Small and medium-size business (SMB) leaders have a lot on their minds. The looming recession and inflation have created financial uncertainty. Meanwhile, the global rise in sophisticated ransomware threats and geo-political tensions are escalating cyber threats.
With so many factors and pressures at play, how are SMBs navigating this challenging business landscape while fighting back against cybercriminals?
Insight from OpenText Security Solutions’ 2022 Global Ransomware SMB Survey sheds light on security priorities, concerns and posture. Feedback from SMBs across multiple industries and countries confirm security teams and the C-suite are worried about increasingly sophisticated and relentless attacks.
Ransomware is a top concern for SMBs:
An overwhelming majority (88%) of SMBs indicated they are concerned or extremely concerned about an attack impacting their businesses. This worry is heightened by increasing geopolitical tensions. In fact, more than half (52%) of respondents now feel more at risk of suffering a ransomware attack due to these unfolding events.
SMBs’ ransomware concerns are already becoming a reality. Nearly half (46%) of SMBs have experienced a ransomware attack. Meanwhile, 66% of respondents are not confident or only somewhat confident that they can fend off a ransomware attack. Budget constraints and small security teams were cited as the primary roadblocks.
Despite concern, security awareness training is infrequent:
The vast majority of SMBs believe a successful ransom attack is the result of someone clicking on a malicious link or opening an email attachment. Yet despite this knowledge of users as the preferred attack surface, many SMBs (based on action) don’t view their employees as a first line of defense.
Sixty-seven percent of SMBs conduct security awareness training twice a year or less. Of these SMBs, 31% conduct security awareness trainings only once a year; 10% only if an employee fails a phishing test.
Fear of small security budgets getting smaller:
Sixty-seven percent of SMBs spend less than $50,000 annually on cybersecurity. While 59% reported plans to increase their security budget in 2023, 57% fear inflation will lead to a change in plans resulting in budget cuts.
SMB security teams are spread thin; MSPs are an appealing option:
The majority (68%) of SMBs have fewer than five people on their security team. To help alleviate resource constraints, more than half (58%) of respondents use external security management support. In the future, 65% of SMBs that don’t currently use a managed services provider (MSP) for their security needs would consider doing so.
Fighting more, with less
Adversaries have become increasingly sophisticated and relentless as the surface area of attacks only grows. Meanwhile, fear of looming budget cuts impacting already over-stretched security teams put SMBs in a vulnerable position.
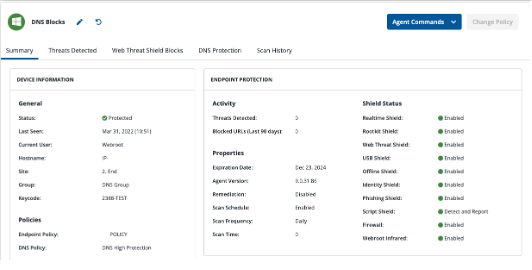
Ongoing education and awareness of new attack vectors and defense against common channels such as email are critical for achieving a cyber resilience posture. Monthly phishing simulations are a great way to keep users current and accountable. A multi-layered approach that includes email security, DNS filtering, endpoint protection, and backup and recovery is essential to mitigating risk and exposure from attacks.
To learn more, go to: https://www.opentext.com/products/security-cloud