Cryptographic Locker
It seems as though every few weeks we see a new encrypting ransomware variant. It’s not surprising either since the business model of ransoming files for money is tried and true. Whether it’s important work documents, treasured wedding pictures, or complete discographies of your favorite artists, everyone has valuable data they don’t want taken.
This is the last thing anyone wants to see.
This variant does bring some new features to the scene, but also fails at other lessons learnt by previous variants. Starting with the new features this variant will now just “delete” the files after encrypting them (it just hides them from you). This doesn’t add any more intangibility since they are encrypted with AES-128 anyway, but it does add a greater sense of loss and panic since all of your common data directories will appear to have been cleaned out. Another new feature is the constant raise in price every 24 hours. While price bumping was used on previous variants, this one doesn’t have a limit and will increase by .2 bitcoins (~$97) every 24 hours until you crack or make peace with this loss.
Where this variant falls short on overall volatility is in the failure to delete the VSS (Volume Shadow Service) so using tools like Shadow Explorer will work to retrieve your files and circumvent paying the ransom. As I’ve said in previous blogs I do expect issues like this to be fixed once this malware is adopted by more botnets for widespread distribution.
Webroot will catch this specific variant in real time before any encryption takes place. We’re always on the look out for more, but just in case of new zero day variants – remember that with encrypting ransomware the best protection is going to be a good backup solution. This can be either through the cloud or offline external storage. Keeping it up to date is key so as not to lose productivity. Webroot has backup features built into our product that allow you to have directories constantly synced to the cloud. If you were to get infected by a zero day variant of encrypting ransomware you can just restore your files back as we save a snapshot history for each of your files up to ten previous copies.
The Weekend of Nude Celebrity Selfies, iCloud, and How to Protect Your Personal Info
What do celebrities (mostly young and female), 4chan, hackers, Bitcoin, and iCloud have in common?
They’re all ingredients of a scandalous Labor Day Weekend, one that was filled with celebrity ‘skin’, outrage, confirmation (and denial)…and now an FBI investigation into the crazy incident that has everyone talking.
But is it the ultimate internet scandal or a sobering reality of the importance of safeguarding your content to reduce the risk of it being stolen? Both.
Before we go into that, however, in a nutshell (and in case you don’t know by now), here’s what happened:
On Sunday, users of the often-controversial message-board 4chan, saw a large trove of nude celebrity pics posted on the /b/ (also known as the ‘random’) thread. The extensive list of celebrity ‘victims’ included Jennifer Lawrence, Kate Upton, Mary Elizabeth Winstead, Kirsten Dunst, Ariana Grande, Kim Kardashian, Victoria Justice and many others. Afterwards, the photos quickly spread to Reddit.
Then the reactions started to come in.
While Jennifer Lawrence didn’t respond herself, here was her spokesman’s reaction (which confirmed the pictures’ legitimacy): “This is a flagrant violation of privacy. The authorities have been contacted and will prosecute anyone who posts the stolen photos of Jennifer Lawrence.”
(Source: Washington Post)
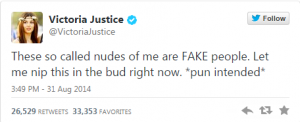
Not surprisingly, many of the celebrities were quick to respond themselves, taking to Twitter, some denying the legitimacy of the photos while others admitting that they were real. Below are some of the celebrity reactions on Twitter.
Actress and singer Victoria Justice took the humorous route as she called ‘her’ pics ‘fake’:
On the other end of the spectrum, actress Mary Elizabeth Winstead took a very serious tone as she confirmed that her stolen photos were real:
And here was Kirsten Dunst’s reaction:
But why is Dunst ‘thanking’ iCloud? And who was behind this ‘leak’? Million-dollar questions. Let’s start with the ‘who’.
It’s still uncertain exactly who the perpetrator (or perpetrators) are. According to reports, 4chan apparently hosted a shady, unorganized ‘black market’ for celebrity photos where users would sell, buy and/or swap these photos and often boast of their ‘collection’. And while some Redditors have put the blame on Bryan Hamade, a 27-year-old man from Georgia, he is ‘vehemently denying’ the claims (he did an interview with BuzzFeed yesterday morning). You can read it here (warning: could have some NSFW content).
Now back to the iCloud bit…
Some 4chan hackers claimed that they exploited a previously-unknown flaw in Apple’s iCloud, more specifically the photos, contacts, and music syncing feature.
After ‘more than 40 hours’ of investigation, however, Apple is claiming that its systems aren’t the ones to blame for the breach, saying that this was a targeted attack on the celebrities rather than a widespread breach. Here is part of their statement: “None of the cases we have investigated has resulted from any breach in any of Apple’s systems including iCloud or Find My iPhone.” For more on Apple’s take, you can read the CNET report here.
Also, as mentioned before, the FBI is now involved. The following is a comment from FBI spokesperson Laura Eimeiller regarding the matter: “[The FBI is] aware of the allegations concerning computer intrusions and the unlawful release of material involving high profile individuals, and is addressing the matter. Any further comment would be inappropriate at this time.”
