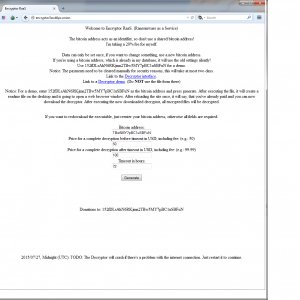
Encryptor RaaS (Ransomware as a Service)
A new ransomware has emerged and its very similar to tox as it is created for hackers to easily design encrypting ransomware payloads to distrube from their botnets. Since the creator of Tox was selling his operation, this could very well be the end result of that. The idea is to contract hackers with already operational botnets and campaigns use this page to create encrypting ransomware binaries to their specifications and then hand off 20% of their succussful scams to the Encryptor RaaS author.
All a hacker has to do with this page is just input the bitcoin wallet address they want the funds to go to. Then customize the price they want for immediate payment, late payment, and lastly a timer for what is considered a late payment.
Skip forward to infecting a victim and there is no GUI popup. Just all your documents are now encrypted and you have this new instructions text at every directory.

Typically you have to install a layered tor browser to get to here, but tor2web currently is supporting a gateway to the page even if you’re just using a normal browser like firefox or chrome. Here is what you’ll be presented with.

Instructions are fairly clear on how to install a bitcoin wallet and send money to the hackers holding your files ransom. If you wait too long then the price will go up – and is set by the generator we showed earlier. Once you have paid the ransom this page will update showing “PAYED” and will then have a link to the decryptor. The decryptor doesn’t have a GUI either and will just run in the background until all files are decrypted.
MD5 Analyzed: D87BA0BFCE1CDB17FD243B8B1D247E88
Additonal MD5 Analyzed: ECDACE57A6660D1BF75CD13CFEBEDAEE
Webroot will catch this specific variant in real time and heuristically before any encryption takes place. We’re always on the look out for more, but just in case of new zero day variants, remember that with encrypting ransomware the best protection is going to be a good backup solution. This can be either through the cloud or offline external storage. Keeping it up to date is key so as not to lose productivity. Webroot has backup features built into our consumer product that allow you to have directories constantly synced to the cloud. If you were to get infected by a zero day variant of encrypting ransomware you can just restore your files back as we save a snapshot history for each of your files up to ten previous copies. Please see our community post on best practices for securing your environment against encrypting ransomware.
Macs are immune to malware? Yet another Apple exploit…
Yesterday information was published online through www.theregister.co.uk discussing an exploit that was discovered in the Mac OSX 10.10 Yosemite operating system. The discovered exploit allows a user to gain root access on a machine without any admin credentials. The exploit uses an environment variable called DYLD_PRINT_TO_FILE that was added in the Yosemite operating system, and is used by the OS to specify where the dynamic linker logs error messages. It was discovered however that the environment variable can be used maliciously in order to modify files that are owned by the “root user” account. The bottom line is that with one basic line of code a malware author could easily do away with the password requirement for the user account being compromised, therefore giving them full reign on the system.
While this exploit has not yet been seen implemented into any new malware in the wild, it is important to be aware that such a huge vulnerability exists. As usual, Mac users should always exercise prudence when downloading and installing software onto their machines, as well as download a reliable internet security app. In addition, the exploit is not present in older versions of Mac OSX, such as Mavericks, and is not present on the 10.11 beta of El Capitan.
The vulnerable code is found below
echo ‘echo “$(whoami) ALL=(ALL) NOPASSWD:ALL” >&3’ | DYLD_PRINT_TO_FILE=/etc/sudoers newgrp; sudo -s
Another Hacking Team exploit that is CRITICAL for ALL Windows systems – CVE-2015-2426
 It just doesn’t seem to end with all the exploits being revealed by the Hacking Team dump earlier this month. This vulnerability could allow remote code execution if a user opens a specially crafted document or visits an untrusted webpage that contains embedded OpenType fonts. The Adobe Type Manager module contains a memory corruption vulnerability, which can allow an attacker to obtain system privileges on an affected Windows system.
It just doesn’t seem to end with all the exploits being revealed by the Hacking Team dump earlier this month. This vulnerability could allow remote code execution if a user opens a specially crafted document or visits an untrusted webpage that contains embedded OpenType fonts. The Adobe Type Manager module contains a memory corruption vulnerability, which can allow an attacker to obtain system privileges on an affected Windows system.
Adobe Type Manager, which is provided by atmfd.dll, is a kernel module that is provided by Windows and provides support for OpenType fonts. A memory-corruption flaw (buffer underflow) in Adobe Type Manager allows for manipulation of Windows kernel memory, which can result in a wide range of impacts. This vulnerability can allow an attacker to gain SYSTEM privileges on an affected Windows system. Hackers would use this to infect users systems with any type of malware and gain remote control access if they desired – all without notifying the user. Also, this vulnerability can be used to bypass web browser and other OS-level sandboxing and protections.
