Breach Therapy: 10 Companies Who Can’t Wait For 2014 To Be Over
Whether it be iPhones with bigger screens, major video game releases to make next-gen systems finally worth it, or wearables that are actually appealing to consumers, it’s safe to say any technological ‘advancement’ of this year was overshadowed by the seemingly endless wave of breaches that plagued companies and consumers alike.
With the New Year only a couple weeks and change away, let’s look back at 2014, aka the ‘Year of the Breach’, and revisit 10 companies who want nothing more than to forget their breach nightmares and start fresh in 2015:
Michaels
Going back almost a full year to January, and you have what was one of the first post-Target breach breaches to come to light. According to numerous sources (and reported by the ever-informed Brian Krebs), all signs were pointing to a potential Michaels breach. That same day (January 14), the US Secret Service said it was investigating further.
Fast-forward to April and we get the confirmation, with Michaels Stores Inc. announcing that 3 million customer credit and debit cards were stolen in Michaels and Aaron Brothers stores as a result of two eight-month long security breaches.
Goodwill
On July 21st, news of another breach started coming in. This time, the victim was Goodwill Industries. Or more specifically, the systems of a third-party vendor that processes payments for some Goodwill members (20 to be exact, which represents ~10% of all stores).
This breach, which was determined to be caused by a piece of malware called ‘Rawpos’, resulted in exposed information of 868,000 customer credit cards. Goodwill released details of the breach in September on their site.
The Home Depot
Speaking of September, that was a rough month for The Home Depot, which began when the company said it was “investigating some unusual activity with regards to its customer data.”
That ‘unusual activity’ ended up being a massive breach that involved pretty much every Home Depot location in the country.
Sure enough, six days after the initial reports started filing in, the company admitted that its payment systems were in fact breached, and that the attack was going on for months. What was not yet known was the scope of the attacks.
That announcement came 10 days later, with The Home Depot saying that the malware was contained, 56 impacted debit and credit cards later. The disclosure made the incident the largest retail card breach…ever recorded.
Japan Airlines
On October 1st, with The Home Depot breach still fresh on peoples’ minds, Japan Airlines said that it was the latest breach victim and that 750,000 frequent flyer club members’ information may have been stolen after hackers breached JAL’s Customer Information Management System and installed malware on computers that had access to the system.
The potentially stolen data included everything from customer names to membership numbers and home addresses.
JP Morgan
And then, just one day later, JP Morgan confirmed an absolutely giant breach that affected 76 million households and 7 millions small businesses. Affected were customers who used Chase.com and JPMorganOnline websites, and the Chase and JP Morgan online apps.
Stolen information included names, email addresses, phone numbers, and home addresses, but more potentially-devastating information such as account numbers, passwords, and Social Security numbers were not believed to be impacted.
Fox Business also came out with a report saying that the nation’s largest bank was also bracing for a mass-scale spear-phishing campaign right after the breach was exposed, and that the stolen info was the ‘first wave’ that would help the cybercriminals steal the aforementioned ‘good stuff’, which they could do with legitimate-looking emails targeting those customers who’s data they already nabbed.
While no such campaign has yet happened, it has not yet been determined for sure who was responsible for the breach and the investigation is still ongoing.
You can find more detailed descriptions of The Home Depot, Japan Airlines, and JP Morgan breaches in a previous blog I wrote.
Kmart
Later in October, Sears Holdings Corporation announced that it discovered a breach at its Kmart stores that was due to malware on their POS (Point-of-Sale) machines. At that time, Sears also announced that the malware was removed and that there was an ongoing investigation.
The investigation went on to reveal that the attack started in early September, which means that the breach was going on for a full month. Despite that, Kmart said that no personal customer information was stolen as a result of the breach.
Staples
Just over a week after the Kmart breach, Brian Krebs reported that he got information from multiple banks who said they were seeing a patter of credit card fraud linking back to a series of Staples stores in the Northeastern part of the country. At that time, Staples said it was investigating the issue.
According to a Bloomberg update from last month, Staples said that it believed the malware that caused was identified and eliminated, but that the investigation was still in its early stages and that they could not yet estimate the scope of the breach or how much data was stolen.
Last month, it was also reported that a link was found connecting the Staples and Michaels breaches.
USPS
On November 10th, numerous reports came out saying that the United States Postal Service was breached back in September, and that Chinese hackers were responsible.
This breach impacted both employees and customers, compromising data of 800,000 workers and 2.9 million customers.
Bebe
Earlier this month, security researcher Brian Krebs got word from banks about fraudulent charges on credit cards that were recently used at Bebe women’s clothing stores across the nation.
Sure enough, just a day later, Bebe Stores Inc. confirmed the breach, saying that the hackers got hold of customer information that may include customer names, account numbers, card expiration dates, and verification codes.
Sony
(Source: IB Times UK)
The latest, and perhaps most devastating (for the company affected, at least) of all 2014 breaches, the attack on Sony continues to make headlines daily as new details emerge and new information is leaked.
This breach has all the ingredients for a Hollywood flick (a mysterious enemy, global threats, massive exposure, a potential inside job, etc), which is ironic, considering that The Interview, a Hollywood comedy about two accidental ‘agents’ assigned to assassinate North Korea’s leader Kim Jong-un, may be what started the breach to begin with.
So far, the attack has crippled Sony’s corporate network, exposed personal employee information such as executives’ salaries, social security numbers and medical records, and leaked email conversations that have landed some top execs in hot water. And new details are continuing to emerge.