As this story continues to develop, many of you are probably wondering (and worrying) about the security of your own, personal (and possibly sensitive) information. Some people are arguing that the easiest way to avoid these scandals would be to not take nude selfies in the first place, (NYT Colunmnist Nick Bilton and comedian/actor Ricky Gervais both made similar jokes on Twitter about it – see below), while others are calling that ‘gross advice’ (read Amanda Hess’ Slate article here).
Gervais ended up deleting his Tweet, but here’s what he said originally: “Celebrities, make it harder for hackers to get nude pics of you from your computer by not putting nude pics of yourself on your computer.”
Here was Bilton’s Tweet (he later apologized):
A major takeaway, regardless of your opinion on this matter (or whether you snap revealing pics of yourself on your iPhone), is that many people take internet and mobile security for granted and don’t do enough to protect their personal information.
Here are some general tips safeguarding tips that will help reduce the risk of losing or unwillingly exposing your personal info:
- Malware often targets user log-in details. Use security software to protect yourself, particularly one with a secure web browser. We here at Webroot have found that over 50% of internet traffic stems from mobile devices, and web browsing is the most likely source of attacks.
- Have a different secure password for each place you store important data – pictures, documents, etc. is critical – and change the password often (at least once every few months). This will keep you a step ahead of cyber criminals.
- Watch out for phishing attacks! Never click on a link in an email except from a trusted party. Never enter your login information just because a company sends you an email with a link to a page that looks like the real company page – it could be a fake phishing page.
- Use passwords that are difficult for automated computer programs to crack. Use phrases or even whole short sentences like CowboysNeverbeat49ers!! Change it often.
- Pet names, birth dates, and simple number combinations are not secure passwords, nor a replacement for real-time protection software and basic security practices.
And one tip for Apple iCloud users – Apple is saying that its internal systems aren’t to blame and they’re probably telling the truth. But the fact that iCloud wasn’t breached isn’t an excuse to use a weak password or have a simple (or honest) answer for your security question. Remember, the easier it is for you to log in to an account, the easier it else for somebody else to do so, too.
Oh, an one last thing. Just because you delete a photo from your iPhone doesn’t mean it’s automatically deleted from iCloud (or wherever else you may have stored it). Stay secure!
A Primer on BitCoin
Editors Note: One day, we found ourselves discussing the security of bitcoin, only to realize that many readers may not truly understand the digital currency. Luckily, a team member’s father, Eoin Meehan, is well versed in the subject and has submitted a guest blog to help everyone understand this popular form of cryptocurrency.

Bitcoin is a cryptocurrency, reportedly designed by Satoshi Nakamoto in 2008. To fully understand how it works we must look at how “ordinary” currencies work.
To quote Sheldon Cooper “It was a warm, summer’s evening in ancient Greece …”
Well, no, we don’t need to go back THAT far.
Currencies evolved as people used bits of precious metals as tokens to exchange for goods and services, rather than using OTHER goods and services (which is barter). Gold and silver served this purpose well because they were
- Rare metals and durable
- Elements, so it was easy to see if they had been tampered with and
- Acceptable by everyone who traded with them – a common medium of exchange
Eventually someone realised that physically moving large amounts of precious metals was both cumbersome and risky, and came up with the idea of a paper token denoting ownership of a piece of gold that was held somewhere secure. The paper token said that whoever held this piece of paper could go to where the gold was stored and demand it to be handed over (which is why notes used to have “I promise to pay the bearer on demand the sum of x pounds” – its x pounds worth of gold).
Everyone accepted the concept of the paper representing the gold and so it took on the value of the gold itself. This became known as the “Gold Standard”
Then someone realised that because everyone was happy with the pieces of paper representing “value” there was really no need to keep tons of gold in a secure location, in case somebody actually turned up and asked for their pound of gold. And that’s what we have today with currencies such as the Euro.
So today, a currency has to have three attributes to be a currency:
- The tokens are rare or controlled.
- The tokens representing that value are very difficult to generate and replicate
- A value accepted and agreed by everyone who uses it – a common medium of exchange
Bitcoins are tokens that can be exchanged between parties in a transaction, just like physical notes. There are no physical bitcoins, so the transfer happens just like transferring money between bank accounts.
These “bank accounts” do not exist in any institution, but as “wallets” on electronic devices. These wallets are encrypted files on a PC, laptop, tablet or smartphone, managed by a Bitcoin-compliant application. The Bitcoin standard uses public/private key pairs to authorise and authenticate transfers between wallets, and each wallet has its own private/public key pair.
The transfer happens across a peer-to-peer network similar to Tor or Bittorrent.
But what happens if Alice sends 5 Bitcoins (BTCs) to Bob, and ALSO tries to send the SAME 5 BTCs to Carol?
