Tips for Card Security and Fraud Protection
Cyber-criminals love to hit consumers where it hurts, and I’d say the most vulnerable location would have to be our wallets.
I frequently receive inquiries asking how a consumer can better secure their credit card and financial accounts. This ultimately led to me authoring this blog as a point of reference. Fortunately the industry is beginning to implement better practice and new methods to prevent this, and as always, someone, somewhere, will eventually find a way around that.
I’ve included a few tips here that everyone should acknowledge, and a few that may not be relevant to your environment. Obviously there are a TON of steps you can take to better your security, but if I wrote them all down, we would have a novel as opposed to a blog post. For the sake of being concise, I’ve kept this short and sweet, so to speak.
- Physical security is important, keep your credit and debit cards in a secure location that only you can access.
- Never write down your PIN, and make sure it is not personally identifiable information such as birthdays, phone numbers, etc. Cover it up when entering it publicly.
- Make sure that you add your signature to your card, this is something that most neglect or have neglected to do in the past. I know I’ve certainly been guilty of it.
- Regularly review your statements for transactions you do not recognize. Cyber criminals will frequently make minuscule charges first to see if you are checking your statements, and if not, make larger transactions. Some of the most successful campaigns such as this have accrued countless amounts of money with charges as small as a penny at a time.
- Before using your card at a public ATM, ensure that the machine has not been tampered with. Skimmers are becoming smaller and more popular methods for scraping card data.
- Confirm that when making a withdrawal, the amount on the receipt matches the amount withdrawn. Shred the receipt before disposing of it.
- If you receive a new card, completely destroy the old one.
- When purchasing anything online, ensure that the website utilizes HTTPS. Never submit financial or personal data via unencrypted connection.
- As stated in my previous blog, always log out of a website, app, or platform when you are done using it. Most websites and banking apps now implement a time-out policy that requires re-authentication after a certain time frame.
- Never write down your entire card number on a physical medium and never mail it.
- Always keep your card within sight of you. If a teller needs to take it to a machine, request that you accompany them, or ask them to bring the machine to you.
- Avoid using public computers whenever possible and never make important transactions on an unsecured network.
- As we move into chipped base cards that offer more protection, cyber criminals now have the ability to scan these cards. While in its early stages and having limited range, this technology will continue to improve. If you utilize one of these cards, invest in an RFID sleeve to prevent your data from being swiped.
There is a lot more that could be added to this and as we see security measures improve, we will also see the technology to compromise them improve as well. What is secure today, may not be tomorrow.
What is a computer virus?
It is a long-standing joke that if you do a web search on any medical symptom, it will always lead to a web diagnosis of cancer. In the same manner, searching for any computer problem will always lead you to conclude that you have a nasty computer virus. Chances are you have never had, and never will have a computer virus, as this handy Venn diagram from XKCD.com demonstrates:
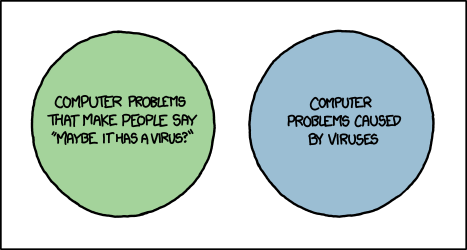
Now perhaps I’m being a bit nit-picky about the connotation of the term “virus” but there is quite a bit of misinformation and FUD (Fear, Uncertainty and Doubt) out there when it comes to computer viruses. Wikipedia defines a computer virus as “a malware program that, when executed, replicates by inserting copies of itself (possibly modified) into other computer programs, data files, or the boot sector of the hard drive.” The key here is that a virus spreads via various methods of replication – infecting other files. The vast majority of malware does not do this, and a virus is not going to change your home page, display pop-up ads, or install a toolbar as adware or Potentially Unwanted Applications (PUAs) may do. Your printer issues are not being caused by a virus either.
If you search for the name of any browser redirect, toolbar, pop-up ad, or any number of other computer problems you will almost always end up on a web page that claims the issue is due to a virus. These pages are rarely from reputable security vendors, and are often security blogs that feature prominent advertising for various legitimate and not-so-legitimate security software. The term “virus” is used to make you think the problem is far worse than it actually is in hopes that you will purchase the advertised security programs. These tactics are similar to those used by Rogue Security Software and tech support scams.