This list highlights only 10 of some of the most prominent companies that experienced a breach this year. As you can see, no industry is safe and no two breaches are exactly the same. The one constant? All 10 of these companies will have ‘Don’t get breached!’ as one of their New Year’s Resolutions.
Social Engineering improvements keep Rogues/FakeAV a viable scam
The threat landscape has been accustomed to rogues for a while now. They’ve been rampant for the past few years and there likely isn’t any end in sight to this scam. These aren’t complex pieces of malware by any means and typically don’t fool the average experienced user, but that’s because they’re aimed at the inexperienced user. We’re going to take a look at some of the improvements seen recently in the latest round of FakeAVs that lead to their success. While the images shown may have different names of A-Secure, Zorton, and AVbytes, they are identical in execution, appearance and are likely from the same author(s). Webroot users are protected from all variants of these encountered.

This is what the GUI looks like and it’s pretty standard. Well polished and full functionality of all buttons. Those “scanned files” don’t actually exist, but those directories do so this simple indexing can add some form of legitimacy of unsuspecting users.

This is probably the biggest improvement to the veil of legitimacy. These brands of FakeAV now come with an action center window that is almost identical to the real one. Right where you would normally see your legitimate security software’s status via windows they have theirs listed in all the same fashion. This is just a fake action center and the malware will prevent you from opening the real action center and will just redirect you to this window. I can see this tactic fooling even the average user at times. These rogues wouldn’t be complete without a payment “website” and these probably have the best developed so far. Here is the payment page and the home page.

Not only do these pages contain fake awards from legitimate testing companies, but they also have phony reviews and even a simulated news feed with product updates, blogs and press releases. This really is the icing on the scam cake as depending on the limited interaction you’ve had with the rogue, it could be enough to convince you that this program will actually help you and may be worth the money. Now skeptics will notice that there are some flaws like “VMworld 2011 Europe” – how would a 2015 product make it to that expo? And the image used at the top of the home page shows Win XP security when the product is for Win 7. These are all minor mistakes and could have easily been fixed. I suspect that we’re only going to see more innovation in the future and eventually might find rogues that will blur the lines between legitimate and fraudulent so well that they’ll be almost indistinguishable.
Vaporizer chargers can contain malware
Vaporizers (AKA E-cigarettes) have been gaining some serious traction and widespread use over the past few years. The sudden surge of popularity isn’t too surprising considering the fact that the health implications of nicotine consumption are vastly more favorable with vaporizers when compared to traditional cigarettes.
Most Vaporizers charge through a propriety connection to USB that looks something like this:

Should be harmless, right?
In a recent reddit post, the poster reported that an executive at a large corporation had a data security breach on his system from malware, the source of which could not be determined initially. The machine was patched up to date, had updated anti-virus protection, and Weblogs were evaluated. “Finally after all traditional means of infection were covered; IT started looking into other possibilities…” The made in china USB charger had malware on it that, when plugged into a computer’s USB port, would phone home and infect the system.
Now for those of you scratching your head going – hang on a minute… Windows hasn’t auto-executed anything from USB in YEARS. USB drivers are loaded from the library on the PC and I would know when it was plugged in and I would have to click and run a file in that folder – this whole story sounds fishy… Let me introduce you to BadUSB. Essentially this USB control chip would be reprogrammed to act as a keyboard + mass storage device. Once plugged in, it sends key-commands to open command prompt and then executes files from the storage. It’s not as if this vector of attack is brand new either – at least conceptually. According to @th3j35t3r (the Jester), a well known cyberwarrior in an article titled ‘What would I do if I was Chinese PLA’, USB charger attacks such as this are “theoretical but entirely possible, if not probable”.
My personal suggestion to those concerned is to only charge USB devices through a wall adapter (they charge faster anyway). If you REALLY need to charge through USB then I suggest getting one of these, dubbed “USB Condoms”, which will make sure that only power is drawn and no data is exchanged.

What kind of defenses exist for this type of attack? Basically not much. Malware scanners cannot access the firmware running on USB devices and USB firewalls that block certain devices do not exist yet. Behavioral detection is unlikely since the device’s behavior is just going to appear as though a user has simply plugged in a new device. It’s very unsettling and the threat is there however unlikely we think it is. While I doubt this is widespread or even remotely common, I did make sure to take apart my charger and made sure that there were no data pins and that it was only drawing power through USB.
Safe Online Shopping, Happy Online Shopping – 5 Security Tips for the Holiday Season
The holiday season is almost upon us, which means the holiday shopping season is also almost upon us.
And as always, it’s bound to be a crazy time of scrambling for the biggest and best deals, both in stores and online.
But while your wallet is destined to take a hit as you stack up on gifts for your family and friends, you want to make sure cybercrooks don’t make your list of people who will be receiving presents this year.
Sadly, with 2014 being labeled by some as ‘The Year of the Hack’, it may be easier for them than ever before to do just that. Fortunately, armed with some general security know-how, you can make their hacking jobs significantly harder while making your online shopping experience slightly less stressful.
Here are 5 online shopping tips to stay secure this holiday season:
Be Breachophobic
This one applies to traditional holiday shopping as well…
With the influx of massive data breaches across a wide variety of industries, no company seems to be safe. And popular retailers have been hit particularly hard (looking at you, Target, Michaels, Home Depot, Staples, KMart, etc).
Unfortunately, these breaches don’t show any signs of slowing down. Perhaps even more unfortunately, as a result of this, consumers are experiencing ‘breach fatigue’ and not changing their buying behavior even in the midst of all these attacks (according to a recent report from Ponemon).
But in this case, fear is actually a good thing. It keeps you on your security toes. Don’t have the ‘yeah, a lot of people are impacted, but it won’t happen to me’ attitude when it comes to breaches.