To stop this happening there is a data construct called the block-chain which is held on all nodes participating in the Bitcoin network. The blockchain is an encrypted list of all transactions that have been “approved” in the Bitcoin universe, and acts as a shared ledger. Once Alice sends her 5 BTCs to Bob, those 5 BTCs are logged in the blockchain as a transfer between Alice’s wallet and Bob’s wallet. If Alice tries to send the SAME BTC’s again, the network will reject the transaction, as the BTCs are already “accounted for”
So how are the transactions added and “approved” to the blockchain? This is done by special nodes called “miners”. Miners have two functions – to authorise transactions and to generate new Bitcoins (hence the name).
When Alice sends Bob the 5 BTCs, the transaction is broadcast the Bitcoin network, and the transaction is marked pending (not complete). Miners listen for these broadcasts and begin working on adding the transaction to the blockchain.
The process of adding the transaction to the blockchain is computationally intensive. The miner has to apply a hash-function to the block-chain + the new block to generate a hash. Normally for hashing purposes we can just stop there. One computationally intensive process to create a number. But Bitcoin applies a ceiling such that the hash created must be equal-to or less-than the ceiling. This means the miner must recalculate the hash many times until it returns an acceptable value. If two miners return values, then the lower one “wins”. Once the hash is created and accepted, working backwards to see if this hash is valid for this block is trivial. So verification is easy.
This ceiling value is also how the network “self-regulates”. The more miners there are connected, the lower that ceiling value goes (the harder the task).
Once a miner successfully calculates the hash value, the block-chain is updated and the wallet applications notified. (Because of the intensity of the calculations, there is about 10 minutes between the transaction and its confirmation).
Now we come to the second function of the miner. As a reward for calculating the hash, the miner is allowed create a certain number of new bitcoins, and these are recorded as part of the verified transaction. They are then transferred to the miner’s appropriate wallet and “come into circulation”.
The number of bitcoins a miner is allowed create is a function of the total number of bitcoins that will ever be allowed. Currently its 25 BTCs. For every 210,000 blocks added to the blockchain, this number is halved. So Bitcoins become harder to generate the more that are in circulation. There is an arbitrary limit in the protocol that there will only ever be 21,000,000 bitcoins.
So one question you might ask is – what happens when all bitcoins are mined? What incentive is there for miners to keep, eh, mining? The protocol considers this. In each block record in the block-chain, a miner can charge a fee or commission for calculating the hash and verifying the transaction. So miners will still be mining bitcoins for their owners except they will be paid by other members to verify transactions.
Once Bitcoin is accepted a medium of exchange each BC has a value. This value can then be “matched” with real-world currencies just like a foreign-exchange transaction. There are a number of electronic exchanges set up which will perform this forex transaction … for a fee of course! The most notable one is probably is MtGox.
Sony’s PSN Network Haymaker’d by DDoS Attack; Exec’s Plane Grounded Over Bomb Threat
Sony had a rough weekend. And not just Sony; last weekend wasn’t the best time to be a gamer. Here’s the skinny…
Early yesterday morning, Sony’s PlayStation Network (PSN for short) was hit with a massive Distributed Denial of Service (DDoS) attack, causing it to crash temporarily and hamper online play for many PlayStation gamers.
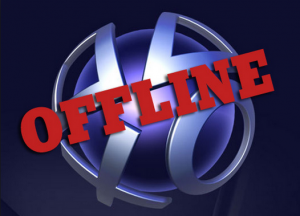
Sony Online Entertainment President John Smedley quickly took to Twitter to let users know about the attack before tweeting that he’d be offline for three hours as he flew back to San Diego from Dallas on AA Flight #362. Well, not long after the plane took off, someone tweeted to American Airlines that “it was receiving reports that [Sony Online Entertainment CEO John Smedley]’s plane #362 from DFW to SAN has explosives on-board, please look into this.” That, plus a handful of references to the 9/11 attacks.
The plane was quickly diverted to Phoenix, where it would be checked for explosives (thankfully, there were none to be found as far as anyone knows).
Was the DDoS attack connected to the bomb scare? At first, it sounded like it. The tie? ‘Lizard Squad’.
Who? Let’s start at the beginning, Aka, last Saturday.
According to an ARS Technica report:
“It all started Saturday, when a group going by the handle “Lizard Squad” tweeted links to a number of prominent Twitch streamers, directing followers to target DDoS attacks at servers for Blizzard and League of Legends maker Riot Games. The group’s sophomoric MO: demand that the streamers write “LIZARD SQUAD” on their forehead in marker to get their games back online.”
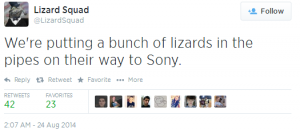
But what’s the tie to Sony’s PSN going down? @LizardSquad started taking aim at Sony early Sunday morning, coinciding with the outage, and posting the following:
But now, Lizard Squad’s responsibility for the initial PSN attacks is in question. According to numerous reports, a hacker going by the handle @FamedGod is taking credit for the attack. He’s tweeted ‘proof’ (see below) and posted a on YouTube (link below).
