![]() Last week, Activision/Blizzard released a long-anticipated patch for its immensely popular game, World of Warcraft. While I don’t play this game, a number of our Threat Researchers do, and they’ve been on the lookout for shenanigans. Curtis Fechner found a doozy.
Last week, Activision/Blizzard released a long-anticipated patch for its immensely popular game, World of Warcraft. While I don’t play this game, a number of our Threat Researchers do, and they’ve been on the lookout for shenanigans. Curtis Fechner found a doozy.
The update comprises a major overhaul of many core systems within the game, affecting the graphics engine, game rules, player abilities, and also the interface. Many players use downloadable, player-created add-ons to further customize the appearance of the user interface; Patches as comprehensive as this one mean that many of the old add-ons simply won’t work until the add-on’s creator releases a new version.
So this week’s rush to patch the game and update some add-ons led to some interesting news. One of the add-ons Curtis uses is something called RatingBuster, written by a player who goes by the name WhiteTooth. The add-on, available from a number of locations, typically comes in the form of a .zip archive and contains several plain text files (called LUA files). But earlier this year, someone registered the domain name ratingbuster.org and began serving Trojans from this legitimate looking Website instead of the RatingBuster add-on.
This fake RatingBuster comes in the form of an executable file named rbv1.4.9.exe — running unknown executables is a big no-no most WoW players know to avoid. This particular executable is a self-extracting RAR archive, which utilities like WinRAR can easily unpack. Inside the archive is another file, a single executable named bot.exe (22794 bytes, MD5: 6831c35e6d19ea0a1e1e9e346368b3e3). This is our malware installer, stored inside the other installer.
Once run, bot.exe spends a few moments dropping some files into the Temp directory on the computer. One of the files is a packed version of the Windows core operating system component, kernel32.dll. Another file is the actual malware, a DLL file with a .txt file extension. Once bot.exe initializes this second DLL file (14090 bytes, MD5: b67f9b94836174f94e73440947067c1d), it deletes itself.
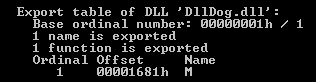
A registry key loads the DLL every time the computer reboots. When loaded, the DLL hooks into every running program on the infected computer, so you can’t just delete it. It uses a different filename each time bot.exe is run, but the naming convention is always six numbers followed by the .txt extension. The DLL’s internal name is DllDog.
The worst part of this stupid Trojan is that even though it contains WoW add-ons, it doesn’t even install the add-on most WoW players would have downloaded this installer to get.
Even the domain is a joke. Registered in February, 2010, ratingbuster.org’s WHOIS registration information indicates the site’s owner is from Scottsdale, China. Yeah, I didn’t know there was a Scottsdale in China, either. The falsified WHOIS data also incorrectly claims the domain is the property of a legitimate WoW fansite, curse.com. However, Curse’s site was registered in the US, while ratingbuster.org was registered using a registrar named Xiamen ChinaSource Internet Service Co., Ltd.
Seeing as the malicious domain was registered in Curse’s name, using Curse’s email address, I think the ultimate payback would be if Curse seized the domain and blackholed its DNS. What’s the criminal who registered the domain going to do, call the Chinese cyberpolice about his crimeware site getting shut down by its legitimately registered owner?
Both bot.exe and its DLL payload have very low AV detection rates. We’ve created a new definition to deal with the likes of scumbag game phishers such as this one. Not only will we block the ratingbuster.org domain from now on, but we can also easily remove the infection — we’re calling it Trojan-PWS-DllDog — from the computer of anyone infected.
If you don’t have a copy of our product, and are technically savvy enough to work in the Windows registry, simply browse to
HKEY_CURRENT_USERsoftwaremicrosoftwindowscurrentversionrun
and delete the value named “configuring” before you reboot the computer. When it starts back up, browse to your Temp folder and delete its entire contents. Don’t forget to back up your entire registry and make a System Restore point before you start, just in case you do something that renders your computer unbootable.
And if you suspect you’ve been duped into installing DllDog, once your machine is malware-free, change your WoW password and the passwords you use for any gaming forums or message boards. You might also consider getting one of the Blizzard Authenticators, because all the cool kids are carrying around two-factor authentication tokens these days, and it can keep your account from being stolen.