By Ian Moyse, EMEA Channel Director
 With Christmas fast approaching, (lest we forget the shops have kindly put all the Christmas goods out in September and early October again!) we can expect online attacks to increase as per their normal schedules, ramping up through the end of the year.
With Christmas fast approaching, (lest we forget the shops have kindly put all the Christmas goods out in September and early October again!) we can expect online attacks to increase as per their normal schedules, ramping up through the end of the year.
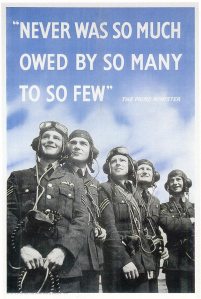
With apologies to Sir Winston Churchill, never in the field of Internet conflict was so much harm done to so many by so few.
For all the benefits the Internet provides our lives, no single technology has given so few criminals the ability to cheaply and easily target the many. We’ve seen the rise of the dark economy, where far flung cybercriminals trade skills and produce burglary tools for sale, and we live with the consequences every day. Sophisticated attacks target both our computers and our users, through social engineering.
While the increases in cybercrime incidents seem to indicate a greater number of attackers, the reality is that the growth of the Internet itself gives rise to the ever-increasing volume of botnets, keyloggers and spam. The Internet makes us all contactable and, to a degree, easily identifiable. As we surf the Web, we leave traces of our presence in the form of electronic footprints — cookies, blog postings, and of course, our activities on social networks and other online forums.
And yet, no matter what we do to stem the tide, the problems only seem to increase in size and scope.
You can tune in and listen live to more of Ian Moyse’s predictions for next year’s most serious threats in his free Webinar, ThreatNet 2011, Thursday, November 4, at 10am Eastern.
As our operating systems become increasingly hardened to direct attack, the humans behind the keyboard remain as susceptible as ever to social engineering scams. Fake Web pages phish our passwords, all the while taking on the appearance of the genuine article. Keyloggers such as Zbot steal the passwords not only for our bank accounts, but for the FTP servers that control what information can be posted to our own Web sites, and those FTP passwords become a commodity criminals trade and use to host malicious pages and files on innocent users’ servers. As it becomes more and more difficult to distinguish fake sites from real ones, we struggle mightily to train colleagues, family, and friends not to post too much information about themselves online, lest they themselves find their identities stolen.
The growth of the Web, and the wider availability of inexpensive computers, also has lead to a greater percentage of unsecured computers and more sophisticated and empowered hackers probing the Internet. With the Web entrenched in our daily lives and social networking sites growing faster than ever, the ability for someone to connect to vast volumes of people is upon us. With this great access comes greater threats. An incident nowadays can affect anything from a single computer, to a range of host computers at hundreds of thousands of locations, in a relatively short space of time.
In moving from centralised computing to a more distributed model, the business world has enabled the attacker to follow suit – to disperse and grow their attacks to volumes never envisaged before and to allow one individual to reach out to millions with scams, spyware and exploits. Never before in history has one individual with a lack of resource or funds been so empowered to use knowledge to the detriment of so many so quickly. We now see organized crime bringing together teams of these “expert” attackers, giving them resources to do damage far in excess of what a lone backroom spammer could accomplish.
The question is, how long before we see a repeat of the growth of volume in spam applied to far more malicious attacks? In 2007 there was a 400% year over year growth in the volume of spam. Now we see the growth of malware, phishing, and backscatter as well as spam, and the growth takes mere weeks or months instead of years. Is there a new type of scaled attack coming? Is there a larger spambot network already laying dormant, waiting for its cue to kick into action? No one can predict, but we can be sure that the financial benefits of cyberattacks give criminals no motivation to stop trying.



















Ian’s article is most timely – just today, a DDoS attack brought down a whole country – Minamar (Burma). The scale and capabilities of the “bad guys” these days is truly phenominal and in some cases it’s foreign governments as well as organized cybercrime that are behind these attacks. They have really deep pockets and resources. Such attacks (be they DDoS or SpamBots) need a similarly scaled response. By blocking malicious traffic in the cloud (as Webroot Software does), users can enjoy a level of “defence in depth” that was not possible a few years ago. Endpoint protection (while still needed) just doesn’t cut it anymore as the only defence a system needs. And the genie is out of the bottle with regards to many user’s personal information which has been scattered out in cyberspace for easy pickings. International bounderies cloud things even more as the Internet traverses a myriad of legal jurisdictions in 195 different countries. Churchill would not be amused…