Cryptolocker Ransomware and what you need to know
The basics
The Ransomware known as Cryptolocker has been prominent in the media lately, and one that we’re asked about often. Ransomware in general is nothing new, we have been seeing ransomware that hijacked your desktop wallpaper demanding payment for several years now, but while the older ransomware was rather easily removed, Cryptolocker has taken ransomware to a new level. What Cryptolocker does is encrypt files (primarily document files but also image files and other file types) on your computer and any network drives that computer has access to using a very strong encryption method and then demands payment with a 72-hour time period in order to get the files decrypted. This works by using public key encryption and there is no way to decrypt the encrypted files without paying the ransom for the private key.
What you can do help prevent getting infected in the first place and minimize the damage
Run up-to-date security software such as Webroot SecureAnywhere. As with any malware, blocking it in the first place is the best defense.
Since Crypolocker is typically installed through malicious email attachments, familiarize yourself (and your employees) with how to identify potentially malicious and suspicious emails. This will not just help prevent against Cryptolocker, this is a delivery method commonly used by all flavors of malware.
Isolate an infected computer from any network drives at the first sign of infection. Unplug the network cable or disable the wireless connection. This is especially important in Enterprise (Business) environments in order to help prevent files on network drives from being encrypted.
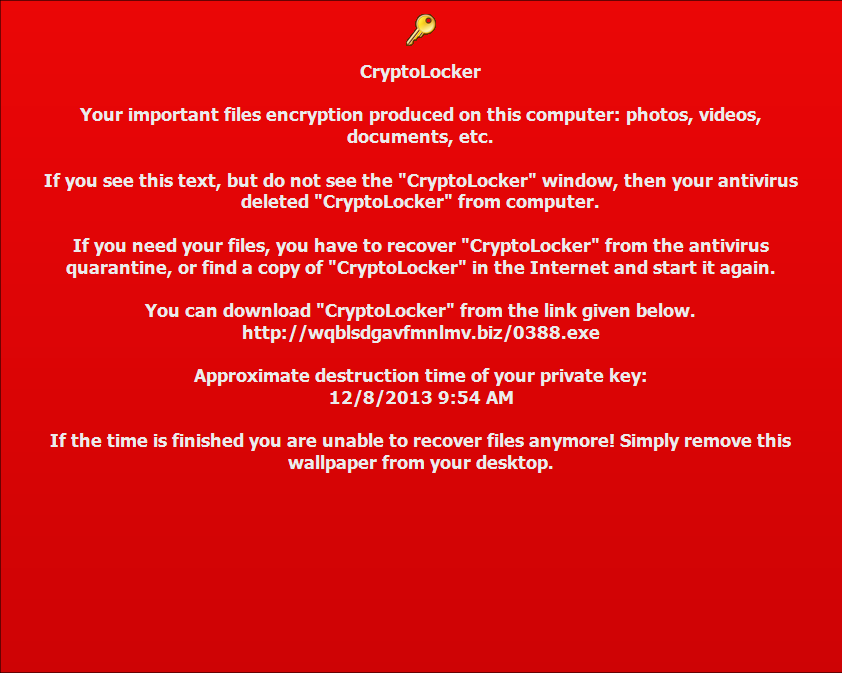
Some Cryptolocker variants also change your desktop background with additional information in case your antivirus has removed the Cryptolocker files and you still wish to pay the ransom to recover your files.
Backup, backup, backup. You should be backing up your essential files anyway, and you could look at Cryptolocker as a brutal reminder why backups are so essential. Off-site or cloud backup is highly recommended, as off-site backup has long been an essential part of any Disaster Recovery Plan. If you are a home user backing up to a removable drive, be sure to disconnect it when not in use since Cryptolocker can encrypt your backup files on the external drive.