If you are searching for more information on a computer problem, pay attention to the sites that come up in the results, and to the terminology used. If the term “virus” comes up, chances are that the result is not from a trusted security company or computer support forum. There are several general computer support forums out there which offer excellent free support for general computing issues. For issues related to specific programs or hardware, most companies have their own support forums these days, and in many cases someone else has experienced the same issue that you are having.
Are antivirus testing scores a true reflection of our Mac product efficacy? You decide…
In a world full of new malware and various types of cyber threats continuing to pop up on a daily basis, the average consumer has reached a point where a good antivirus security solution is an absolute must; even when dealing with so called “immune” operating systems like Mac OSX. However with so many antivirus products to choose from for the Mac, how is the average consumer supposed to make sound decisions about which product will give them the best protection and the greatest peace of mind?
These days, most consumers in the market for a new product simply jump on Google and look for general product reviews; however with so many mixed results, and an array of product features to choose from and compare, the antivirus playing field can quickly become very confusing and overwhelming. As an alternative, another source of information that consumers turn to for data about antivirus solutions are third party antivirus (AV) testing companies. For years these companies have performed baseline comparative tests on many of the most popular AV products in an effort to test the product’s malware detection and remediation capabilities, as well as looking at how machine performance is affected by the product being installed and run on the user’s machine. In recent years they have also started to do testing for AV products being developed for the Mac OSX platform. The results of these tests are typically published with an overall bottom-line score for each product being tested, which is based on the product’s overall malware/virus detection percentage.
As a result, the average consumer looking at these tests will use some type of previous brand recognition or family/friend influence, in conjunction with the AV testing scores, in order to make a swift decision on the “best” antivirus software for their needs. It is easy for the human psyche to say, “Oh this product scored 100%, so it must be good.” The issue with this type of decision making process is that unfortunately the assumption is made that all AV products are created equal, and that the Mac AV testing platform and testing methodology creates a true simulation of real world execution and installation of the malware being tested. This could not be further from the truth.
In order to test the true efficacy of an antivirus product, AV testing companies should actually be installing the malware and executing the viruses in question, in order to see how the antivirus product handles an actual simulation of an end-user infection. Unfortunately, the reality of the situation is that AV testing companies generally do not use “real world” simulations of malware executions and installs when testing Mac AV products. Instead they perform their tests using a method called “zoo testing,” which involves putting hundreds of malicious file samples into a folder and then putting that folder somewhere on the testing PC before running their test. Often these files do not even reside inside of the full Mac bundles necessary for execution or have even had their executable bit stripped from the binary, in effect making them benign to any system. The issue here is that none of the malware is actually executed or installed on the testing machine, nor does it constitute any kind of real threat to the system. In addition, this type of approach is often easily “gamed” by AV companies that are simply looking to do well on the test.
Without getting too technical, in recent years advancing technologies in the antivirus industry have continued to make leaps and bounds in terms of the detection and remediation methods and backend systems that are being used to detect malicious activity and protect end users from security breaches on their machines. Webroot has been a pioneer in implementing technologies that are forward-thinking, adaptive and have brought our product efficacy to unprecedented levels. Unfortunately, in order to actually be correctly tested on the effectiveness of these newer methods and technologies, it requires AV testing companies to install real infections, rather than a zoo of files that can’t even be executed. AV testing companies have been reluctant to adapt their Mac testing methodologies to changing technologies and approaches. So, what does this say about the validity of AV test scores? Does this approach make AV testing results a useful tool for sound consumer decision making when deciding on a Mac security solution?
AV testing has been a big concern for many companies over the years. We all want our products to perform at a high level and carry a positive market leading reputation. For many AV companies this has been true to the extent that they focus their primary client development efforts towards malware detection for AV tests, rather than real life infections. Isn’t this approach a detriment to the effectiveness of the product for the end-user? Here at Webroot, due to known issues in the AV testing climate, we have shifted priorities in order to drive our efforts and innovation into developing the best security products and customer experience that we can attain. We believe that our excellent standard for real world efficacy, in addition to the many value added features that are built into our products, bring the greatest value to our customer base.
10 Tips for Improving Your Home Router Security
With the recent news of router vulnerabilities, we thought it would be an excellent time to provide a few tips for improving your home router security. While nothing is hack-proof in the world we live in, you can take many steps to deter attackers from targeting you. I have arranged this from easy to do, to increasingly technical.