PSN Vulnerability (YouTube Video)
While the origin of the attack remains a mystery (we’ll be keeping eye on the story as new details emerge), it’s now clear that Sony wasn’t the only target of the DDoS attacks. As mentioned in the aforementioned ARS Technica piece, Blizzard (more specifically its Battle.net game services) and Riot Games servers were affected. Xbox Live and Grinding Gear’s ‘Path of Exile’ were also reportedly hit.
Now what?
As far as the DDoS attacks are concerned, Blizzard tweeted 19 hours ago, saying that “services appear to be stabilizing”… while PSN and Xbox Live seem to be back to their normal, pre-DDoS states.
What about the bomb scare? According to USA Today, an American Airlines spokesperson says the FBI is investigating the issue.
ZeroLocker
Recently in the news we saw FireEye and Fox-IT provide the ability to decrypt files encrypted by older crpytolocker variants. They used the command and control servers seized by the FBI during operation Tovar. Since they have access to those RSA keys they essentially have the password required for every single file encrypted by a Cryptolocker variant that used Evgeniy Bogachev’s botnet. That is a major portion of the traditional red GUI cryptolocker that became famous. Any previous victims from these variants that still have encrypted files left on their machine should be able to decrypt them with ease. All they have to do is upload a single encrypted file to this webpage and their server will email you your RSA key. Then you can just download their tool (dubbed “DeCryptolocker”) and input the key and it will decrypt all files that are still encrypted. Sadly, anyone that was hit with different variants of encrypting ransomware are still out of luck.
However, since the emergence of their tool to decrypt files for free, there has been a new encrypting ransomware going around that aims at scamming you into thinking this is a similar helpful tool – except that it demands something all scams do….payment.
Presenting ZeroLocker
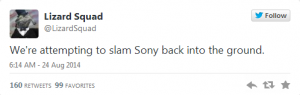
At least they have a 100% guarantee…
This newest edition to the ever popular business model that is encrypting ransomware doesn’t really have many improvements over the others we’ve already seen. Using Bitcoin for payment is standard now. This variant doesn’t show the GUI untill all encryption is completed and the computer is suddenly restarted. Upon restart this window is presented and threatens that you will lose all your files if you close or remove it. The payment structure is right where industry average is – PAINFUL. This specific variant we analyzed does not delete the VSS (Volume Shadow Service) and you can get all your files back by using programs like Shadow Explorer. Once again I expect issues like this to be fixed once this malware is adopted by more botnets for widespread distribution.
Webroot will catch this specific variant in real time before any encryption takes place. We’re always on the look out for more, but just in case of new zero day variants – remember that with encrypting ransomware the best protection is going to be a good backup solution. This can be either through the cloud or offline external storage. Keeping it up to date is key so as not to lose productivity. Webroot has backup features built into our product that allow you to have directories constantly synced to the cloud. If you were to get infected by a zero day variant of encrypting ransomware you can just restore your files back as we save a snapshot history for each of your files up to ten previous copies.
8 Tips to Stay Safe Online
Yesterday, the New York Times published an exclusive story on what many are stating to be the largest series of hacks ever, all revealed by Hold Security in their latest report. With a report of over 1.2 billion unique username-password combinations and over 500 million e-mail addressed amassed by a Russian hacker group dubbed CyberVol (vol is Russian for thief). While the reactions among the security industry are mixed, with some researchers raising a few questions of the masterwork behind the hack, the story does bring to the public’s attention the necessity of strong, personal, online security policies for all aspects of the connected life.
As our researchers have shown in the past, gathering a collection of username and passwords can be easier than many think, with many scraping programs being sold on the deep-web market to the highest bidders. And while some companies, including Hold Security, are offering paid solutions to help detect and monitor if their accounts have been breached, this does not change the fact that the first layer of security begins at the user.
8 tips to help you stay safe and secure on the internet
- Use two-factor authentication whenever possible. Two-factor authentication adds another layer of security when logging into a website, be it e-mail, banking, or other websites. Some websites, such as Google, will text you a code when you login to verify your identity, while others have small devices that you can carry around to generate the code. Authenticator apps are also available on all major smartphone platforms. Other types of two-factor authentication do exist as well, so look in the settings of your banking, shopping, and e-mail hosts for the option.
- Signup for login notifications. This security layer is often used in place of two-factor authentication, including by websites such as Facebook. If your account is accessed from an unfamiliar location, a notification is sent via e-mail, app, or text-message to the account holder. This is a great layer of security that offers you on-the-go protection. This feature, if offered, can usually be found in the security settings of the website, such as banking and social media, you are accessing.
- Use a secure password. We have all signed up for some website with a basic password, thinking there is no way that someone would want to hack our account. But that may not be the case. Setting an easy password on one website often leads to that password being used across many websites. The easier you make it for a thief to brute-force access your account, the more likely you are to have your other accounts hacked. By establishing a mixture of characters, numbers, and letters into a password, recommended to be 10 characters or more, you add a high level of difficulty for any brute-force password theft. Password managers like the one included in our Internet Security Plus and Complete antivirus programs can help make managing this easier.
