![]() Most of yesterday, Threat Research Analyst Armando Orozco and I took a closer look at a piece of malware discovered by a university security researcher, Xuxian Jiang of North Carolina State. The malicious code, which the malware creator named Plankton, is embedded into a number of apps that were briefly posted to Google’s Android Market earlier this week, then rapidly pulled down after the researchers informed Google of their initial findings.
Most of yesterday, Threat Research Analyst Armando Orozco and I took a closer look at a piece of malware discovered by a university security researcher, Xuxian Jiang of North Carolina State. The malicious code, which the malware creator named Plankton, is embedded into a number of apps that were briefly posted to Google’s Android Market earlier this week, then rapidly pulled down after the researchers informed Google of their initial findings.
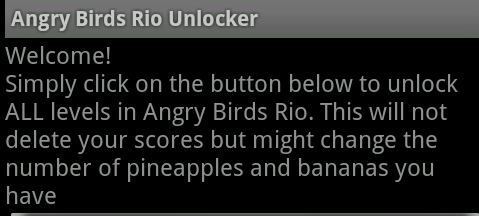
The Plankton code appears in a number of applications that were all focused on the popular game series Angry Birds. Some of the samples we looked at came as Android apps with names like Angry Birds Rio Unlocker v1.0, Angry Birds Multi User v1.00 or Angry Birds Cheater Trainer Helper V2.0.
When executed, the program displays the following text on the screen:
Welcome!
Simply click on the button below to unlock ALL levels in Angry Birds Rio. This will not delete your scores but might change the number of pineapples and bananas you have
None of the programs function as advertised. Instead, the malicious apps install additional code into the Android device into which they’re installed. These additional functions provide remote access and control of the Android device to, presumably, the distributor of the malicious apps, whose identity remains unknown at this time.
It’s nice that the creators of the Trojan labeled their code so distinctly. We can filter them off an infected device like a whale slurps krill.
Unlike several recently-discovered malicious apps, these Android Trojans don’t invoke various exploits on the Android device in order to obtain root, or administrative, access to the operating system. Instead, the remote commands simply give an unknown criminal access to what some may consider sensitive data on the phone, including the browser history, bookmarks, and homepage settings in the built-in Android browser.
When executed, the app also contacts a command-and-control server, which sends back instructions for the app to download an additional Java .JAR file. The app pulls down the .JAR file and installs it quietly in the background. We’re currently working on an analysis of these payloads; Early reports from the university researchers indicate that the payloads are simply reworked versions of the remote access code embedded in the Trojan, modified so they’re slightly harder to detect using existing antivirus signatures.
As we have following previous disclosures about novel Android malware, such as the recently discovered DroidKungFu, we’re currently protecting Android devices that have our Webroot Mobile app installed from Trojans such as Plankton.
And of course, Android users can protect themselves by using a little common sense when they download apps: Does the app sound like what it promises to do is too good to be true? Does it ask for all kinds of permissions that it shouldn’t need to fulfill its mission? Did you get it from the official Market or a legitimate app store such as Amazon, or from some random app collection? If you can answer yes to any (or all) of these questions, just don’t install the app.





















I think smartphones is next target of hackers and malware developers. One question arise here is how to keep android device safe? I personally suggest to think twice before downloading and installing app from unverified sources like outside of the market.
So many android viruses. You hear about the one that records all your calls?
I guess this is inevitable. It just sucks though, because like computer program hacking, its all so anonymous.