If you learn of a breach at a company whose store you recently bought something in or at a bank that you use, take a proactive approach. Call you credit card company and have a new card issued ASAP. Call your bank and find our what steps you need to take to protect yourself. These are not the most fun activities, but they could save you from a potential financial/data loss nightmare.
Likewise, if you’re planning to go shopping at a particular retailer and you find out they’ve recently experienced a data breach, look to do your shopping elsewhere. Ok, maybe you won’t be able to take advantage of that exclusive Black Friday deal, but most of the competing big-name stores will likely have something similar. Plus, what good is that brand-new big-screen TV you got for a ‘steal’ if attackers got access to your credit card number?
Beware of enticing ‘Amazing Deal’ links in your email inbox
If a deal looks too good to be true, it probably is.
Phishing emails are still a popular tool for cybercriminals. The difference these days, however, is that they look more legitimate than they did in the past. Obvious red-flags like blatant grammatical errors or strange email addresses from the sender are less common and the bad guys are finding more creative ways to get you onto their fake, information-stealing pages.
An example of a UPS Phishing email (Source: PC Mag)
And the fact that the holiday season has many legitimate great deals actually benefits cybercriminals, giving them a perfect opportunity to blend in with a phishing email that would normally seem out of place.
So don’t just immediately click a link in that ‘great deal’ email that popped up in your inbox. Verify that the sender is legitimate, check for grammatical errors and inconsistencies, and even compare it with another email you’ve gotten from that company in the past that you know was legitimate. If there’s something odd or out-of-place, don’t pull the purchase trigger and potentially open yourself up for identity theft or money loss.
Know your surroundings
Just because you can connect to WiFi almost anywhere doesn’t mean you should connect to WiFi any time it’s available.
If you’re doing any of your holiday shopping online, it’s really in your best wishes to do it over a secure network.
As appealing as it may seem to knock out some of your holiday shopping as you’re sitting sipping your mocha at that coffee shop, know that public WiFi hotspots are just that – public. That means anybody can connect to them, including an attacker looking to catch a hapless holiday shopper unawares.
There’s a much lower chance someone will break into your network at home, unless of course your home network isn’t password protected. Which brings up another good tip – password-protect your WiFi network at home. And make sure to actually use a strong password! No ‘password’ for your password.
Mobile Devices are vulnerable, too
PC, Mac, Android, iOS…it doesn’t matter. No device/operating system is malware or hacker-proof. Let me rephrase: that means mobile devices aren’t in the clear! No, not even the iPhone is safe; remember the recent WireLurker malware?
So if you’re thinking: “I’ll just do my all my online holiday shopping on my tablet to avoid the chances of getting hacked”, don’t do that. It’s a flawed mindset.
Mobile is a hot target for hackers at the moment. Remember that today’s mobile devices aren’t the bricks of yesteryear that you used to make calls and play Snake. Nope, today’s smartphones (and especially tablets) are bonafide computing machines, and protecting them in the same way you’d protect your computer isn’t an idea that should be ignored.
But aside from installing mobile security (which you should definitely do), there are other actions you can take to mitigate mobile risks, a major one being not jailbreaking/rooting your devices and/or using third-party app stores. Easier to do and access on Android devices, these third-party app stores are often riddled with malicious apps that can steal your information and dollars.
Safeguard all your devices
Even if you’re intelligent in your browsing and downloading habits, having computer ‘street smarts’ isn’t enough anymore. New threats are emerging seemingly by the hour, vulnerabilities like HeartBleed and Shellshock are coming into light, and if you fall victim to an encrypting ransomware (that seems to be ever-evolving) with no sort of protection, you’re paying hundreds of dollars to get your files back or paying even more for a new computer.
But let’s bring it back to the holiday shopping topic. Take the fake phishing email scenario, for example. Even if you take the aforementioned steps to verify the validity of the email, you’re not completely out of the ‘cyber’ woods. Like I said, hackers are becoming increasingly more clever and those phishing emails are often very difficult (if not flat-out impossible) to distinguish from the real thing. You need an intelligent security solution to have your back in case you get tricked despite your best efforts.
The holiday shopping season is less than a week away so be sure that you’re ready and that your devices are secure. Follow these basic online shopping security tips and go out there and buy those presents…carefully, yet confidently! And by ‘go out there’, I mean on the internet. That way, you can avoid this:
(Source: CNN Money)
Happy holiday shopping!
CoinVault

CoinVault
Today we encountered a new type of encrypting ransomware that looks to be of the cryptographic locker family. It employs the same method of encryption and has a very similar GUI (kills VSS, increases required payment every 24hr, uses bitcoin payment, ect.).

CoinVault GUI
Here is the background that it creates – also very similar.
What’s unique about this variant that I wanted to share with you all is that this is the first Encrypting Ransomware that I’ve seen which actually gives you a free decrypt. It will let you pick any single file that you need after encryption and will decrypt it for you.

It even works too! How nice of of them.
This is a really interesting feature and it gives a good insight into what the actual decryption routine is like if you find yourself actually having to pay them. I suspect that this freebie will increase the number of people who will pay.
Webroot will catch this specific variant in real time and heuristically before any encryption takes place. We’re always on the look out for more, but just in case of new zero day variants, remember that with encrypting ransomware the best protection is going to be a good backup solution. This can be either through the cloud or offline external storage. Keeping it up to date is key so as not to lose productivity. Webroot has backup features built into our product that allow you to have directories constantly synced to the cloud. If you were to get infected by a zero day variant of encrypting ransomware you can just restore your files back as we save a snapshot history for each of your files up to ten previous copies.