- Change your passwords regularly. There is a reason your office requires regular password changes for your e-mail. Even if your password is compromised, by changing it regularly across all your accounts, you remove the chance of your account being accessed. A pro-tip would be to set a reminder for every 90 days on your calendar with a link to all your accounts settings pages. It makes it easiest to click through and make the changes regularly.
- Only access your accounts from secure locations. It might only be 30 seconds of access to your bank account on that free WiFi at the coffee shop, but if the network has been compromised, that is more than enough time to collect all the data needed for a thief. While the convenience factor is there, if you must access the accounts, you might want to look into a VPN (Virtual Private Network) to ensure an encrypted connection to your home or work network.
- HTTPS access. In most browsers and information heavy websites, there is a way to force a HTTPS connection when available. This connection adds another level of encrypted security when logging in, making it even more difficult for data thieves to gather your information when logging in. To check if you are on a HTTPS connection, look for a padlock in the URL bar in the browser or check the URL itself for it to begin with HTTPS.
- Increase junk filtering and avoid clicking through on e-mails. You just received an e-mail letting you know that you have a new deposit pending and need to login and verify. Many phishing schemes start with something looking very innocent and official, but lead unassuming users to websites designed to collect the information direct from you. If you receive an e-mail from one of the account-holding websites, open a new tab and go direct to the website instead of clicking the links provided. It adds only a few seconds to the access, but keeps you out of any legit-looking phishing websites. Most legitimate services will never ask you for your login credentials, so make sure to avoid giving out this information. By increasing your level of junk filtering with your e-mail client as well, many of these e-mails will be caught before making it to your inbox.
- Use an up-to-date security program. Ensure you have the most up-to-date version and have the correct security settings enabled. Security AV programs are designed to keep the malicious files such as keyloggers and data-miners off your computer and the user protected. This direct layer of security ensures your devices, from phones to tablets to computers, are all protected when you are downloading and accessing files. Note that some programs, such as Webroot SecureAnywhere, are always up-to-date and require no further action from the user.
While the threats to online accounts are out there, the tips to staying safe can help you stay protected and utilize features often already available by the companies and their websites, and most without costing you additional money. These internet safety tips should help ensure your security online while still providing the convenience online access offers.
Helpful links:
- Google Security: https://www.google.com/settings/security
- Facebook Security: https://www.facebook.com/help/securitytips
- Twitter Security: https://support.twitter.com/articles/76036-safe-tweeting-the-basics
- Secure Password Generator: http://passwordsgenerator.net/
- Google Chrome Security Settings: https://support.google.com/chrome/answer/114836?hl=en
- Firefox Security Settings: https://support.mozilla.org/en-US/products/firefox/privacy-and-security
- Internet Explorer Security Settings: http://windows.microsoft.com/en-us/windows/change-internet-explorer-security-settings#1TC=windows-7
- Microsoft Outlook Two-step authentication: http://windows.microsoft.com/en-us/windows/two-step-verification-faq
- Google Two-Step authentication: https://support.google.com/a/answer/175197?hl=en
A Look at PC Gamer Security

In the new study on security and PC gamers, Webroot found that many gamers sacrifice their protection to maximize system performance and leave themselves vulnerable to phishing attacks and gaming-focused malware. The study also provides tips for protecting gaming credentials and safeguarding against phishing attacks.
Webroot PC Gamer Security Study Findings:
- 47% experienced an online attack with 55% of the attacks impacting system performance.
- 35% of PC gamers choose not to use security or rely on free clean-up tools.
- “Does not slow down system performance” ranked among the most important security program characteristic to gamers and Webroot has the first antivirus for PC gamers without system impact.
- Trojans, Phishing, and Rootkits ranked as the top attacks against PC gamers.
- The top source for information about Internet security were from forums and fellow gamers.
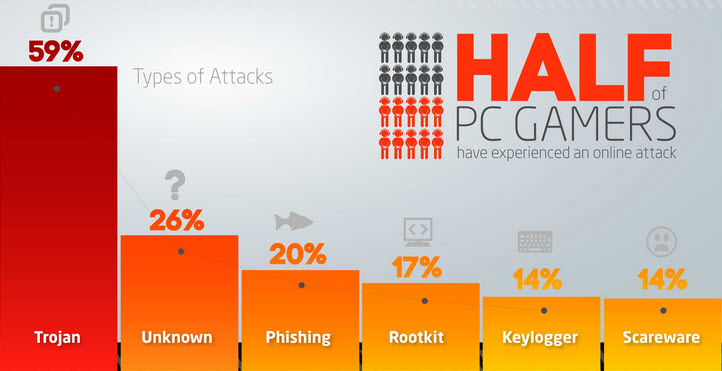
The survey was conducted during E3 2014 and was based on the responses gathered from over 1,200 PC gamers. The conclusion was that one third of PC gamers do not use a security program while gaming, although 47% have experienced a malware or phishing attack.