This is a confirmed exploit on Windows XP and up and Windows Server 2003 and up. Since Windows XP and Windows Server 2003 are no longer supported by Microsoft, there is no patch for users on those operating systems so we HIGHLY advise that you migrate to a newer operating system. Windows Vista, 7, and 8 users are going to have an update rolled out shortly that will patch this vulnerability so make sure you keep an eye out for updates. More info here
Turning failure into success
As a security professional it’s hard to say ‘I told you so’ but as far back as 2009-2010 Webroot was saying that the endpoint market was broken and that a new approach to stopping malware infections on endpoints was needed. At that time the rest of the endpoint security market was particularly quiet on their efficacy at stopping attacks they just kept pointing at meaningless and some would say gamed ‘independent’ test results about how great their efficacy was.
Of course the ‘chickens came home to roost’ and that efficacy was thrown under a Mack Truck over the past couple of years by the volume and frequency of new malware and its variants that was hitting endpoints. The attack patterns changed too. No longer did you have broad-based attacks now you had targeted, individualized and especially in 2014 continuous attacks aimed at known individuals in organizations.
The availability and open nature of today’s communications plus the exploitation by the big Internet players and other actors has meant everyone’s life can be pried into and used to make life more convenient, but with that convenience comes a dark side (that for many observers is seemingly winning and cannot be thwarted.) Frankly neither I, nor Webroot believe that.
Attackers’ methods can be turned against them and the attentions of the priers thwarted by only allowing them to access what you want them to access. Lots of security vendors believe that too. If those who want manipulate get smart then we need to get smarter. We can have smarter cybersecurity and we can make it consciously work together to make life very difficult indeed.
At Black Hat Webroot will be demonstrating and talking about some of the security solutions and collective threat intelligence that by working together make endpoints, servers, networks and the Internet safer for us all and are turning previous failures into success. In the end its choosing battles and winning the wars that will matter.
Happy Video Game Day 2015
Webroot would like to wish our fellow gamers a happy Video Game Day! To celebrate this epic game playing day, we want to help keep you safe and highlight the top motivation for PC gaming attacks.

Gamers are being targeted more and more by malware, trojans, and keyloggers, especially those that participate in pay-to-play games and MMORPGs (Massively Multiplayer Online Role-Playing Game). Your accounts, personal identity, banking information and even credit card numbers can be stolen if you are playing without a cyber-security solution. The PC gaming market is increasing rapidly and is expected to reach $30.9 Billion in 2016, and with that, the targets are getting bigger and more lucrative.
Top Motivations for PC Gaming Attacks:
- Financial Gain: To obtain records of your secure data
- Digital Assets: Take control of your account to sell or trade
- Social Hacking: Damage to user reputation and identity theft
- Free Gaming: Access to your user account for free gameplay
So the motivation is there, but some people might insist that the threats do not exist. But already this year, we have seen a large variety of attacks targeting gamers through a variety of methods. Some are simple, others more advanced, but the threats against gamers and their accounts do exist.
Top Threats in 2015:
- Spear Phishing: Targeted attacks via email and game chat to steal login information
- Keylogging: Captures keystroke information and sends it to the attacker
- Chat Attack: Hacking attempts where the attacker embeds the attack via chat systems on Skype, TeamSpeak, Steam, League of Legends, etc.
- Ransomware: Malware that restricts access to a system until the ransom is paid
- Trojans: The attacker sends the system instructions to install malicious software or remote execution of system commands and other data intrusion
Some gamers defend the idea of installing no antivirus security one their machines, citing claims of slowed performance and interruptions. While traditional security solutions often have gamer modes, they still impact security, and others will turn off security layers during game play, rendering machines less secure.
Top Reasons Why Gamers Don’t Use a Security Program:
- They rely on free diagnostic and clean-up tools
- There are too many alerts and interruptions during gameplay
- It slows down their gameplay
- They aren’t concerned about infections
- It requires switching to a gamer mode
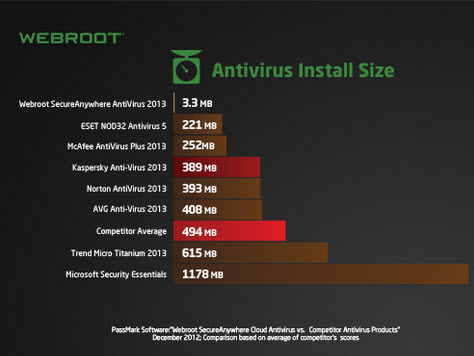
But new technologies do exist that are designed to keep gamers safe while playing online, even in this ever increasing threat world. Webroot SecureAnywhere for Gamers will not scan or update during your game and does not require a gamer mode.