Simple steps to secure your home router
- Create a unique login. Most routers use a default login username such as “admin”, and a password that is usually just “password”. Be sure to change the login information (username and password) to something unique to you. Please note that this is different than your WiFi name and password.
- Create a username and password for your connection (WiFi). Consider changing it from the default to something that is not personally identifiable. Ideally, you DO NOT want your the manufacturer (Netgear. Linksys, etc.) or address as your WiFi name. Choosing WPA2 over WPA or WEP is also advisable. A long passphrase as your password that contains more than 20 characters is important here. REMINDER: you can disable the SSID broadcast so that only users that know your network name can connect. If you plan on having guests, create an entirely different Guest network. It is never advisable to give the credentials to your main connection.
- Avoid using WiFi Protected Setup (WPS). WPS is a nice convenience, but it leaves your WiFi network vulnerable. Malicious actors can use this to attempt connection with a PIN, possibly leaving you open to brute-force attacks.
- Keep router firmware up-to-date. Unlike your computer, your router doesn’t send reminders for new updates. It will be up to you to make sure you’re logging into your router regularly to check for updates.
More complex security tips
- Disable Remote Administrative Access. In addition, consider disabling administrative access over Wi-Fi. An Admin should only be connecting via a wired Ethernet connection.
- Change the default IP ranges. Almost every router has an IP resembling 192.168.1.1 and changing this can help prevent Cross-Site Request Forgery (CSRF) attacks.
- Restrict access via MAC addresses. Your router gives you the capability to specify exactly what devices you want to connect so that others are not permitted. You can usually identify the address of the specific device in the Admin Console of the router.
- Change from the standard 2.4-GHz band, to the 5-GHz band. If the devices you use are compatible, it is generally advisable to make this change. Taking this step will decrease the range of the signal and could stop a potential attacker that is farther away from your router from discovering it.
- Disable Telnet, PING, UPNP, SSH, and HNAP. You can close them entirely, but I generally advise putting them into what is referred to as “Stealth” mode. This stops your router from responding to external communications.
- Log out! This does not just apply to routers, though. You should log out of any website, utility, or console when you are done using it.
These router security tips should help protect your WiFi data from cybercriminals desiring to hinder your online activities.
Tech Support Scams Continue
We’re regularly asked about phone calls from “Microsoft” claiming that your computer is infected, and whether or not it is a scam – it is. Sometimes it’s a call from another “tech support” company, or a warning message on your screen. The truth is that Microsoft and other companies will not contact you to tell you that you have a computer problem through a phone call, email, or a pop-up warning message.
These scams are nothing new. We blogged about this previously in April of 2013 and a lot has changed in the malware world since then, but these scams continue. That we’re bringing these scams up again tells you one thing though – people continue to fall for them – don’t let yourself become a victim of one of these scammers.
If you’re contacted by one of these scammers, hang up, don’t click that link, and don’t call that number. Usually they’ll try to get them to let you access your computer remotely – don’t let them, and certainly don’t give them any personal information or a credit card number.
As long as you don’t let them log on to your computer remotely or download and install any software because of these scams you probably don’t have anything to worry about. These scammers don’t typically install malware on your computer; the scam is to get you to pay for tech support that you don’t actually need.
More information can be found on scams using the Microsoft name at the following links:
http://www.microsoft.com/security/online-privacy/msname.aspx
http://www.microsoft.com/security/online-privacy/avoid-phone-scams.aspx
http://www.microsoft.com/security/online-privacy/avoid-phone-scams.aspx
Keep your personal data personal
It’s National Cybersecurity Awareness Month in the US and Stay Smart Online Week in Australia, so you might say that security is on the minds of more people around this time. So as we start taking the lessons in and changing some of our habits, there is another area that could use more attention; our personal data.
With a large variety of social networks available around the world, the opportunities to share are endless, but with that, so is the opportunity for information gathering by malicious parties as well as chances that private information could be revealed in a breach. One way to avoid this from occurring is by being careful with your information and be aware with what information you give out. An example of this can be seen from the recent Ashley Madison scandal where people not only posted their real names and personal details, but also linked their work email in some cases, embarrassing not just themselves but the organisations they work for. Also the less information you give out (like emails and phone numbers) the less likely you’re hit with spam.
And then there comes the personal data that you carry with you, be it from home to the office or on your next big vacation. This data could be stolen and compromised for malicious intent such as stolen identities, financial fraud, or even blackmail.
