GDPR represents a massive paradigm shift for global businesses. Every organization that handles data belonging to European residents must now follow strict security guidelines and businesses are now subject to hefty fines if data breaches are not disclosed. Organizations around the world have been busy preparing to comply with these new regulations, but many internet users are unaware of how GDPR will impact them. While this new oversight enhances user privacy protection, its implementation also opens the door for GDPR-specific cyber threats.
Anyone with even the slightest online presence has been subject to a barrage of new terms and conditions released by companies concerning GDPR, which became effective on May 25, 2018. Criminals are taking advantage of this overwhelming surge of new terms of agreements to execute scams.
A phishing scam purporting to come from Apple is the most popular that we’ve seen. It declares that “For Your Safety, Access To Your Apple ID Has Been Restricted”, then prompts users to update account information before being allowed back in. This particular campaign was designed to capitalize on fatigue from the myriad of updated terms of agreement and privacy policy notifications internet users have encountered in the weeks leading up to GDPR, hoping to catch them off guard. The idea behind the scam is that potential victims are less alert and more likely to agree to and click through anything related to updated terms and conditions. Here’s what the phishing page looks like:
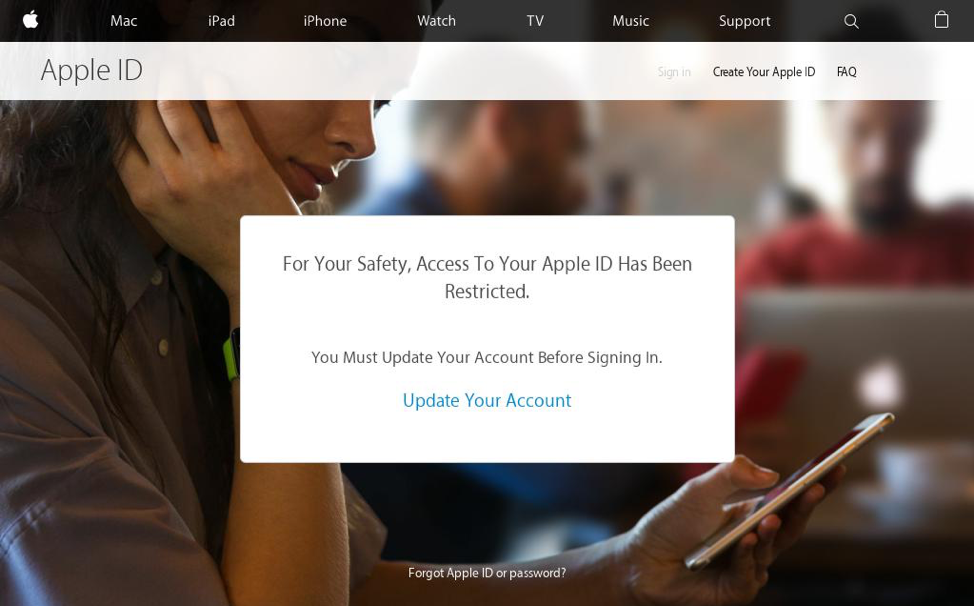
Source: hxxps://www.securitycentre-appleid.com [phishing URL]
When victims click “Update Your Account”, they’re then presented with a fake login page designed to capture their Apple ID credentials.
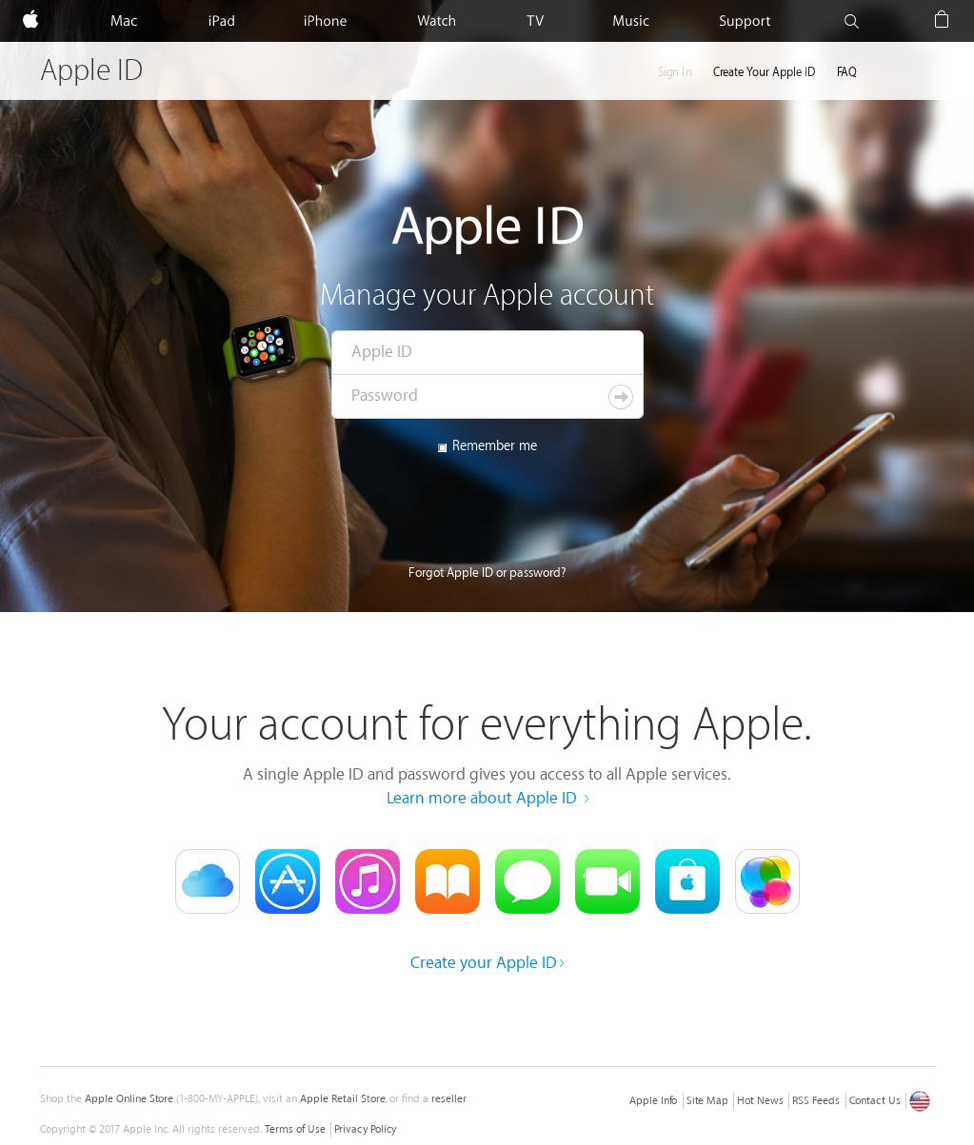
Source: hxxps://www.securitycentre-appleid.com/Locked.php [Phishing URL]
Targeted Ransomware
Beyond simple phishing scams, GDPR brings new pressure criminals can leverage concerning personal data that companies are responsible for. Targeted ransomware has become popular recently, especially through the RDP attack vector. Cybercriminals are now in a much better position to demand substantially larger ransoms when dealing with company data belonging to EU residents than before.