Using real-time protection without sacrificing performance be using the cloud, Webroot SecureAnywhere ® Antivirus for PC Gamers reduces maintains a small footprint the PC increasing drive space, decreasing hard drive read/writes, and improving overall performance. No longer do gamers need to make the sacrifice of turning off security software to increase their speeds. One of a gamer’s worst nightmares is being milliseconds away from a kill shot or reaching a checkpoint when their screen minimizes for a Windows Update or a system scan from their antivirus solution. That’s why Webroot’s gamer security will not alert you or minimize your screen during gameplay. We understand the importance of lightning fast internet connections and zero slowdowns during gameplay.
To learn more about Webroot SecureAnywhere ® Antivirus for PC Gamers, click here.
The OPM data breach was probably inevitable
Breaches big and small have been in the news, from small organizations losing banking files to global groups like Sony losing seemingly everything to hackers. But with the recent Office of Personnel Management (OPM) hack that was revealed recently, with anywhere between 18 and 32 billion individual records stolen by digital infiltrators, we have not seen a breach to this scale.
The scary, and somewhat disappointing aspect, is that the breach was probably inevitable.
Encryption Not Present
While OPM Director Katherine Archuleta had noted the need for an upgrade in the technology and implementation of encryption on all the data 18 months prior, the need was dismissed due to the age of the networks. During testimony today with the House Oversight and Government Reform Committee, she said “It is not feasible to implement on networks that are too old.”
Contractors Credentials
On the other side, would encryption had helped as the breach all started with compromised contractors credentials? Dr. Andy Ozment, assistant secretary, Office of Cybersecurity and Communications stated during the same hearing that encryption would “not have helped in this case” as the attackers would have had the data encrypted once they accessed the machine.
Previously Breached
In July of 2014, the OPM had a breach of its networks, apparently with the breach being traced back to China. OPM downplayed the breach stating that no personal data was stolen but provided credit monitoring to employees. Following this breach, the Office of the Inspector General completed an audit of the whole department, finding significant failures in the security layers. The full investigation also found that there was no inventory of the endpoints, devices, databases, and investigators were not able to see if OPM was scanning for breach and vulnerabilities.
Two-Factor Authentication
During the same audit “We believe that the volume and sensitivity of OPM systems that are operating without an active Authorization represents a material weakness in the internal control structure of the agency’s IT security program,” the report concluded. In a day and age when two-factor has become a standard recommendation from the local IT friend to even the CIO of the US Department of Energy (http://energy.gov/cio/two-factor-authentication), this is one of the biggest failures within the OPM’s security layer. Lacking a physical CAC card or even phone authentication for login into the local machines and thus into the network could have saved the data from falling into the wrong hands.
These are just four of the issues leading up to this breach, areas often and exhaustively preached by security companies and professionals worldwide as the biggest and most vulnerable areas of attack. Beyond this, the audit itself not only highlighted the areas in need of immense improvement and increased security, but essentially laid the groundwork for the hackers, exposing all the weaknesses that have since been exploited, resulting in this breach.
For the full Inspector General report cited above from 2014, please click here: https://www.opm.gov/our-inspector-general/reports/2014/federal-information-security-management-act-audit-fy-2014-4a-ci-00-14-016.pdf
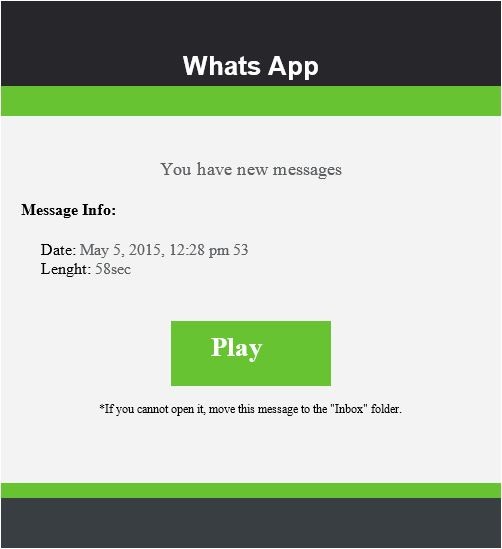
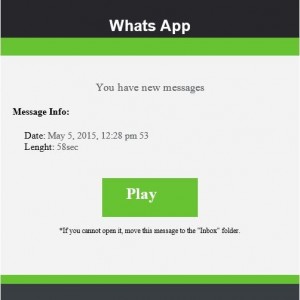
WhatsApp Spam Emails Making a Comeback
In 2013 we shared a series of blog posts about several WhatsApp scams making the rounds redirecting people to pharmaceutical sites and malware.
In recent weeks we have seen that these scams have made a comeback and are evading modern spam filters.
Sample Spam Email:
Using the email above as an example, by pressing the ‘Play’ button on a Desktop or Mobile browser the user is taken to a site masquerading as an article from the BBC titled:
SPECIAL REPORT: We expose how to lose 23 lbs of Belly Fat in 1 Month With This Diet Cleanse That Celebrities Use
Instead of taking the user directly to the scam site, they try to dupe the would-be victim into thinking that the deal is legitimate by impersonating the above article. All other links lead to the real BBC site, however attempting to leave the page will also launch a pop-up window to the fake shop which can be confused for a legitimate advertisement.