It’s always handy to encrypt your drive, whether you travel with your device or not. It is vital to encrypt a drive if it has sensitive data on it relating to you or the organisation you work for. There has been quite a few cases in this country where unencrypted devices from organisations go missing with customer data on it, then the Data Protection Commissioner will get involved and likely impose penalties on the organisation. An example of this: http://www.independent.ie/irish-news/three-eircom-laptops-containing-customers-data-including-bank-details-stolen-26820140.html. As well as encrypting your drive, don’t keep sensitive data (passwords, security questions, info you don’t want other people to see, etc.) in unencrypted text files lying around your system. If anyone gets access to the computer these files will be compromised.
In this day and age it can never be too much effort to keep personal data personal, and with a few steps, you can help minimize the risk to that information. While some might take time to get used to, a healthy habit of being aware will only help in the long run.
Dow Jones Data Breach
In a letter to customers sent today, Dow Jones & Co has revealed that its services were breached, possibly exposing the credit and debit card information of customers. Reportedly only impacting “fewer than 3,500 individuals,” the information provided shows that the unauthorized accesses took place between August 2012 and July 2015.
“In today’s world – where literally anyone connected to the Internet is vulnerable – it’s no longer just a question of spending, it’s a question of processes and skills. Following the Dow Jones breach, I’m heartened that the CEO has publically said that no company is immune to cyberattacks. Solely recognizing that all organizations need comprehensive security solutions is the first step to reducing the onslaught of breaches we’ve witnessed over the last few years,” said Grayson Milbourne, Security Intelligence Director of Webroot.
“As large company breaches have revealed, security isn’t always a question of budget but also a question of skills and background checks. The name of the game is to find out what is going on in an environment and reduce the risk. Overall, there is a clear trend of attacks that aim to compromise companies who store vast amounts of user data. These businesses need to prepare for continued attacks by updating their security policies and systems to be on high alert.”
While Dow Jones & Co is reporting the information has been possibly compromised, they are also reporting that no evidence is pointing toward the information actually being used in authorized manners.
Bringing Layers of Security to Your Home Computer
When it comes to protecting your personal information in our ever-expanding cyber world, there are many ways to defend yourself. Since the vast majority of attacks originate on the Internet, it is smart to use multiple layers of security to ensure your computer (and the information it contains), stays secure.
One of the most common forms of protection is a Firewall, which is designed to block unauthorized access to the system, while still allowing communication outbound. Microsoft provides a firewall within the Windows OS as a standard security setting.
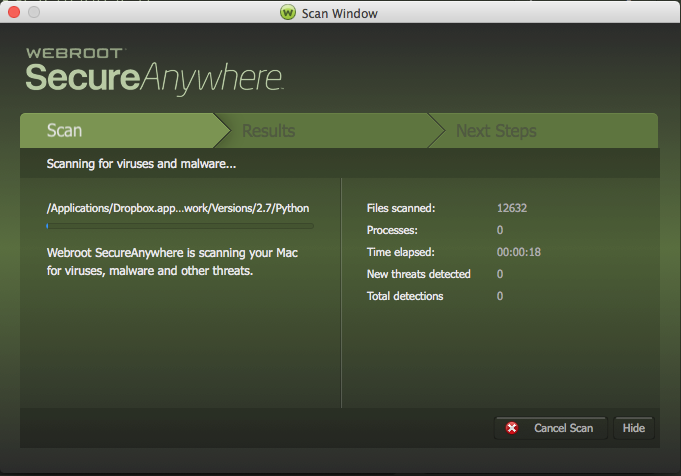
Along with having a Firewall, it is strongly recommended to have an Antivirus software running as well. This layer provides a defense against known malware and can use behavioural data to determine if a program is acting suspiciously. Of course I recommend Webroot SecureAnywhere, but the general rule is no matter who you have protecting your machine, to keep it updated at all times.
In the case of a successful breach or even just a computer malfunction, having some form of backup (online or external), can be extremely valuable. With an external backup solution, it is important to update it regularly, to ensure any new data or changes are saved. Also ensuring that this backup solution is not constantly connected to your PC helps if any infection does get through, keeping that backup protected. Online backup services usually allow backups to be created at a pre-determined time/day, automatically.
Finally, having the latest version of your preferred Internet browser along with a good Ad-blocking program will aid in keeping your web-browsing experience safe and more enjoyable. With the latest version, it will have many updates to the current security risks, coupled with usability and feature changes.