A Recap of the JP Morgan Breach
There is a clear trend that every year there are bigger targets compromised with increased frequency with more personal data being collected. The recent attack on JP Morgan Chase is especially alarming considering they are the largest US bank and hackers had gained access to numerous servers with administrative access for nearly a month before being detected.
According to reports, JP Morgan Chase account details for every consumer and business customer, including to name, address, email address and phone number, were compromised. Fortunately more specific details such as account numbers, social security numbers (SSNs) and passwords were not accessed. This is due to much stronger security measures being implemented to keep this data safe.
While the nature of the breach have not been disclosed, the company may have been targeted by a group of Russian hackers. Often these attacks are very well planned, targeting a few key employees for the first stage of the breach. These individuals are analyzed to understand their web habits.
Based on their analysis, an attack will be staged to either infect a target system or to gain credentials. Often it happens by attacking a website that is frequently visited by the target as security of an individual website is far less than that of a big corporate bank.
To reduce the impact of this attack, JP Morgan Chase could have applied the same level of encryption and security to user account details that they applied to account numbers, SSN’s and passwords. Another option would be to enforce a strict two factor authentication policy for all network administrators.
Overall, there is a clear trend of attacks that aim to compromise point of sale systems as well as companies who store vast amounts of user data. These businesses need to prepare for continued attacks by updating their security policies and systems to be on high alert.
We analyze Cryptobot, aka Paycrypt
Recently during some research on encrypting ransomware we came across a new variant that brings some new features to the table. It will encrypt by utilizing the following javascript from being opened as an attachment from email (posing as some document file).

Malicious script from email
Once full encrypted you’ll get a popup text document informing you that all your files have been encrypted and how to pay money to get your key to decrypt. This specific sample is Russian, and the instructions were also in Russian so I didn’t show it here. The really interesting thing about this variant that I wanted to share is that once it finishes it actually shows you a twitter feed that populates a tweet every time someone pays the ransom. I suspect this does increase the chance that people will pay the ransom.

Blurred out emails of the victims who paid
Webroot will catch this specific variant in real time before any encryption takes place. We’re always on the look out for more, but just in case of new zero day variants – remember that with encrypting ransomware the best protection is going to be a good backup solution. This can be either through the cloud or offline external storage. Keeping it up to date is key so as not to lose productivity. Webroot has backup features built into our product that allow you to have directories constantly synced to the cloud. If you were to get infected by a zero day variant of encrypting ransomware you can just restore your files back as we save a snapshot history for each of your files up to ten previous copies.
What To Know About Apple and WireLurker
Everyone’s heard the saying ‘Macs aren’t malware-proof’, right? Oh, you haven’t? Count me not surprised.
It could be due to the fact that that’s not an actual saying, but the more likely reason is that there is a deep-rooted belief among Apple users that Apple products and services are somehow, by default, impervious to viruses, malware, hackers, etc. Allow me to reiterate: THEY’RE NOT!
Need proof? Well, we could look back two years ago to Dexter (not the hit Showtime show). Or let’s rewind to early this year, when researchers learned that Macs were still vulnerable to 2011’s famous ‘Flashback Trojan’? Or how about iDroid, the mobile trojan capable of infecting both Android and iOS devices? Then there was September’s iCloud hack fiasco that started the wave of nude celebrity photos across the world wide web. And then, just yesterday, it came to light that two of Apple’s security tools, Gatekeeper and XProtect may not pick up the recently-discovered iWorm malware.
But just in case all that isn’t enough, enter WireLurker, the newest piece of evidence to back up the ‘Mac-and-iOS-malware-is-real’ school of thought.
(Source: Mashable)
Discovered by security researchers from Palo Alto Networks (you can download the report here), WireLurker is a new family of malware that was found in the wild on a popular third-party Chinese app store called Maiyadi, and that allows hackers to infiltrate iOS devices through an infected Mac via a USB connection (only the second known instance of this kind of iOS attack). But what truly makes it unique is that it’s able to infect iOS apps in a fashion similar to a traditional virus and, even more importantly, it doesn’t require for the iOS device to be jailbroken to do its damage.
According to the report, WireLurker has already ‘trojanized’ 467 OSX apps in the Maiyadi App Store. Those apps have been downloaded 356,104 times.
The (relatively) good news is that this malware attack is pretty limited in scope. We were able to secure a quote from Ryan Olson of Palo Alto Networks, one of Webroot’s technology partners:
“Our lead researcher on this effort, Claud Xiao, first began investigating the malware after seeing reports of strange activity on Mac OS and iOS devices in China. He tracked the attack back to it’s source and took a deep dive into the malware to discover how it works. We don’t expect this WireLurker malware to spread to the United States, but the tactics that it uses are likely to be copied by new attackers who could have new targets in mind.”
An Apple spokesperson offered some more good news:
“We are aware of malicious software available from a download site aimed at users in China, and we’ve blocked the identified apps to prevent them from launching. As always, we recommend that users download and install software from trusted sources.”
The fact that WireLurker is only targeting users in China may be a sign of relief for the West, but, as Olson pointed out, it doesn’t mean a similar attack couldn’t be expanded to wreak havoc outside of China. iOS (unlike OSX) has had a fairly spotless record when it comes to malware up until this point (if you don’t factor in ‘jailbroken’ devices), but WireLurker is the first real virus scare for the OS because it doesn’t require a jailbreak to infect the device, making it an exception to the ‘the Apple App Store is the best protection against viruses’ rule.
So what does all of this mean for Apple device users?
