In today’s digital world, passwords have become a necessary part of life. But even though you use them for almost everything you do online, you probably don’t give them the thought they truly deserve. May 1, 2025, is World Password Day, a reminder that passwords are the unsung heroes of cybersecurity, the first line of defense for all your sensitive personal data. This annual event encourages you to level up your password game and strengthen your online defenses. World Password Day is more relevant than ever in today’s evolving threat landscape.
Data breaches are on the rise, and according to the 2024 Verizon Data Breach Investigations Report, a staggering 81% of them are linked to weak or compromised passwords. The bottom line? If you’re still relying on “Fluffy123”, you could be putting your personal information at risk. Let’s explore password-based attacks, and some steps you can take to lock down your logins, once and for all.
Threats to your passwords
Managing all your passwords can be a hassle. They’re easy to forget and hard to keep track of, so people tend to use and reuse simple passwords they can remember. But here’s the issue – cybercriminals are getting smarter and their attacks are only getting more sophisticated. If a scammer gains access to your personal details, they can create havoc with your finances and cause you stress for years to come. In the past, brute force attacks were the go-to method, which involved simply using trial and error to crack passwords. Today, hackers use much more complex methods – here are a few examples.
- Password phishing: In a phishing attack, scammers will use emails, phone calls, or texts to pose as trusted businesses and service providers. They may send you a fake invoice to pay. They might offer you an amazing deal on an upgraded service. Sometimes they threaten to cut off a service if you don’t respond immediately. The goal is to trick you into giving up your username and password so they can access your data and steal your money.
- Credential stuffing: Once hackers have your login details, they often try what’s called credential stuffing – using your stolen credentials (username and password combinations) to try and break into your other accounts. Why does this work so often? Because more than two in three people admit they reuse passwords across multiple accounts.
- Malware: Infostealer malware can be used by hackers in the background to steal your personal information including your passwords. Once the malware is on your device it can search your web browsers, email clients, digital wallets, files, applications, etc. looking for sensitive information. They can even look for old forms you filled out with passwords, record your keyboard strokes, and take screenshots of your computer dashboard. The malware then sends this information back to hackers’ servers, sometimes within seconds. Hackers can use this type of malware for large attacks as seen by the targeted attack on Snowflake customers.
Password security checklist
- Create strong passwords
Longer is stronger: Aim for passwords that are at least 16 characters long. Research shows this number of characters takes exponentially longer to crack.
Difficulty matters: “12345” may be an easy password to remember, but it isn’t going to keep the cybercriminals away. Create a unique mix of uppercase, lowercase, numbers, and symbols for each password.
Be unpredictable: Avoid using obvious patterns and personal details that will be easy for hackers to figure out. This means no street addresses or phone numbers, and especially no personal details you might be sharing on social media.
Did you know? More than 50% of people admit to using familiar names for their passwords, such as their kid’s name or their pet’s name. 15% said they use their own first name in their passwords! - Change reused passwords
If you’re reusing the same password across accounts, it’s time for a refresh. All it takes is one compromised account for a hacker to potentially unlock dozens more. Start with your most sensitive accounts, such as banking, email, and healthcare and update those first.
Did you know? According to a study by Forbes Advisor, on average, people reuse the same password for at least four accounts. - Use multi-factor authentication
Even if a hacker obtains your password, you can still stop them in their tracks by adding a second layer of security to your login process. Multi-factor authentication (MFA) includes things like one-time codes sent to your phone or scans of biometric features, such as your face or fingerprints.
Did You Know? Using MFA can stop over 99% of account compromise attacks. - Consider using passphrases or passkeys
These are two alternatives to passwords that you might want to consider.
- A passphrase is a string of unrelated words that’s easy to recall and tough to crack. For example, something nonsensical like “FancyGoldEmuDancing “ will be hard for a hacker to guess, but it might be easier for you to memorize than a string of numbers and symbols.
- A passkey is an authentication method that uses biometric data, like facial recognition or a fingerprint. It can also use a swipe pattern (a three-by-three grid of dots) or a PIN. A passkey is used across all your devices, creating a password-free login.
Did you know? Not only does signing in with a passkey make your data much more secure, it’s also three times faster than using a conventional
password.
- A passphrase is a string of unrelated words that’s easy to recall and tough to crack. For example, something nonsensical like “FancyGoldEmuDancing “ will be hard for a hacker to guess, but it might be easier for you to memorize than a string of numbers and symbols.
- Use a password manager
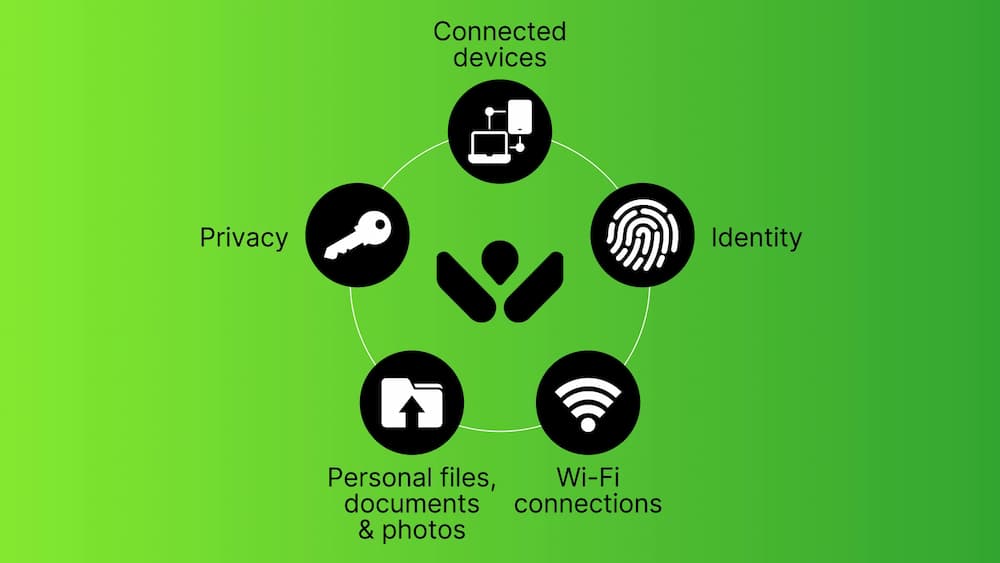
Password managers are tools that make your life easier by doing the hard work for you. By automatically generating and storing your strong passwords, they reduce the risk of recycled or forgotten logins and provide secure access across all your devices. Webroot solutions include password managers and much more, including features like real-time phishing detection to prevent credential theft.
Did you know? Users who rely on password managers are less likely to experience identity theft or credential theft than those who don’t. - Protect your devices
Antivirus software scans detect and defend against any virus or malicious program like malware, trojans, adware and more that might cause damage to your devices. Webroot products offer robust antivirus protection that continuously scours the internet to identify and block the latest threats.
Did you know? Hackers are moving away from browser-based attacks and embedding malicious software into everyday files like documents, installers and media. More than 50% of all consumer malware now enters through downloads and desktop.
Never forget that your passwords are the very foundation of your digital defense strategy. With cyberattacks becoming more and more sophisticated, creating strong passwords is no longer optional – it’s essential. This World Password Day, take the time to check in on your password practices. Update those old logins, enable MFA, and let Webroot do the heavy lifting. Just a few simple steps today can save you a world of trouble tomorrow.
Looking for more information and solutions?