“We understand the high expectations that gamers have of their systems, and the frustration they have had with traditional antivirus programs. But the desire for performance can’t be at the expense of protection – there’s too much to lose,” said Mike Malloy, executive vice president of products and strategy at Webroot. “We believe by following some basic best practices and using a cloud-based security program that is very light on system resources, such as Webroot SecureAnywhere Gamer Edition, PC users don’t have to choose between performance and protection.”
Running a gaming system without traditional antivirus security can improve gameplay performance, but it leaves gamers vulnerable to identity theft and online attacks that can jeopardize both their real and in-game lives. This is why Webroot created the first cloud-based antivirus for PC gamers and developed a list of tips for staying safe online.
Tips for Gaming Securely:
- Use browser-based URL filtering.
- Deploy anti-phishing detection.
- Avoid public Wi-Fi and use a cloud-based anti-malware program.
To read the full press release, please click here.
If you’d like to view or download the infographic on the report, you can do so by clicking here.
Critroni/Onion – Newest Addition to Encrypting Ransomware
In my last blog post about a week ago, I talked about how Cryptolocker and the like are not dead and we will continue to see more of them in action. It’s a successful “business model” and I don’t see it going away anytime soon. Not even a few days after my post a new encrypting ransomware emerged. This one even targets Russians!
Presenting Critroni (aka. Onion)
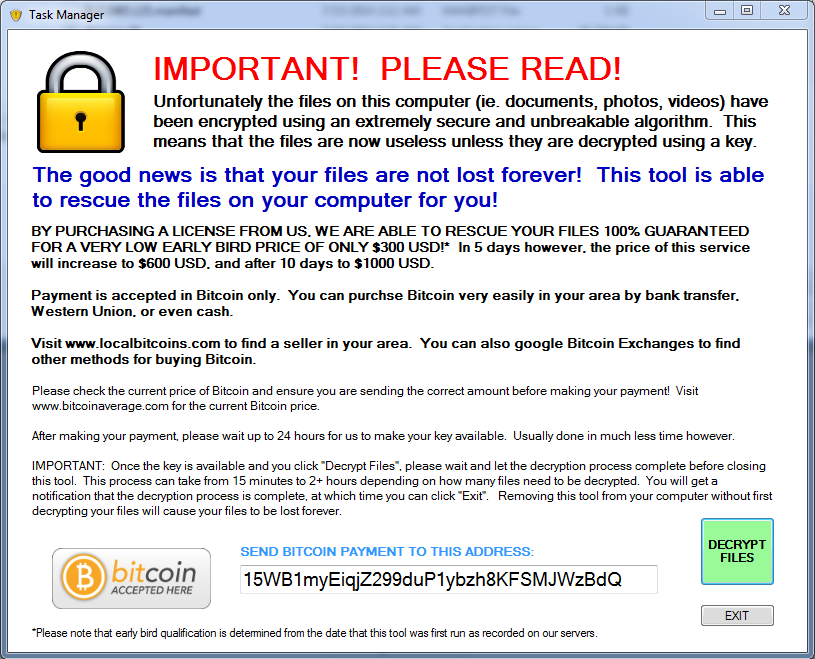
This newest edition of encrypting ransomware uses the same tactics of contemporary variants including: paying through anonymous tor, using Bitcoin as the currency, changing the background, dropping instructions in common directories on how to pay the scam. Some upgrades that are new to the encrypting ransomware scene are logging the entire directory list of files that were encrypted. They store this list in your documents folder for your convenience come decryption time (how nice of them).
The ransom amount scales with how many files are encrypted. My specific encryption only wanted “.2 Bitcoin (about 24USD)” Please note that the exchange rate displayed by the malware is extremely wrong and .2 Bitcoin is about $120.
This specific variant we analyzed does not delete the VSS (Volume Shadow Service) and you can get all your files back by using programs like Shadow Explorer. I expect that once this malware goes into widespread distribution for the US and UK that “issues” like this will get fixed and the price will rise to around .5 BTC (around $300) on average. Webroot will catch this specific variant in real time before any encryption takes place. We’re always on the look out for more, but just in case of new zero day variants – remember that with encrypting ransomware the best protection is going to be a good backup solution. This can be either through the cloud or offline external storage. Keeping it up to date is key so as not to lose productivity. Webroot has backup features built into our product that allow you to have directories constantly synced to the cloud. If you were to get infected by a zero day variant of encrypting ransomware you can just restore your files back as we save a snapshot history for each of your files up to ten previous copies.
Please note there are variations in the naming of this file, including Onion and Critroni.A.