Other Webroot resources on Cryptolocker
ThreatVlog Episode 11: Staying safe while doing holiday shopping online
In this edition of the Webroot ThreatVlog, Grayson Milbourne talks about the threats that exist online in the holiday shopping craze. As more and more money is spent online, criminals are becoming more skilled at stealing all sorts of personal information, from credit card numbers to identifying credentials. As with all shopping, common sense is necessary, and with the tips and tricks provided, you will be even more protected while finding that perfect gift online.
http://youtu.be/ayzVT0NQngU
Compromised legitimate Web sites expose users to malicious Java/Symbian/Android “Browser Updates”
We’ve just intercepted a currently active malicious campaign, relying on redirectors placed at compromised/hacked legitimate Web sites, for the purpose of hijacking the legitimate traffic and directly exposing it to multi mobile OS based malicious/fraudulent content. In this particular case, a bogus “Browser Update“, which in reality is a premium rate SMS malware.
Today’s “massive” password breach: a Webroot perspective
First, this is not a blog about a big corporate breach, or a massive new discovery. Rather, the researchers at Trustwave gained access to a botnet controller interface (the C&C element of a botnet) known as Pony and revealed the data within. Not surprisingly, as the vast majority of botnets target user credentials, this controller had a good deal of data related to passwords. While 2 million passwords might seem like a lot, it is really a drop in the bucket compared to many recent breaches. Think about Adobe who lost a minimum of 28 million, but is rumored to be closer to 130 million, login credentials to their services. Combine this with the fact that many people use the same password for all online accounts.
Commercial Windows-based compromised Web shells management application spotted in the wild
For years, whenever I needed a fresh sample of pharmaceutical scams, I always sampled the Web sites of major educational institutions, where a thriving ecosystem relying on compromised Web shells, continues to enjoy the high page ranks of the affected Web sites for blackhat SEO (search engine optimization) purposes. How are cybercriminals managing these campaigns? What type of tools and tactics do they use? In a cybercrime ecosystem that has logically migrated to Web-based platforms for a variety of reasons over the last couple of years, there are still those who’re keeping it old school, by releasing host-based DIY cybercrime-friendly applications. In this post, I’ll discuss a commercially available Windows-based compromised/hacked Web shells management application.
Cybercrime-friendly VPN service provider pitches itself as being ‘recommended by Edward Snowden’
We’ve recently spotted a multi-hop Russian cybercrime-friendly VPN service provider — ad featured not syndicated at a well known cybercrime-friendly community — that is relying on fake celebrity endorsement on its way to attract new customers, in this particular case, it’s pitching itself as being recommended by ex-NSA contractor Edward Snowden. How have anonymization tactics evolved over the last couple of years? Have the bad guys been ‘innovating’ on their way to cover the malicious/fraudulent online activity orchestrated by them? Let’d discuss some of the current trends in this ever-green market segment within the cybercrime ecosystem.
Fake ‘October’s Billing Address Code’ (BAC) form themed spam campaign leads to malware
Have you received a casual-sounding email enticing you into signing a Billing Address Code (BAC) form for October, in order for the Payroll Manager to proceed with the transaction? Based on our statistics, tens of thousands of users received these malicious spam emails over the last 24 hours, with the cybercriminal(s) behind them clearly interested in expanding the size of their botnet through good old fashioned ‘casual social engineering’ campaigns.
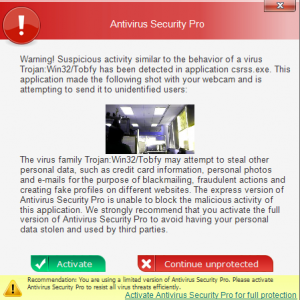
Rogue antivirus that takes webcam pictures of you
Recently we heard of a rogue fake antivirus that takes screenshots and webcam images in an attempt to further scare you into succumbing to it’s scam. We gathered a sample and sure enough, given some time it will indeed use the webcam and take a picture of what’s in front of the camera at that time. This variant is called “Antivirus Security Pro” and it’s as nasty as you can get.
