvest domain data through the Alexa service, that we’re aware of:
What would a superficially boosted Alexa PageRank be used for by a cybercriminal? A boosted Alexa PageRank can increase the probability of a successful sale for the given domain, a default feature/commonly accepted practice for the majority of underground market/OTC (over-the-counter) Web shells including E-shop services that we’ve profiled in the past.
We’ll continue monitoring the development of the application.







Great post.