Pop-up window loads when leaving the site:
If the user chooses to learn more about the ‘celebrity cleanse’ they are then taken to a site where they are prompted to enter personal information including personal email, postal address, and phone number.
Sample screenshot of the landing scam page:
Remember, always buy from a legitimate, trusted site. If something seems too good to be true, it usually is.
Rombertik
Yesterday in the news we saw a huge spike in the interest of the Rombertik malware. Rombertik infiltrates the computer through email phishing attacks that drop as a .scr screen saver executable that contains the malware that will inject code into your browsers to spy on you and threaten your MBR or Encrypt documents if it detects that it’s being analyzed or sandboxed. We’ve been catching these variants since January 13th, but only now has it become so popular with the media coverage.
The initial drop is a zipped attachment and once unzipped it’s a .scr screensaver executable file. The first stage of the malware is checks to make sure it’s not being debugged or sandboxed where if it fails these checks will attempt to overwrite your MBR (Master Boot Record).
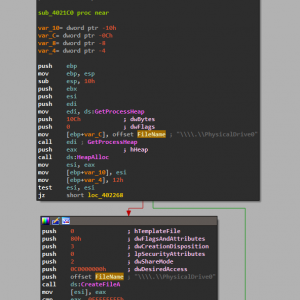
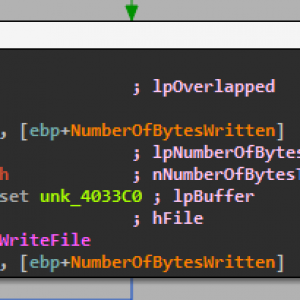
Here we can see the code “\\\\.\\PhysicalDrive0” in the first image where it is attempting to obtain the handle to the MBR. If it can get access to the MBR then it will perform the second image where it writes 200 hex bytes to the MBR with buffer to display the below message after the BIOS when starting your computer – forcing a bootloop until the operating system is reinstalled.
However, you will need to give this administrator rights in order for the MBR or encrpyting routine to complete. So unless you’re an XP user, you’ll see that familar user account control pop up asking if you wish to give “yfoye.exe” permission. I don’t know how many users are blindly giving permission to random executables that are originally expected to be documents from attachments (many group policies in businesses are also set to not give admin rights to email attachments), but I would suspect that the scare hype of this malware is limited to XP users.
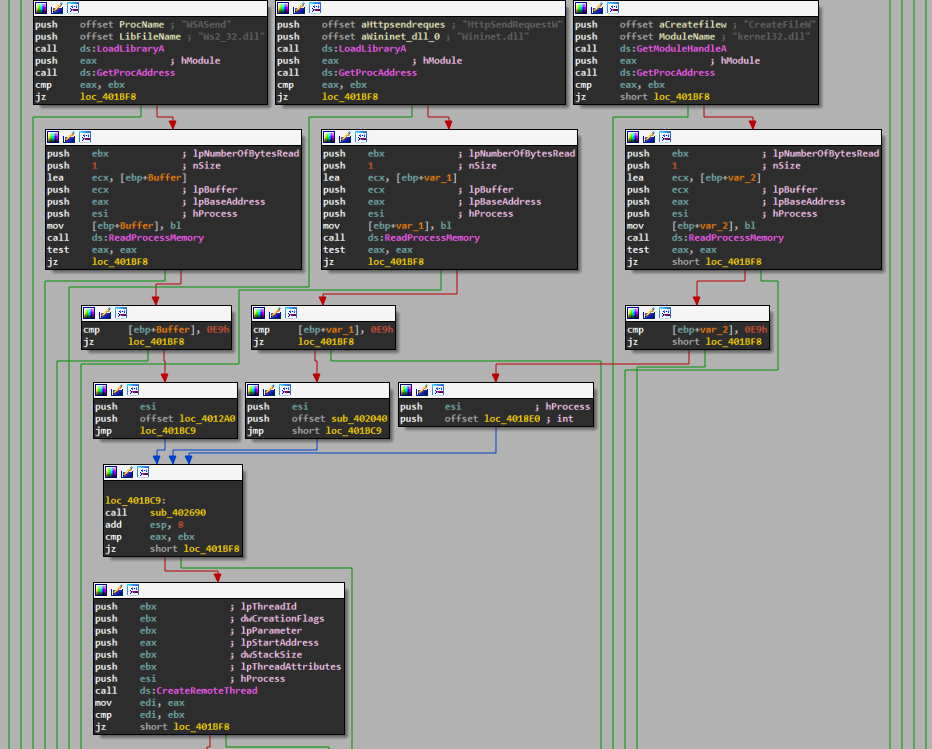
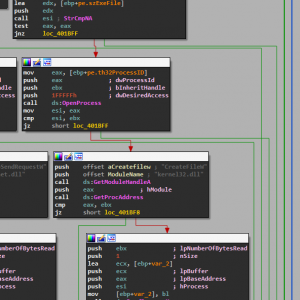
After all the checks for sandboxing and debugging are cleared the malware will then perform it’s normal operation of hooking into your browser. Below in the first image is Rombertik searching for handles to the Firefox process (it does this with other browsers like Chrome as well).
