When Microsoft disabled AutoRun on XP and Vista back in February, 2011, everyone thought this was game over for the bad guys who were abusing the removable media distribution/infection vector in particular. However, pragmatic and market demand-driven opportunistic cybercrime-friendly vendors quickly realized that this has opened up a new business opportunity, that is, if they ever manage to find a way to bypass Microsoft’s AutoRun protection measures.
Apparently, they seem to have a found a way to bypass the protection measure by tricking Windows into thinking that the connected USB memory stick is actually a ‘Human Interface Device’ (keyboard for instance), allowing them to (physically) execute custom scripts within 30/40 seconds of connecting the custom USB memory stick to the targeted PC.
From theory into practice, let’s profile their international underground market propositions and discuss the impact these USB sticks could have in today’s bring your own device (BYOD) corporate environment.
More details:
Sample screenshots of the actual advertisements:
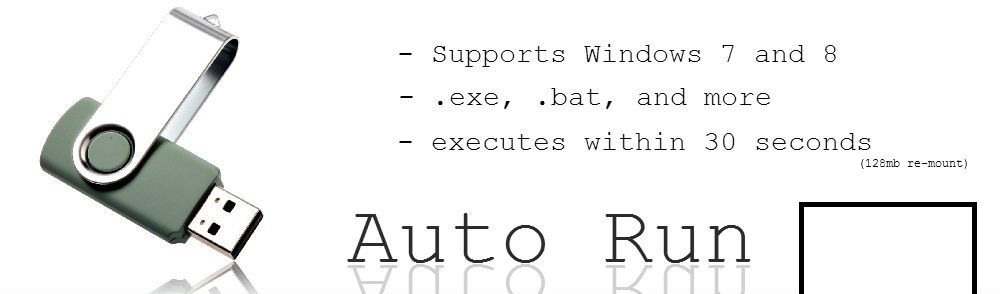
According to the advertisement, the malicious script/file executes in under 50 seconds on first mount, and within 30 seconds on a second re-mount, followed by just 6 seconds of visible (malicious) activity on the screen, with the vendor behind the ‘solution’ also working on Mac OS X version. The price for a custom 128MB USB memory stick is $54, and the price for a custom 8GB USB memory stick is $64.
We’re also aware of yet another cross-platform (Windows, Mac OS X, Linux) commercially available (not advertised at any cybercrime-friendly communities for the time being) AutoRun protection bypassing ‘solution’, relying on the same concept as the first one. However, due to its payload generating capability, custom scripting language, and lower price ($39.99), we expect that the custom USB ‘solution’ pitched to pen-testers internationally would remain the tactic of choice to anyone wanting to compromise a host, once they manage to bypass the physical security (if any) in place.
Time to get back to the basics – physical security.
You can find more about Dancho Danchev at his LinkedIn Profile. You can also follow him on Twitter.