Michael Sweeting, one of our Senior Threat Analysts and who specializes in Apple devices sums it up nicely:
“End users of non-jailbroken iOS devices are typically unable to load third party applications, and are therefore somewhat protected from malware attacks propagated through app installs. OSX.WireLurker however is a new approach to infecting iOS devices with information stealing malware, by infecting third party application installers for OSX, and in turn infecting the iOS device once connected to the Mac via USB. This type of infection should once again remind Mac and iOS users alike that these devices are not immune to attacks, and even bigger more sophisticated attacks may be on the horizon. Users should continue to exercise caution and prudence, and should avoid downloading Mac software from third party app stores.”
That ‘caution and prudence’ doesn’t only mean updating iOS, avoiding connecting your iPhone or iPad to unknown/untrusted computers, and not jailbreaking your device and sticking to the App Store (all of which are encouraged security tips, by the way). It may also mean safeguarding your Mac with an internet security solution.
Or maybe most importantly, it may mean finally accepting that Apple devices aren’t unhackable machines. But hey, if you already exercise the former precautions, you probably already take Apple security seriously and the last point likely doesn’t apply to you.
Son of a Breach! Can Companies Just Safeguard Their Customers’ Data?
Just when consumers were starting to regain some company trust and safe-shopping stability after last year’s massive Target breach, a string of new large-scale company breaches quickly reminded us consumers just how insecure our personal data can be.
Needless to say, it’s been a rough year for some major companies and an even rougher year for thousands of unlucky customers. Let’s look at three of the major breaches of the last couple of months.
Home Depot
(Source: Krebs On Security)
Early last month, reports started coming in that the home improvement giant was investigating “some unusual activity with regards to its customer data.” Security reporter Brian Krebs immediately called credit card breach, especially since multiple banks came out to say that they were seeing evidence that Home Depot was the likely source of a batch of stolen credit and debit cards that went on sale in the cybercrime black market that morning.
Sure enough, six days later, the company admitted that its payment systems were in fact breached and that the hack was going on for months. They went on to say that while credit card data was exposed, personal pins were not. Reassurance (not really). And while the exact number of affected cards wasn’t known at that time, one thing was for certain: If you used a credit card at one of Home Depot’s U.S or Canadian stores in the past 4-5 months, you needed to consider your credit card stolen and get on the phone with your bank ASAP.
About two weeks later (September 18th), Home Depot announced the number. A whopping 56 million cards were impacted, making the incident the biggest retail card breach…ever (on record, at least). The ‘silver lining’? Home Depot also said that the malware was now contained.
Japan Airlines
(Source: Google Images)
Before the month of September passed (and with Home Depot still fresh on everyone’s minds), another large company from a completely different industry had some bad news to share with its customers…
On September 30th, Japan Airlines (JAL) confirmed that as many as 750,000 JAL Mileage Bank (JMB) frequent flyer club members’ personal info was at risk thanks to a breach. Apparently, hackers were able to get into JAL’s ‘Customer Information Management System’ by installing malware onto computers that had access to the system. The data that was accessed? Everything from names to home addresses to birthdates to JMB member numbers and enrollment dates. The good news is that credit card numbers and passwords did not appear to be exposed.
There have not been any new developments about this breach, but you here is the official statement by JAL from September 29th.
JP Morgan
(Source: Reuters)
October 2014 was only two days young when yet another major company confirmed a data breach. This time, the victim was JP Morgan. Or rather, JP Morgan customers who used Chase.com and JPMorganOnline websites, as well as the Chase and JP Morgan mobile apps.
Last Thursday, the nation’s largest bank revealed that a mid-August cyberattack exposed personal info for 76 million households, as well as 7 million small businesses. More specifically, names, email addresses, phone numbers and addresses were stolen, while JP Morgan went on to say that there was no evidence that account numbers, passwords, Social Security numbers or birthdates were exposed. While the bank found out about the breach of it’s servers in August, it has since been determined that it began as early as June.
Unfortunately, not much else is certain at this time. What we do know is that Russian hackers are suspected (still not confirmed), over 90 over JP Morgan’s servers were affected, and it is believed that nine other financial institutions were also targeted (although we don’t know their identities). The lack of concrete information is scary in it’s own right, but the fact that JP Morgan is staying mum on the matter is even more troubling. According to a Huffington Post report from earlier today, the bank is refusing to say how many people were actually hit by the breach, with spokeswoman Trish Wexler saying that JP Morgan isn’t offering more details beyond what was announced last Thursday. This could mean that the breach, already the largest (against a bank) in history, could potentially be even larger than the reported 76 million households and 7 million small businesses, keeping in mind that ‘households’ is not the same thing as ‘individuals’.
Additionally, Fox Business is reporting that the bank is now bracing for a massive-scale spear-phishing campaign in the wake of the breach. according to their sources. Considering that no bank info was compromised in the original breach (JP Morgan said in a statement that they haven’t “seen unusual fraud activity related to the incident”), this is a plausible next-step. Using the personal info obtained in the ‘first wave’, the attackers can send out legitimate-looking emails to the affected customers that say there is a problem with the user’s account and ask for Social Security numbers, passwords, etc. Alternatively, the emails could ask the customer to click an embedded link to update their account info, but in reality, the customer is taken to a official-looking fake site from which the attackers can nab the important financial information. In either case, the virtual trap is activated at that point.
What to do?
It’s no secret that data breaches are on a steep rise. According to a the Identity Theft Research center, there have been 579 data breaches this year, 27.5% more than there were at this time last year. And that number is only going to continue to increase.