Each of these solutions has their own strong and weak points, but combined together they cover most of the areas you will have access to while using a computer. With multiple layers of security, you can make your computing experience safer and have the reassurance that your personal information is much more difficult to compromise.
It’s Time To Join The Family
Cybercrime. Remember the days when cybercrime was a word only super nerds and fans of the hilariously bad 1995 film Hackers used to say? No longer. You can hardly go a week without reading about the latest data breach, exploit, or hacktivist plot.
Back in the day, cybercriminals used to primarily fall under the lone wolf category, writing scripts and hunting for exploits without sharing their techniques, because if they did, it might cut into their profits. But, in the last few years, cybercrime has shifted from strings of unrelated, uncoordinated attacks—the digital equivalent of a bank robbery or a mugging—to highly calculated, business-like maneuvers determined to maximize revenue and get the hackers’ branding out there.
It isn’t just businesses that are suffering from these well-planned attacks, either. Even people with no affiliation to the companies suffering from data breaches are having their identities and payment information stolen.
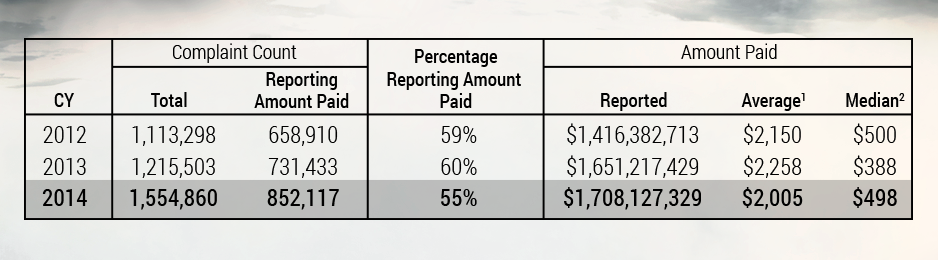
The FTC has seen growth in the last several years in reported cases of identity theft and payments fraud among consumers, with the costs also rising each year. With cybercriminals banding together to exploit the masses, it’s time consumers did the same.
Webroot® AntiVirus for PC Gamers takes a new approach to securing your gaming rig. By utilizing a Smarter Cybersecurity® approach to protecting devices, each computer defended by Webroot helps secure the rest of the Webroot network—our own, modern-day digital Family.
In Victorian London, the working-class had to band together to fight against exploitation and crimes perpetrated against the masses. In Assassin’s Creed Syndicate, you will play as twin Assassins Jacob and Evie Frye and fight for their cause. It’s time you did the same today and secured your gaming experiences with the lightest, fastest security in history!
Try Webroot AntiVirus for PC Gamers for FREE today and enter for a chance to win an Origin® EON15-S gaming laptop! Take down enemies of The Family in high-def style on this sleek, performance-driven laptop.
Get rewarded for doing what you already love to do. Sign up at www.assassinscreed.com/rewards to earn credits towards bonus in-game content, enter sweepstakes, and even win an Origin® EON15-S gaming laptop! Check out protect-the-future.com today and earn even more bonus Credits!
Avoid Unwanted Applications
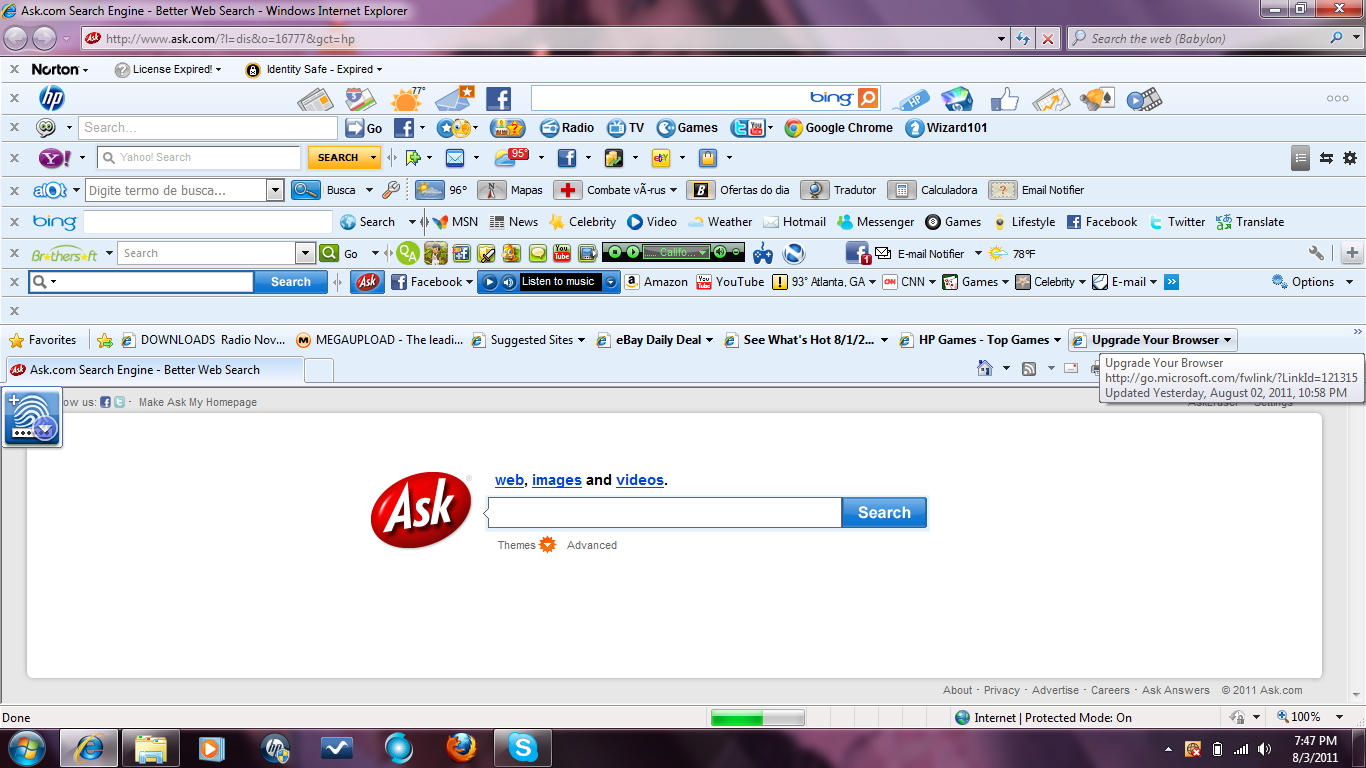
