What would an average cybercriminal do if he had access to tens of thousands of compromised email accounts? He’d probably start outsourcing the CAPTCHA solving process, in an attempt to hijack the IP reputation of both Domain Keys verified and trusted domains of all major free Web based email service providers.
What about sophisticated attackers wanting to conduct cyber espionage on a mass scale, in an efficient and anonymous — think malware-infected hosts as stepping stones — way? As of early 2013, those willing to pay the modest price of 3000 rubles ($97.47), can get access to a command line DIY tool that’s specifically designed for this purpose – automatic, anonymous and efficient data mining combined with compromised email account content grabbing.
Let’s profile the DIY tool, feature screenshots of the tool in action, and discuss its potential in the context of utilizing OSINT through botnets.
More details:
What the script does is fairly simple, yet the consequences of using it on a mass scale can empower a pragmatic cybercriminal with invaluable amounts of intellectual property. By utilizing the IMAP protocol, the command line tool allows a cybercriminal to apply a diversified set of filters for automatic extracting of a hacked email account’s content, including sent/received attachments, emails containing passwords for any service, and most interestingly, it allows a cybercriminal to gain access to this data by using a malware-infected host as a stepping stone, in this case, a Socks server.
The current version of the tool supports GMail, Yahoo! Mail, Me.com, AOL.com, Mail.com, Mail.ru, Rambler.ru, Yander.ru, Qip.ru, but naturally, can work on any server given a working mail server address and a port. As a bonus, potential buyers will also receive sample .bat and .vbs scripts helping them automate the process even further.
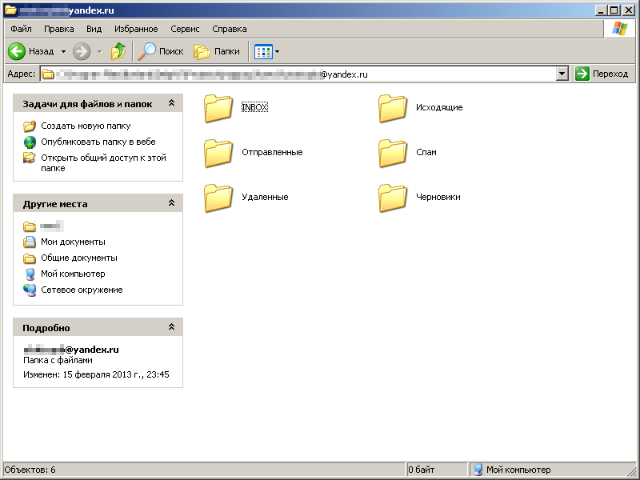
Sample screenshot of the output of content grabbed from a compromised email account:
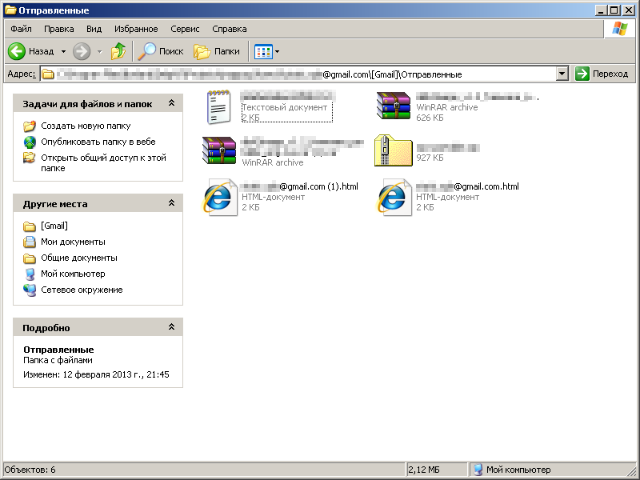
Sample screenshot of automatically extracted .rar attachments from a compromised GMail account:
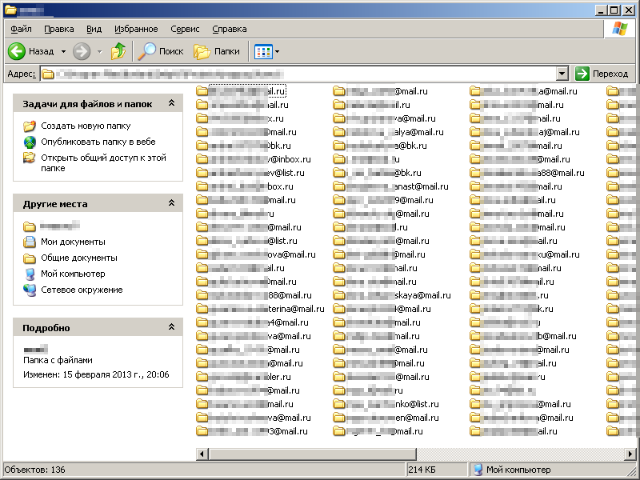
Sample screenshot demonstrating the efficiency-centered command line tool in action:
It’s a public secret that employees don’t just bring their own device to the workplace these days, but also, periodically forward work related intellectual property to their private Web hosted email accounts. Thanks to this fact, a potential cyber spy could easily purchase access to hundreds of thousands of compromised email accounts obtained through data mining a botnet’s infected population, to later on once again data mine the actual content of the infected population’s email communications.
And although the concept used as a foundation for this command line tool is nothing new, we anticipate that the cybercriminal behind it will receive a flood of customer orders, mostly from novice cybercriminals looking for ways to acquire valuable intellectual property, and later on monetize it.
Users are advised to monitor their email account activity logs for suspicions activity and to ensure that they access their email account from a malware-free host. Also, make sure to active two-factor authentication when available.
You can find more about Dancho Danchev at his LinkedIn Profile. You can also follow him on Twitter.