Then the second images shows it will connect to home and ensure that it can securely transmit the data it intercepts. Below, the malware injects a thread into the browser process to intercept and monitor network traffic API calls
For Rombertik specifically it drops through email phishing and Webroot has multiple layers of protection. First is going to be through the zip – we actually detect this exact drop as a zip once it writes to disk. If that doesn’t trigger, then next layer is once it’s extracted and will be blocked in real time right as the .scr executable inside the zip it’s written to disk. If that fails, then next layer of protection is through heuristics if an action by the file is picked up. Since after the sandbox checks it launches a second copy of itself and overwrites the second copy with remaining thread process it’s very suspicious and a common tactic used by encrypting ransomware as well so our heuristics look out for actions like this.
MD5 Analyzed:
F504EF6E9A269E354DE802872DC5E209 (W32.Rombertik.Gen)
Aditional MD5s:
9FA5CE4CD6323C40247E78B80955218A (W32.Rombertik.Gen)
21A728FCD1A45642490EE0DAF17ED73A (W32.Rombertik.Gen)
FAADD08912BADEF2AB855D0C488B9193 (W32.Rombertik.Gen)
AC94549FAF48D11778265F08535A55B7 (W32.Rombertik.Gen)
D95495728DB1D257C78BCC19B43E94FF (W32.Rombertik.Gen)
3733DD9DF99C08953216B3DA5A885EFD (W32.Rombertik.Gen)
B5AFBB36D9E3EC3BC4A9445627C23E4F (W32.Rombertik.Gen)
38F5191DE5B8C266746006E9766B2F9D (W32.Rombertik.Gen)
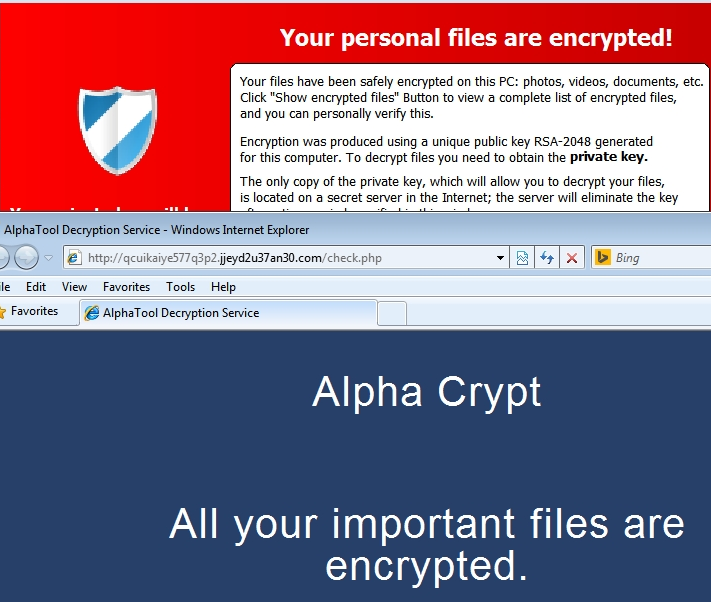
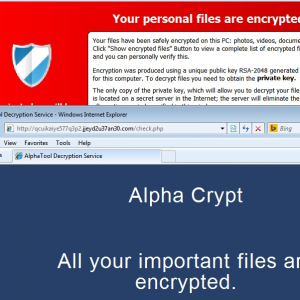
AlphaCrypt
We’ve encountered yet another encrypting ransomware variant and at this point it’s expected since the scam has exploaded in popularity since it’s inception in late 2013. This one has a GUI that is almost identical to TeslaCrypt.
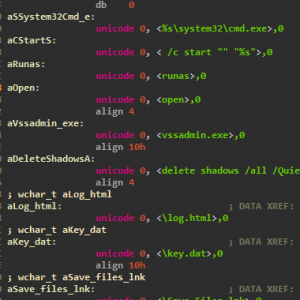
While this may look identical to TeslaCrypt it does have some improvements like deleting the VSS to make sure you aren’t saved by your shadow volume. Take a look at the below strings from an unpacked memory dump.
We can very clearly see that it opens up a command prompt and runs the command “vssadmin.exe delete shadows /all /Quiet” This will ensure that all shadow copies are deleted and the /Quiet will make sure that the command does not display messages to the user while its running.