Has your home page changed? Are you getting pop-up ads that are “Provided by” some company you’ve never heard of? Are your search results coming from a different search engine? Welcome to the world of Potentially Unwanted Applications (PUAs.) While they can be annoying, PUAs are easily avoided.
The easiest way to avoid PUAs is to only install programs from their official download sites. Third-party download sites continue to be one of the main sources for PUAs. If you search for software downloads, chances are you will end up on a third-party site rather than an official download page and end up inadvertently installing PUAs.
When installing software, always pay attention to the install process – don’t just click “next” until the install is complete. Most installers allow you to opt-out of installing optional software, but they don’t always make it easy. Pay attention to any available install options, and always choose a custom install when possible. Watch for “skip” or “decline” buttons that will allow you to not install bundled applications. Look for check boxes that ask you if you want to install additional applications of change your home page or search settings. If you follow these suggestions it will help you to avoid installing PUAs.
Phishing Attacks and Lessons Learned
Phishing attacks have been a prevalent, and often quite successful method of obtaining sensitive data from unsuspecting victims for quite a few years now. These attacks are extremely common through email and usually only require the user to click on a link contained within, and enter the information requested. Due to the simplicity of obtaining potentially valuable data from users, many companies have been instituting security training for these types of attacks by using phishing tests to determine their employees’ ability to discern a real email from a possible phish.
With the latest breach coming from the United States’ Office of Personnel Management, the question remains of what could have been done to prevent such a high-security organization from making a simple mistake that could be catastrophic? The answer seems to be increasing the amount of security training that is taking place within these organizations, in regards to phishing attacks and basic online security.
Unfortunately, many users continue to fail these types of tests, while still holding high-level security clearance. This is likely due to the lack of reprisal for the user, aside from more security training sessions, which allows the poor behaviour to carry on. Paul Beckman, CISO for the Department of Homeland Security, has a different idea about consequences for these individuals, who are often senior managers or other C-level employees. He states, “Someone who fails every single phishing campaign in the world should not be holding a TS SCI with the federal government”, and suggests that these employees should have their security clearance removed until such time that they can prove to be responsible with extremely sensitive information.
