 A new version of Trojan-Pushu is doing some interesting stuff to bypass captchas used by Microsoft’s Hotmail/Live.com/MSN webmail services in order to spam people with links to malicious Yahoo Groups pages.
A new version of Trojan-Pushu is doing some interesting stuff to bypass captchas used by Microsoft’s Hotmail/Live.com/MSN webmail services in order to spam people with links to malicious Yahoo Groups pages.
The three-year-old spy (known by a variety of other aliases, including Cutwail, Pushdo, Diehard, and Rabbit) has always been, primarily, a spam bot. In this case, however, the spy is not sending spam by connecting to open mail relays or more traditional means; It’s spamming through the Hotmail/Live.com Web mail interface. Most interestingly, during the course of the spam sessions, the spy apparently pulls down “audio captchas” and successfully sends back the correct response, which permits it to continue spamming.
Audio captchas are just what they sound like they are: A voice, often female, reads a sequence of 10 numbers in an artificially noisy background. The purpose is simple: to ensure that a human being, and not some automated process, is entering data into a form. Just as you would type in the scrambled-up letters from a captcha image to proceed, with an audio captcha you have to type the correct numbers from the recording, or the site won’t let you continue.
That doesn’t seem to be a problem for this Pushu variant. We’ve seen Trojans attempt to crack visual captchas a number of ways, including using optical character recognition; employing a mechanical turk service (where humans are paid fractions of a penny for each correctly entered captcha); or by prompting the victim him- or herself to enter captcha text, disguising the captcha form as some sort of Windows prompt. This is the first time I’ve heard of a Trojan attempt to crack the audio captcha, let alone succeed.
The sample we saw uses both the icon and the file properties of the free password manager application KeePass. But this is no password manager. Within about five seconds of execution, the application moved a copy of itself, named reader_s.exe, into the system32 folder and began making network connections.
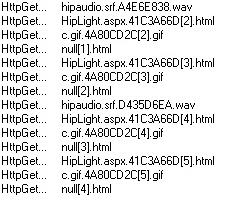
Initially, the file contacted four computers over the Internet that acted as command-and-control servers. Three of the four IP addresses were already on several blacklists; the fourth is a member of a range of IP addresses known to have been used in the past by the infamous Russian Business Network to engage in exactly these kinds of shenanigans. The Trojan retrieved instructions, and didn’t contact the CnC servers again. It began spamming less than three minutes after it was executed, and began querying for its first audio captcha almost a minute later.
In the case of Hotmail/Live.com, the audio captcha files are small WAV audio files with the file name hipaudio.srf. Listening to them forces you to concentrate, because the numbers are awash in noise, almost as if someone was reading them over the PA system in a noisy airport terminal. The cryptic messages are more reminiscent of the old, cold war-era shortwave radio number stations reputedly used by spy agencies.
In our tests of the samples we collected, the Trojan is able to send spam messages for a period of time before Live.com prompts the bot with a captcha form; The bot retrieves one of these WAV files from Microsoft’s servers, then returns an answer to the server after a pause of from three to ten seconds.
In one seven minute test period where I permitted the bot to operate freely, the bot demonstrated remarkable capability to bypass the audio captchas. In most cases, it was able to submit the correct answer within two tries, though in one instance, the bot tried six times before it could proceed, and once it gave the correct answer the first time. Once it submits the correct answer, the bot resumes sending its spam. In addition, the bot periodically logs out, then logs back in using a different user account, indicating that the operators of this botnet are trying to fly beneath the radar.
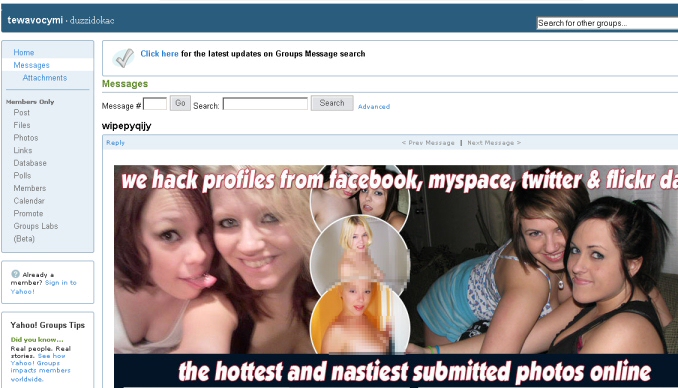
The spam emails themselves are short, written by someone who doesn’t have a strong grasp of English grammar. That’s putting it mildly, because they are hilariously bad. They’re just a line of text with a link to a Yahoo Groups page that looks like: http://groups.yahoo.com/group/(random ten-letter name)/message/1
The messages resemble somewhat ham-handed social engineering. Here’s a selection of some of the pickup lines we saw the lounge lizard use. I leave it as an exercise to the reader to make a determination as to how effective these would be.
God bless you my son. He wants you to look this hot photos right now!
The old friend of mine. You are looking so manhood on your delineations.
Mamma mia! your grandmother is doing so strange things here! Look at these delineations!
How could we be so stupid when we were foting our action at the love making time? Look Here!
Become more emancipated man with the most pretty girls of our site.
You look good in black and white photos. Keep posting such photos on facebook.
Are you fond of the girls you are looking at? Stop looking and take them.
How many hours did you spend out? You look very fit in your new pictures brother.
Stop talking about “this”. Visit our site and do not worry.
Nothing can be better than meeting a nice young girl and making love with her at night.
Is it really your photo? I do not believe in it! Prove it to me!
The Yahoo Groups pages changed every few hours. They all link back to something that calls itself the Hacked Blackbook, which claims that its pornographic pictures originate from hacked social network accounts.Apparently, it’s a “free signup” but you have to provide a bunch of personal and credit card details in order to do so. Yeah, I see what you did there, fraud guy.
Reliable sources who wish to remain nameless inform me that the photos posted on these spamvertised websites are actually amateur porn models and don’t come from “hacked profiles from Facebook, Myspace, Twitter & Flickr” as the spam ads claim.
Fortunately for our customers, Pushu is fairly rudimentary to find and remove. Without adding any additional detection, we were able to knock out this sample. Now that’s what I call looking manhood on your delineations!






















I believe this is this is a “crack”.
How can this be stopped.
I’m glad to see sites like this one around. Thanks
I just loved this blog. Here I found each and every content posted very nicely which is very understanding and useful as well.
I have never homeschooled. I can say I’m not totally against it. I can see the benefits if the parents are willing to work just as hard as the kids. I think it really depends on the situation. Some parents do a great job and others do a lousy job.