When it comes to digital security, little is as important as knowing how to create a strong password. An ideal password is easy enough to remember so that it doesn’t need to be written down, yet complex enough to prevent someone else from guessing it. For many, this is a challenging and even frustrating experience, a delicate balancing act. However, there are a few techniques that can help you to reliably create strong passwords. The first thing to know is what passwords you should NEVER use.
SplashData, an online security company who’s “SplashID” software allows you to securely store your passwords, has recently released a list of the Worst Passwords of 2015. This list was compiled from more than 2 million passwords that were publicly leaked during the last year:
- 123456
- password
- 12345678
- qwerty
- 12345
- 123456789
- football
- 1234
- 1234567
- baseball
- welcome
- 1234567890
- abc123
- 111111
- 1qaz2wsx (first two columns of main keys on a standard keyboard)
- dragon
- master
- monkey
- letmein
- login
- princess
- qwertyuiop (top row of keys on a standard keyboard)
- solo
- passw0rd
- starwars
This is the fifth year that SplashData has released a Top 25 list, and many of the entries have been seen year after year. The passwords “123456” and “password” have been the top two entries since SplashData has started publishing an annual Top 25 list. However, due to the popularity of “Star Wars: The Force Awakens”, this is the first year that related passwords like “solo”, “princess”, and “starwars” have appeared on the list.
What we can take away from this list is that many people continue to put themselves at risk by using weak, easily guessed passwords. “We have seen an effort by many people to be more secure by adding characters to passwords, but if these longer passwords are based on simple patterns they will put you in just as much risk of having your identity stolen by hackers,” Morgan Slain, CEO of SplashData, said in a statement.
“As we see on the list, using common sports and pop culture terms is also a bad idea. We hope that with more publicity about how risky it is to use weak passwords, more people will take steps to strengthen their passwords and, most importantly, use different passwords for different websites.”
So, what can you do to ensure that your passwords are strong?
- Avoid using full words and names. Hackers regularly use “dictionary attacks” to guess passwords, and any word or name that is commonly known is considered unsafe to use.
- Create passwords or passphrases of twelve characters or more with mixed types of characters. A password longer than 12 characters, if created with the appropriate complexity, will be nearly impossible to guess quickly.
- Use a different password for each website you log into. If someone is able to discover your password for one site, they will not be able to use that same password to log into another site with your information.
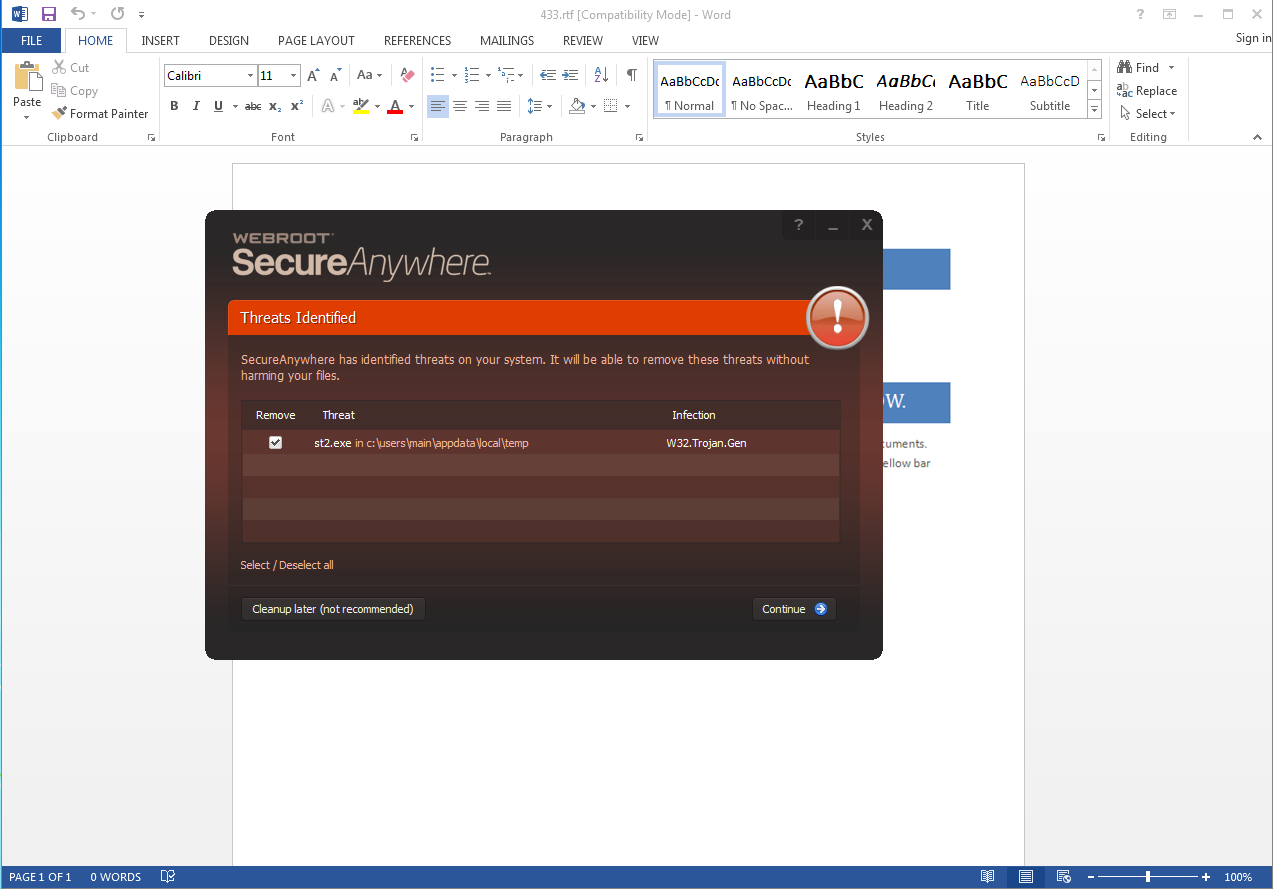
- Use a password manager such as LastPass or SplashID to organize and protect passwords, generate random passwords, and automatically log into websites. This is also a feature that is offered with some Webroot SecureAnywhere software packages.
- Test your password for complexity with a password checker, such as Password Meter.
To create a strong password, try using the “Letter/Number Substitution” technique, which generate seemingly random jumbles of letters and numbers that only you would remember. First, think of a phrase that you want to associate with the site or service you are setting up.
- Example: “testpassword” (DO NOT USE)
Next, substitute characters for some of the letters using numbers and special characters which resemble those letters.
- Example: “t3$9@S$w0rD” (DO NOT USE)
This example password is rated as 100% “Very Strong” using the Password Meter. By using this technique with even longer words in combination with numbers or special characters placed between the words, you can create passwords that will be nearly impossible to guess. With these tips in mind, you can ensure that your password won’t appear on next year’s list!