Beckman said he hopes to move forward with the discussion of cracking down on repeat offenders, but it will all take more time and getting more CISOs on board. Meanwhile, these types of attacks are becoming more personal and thus, more difficult to prevent against.
With other companies able to learn lessons based off the circumstances surround the OPM hack though, we hope too see a continued shift towards education and understanding from the largest corporations down to the standard internet user. Maintaining awareness and understanding of the threats on the internet, especially effective ones such as phishing, is the first step in moving towards safer browsing habits.
History of Mac Malware
The subject that fan boys of each side love to argue about. Mac malware. The fact is that malware for Mac is real and it continues to grow as a problem. In 2012 Apple removed the statements “It doesn’t get PC viruses” and “A Mac isn’t susceptible to the thousands of viruses plaguing Windows-based computers.” I would like to shed light on the malware from beginning to now in hopes that it will bring an understanding of why security is needed on all operating systems, including your Mac.
 1982 – The first threat that occurred was the Elk Cloner (this however did not actually affect the Mac) which would cause the Apple II to boot up with a poem:
1982 – The first threat that occurred was the Elk Cloner (this however did not actually affect the Mac) which would cause the Apple II to boot up with a poem:
Elk Cloner: The program with a personality
It will get on all your disks
It will infiltrate your chips
Yes, it’s Cloner!
It will stick to you like glue
It will modify RAM too
Send in the Cloner!
1987-2003
There were a few different malware families that came out but being as they are using an operating system that is not really used I won’t go into great detail. In 1987 nVIR virus began to infect Macintosh computers. In 1988 HyperCard viruses started to gain traction. HyperCard was software created by Apple to execute scripts immediately on opening. MDef was discovered in 1990. MDef infected application and system files on the Mac. In 1995 Microsoft released a virus that would infect both PC and Mac users via Microsoft Word called Concept. In 1996 Laroux, the first Excel macro virus was found but didn’t actually do anything to Macs until Excel ’98 was released. In 1998 Both AutoStart 9805 and Sevendust were discovered.
2004-Present – This brings us into the modern operating system we all know and love OS X. Also the time frame where threats are created that can still affect systems in use today.
2004 – Renepo was found. It had the ability to disable a system firewall, and it would try to copy itself to /System/Library/StartupItems.
 2004– Amphimix a program which is also a MP3 file. When launched it displays a dialog box which reads “Yep, this is an application. (So what is your iTunes playing now?)” It then loads itself into iTunes as an MP3 file called “Wild Laugh”, playing four seconds laughter.
2004– Amphimix a program which is also a MP3 file. When launched it displays a dialog box which reads “Yep, this is an application. (So what is your iTunes playing now?)” It then loads itself into iTunes as an MP3 file called “Wild Laugh”, playing four seconds laughter.
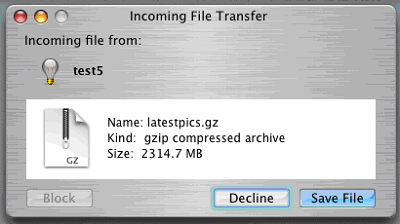 2006 – Leap is widely considered to be the original Mac Trojan. Leap used iChat to spread itself; forwarding itself as a latestpics.tgz file to the contacts on the machine. Inside the Gzipped Tar File (.tgz) was an executable file masked as a JPEG. When executed, it infected all Cocoa applications.
2006 – Leap is widely considered to be the original Mac Trojan. Leap used iChat to spread itself; forwarding itself as a latestpics.tgz file to the contacts on the machine. Inside the Gzipped Tar File (.tgz) was an executable file masked as a JPEG. When executed, it infected all Cocoa applications.
2006 – Inqtana was the second worm for Mac OSX. The worm propagated through a vulnerability in unpatched OSX systems.
2008 was a big year for Mac malware… Apple published an advisory to use antivirus software. They removed the statement from its website after being up for about two weeks.
2008 – BadBunny is a multi-platform worm written in several scripting languages and distributed as an OpenOffice document containing a macro. It spreads itself by dropping script files that affect the behavior of popular IRC (Internet Relay Chat) programs, causing it to send the worm to other users.
2008 – RSPlug is a Trojan that changed DNS to send users to malicious servers. It originally spread as a video codec that was downloaded from various porn websites.
2008 – AppleScript.THT tries to disable security software, steal user’s passwords, turn on file sharing, take screenshots of the desktop, and take a photo of the user via the built-in camera. The malware exploits a vulnerability with the Apple Remote Desktop Agent, which allows it to run as root.