Cryptolocker is not dead
Recently in the news the FBI filed a status report updating on the court-authorized measures to neutralize GameOver Zeus and Cryptolocker. While the report states that “all or nearly all” of the active computers infected with GameOver Zeus have been liberated from the criminals’ control, they also stated that Cryptolocker is “effectively non-functional and unable to encrypt newly infected computers.” Their reasoning for this is that Cryptolocker has been neutralized by the disruption and cannot communicate with the command and control servers to receive instructions or send RSA keys after encryption. Read more here
While seizing the majority of the GameOver Zeus Botnets from the suspected “mastermind” Evgeniy Bogachev was a big impact to the number of computers infected with GameOver Zeus – about a 31 percent decrease, it’s a very bold claim to state that Cryptolocker has been “neutralized”. The reason why this claim should be scrutinized is because it is only the samples dropped on victims computers that communicated to those specific servers seized that are no longer a threat. All samples currently being deployed by different botnets that communicate to different command and control servers are unaffected by this siege – the majority of encrypting ransomware. Although Evgeniy Bogachev and his group had control of a major chunk of zeus botnets and command and control servers that deployed cryptolocker, it was certainly not all or even the majority of zeus botnets in existence. Most malware authors spread their samples through botnets that they either accumulated themselves (Evgeniy), or just rent time on a botnet from someone like Evgeniy (most common). So now that Evgeniy’s servers are seized, malware authors are just going to rent from some of the many other botnets out there that are still for lease.
Here are some pictures of samples that we’ve encountered that are still hard at work at infecting users.
All of these work in almost exactly the same way as the infamous traditional cryptolocker we’ve all seen, but they have some improvements. First is that there is no GUI and instead just background changes and texts instructions in every directory that was encrypted. Second is that you no longer pay using a moneypak key in the GUI, but instead you have to install tor or another layered encryption browser to pay them securely and directly. This allows malware authors to skip money mules and increase the percent of profits. The best way to stay protected by attacks like this is to utilize backups to either the cloud or offline external storage. Webroot has backup features built into our product that allow you to have directories constantly synced to the cloud. If you were to get infected by a zero day variant of encrypting ransomware you can just restore your files back as we save a snapshot history for each of your files up to ten previous copies.
So while this is a great win on behalf of the FBI, it’s very bold to claim that cryptolocker is now dead. A better way to put it would be that Evgeniy M. Bogachev’s brand of cryptolocker and anyone who purchased time on his botnet is now useless.
New Study Reveals Disparities Between Corporate Mobile Security Policies and BYOD Practice
In the new BYOD Security Report conducted by Webroot through first-of-its-kind research, Webroot examined the use and security of personal mobile devices in the work environment, looking at the prevalence of employee-owned devices. The initial survey, conducted in late 2013, explored the prevalence of employee-owned devices, how they are being secured, and employee concerns regarding company-mandated security programs. The second survey, conducted in March 2014, looked at how IT managers view the risk of employee-owned devices, the prevalence of formal mobile security policies, and the extent to which employee input is included in developing BYOD policies.
Pulling from that report are some interesting key facts and findings, including:
- Although 98% of employers have a security policy in place for mobile access to corporate data, 21% allow employee access with no security at all.
- Over 60% of IT managers surveyed reported the use of personal devices by their employees and 58% indicated they were ‘very’ or ‘extremely’ concerned about the security risk from this practice.
- Most employee devices are lacking real security with only 19% installing a full security app and 64% of employees limited to using only the security features that came with their devices.
- Over 60% of employers indicated they seek employee input on mobile device security policies, but over 60% also said employee preference has little or no influence on mobile security decisions.
- Top concerns from employees regarding a company-mandated security app include employer access to personal data, personal data being wiped by an employer, and employers tracking the location of the device. Other concerns included impact on device performance and battery consumption.
- 46% of employees using personal devices said they would stop using their devices for business purposes if their employer mandated installation of a specific security app.
All in all, the report shows that there are striking signs that many employers and employees do not take necessary steps to ensure the protection of the corporate data on their personal devices. While this is a weakness in the systems now, tools such as Webroot Business Endpoint Protection and SecureAnywhere Business Mobile Protection do exist to help implement security policies, and when paired with new, forward-thinking BYOD policies, can prove to be effective in keeping the corporate data secure.
A successful Gartner Summit for Webroot
 Webroot, the market leader in cloud-based, real-time Internet threat detection, recently returned from the 20th annual Gartner Security and Risk Management Summit in National Harbor, Maryland. Attended by many of the world’s top business and IT professionals in industries ranging from finance to information technology to government, the focus of this year’s conference was enablement of an organization to move forward towards its objectives, while ensuring security and protection. The show’s theme at this year’s conference, “Smart Risk: Balancing Security and Opportunity”, summarized the challenges that many large companies are experiencing today, as they work to ensure the safeguarding of their information without slowing down the company’s productivity.
Webroot, the market leader in cloud-based, real-time Internet threat detection, recently returned from the 20th annual Gartner Security and Risk Management Summit in National Harbor, Maryland. Attended by many of the world’s top business and IT professionals in industries ranging from finance to information technology to government, the focus of this year’s conference was enablement of an organization to move forward towards its objectives, while ensuring security and protection. The show’s theme at this year’s conference, “Smart Risk: Balancing Security and Opportunity”, summarized the challenges that many large companies are experiencing today, as they work to ensure the safeguarding of their information without slowing down the company’s productivity.
