by Dancho Danchev
Malicious attackers quickly adapt to emerging trends, and therefore constantly produce new malicious releases. One of these recently released underground tools, is the PickPocket Botnet, a web-based command and control interface for controlling a botnet.
Let’s review its core features, and find out just how easy it is to purchase it within the cybercrime ecosystem.
As you can see in the attached screenshot, the seller of the PickPocket Botnet has managed to infect 388 hosts, with 12 of them currently online. What are some of the core features of the botnet kit?
Translated cybercrime underground market proposition:
-Formgrabber :
*IE 8/9
*FF 3/4.
-RDP (reverse connection).
-FTP Viewer , can browse files on PC.
-DDOS
-Download & Execute
-Donload File
-CMD , send cmd command to bot’s
-Socks5
-Visit webpage (hidden)
-Visit webpage non-hiden
-Spread USB/Emails
-Kill AV’s (windows xp ,2003 , 2000 – only)
-Spam (Find emails on bot PC and spam them)UPDATE :
* IRC -(BotNet works with HTTP panel + IRC as backup)
* DDOS -(New method off ddos , powerful)
* Spread Addet : P2P spread + Spreader on all usersPrice : 200LR = 3 months hosting + Setup + FUD (with no RDP Conection)
Price : 300LR = 3 months hosting + Setup + FUD (RDP Conection)
PickPocket bots have DDoS functionality, and spread over email and AutoRun. Updated versions of the bot also spread over P2P, with the botnet master adding additional functionality to the botnet on a periodic basis. Moreover, the bot is capable of killing antivirus software on Windows XP, 2003 and 2000, next to harvesting email addresses from the infected PC, and then spamming them.
The botnet master is facilitating sales using Liberty Reserve and is offering a managed service with 3 months of hosting for the command and control infrastructure of the botnet.
Just how prevalent are bots using AutoRun as a core spreading mechanism? In February 2011, Microsoft disabled AutoRun on Windows XP and Windows Vista machines, resulting in a significant decline in AutoRun infections. Although one of the other spreading mechanisms of the PickPocket Botnet is clearly outdated, the other are in tact with the modern threat landscape, the propagation over email and P2P in particular.
You can find more about Dancho Danchev at his LinkedIn Profile. You can also follow him on Twitter.







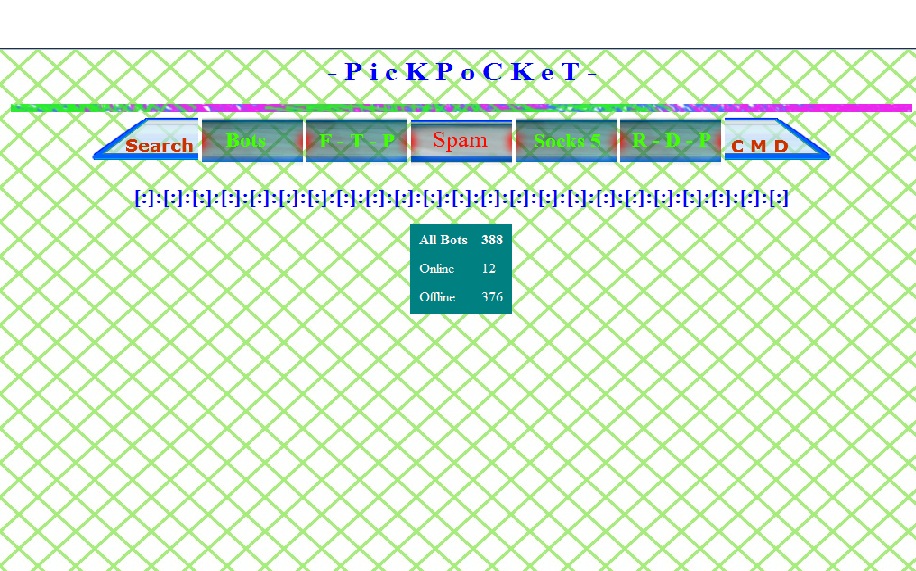
nice GUI