The rogue locks down any of the Advanced Boot Options: Safe Mode, Safe mode with Networking, Safe mode with Command prompt, directory services restore mode, ect. As soon as these are picked the computer will just restart back into normal mode where all executables are flagged as malicious. If you don’t purchase the scam in a few minutes it will take a picture with the web cam and then warn you that [insert name of good process].exe is “malicious” and attempting to send it to unidentified users. This is a really impressive step in social engineering to scare people and I’m sure has increased the percentage of people who pay out to the scam.
However, this is false and there is no trace of the webcam images being sent anywhere. The only network traffic this Rogue has is during initial drop to download all of its components.
Removal
If you have Webroot SecureAnywhere installed then not to worry, this virus should be blocked in real time as soon as it is written to your hard drive; the only notification you’ll receive is a notice that it was quarantined.
However, removing this virus once it has infected you is a little trickier without the comforts of the safe modes. Those of you that try system restore, you’ll notice that this virus disables it. All the file does is disable System Restore. It does not delete any restore points so you can just turn it back on and restore to a previous point. To turn on System restore: Click Start > Right click computer > select properties > Click System protection > Select your OS Drive (Typically C:) > Click Configure > Check “Restore system settings and previous version of files.” Please note that once you restore to a previous point only the registry entries are going to be removed, so although the virus no longer starts up when your computer does, you will still have to manually delete the files.
Location of Files:
%CommonAppData%\”random name”\
%CommonAppData%\”random name”\DD1
%CommonAppData%\”random name”\”random name”.exe
%CommonAppData%\”random name”\”random name”.exe.manifest
%CommonAppData%\”random name”\”random name”.ico
%CommonAppData%\”random name”\”random name”kassgxDq.in
%CommonAppData%\”random name”\”random name”kassgxDq.lg
%CommonAppData% = C:\Documents and Settings\All Users\Application Data\ in Windows XP and C:\ProgramData\ in Vista/7/8
Webroot support is always more than happy to help with removal and any questions regarding infections.
Webroot SecureAnywhere users are proactively protected from these threats.
Fake ‘MMS Gallery’ notifications impersonate T-Mobile U.K, expose users to malware
Over the last two months, we’ve been closely monitoring — and proactively protecting from — the malicious campaigns launched by cybercriminals who are no strangers to the concept of social engineering topic rotation. Their purpose is to extend a campaign’s life cycle, or to generally increase a botnet’s infected population by spamming out tens of thousands of fake emails, exposing users to malicious software. The most recent campaign launched by the same cybercriminal(s), is once again impersonating T-Mobile U.K in an attempt to trick mobile users into thinking that they’ve received a legitimate MMS Gallery notification. In reality though, once the attachment is executed, the victim’s PC will automatically join the botnet operated by the cybercriminal(s) behind the campaign, ultimately undermining the confidentiality and integrity of the host.
ThreatVlog Episode 10: Mobile security tips
In this edition of the Webroot ThreatVlog, Grayson Milbourne talks about ways to keep your mobile device secure from the physical aspect. As our lives become more and more mobile focused, with an increasing amount of private information being stored on tablets and phones, it is always smart to remain vigilant to possible security breaches direct into the phone.
http://youtu.be/v2v-TUOxaQ0
Cybercriminals impersonate HSBC through fake ‘payment e-Advice’ themed emails, expose users to malware
HSBC customers, watch what you execute on your PCs. A circulating malicious spam campaign attempts to socially engineer you into thinking that you’ve received a legitimate ‘payment e-Advice’. In reality, once you execute the attachment, your PC automatically joins the botnet operated by the cybercriminal(s) behind the campaign.
Fake WhatsApp ‘Voice Message Notification’ themed emails expose users to malware
We’ve just intercepted a currently circulating malicious spam campaign impersonating WhatsApp — yet again — in an attempt to trick its users into thinking that they’ve received a voice mail. Once socially engineered users execute the malicious attachment found in the fake emails, their PCs automatically join the botnet operated by the cybercriminal(s) behind the campaign.