In any of these three breaches, it’s important for customers to take basic security steps to ensure their information is safe, whether that means calling your bank and getting a new credit card issued (in the case of Home Depot), changing your password if you’re a JAL frequent flyer and JMB club member, or changing your log-in information and monitoring your online accounts if you bank with JP Morgan or Chase.
As more and more people choose to bank online (and become more internet-dependent in general), it’s also no secret that employing powerful and always up-to-date internet security on your devices is more crucial than ever before. Company breaches and spear-phishing attacks aren’t going anywhere. Take the necessary steps to keep your personal info protected!
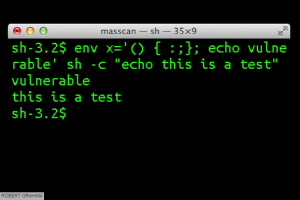
‘Bash’ Shellshocks the Internet – Here’s What You Should Know
Update: Apple has patched the Bash bug. For more info (including links to download the updates on your Mac), check out this TechCrunch report.
As of last week, there’s a new security bug in the news, and it’s wreaking havoc on the Internet.
(Source: Macworld/Errata Security)
Discovered by Stephane Chazelas, a security researcher for Akamai (who revealed the bad news to the world last Thursday), the ‘Bash bug, or ‘Shellshock’, is a particularly nasty vulnerability affecting the Bourne-Again Shell (thus the Bash acronym) of certain versions of the Unix and Linux operating systems. Yes, that includes derivatives like the Mac OS. In other words, it’s everywhere, and could affect a countless number of devices that connect to the internet.
Remember Heartbleed? This is scarier. And potentially a bigger deal, too.
Why? According to Robert Graham of Errata Security:
“Unlike Heartbleed, which only affected a specific version of OpenSSL, this bash bug has been around for a long, long time. That means there are lots of old devices on the network vulnerable to this bug. The number of systems needing to be patched, but which won’t be, is much larger than Heartbleed.”
Oh, and it IS old. How old? Graham said in a different blog post that the bash issue has been around for 20 years.
For the record, the National Vulnerability Database gave Bash a 10/10! Here’s what you should know.
What is it?
As previously mentioned, it’s vulnerability, a bug affecting the Bash shell used in many Unix and Linux operating systems. Think of the Bash shell as the command-line shell. This means that a hacker could take over and issue remote commands to web servers that aren’t patched. As a result, private information could quickly become public information.
Is every device running Linux or Unix vulnerable?
No. According to Rapid7 Global Security Strategist Trey Ford, there are certain requirements that make a server vulnerable. More specifically, servers capable of passing commands over the internet remotely, are susceptible.
What makes it so dangerous?
Bash may not affect as many devices as Heartbleed, but that may be the only consolation. Because (unlike Heartbleed) Bash lets hackers execute commands remotely, the repercussions could be a lot more serious.
Who should be worried? Should you?
While network administrators who manage internet presence for their companies (particularly those running a CGI app written in Bash or using Bash script), should be concerned, the everyday desktop user probably doesn’t have as much to worry about. That is unless you have a bunch of connected ‘Internet-of-things devices’
What about those Internet-of-Things Devices?
This is largely about patching updates, so while the aforementioned everyday desktop user may not be affected by Bash, that doesn’t necessarily mean his or her connected devices aren’t vulnerable. From home automation systems to routers to webcams to refrigerators, there are many Internet-of-things devices that use the Bash script. And most users would probably never think twice about installing software updates on something like a fridge. Now they should.
What’s being done?
Companies like Google and Amazon were quick to react, rushing Thursday to patch this latest vulnerability on their end. And because recent versions of the Mac OS are vulnerable, Apple quickly responded, saying that while most OSX users aren’t at risk, the company was quickly working on patching the flaw. You can read more about that here.
What should you do?
Unfortunately, there’s not much you can do as this is a widespread vulnerability rather than say, a sneaky piece of malware. And because this is the case, you, as a consumer, can’t contain it by yourself. Rather, it’s up to the those maintaining the web servers. But absolutely do pay attention, run updates, and look for notifications from service providers who are vulnerable to Bash. And if a company tells you to take action and change your password because their servers are affected, listen to them and get on that immediately.
What about Webroot Servers?
We took all the necessary precautions and upgraded all of our systems to the patched version. We can verify that none of our services are susceptible. You can find our official statement on this support section of our site.
We’ll be keeping a close watch to see how this story unfolds, but in the meantime, take the necessary steps to ensure you’re as protected as possible and install necessary updates as they become available.
5 million GMail accounts breached, and I was one of them
There is a bit of irony in this blog post, if you will. Over my time at Webroot, I have become a major advocate and vocal evangelist of digital security, from talking about major level breaches to sharing my experiences with dating-website scams. My work has focused around the education of those who will listen and read my work on the value of keeping one’s self safe at home, work, and while traveling. Like many others, I never thought (often quite ignorantly) that my information could get out there in a breach. And if it did, I was sure I would be still protected.
This morning, we found out that there was a breach of over 5 million Gmail accounts, all hosted in a plain text file on Russian hacker forums. Naturally, we wanted to see what the data was like, and there it was, plain as day for everyone to see. We started to look up our various accounts, and out of my whole team, I was the only one to appear. Right in front of me, on a list with 5 million other people, was my information. My heart sank a little, followed by the sort of nervous laugh I get at times all while I played through the major steps I had taken to protect myself prior, and what I needed to go change. Luckily, at the beginning of the year, I did my own security update and implemented two-factor authentication across all my major accounts, changed my standard passwords, and updated my security settings. And while we have covered these tips in the past (along with Tyler Moffitt’s security tips), there is no reason we shouldn’t all go back and just do a quick audit to make sure. In this case, there are two major steps I took to ensure my security online with this breach; changing my passwords and making certain that I have two-factor authentication turned on.