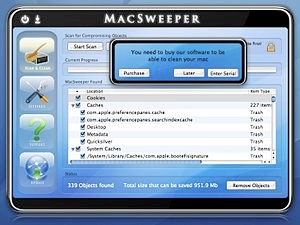 2008 – MacSweeper, Mac’s first ‘rogue’ application (a fake antivirus misleading users by reporting infections that doesn’t exists). When the infected user tried to remove the “infections”, MacSweeper asked to provide credit card details and pay $39.99 for a “lifetime subscription serial key.”
2008 – MacSweeper, Mac’s first ‘rogue’ application (a fake antivirus misleading users by reporting infections that doesn’t exists). When the infected user tried to remove the “infections”, MacSweeper asked to provide credit card details and pay $39.99 for a “lifetime subscription serial key.”
I won’t lie, before I got into threat research, I ended up with this on my Mac…
2008 – Hovdy tried to install itself to /Library/Caches. It disabled syslog/system updates, stole password hashes, open ports in the firewall, disabled security software, installed LogKext keylogger and started web server, VNC, and SSH. It also tried to get root access by way of ARDAgent vulnerability.
2009 – Iservice was discovered in a pirated version of iWork ’09. It copied itself to /usr/bin/iWorkServices and tried to execute a HTTP request. Updated variants were later found in a pirated versions of many high use programs.
August 28, 2009 – Apple released an anti-malware tool called XProtect,at release it could protect a Mac against only two threats (RSPlug and Iservice).
2010 – HEllRTS (aka HellRaiser) is a Trojan that allows control of a computer by a remote user. The remote user has the ability to transfer files, pop up chat messages, display pictures, and even restart or shut down the infected machine.
2010 – Boonana, a Trojan that spread via social media and email disguised as a video. It runs as a Java applet, which downloads its installer to the machine. After installed it starts running in the background and communicating with a variety of servers such as command and control servers.
2011 – MacDefender, another rogue like MacSweeper that installs itself into the /Application folder and wants you to pay them for the “infections” to be removed from your mac.
 2011/2012 – Flashback was disguised as a Flash player download and targets a Java vulnerability on Mac OS X. The system is infected after the user is redirected to a compromised bogus site, where JavaScript code causes an applet containing an exploit to load. The Flashback malware was the largest attack to date, hitting more than 600,000 Mac computers.
2011/2012 – Flashback was disguised as a Flash player download and targets a Java vulnerability on Mac OS X. The system is infected after the user is redirected to a compromised bogus site, where JavaScript code causes an applet containing an exploit to load. The Flashback malware was the largest attack to date, hitting more than 600,000 Mac computers.
2013 – Lamadai, a backdoor Trojan, targeted NGOs (Non-Government Organizations) and exploited a Java vulnerability to drop further malware code.
2013 – Hackback spied on victims and was designed to take a list of certain file types, find all files matching those types, compress them into a zip located in /tmp/ and upload them to a remote server.
2014 – LaoShu went viral via spam emails posing as a notification from FedEx. It contacts a remote server sending system information, files, and screenshots. It is important to note that it is signed with a valid Apple developer ID certificate.
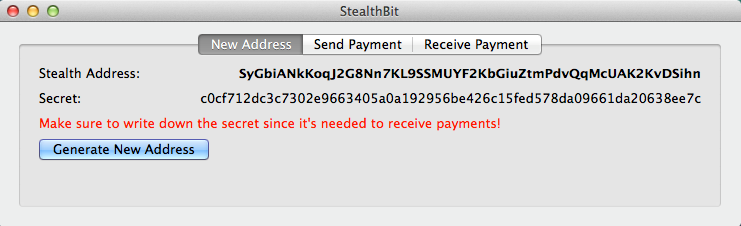
2014 – CoinThief is designed to steal Bitcoins from infected machines, and is disguised as legitimate apps. The source code was on Github for a while under an app named StealthBit.
It’s worth mentioning that these have been the main threats seen on the Mac and not all of them. There are many smaller variants and proof of concepts that are not listed. Also, that I didn’t include any adware variants such as Genieo or VSearch on here, but I did write about in my last blog. Even after seeing all of these there will still be those that refuse to believe that their mac is vulnerable to attack, but trust me it will only get worse from here. Apple is increasing their market share and with that comes an opportunity for malware writers to make more money.