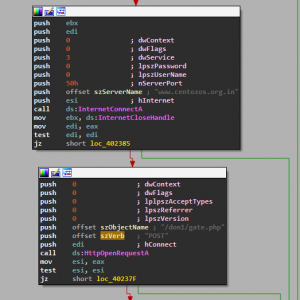
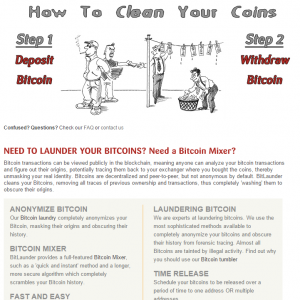
Payment is similar to recent variants – bitcoin through layered tor browsing. Not using a money mule like ukash or moneypak allows the authors to maximize thier earning power and anonymity. They can just take the full ransom amount and put through a bitcoin mixer that will use sophisticated algorithms to scramble it through millions of addresses and completely “clean” the money.
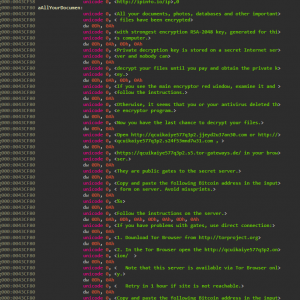
A more convenient feature this variant of encrypting ransomware has is that you are not immediately forced to use install the tor browser and will instead try and use URLs that use public gates to the secret server through your current installed browser. However, these don’t always work so the backup option is to install Tor like we’ve seen previously. See the entire ransom notice below.
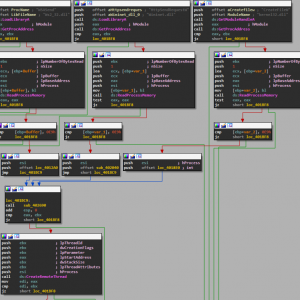
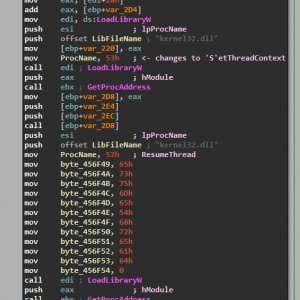
The volatitlity of this variant is quite high since it creates new instances of common windows processes to do the encryption routine to try and be as covert as possible and is extremely similar to how Cryptowall 3.0 opertates. Below is the final bit of unpacking, where it sets the child process context and resumes the thread.
MD5 analysed: 1C71D29BEDE55F34C9B17E24BD6A2A31
Aditional MD5 seen: 6B19E4AE0FA5B90C7F0620219131A12D
Webroot will catch this specific variant in real time and heuristically before any encryption takes place. We’re always on the look out for more, but just in case of new zero day variants, remember that with encrypting ransomware the best protection is going to be a good backup solution. This can be either through the cloud or offline external storage. Keeping it up to date is key so as not to lose productivity. Webroot has backup features built into our consumer product that allow you to have directories constantly synced to the cloud. If you were to get infected by a zero day variant of encrypting ransomware you can just restore your files back as we save a snapshot history for each of your files up to ten previous copies. Please see our community post on best practices for securing your environment against encrypting ransomware.
Google’s new Chrome extension is worth downloading
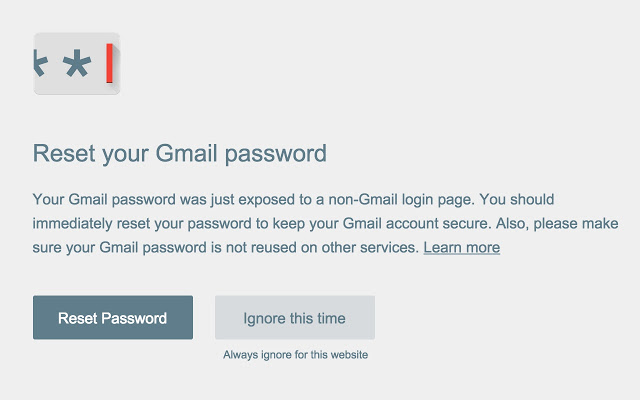
Yesterday, Google announced the release of their newest Chrome extension, Password Alert. The new free tool is designed to warn users of the popular browser when they are entering their Google passwords on non-Google websites, helping to protect their Google accounts from phishing attacks. The application also prevents users from using the same password for their Google account on other sites. While this secondary feature may seem overzealous, it is a necessity if one of these accounts are breached, then a hacker would have a higher chance of accessing the victim’s Google account with the same credentials.
Google is by far the number one target of phishing attacks. Developing a Chrome extension that protects users accessing their Google accounts will certainly help defend against the onslaught of phishing attacks targeting Google. It would be great to see this same technology extended to other browsers and also to protect other major targets of phishing. The Threat Brief includes the top targets for phishing, and while each company uses a different login technique, there is something to be learned from what Google has done with respect to protecting customers as they access their accounts.