Change your passwords: Every three months is the average for a company for changing of passwords, often not allowing you to repeat for at least 10 passwords. This may be an annoyance, but with breaches like this occurring on a daily basis, it’s a necessary step that you should be following at home as well. It’s no longer simply about someone figuring your password out, but rather the idea that any level of breach can grab your standard password and e-mail address, and attempt it across multiple channels until success is found. Changing your password removes this ability. Need help figuring out a new password you can remember? Take your standard password and move one key left or right for each letter. The keystrokes will be similar and it will help product a difficult password. Remember, characters and numbers should be intermixed to increase the difficulty. Reminding yourself with a calendar note to change all your passwords on the same day every three months. I would also recommend looking into a password manager, such as the one included in Webroot SecureAnywhere™ Internet Security Complete for home users, to help with the difficult passwords you now have to remember.
Enable Two Factor Authentication: I have talked about this before (and shared links), and I cannot stress enough the importance of this level of security. With cell phones being at the ready in almost all aspects of our daily lives, this is one of the most convenient and easy layers to implement. By adding this layer, the service will authenticate any login attempt through an independent channel, allowing you to know if someone is attempting unauthorized access. Below are links to the sites listed above for their steps on enabling this step.
- Gmail: https://www.google.com/landing/2step/
- Amazon: http://aws.amazon.com/iam/details/mfa/
- PayPal: https://www.paypal.com/us/cgi-bin?cmd=xpt/Marketing_CommandDriven/securitycenter/PayPalSecurityKey-outside&bn_r=o
- Facebook: https://www.facebook.com/note.php?note_id=10150172618258920
- Twitter: https://blog.twitter.com/2013/getting-started-with-login-verification
While we are still unsure how the hacker was able to get all this information, it’s clear as day that it is out there, and because of that, vigilance is key. Just as you wouldn’t leave your credit cards laying around, you shouldn’t risk your passwords being out there either. Data is valuable, and the more private or financially focused it is, the more we need to take it seriously. So take these simple steps, get another layer of security established, and make it a habit to change passwords so you don’t become another name on the list as I did. In the mean time, you can check and see if your e-mail is apart of the breach by following this link: https://isleaked.com/en.php
Other helpful links:
- Google Security: https://www.google.com/settings/security
- Facebook Security: https://www.facebook.com/help/securitytips
- Twitter Security: https://support.twitter.com/articles/76036-safe-tweeting-the-basics
- Secure Password Generator: http://passwordsgenerator.net/
- Google Chrome Security Settings: https://support.google.com/chrome/answer/114836?hl=en
- Firefox Security Settings: https://support.mozilla.org/en-US/products/firefox/privacy-and-security
- Internet Explorer Security Settings: http://windows.microsoft.com/en-us/windows/change-internet-explorer-security-settings#1TC=windows-7
- Microsoft Outlook Two-step authentication: http://windows.microsoft.com/en-us/windows/two-step-verification-faq
- Google Two-Step authentication: https://support.google.com/a/answer/175197?hl=en
Apple’s Sept 9 Event: New (and larger) iPhones and (gasp), a Watch!
Well, September 9th is here, and the launch of Destiny, one of the most (if not the most) anticipated video games ever, isn’t the only major piece of news coming out of the tech world today.
You may have heard that one Cupertino fruit-logo’d tech company had an event today. And now the details of Apple’s next big(ger) things are official. Initial takeaway? They’re pretty in-line with the the rumors that have been swirling around for months now.
In other words, people got a lot of what they were expecting. Is that a good or bad thing? Depends on what camp you’re in. Probably.
Similar Phones, New Sizes
If you’re an Apple fan who’s only gripe was the small-by-today’s-smartphone-standards screen, your wish is (finally) Apple’s command. The company announced two new phones, each with a never before used (by Apple) size: the new iPhone 6 has a 4.7 inch screen while the new iPhone 6 Plus sports a 5.5 inch one. Yep, the iPhone will finally be competing in the phablet category.
(Source: ARS Technica)
The new devices are also thinner than the current 7.6 mm enclosure of the 5s, with the iPhone 6 measuring 6.9 mm and the iPhone 6 Plus coming in just slightly chubbier at 7.1 mm. To accompany these ‘gains’, Apple also introduces a new ‘Horizontal Mode’, which will help retain comfortable one-handed use and make everything within reach.
The glass now curves around the edges of the phones, but the screen isn’t the sapphire one many people expected, but rather incorporates “a slightly different design element”, according to CNET’s report. The phones’ power/lock button make a move from the top edge to the right spine.
The colors remain unchanged. You will be able to get the new devices in gold, silver, or space gray.
(Source: PC Mag)
What about the display? The regular 6 gets a 1334×750 resolution with 326 PPI (Pixels Per Inch) while the 6 Plus gets a slightly crisper 1920×1080 resolution with 401 PPI. Both iPhones sport Apple’s familiar ‘Retina Display’ (although it’s now being called ‘Retina HD’). While these numbers improve on the 1136×640 (326 PPI) display of the 5s, they still lag behind many of today’s higher-end Android devices, a few of which (LG G3 and the newly-announced Galaxy Note 4 and Note Edge) pack 2560×1440 displays.
