Among the most common misconceptions about the way a novice cybercriminal would approach his potential victims has to do with the practice of having him looking for a ‘seed’ population to infect, so that he can then use the initially infected users as platform to scale his campaign. In reality though, that used to be the case for cybercriminals, years ago, when managed cybercrime-as-a-service types of underground market propositions were just beginning to materialize.
In 2013, the only thing a novice cybercriminal wanting to gain access to thousands of PCs located in a specific country has to do is to make a modest investment in the (managed) process of obtaining it. Let’s take a peek at one of the most recently launched such services.
More details:
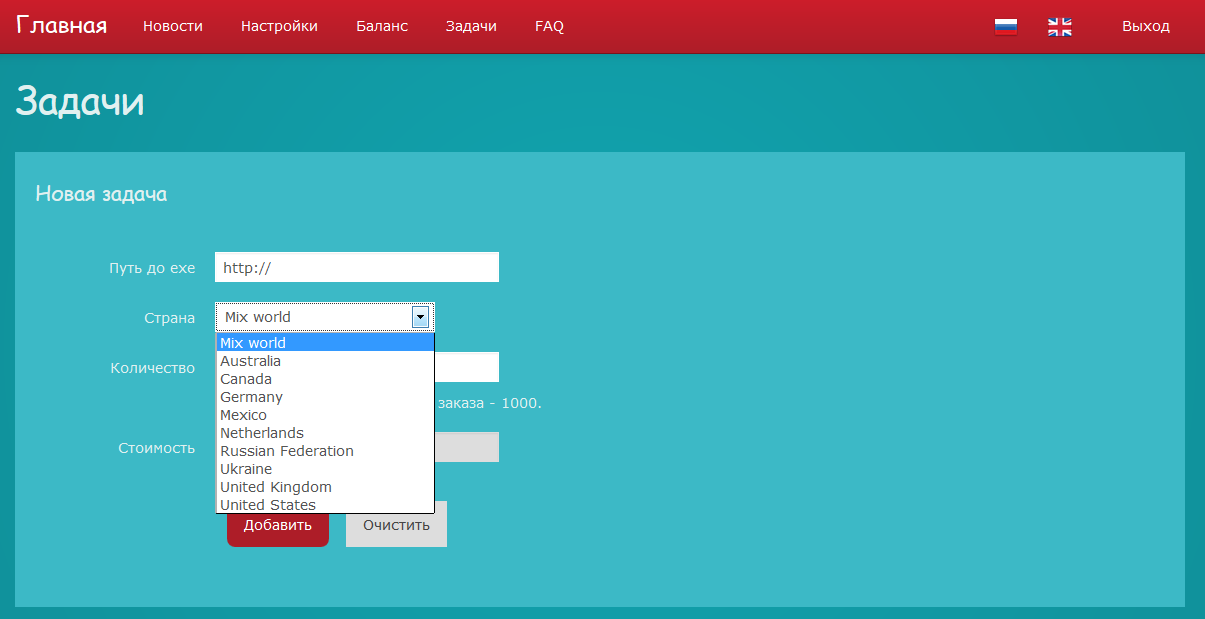
Sample screenshot of the service’s interface:
A potential customer wanting to ‘drop’ any given executable onto the hosts of users located in Australia, Canada, Germany, Mexico, Netherlands, Russian Federation, Ukraine, United Kingdom or the United States, would simply have to provide a ‘live link’ to the actual executable, choose the country of his choice — 1000 hosts minimum — pay, and have his malware dropped on hosts based in his country/countries of choice.
This vendor is a good example of greed oriented, rather than sociocultural/socioeconomic driven underground market proposition, as he’s offering access to compromised hosts based in Russia and Ukraine. A practice which we expect to continue observing, on behalf of novice cybercriminals looking for ways to differentiate their underground market proposition.
You can find more about Dancho Danchev at his LinkedIn Profile. You can also follow him on Twitter.







Someone is hacking my computers and Android Phones. Webroot isn’t finding and killing it. They are still deleting my files and activating different programs. I know who is doing it, but don’t know how to prove it.