Were criminals to target an organization handling EU resident data, they’d be in a position to leverage a ransom amount closer to fines meted out under GDPR laws once they’ve breached and encrypted the data. We expect to see an increase in targeted ransomware hoping to exploit the hefty GDPR fine structure.
Another win for cybercriminals comes in the form of the recent change to the WHOIS lookup, made in response to GDPR data privacy restrictions. The Internet Corporation for Assigned Names and Numbers (ICANN), the organization that manages the global domain system, has removed crucial bits of data from public WHOIS lookups to comply with GDPR.
Before this change, when queries were made on domains using WHOIS lookup, information such as registrant’s name, address, email, and phone number was accessible. This proved invaluable when tracking malicious domains linked to malware campaigns. Now, with GDPR, that information will no longer be available publicly, giving cybercriminals another edge. ICANN has since filed a lawsuit seeking to clarify the law as it relates to WHOIS data collection, according to Threatpost.
GDPR Fails
We’ve also seen some unfortunate failures from legitimate companies sending emails trying to educate and inform their customers of GDPR-related changes—and actually violating the regulations while doing so.
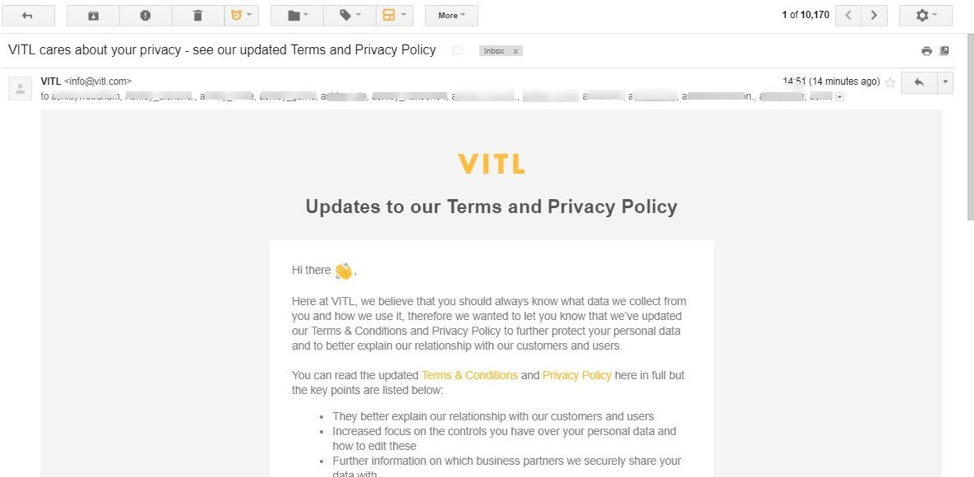
Source: @ashstronge on Twitter
In sending this email on blast to their contacts, the company above failed to hide email addresses, thereby sending their users’ contact information to everyone on their email list. A mistake like this may carry costly consequences under the EU’s new rules. It should serve as a reminder to businesses of all sizes– there’s a lot at stake when handling personal data. With only 42 percent of organizations in the U.S., U.K. and Australia reporting they are ready to comply with recent privacy regulations, ramping up information security safeguards will continue to be imperative in 2018.
Be on alert for scams related to GDPR. Interact carefully with the many privacy policy updates you’ve likely received in recent weeks. Remember to practice good cyber hygiene, and always double check website URLs whenever entering personal data.
What do you think about GDPR’s implications for the evolving threat landscape? Let us know in the comments below or join our Tech Talk discussion in the Webroot Community.