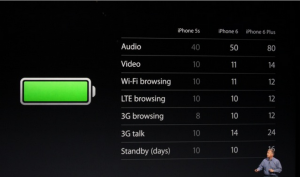
But pixels don’t always tell the whole story and it’s very difficult to tell the difference between 1080p and 1440p on such (relatively) small devices. That, and battery life typically suffers from a higher resolution. Speaking of…
The Internals
When it comes to battery life, Apple is claiming an improvement in battery life in both phones over the current 5s (see chart below)
(Source: ARS Technica)
The devices’ internal hardware gets a boost as well. The new iPhones are powered by Apple’s new A8 processor, which Apple says has 50% faster graphics and a 25% faster CPU. The transistor count has also been bumped up to 2 billion from the A7’s 1 billion. This should all lead to better efficiency and performance.
There’s also the M8 co-processor, which improves on the 5s’ co-processor and will assist the health-conscious iPhone users keep track of their activity and take better advantage of the iPhone’s fitness apps. It’ll also be handing the data coming from the new barometer sensor.
The phones also get upgraded LTE connectivity, bumping speeds up to 150Mbps. Wi-Fi speeds should also clock in at about three times faster than those of the 5s, thanks to Wi-Fi 802.11 support. VoLTE (Voice over LTE) and Wi-Fi calling are also now supported.
Camera
Updated rather than upgraded (if pixel count is your measurement), the camera in the iPhone 6 and iPhone 6 Plus retains its 8MP, but gets a new sensor with ‘Focus Pixels’ technology, which Apple claims uses DSLR-style phase detection autofocus, helping the new devices autofocus lock up to 2x faster than previous iPhones. Users will be able to record 30 and 60 FPS videos in 1080p and capture slow motion videos at 120 or 240 FPS, an improvement.
As far as image stabilization goes, the iPhone 6 gets digital stabilization, but you’ll have to purchase the bigger and more expensive (more on that later) 6 Plus if you want optical image stabilization.
If selfies are your thing, Apple also didn’t forget about its Face-Time camera (otherwise known as the front-facing camera), which receives a larger f/2.2 aperture plus a new sensor for better lighting and sharper image quality. Video capture remains at 720p and there’s also now a burst mode.
NFC/Apple Pay
(Source: Macworld)
Apple has resisted the NFC (Near Field Communication) push for years, but that no longer the case with the new iPhones. With the 6 and the 6 Plus, Apple not only added the protocol, but have also built their new Apple Pay payments system entirely for this cause. It works with the Passport app (as well as without it) and will finally allow users to use their new iPhone to purchase things. For more on Apple Pay, check out this Macworld article.
iOS 8
Apple announced that the new operating system will be available Wednesday, September 17th. For a detailed breakdown of the new features of iOS 8, check out this CNET article.
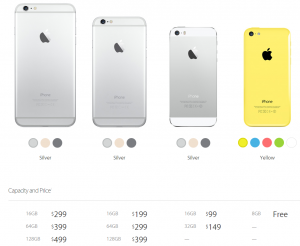
Pricing and Availability
The new iPhone 6 and 6 Plus will launch in eight countries on September 19th. Pre-orders begin on September 12th.
So far, Apple has only released US pricing, but, as you might expect, the new iPhones ain’t cheap. The iPhone 6 starts at $199 for the 16GB version. $299 will get you 64GB, and if you want the max 128 GB of storage, you’ll need to dish out $399. Tack on $100 across the board (for the same amount of storage) and voila, that’s how much the iPhone 6 plus will cost you. Yep, that means on-contract pricing for a 128 GB iPhone 6 Plus is a whopping $499!
In the US, the new iPhones will be available on AT&T, Verizon, T-mobile, Sprint, and US Cellular to start.
The other seven countries that get the September 19 launch are UK, Australia, Canada, France, Germany, Hong Kong, Japan, Puerto Rico, and Singapore.
This also means that the iPhone 5C’s price will drop to ‘Free’ and the iPhone 5S’s price goes down to $99 (for the 16 GB version).
(Source: Apple.com)
‘One More Thing’: The Apple Watch
Apple didn’t end with the iPhone 6 and 6 Plus reveal, however. It wouldn’t be an Apple event if they did, would it? As many people expected, they introduced a new wearable device, called the Apple Watch (interestingly not iWatch like most predicted).
(Source: CNET)
The Verge has a very visual ‘hands-on’ write up and you can read it in its entirety here. Nevertheless, here’s some basic info on Apple’s long-rumored entry into the wearables market:
- Will be available ‘Early 2015’ starting at $349
- Will come in three collections – all different versions (with different finishes) of the same watch. The Apple Watch Edition will be finished in 18K gold.
- Touch-screen (flexible Retina) display, digital crown, infrared LEDs, and photo diodes
- Runs on an S1 Processor
- Equipped with gyro accelerometer
- Has NFC
- You need an iPhone 5 or better to use it
Security
Many people forget that iPhones are not malware-proof. I won’t dive deep into this, but it’s important to keep your new devices protected, whether you’re an iPhone or Android user. We offer protection for both.
Concluding Thoughts
It will be interesting to see how consumers will react to the new iPhones. Many Android vs. Apple battles are already raging on in pretty much every comment section of every story written up on the iPhone 6 and 6 Plus.
The thing is, most Android and Apple users are already dedicated to their respective camps and I don’t think these new iPhones have enough revolutionary features that will lure many Android users away from their Google-powered machines, most of which already have the screen sizes Apple is finally embracing.
But because the 4.7 and 5.5 inch screens are a first for Apple, the real question comes down to the Apple fans themselves. Will the new screen sizes be the must-have addition many previous iPhone users were wishing for or will it alienate the fan base that loved Apple for offering a pocket-friendly premium smartphone?
For now, all we can do is wait and see.