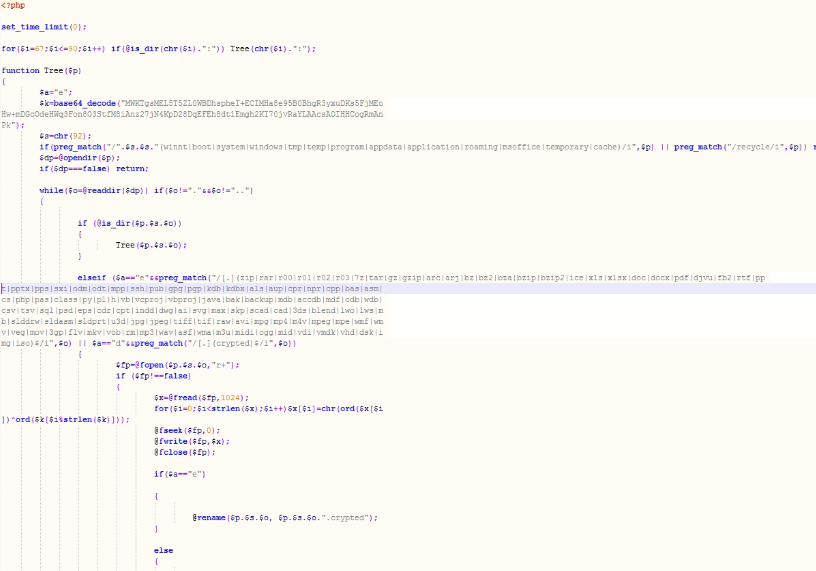
While ransomware has become a buzzword for some, cyber criminals have made it a lucrative business and one which they are constantly evolving. Each day, the Webroot BrightCloud® Threat Intelligence Platform monitors, classifies and scores 95% of the internet to discover 6,000 phishing sites and 80,000 variants of malware and PUAs.
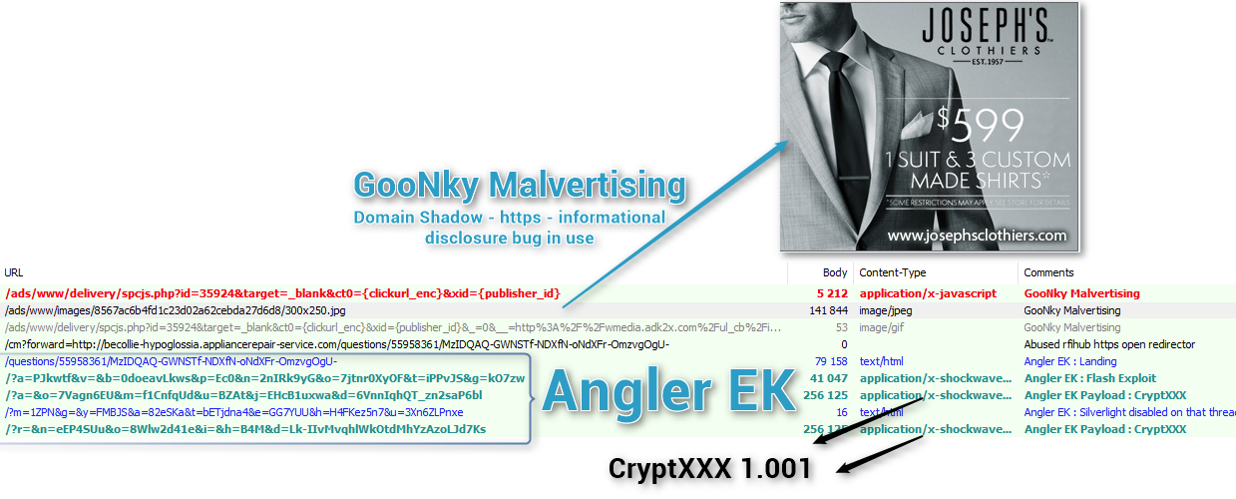
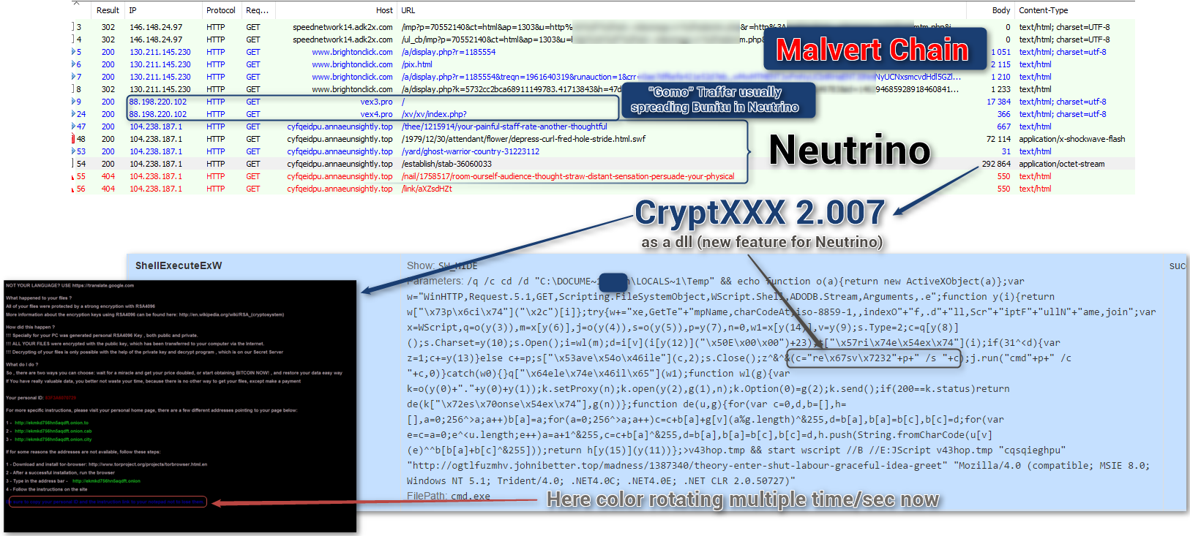
According to Webroot’s latest research, more than 97% of threats are unique to a single endpoint making traditional signature-based antivirus underprepared and ineffective in protecting businesses against today’s threat landscape. In this podcast, Tyler Moffitt, Senior Threat Research Analyst for Webroot, joins Ryan Morris, contributing editor for Penton Technology, to explain the newest and most challenging forms of ransomware, such as malvertising. In addition, they dive into the latest threat trends and arm MSPs with tested and actionable suggestions to help protect themselves and their customers from becoming another statistic.
Penton Technology Podcast with Tyler Moffitt – Ransomware – Part 1
Penton Technology Podcast with Tyler Moffitt – Ransomware – Part 2