This is a good time to remind everyone of very simple and effective strategies to keeping online accounts secure. To start, make sure your primary email password is different from all other passwords. As I mentioned, there is a domino effect if you can break into this account. We all hate remembering different passwords, but this one is a must for proper online security. Secondly, hard to break passwords are very easy to create, and the key is length. My tip is to think of a phrase that is unique to you. For example, I love cheese and skiing -> !Lovech33s3andsk!!ng*. A password like this is very easy to remember and very difficult to crack.
Technology like this is not the end all to password and internet security, but adding this to your tools for everyday use will only help to enhance your protection online.
Download the Password Alert for Chrome here: https://chrome.google.com/webstore/detail/password-alert/noondiphcddnnabmjcihcjfbhfklnnep
A Recap of RSA 2015
Last week marked one of the largest security conferences in the world, and with RSA 2015 now to a close, it is time to look back at what we shared, learned, and shown to the over 30,000 attendees of the San Francisco conference.
 Released: Webroot’s 2015 Threat Brief
Released: Webroot’s 2015 Threat Brief
This report contains insights, analysis, and information on how collective threat intelligence can protect organizations from sophisticated attacks.
- Press Release: http://bit.ly/1EfgHvc
- Download Your Copy: http://bit.ly/1A7cHsz

Shared: Webroot Threat Brief Infographic
Behind the 2015 Threat Brief are some amazing statistics that we thought readers would love to see as an infographic. Produced to help deliverthe state of internet security beyond the readers of the report, the infographic serves as a perfect vessel to share with friends the importance on online security.
- Check It Out Here: http://bit.ly/1Jvv6aX

Our Booth: Bigger and Better Than Ever
“It’s been an amazing week at RSA Conference. With many lessons learned by corporations, the security industry has responded quickly and made great strides this week to battle against the onslaught of cyber threats. Conference attendees responded overwhelmingly positively to our collective threat intelligence, smarter cybersecurity approach, speaking sessions and demos. In fact, our booth traffic has been higher this year than ever before, and we’re definitely looking forward to continuing these conversations at RSA Conference 2016.”
– Dick Williams, CEO, Webroot
Interested in seeing more? We have a full gallery below of our time at RSA Conference 2015, highlighting the Webroot team hard at work showing off the power of Collective Threat Intelligence from Webroot.
Fake Security Scams – 2015 Edition
New year; similar Scams. In 2013, I wrote an article talking about the popular Fake Microsoft Security Scams that were doing the rounds. As expected, these type of scams have continued to grow in popularity as a way for nefarious people to get money from users. Unfortunately, today these scams are more popular than ever. While the premise remains the same, some new versions of these blur the lines between what is a scam and what isn’t.
Recap
It’s worth having a quick look back at what exactly one of those aforementioned scams entails. The classic Microsoft scam goes something like this: the user gets a pop-up in their browser that tells them that they are infected and says to call a number (toll free of course) to get said infection removed. Once the user calls this number they will be directed to a website that allows the scammers (*agents*) to connect to the PC.
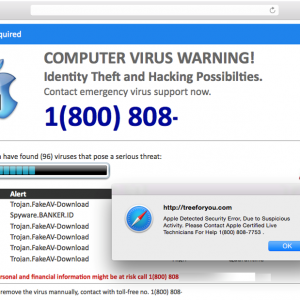
Figure 1: Typical Scam Message
Depending on the version the webpage (see screenshot above), the scam may try to set itself as the homepage, which means that even if the user restarts their PC, they will continue to see this warning message. This can help back up these scammers’ claims that the PC is infected.
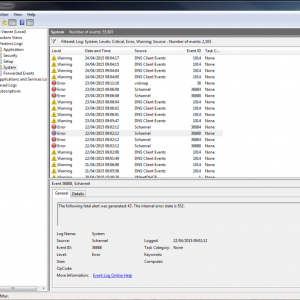
Once the scammers get connected they will show the user all the “infections” that are located in the Windows Event Logs. Windows Event logs are extremely useful to diagnose Windows issues. We would commonly use them to look for hard disk issues as any time Windows has an issue writing to a hard disk it will create a warning/error in the event logs.
After the scammers get connected, they will often install other programs that will show more errors messages. This will either be fake antivirus programs or trial versions of well-known programs that will show cookies that they will use as evidence of an infection.
In the example below, I have shown a snapshot of the warnings and errors from a test PC. It’s worth mentioning that even on a brand new PC there will be warnings or alerts in the Windows event logs.
Figure 2: Windows Event Logs
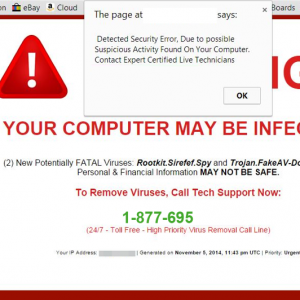
Another version of this type of scam is the version that locks the browser and uses quite intimidating language (as seen in the case below). Apparently, this user has a potentially FATAL Virus! Thankfully, we are a bit away from computer malware being able to cross the organic barrier to kill users but it’s the type of message that can catch less technical users off-guard. In certain cases the alert pop-up will keep re-appearing this locking the browser session.