As a ‘Premier Sponsor’, Webroot attended the Gartner Summit to introduce the next generation threat intelligence services for enterprises, BrightCloud Security Services for Enterprise, which collects and analyzes threat intelligence across multiple vectors – IP, URL, File and Application – from a massive network of nearly 35 million users protected by Webroot endpoint security solutions as well as Webroot technology partners. The team was also on-hand to demonstrate Webroot SecureAnywhere Business-Endpoint Protection, which recently was updated with enhanced management capabilities to help protect large, complex network environments.
With a busy booth during the three days of exhibit time, there was a great deal of interest in Webroot’s Threat Intelligence Server and BrightCloud Services as well as the SecureAnywhere Endpoint Protection solution. The solutions that were introduced aligned well with two key areas that the security community is interested in – namely finding better protection for their endpoints and using external threat intelligence to make their current devices smarter and optimized for more rapid incident response – as well as fitting in with the conference’s overall theme.
While at the event, Webroot was also part of various security discussions and presentations, including two sessions where CISO’s talked endpoint protection and threat intelligence. Webroot’s Dave Dufour and Chip Witt both presented on real-time intelligence gathering, and Webroot CTO Hal Lonas presented on the difference between threat data and threat intelligence. Mike Malloy, VP of Products and Strategy, also gave a talk on ‘the death of traditional antivirus’, a theme that forms the foundation of the Webroot security product lineup.
Thanks largely to a combination of a strong security-focused presence as well as a seamless merging of security goals between attendees and Webroot’s product offerings, the company’s presence at this year’s 2014 Gartner Security and Risk Management Summit was a major success. Webroot is already planning on similar attendance at the coming Japanese and APAC Gartner summits to continue to drive the momentum forward.
A peek inside the online romance scam.
 Online dating can be rough, and no matter how many safeguards are in place in the multiple legitimate dating websites out there, the scammers are getting around the blocks and still luring in potential victims. While the reports of these types of scams are out there (even with copy and paste examples of the e-mails used), people still fall for the scams every day. In this particular case, it was my profile on eHarmony that was targeted, and this is my recount of it.
Online dating can be rough, and no matter how many safeguards are in place in the multiple legitimate dating websites out there, the scammers are getting around the blocks and still luring in potential victims. While the reports of these types of scams are out there (even with copy and paste examples of the e-mails used), people still fall for the scams every day. In this particular case, it was my profile on eHarmony that was targeted, and this is my recount of it.
It started with a potential match; a profile with a collection of tasteful photos of a beautiful woman, not too ‘out there’, but a face that stood out from the crowd. The profile was fairly complete, with a few of the smaller-scale questions not answered. Overall, the profile initially raised no suspicion for me. So, I started the song and dance that is the eHarmony way, and back and forth we went with questions and such. That is, until the last stage when the match sent over a cryptic message of not being able to communicate via the system and that I should e-mail her. And up went the red flag.
Now, most systems out there allow communication up to a certain point, and in this case, eHarmony was on a free communication week, and even if it hadn’t been, we had not reached that final ‘free’ part yet. Assuming that many of the companies have basic language and text scanned in their internal mail systems, it can be supposed that the person on the other end was avoiding being flagged.
So with this e-mail in hand (my inbox), I decided to see how far this rabbit hole went. Using a non-personal e-mail address that I setup for mailing lists, I contacted my match with a basic re-introduction and waited. A few hours later, I received back an incredibly long, detailed e-mail with a few photos attached. The e-mail was not well written, and the local geographic locations mentioned in it did not make sense in the description. At this point, I was 100% sure it was a scam and decided to reverse image search the photos, which lead me to a model out of Australia, and then searched the generic line of text to find over 78,000 results showing almost exact copies of the e-mail I had received.
A quick reply back lead to an even longer response from the scammer, again using photos from the model’s profile page and the same content found on many scam reporting websites. But this time, I was being asked for money, as ‘she’ was stuck in London, unable to get home. Conveniently, there was already a bank account setup for me to transfer money. At this point, I had what I needed for this write-up, and so I marked the account as ‘spam’ and reported the profile to the eHarmony team.
So what can we learn from this little experience? Well, a few things. Despite the safeguards in place to help protect those looking for a relationship online, the protection is not perfect, and users need to be educated. Here are a few tips for you to help spot a potential scammer:
- Claims of being from the United States but currently visiting overseas
- Making claims of wanting to fly back to meet, but unable to do so because of work or a tragic incident.
- Wanting to leave a dating site immediately and use personal e-mail addresses to communicate.
- Irregular use of the English language, improper use of slang, and over punctuation.
- Hinting at or asking for money to help secure travel back ‘home’
- Professionally taken photographs that look straight-out of a runway magazine
Remember, you will never know who is on the other side of that screen until you meet them. Use safe and cautious measures, never give out personal information, and be aware of the tricks being used on the digital daters of today.