Figure 3: It’s not fatal
So what’s new for 2015?
The biggest change compared to when we discussed this topic in 2013 is that these scams have now spread to other platforms, with Mac versions of these scams becoming increasingly popular. And they follow the exact same process as the PC versions. Remember that Macs do get malware and it highly advised that you install an antivirus product on your Mac.
Since these scams use a website, any device that has a browser can fall victim to this type of scam. They’re not OS dependent so if your internet enabled-toaster has a screen and a web browser it could get this type of alert! Joking aside, since it’s a browser-based scam, it’s advisable to have a backup browser installed just in case you have issues with your primary browser.
Figure 4: The Mac version
The Mac versions of this scam are pretty much identical to their PC counterparts. The only difference is that they won’t use the Windows Event Log viewer as it doesn’t exist on the Mac platform but they will use other tricks to try to fool users. In theory you could have a version that targets the Linux platform (since it’s browser based) but that platform (generally speaking) is used by more technical users and thus isn’t the target platform for these scammers.
The “Legitimate” Scam
The most disappointing of the new trends in Fake Security Scams, is the emergence of the “Legitimate” version. What do we mean by this?That well-known and respected multinational companies are using malware as a reason to charge users a fee to fix a device or service. Talk to anybody who works in IT and probably the most common reason why users suspect hardware isn’t working is due to a virus. It’s rarely (if ever) actually due to a virus, although there are of course exceptions to this. Remember the majority of malware these days is designed with the end goal of financial benefit to the person/group pushing the malware.
There is no real advantage for a scammer to stop your printer from working. The days of malware being made just to cause annoyance is long gone (although occasional cases still exist). So now let’s take a look at some of the common “legitimate” Scam types:
Your PC is part of a Botnet (an ISP favourite)
The botnet is a scam that has grown in popularity. An ISP (Internet Service Provider) will claim that a user is part of a botnet (Zeus being a favourite) and that for a flat fee they can clean out this botnet. Since the call has come from a legitimate source, the user will let their guard down and let the ISP “help” them out.
I have been connected to a number of these cases where the user has a PC that is supposedly part of a botnet. After running through the system with a fine tooth-comb and capturing network events, I was unable to find any evidence of botnet traffic. In these cases I advise the customer to contact the ISP and ask for the evidence used to determine the initial diagnosis. I have yet to hear back from any of these cases with some hard evidence of botnet traffic.
Printer (or other device) is not working because of a virus
This is by far and away the most popular type of “legitimate” scam that we encounter. A user is unable to get their printer working and they contact the hardware manufacturer. After going through a number of basic tests. it is determined that a virus is causing the issue and that they can remove the malware and setup the printer for a flat fee (notice the trend?).
I am picking on printers but it can be for any type of connected hardware. I have been connected to customers’ PC and have installed the printer for them after doing a full check for malware on the PC. In every case, it was just a matter of running through the steps and verifying that the device is installed.
What to do in the cases above
If you suspect that you have a virus that is causing a system issue, DO NOT give any credit card information to a 3rd party. Tell them you will contact them back, get the phone number directly from there Website (not the one they may give you over the phone). Contact Webroot and we can determine if there is a malware issue. Pretending to be from an ISP or an official company is a popular technique used by these scammers.
How to protect yourself from these scams
The tips that I discussed in 2013 are still valid. The first step is simply being aware that these scams exist!
- Microsoft will never call you telling you that your PC is infected
- Never allow strangers to connect to your PC
- Do not give any credit card info to somebody claiming to be from Microsoft
- If in doubt, shut down your PC and callWebroot
Tips to best protect yourself:
- Use a trustworthy antivirus program like Webroot Secure Anywhere
- Keep Windows updates turned on and set them to automatically update
- Use a modern secure browser like Firefox or Chrome
- Update any 3rd party plugins (Java/Adobe Reader/Flash player)
- Use an ad-blocker add-on in Firefox/Chrome
Looking Forward
I would like to think in two years’ time I won’t be writing another one of these but it’s a popular method to get money so I don’t see it vanishing any time soon. With Windows 10 fast approaching and with it being used on multiple platforms we may see these types of scams on all sorts of devices (perhaps even the Xbox one!). We have already seen CryptoLocker style apps on the Android platform and due to the popularity it’s only a matter of time before we start seeing mobile versions.
My advice would be to let people that aren’t technical know about these types of scams. The advanced user isn’t the target group for these scams so if you have less tech-saavy friends or family, let them know. Remember that as a Webroot customer, we can check your PC for malware free of charge.
Please contact us if you have any questions or issues. Click on the “Get customer Support” button or you can contact us over the phone.
Links: