At Webroot’s Threat Blog, we often discuss the dynamics of the cybercrime ecosystem. Through the prism of basic business, marketing and economic theories, the idea is to help make them easy to comprehend by most readers. Constructively raising awareness on some of the driving factors behind the epidemic growth of cybercrime. We also often emphasize on concepts such as standardization, vertical integration, for hire, rent or on demand business models, commoditization and economies of scale. This further highlights the legitimate market-like state of the underground marketplace, in terms of the variety of business models, pricing schemes, and current/long term centered business strategies.
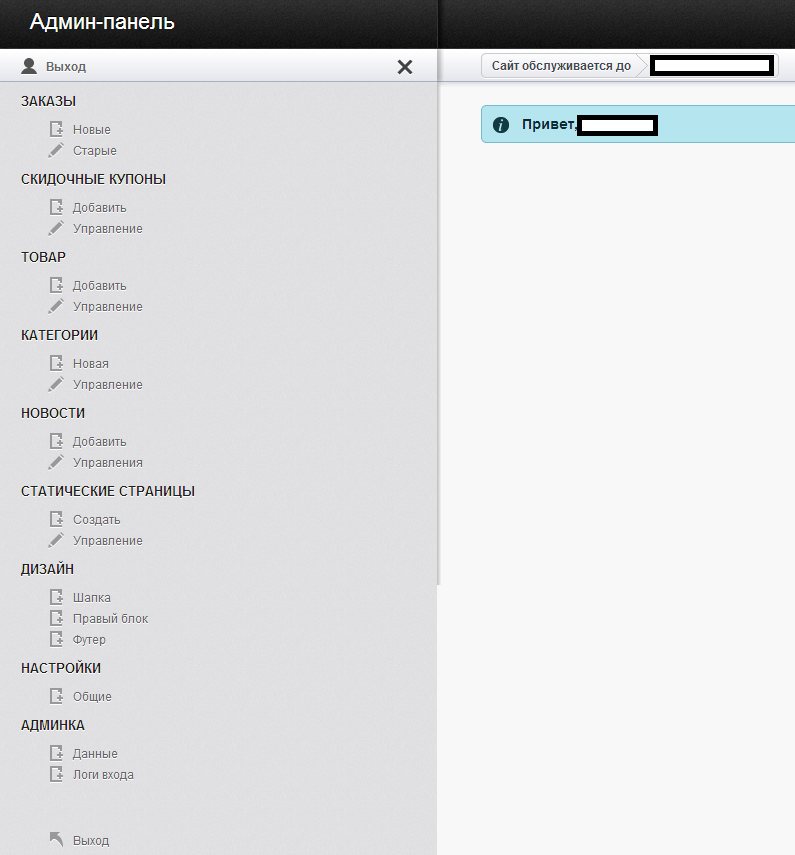
In this post, we’ll put the spotlight on an efficiency-centered administration panel for a DIY (do it yourself), self-service type of E-shop script, to be used by prospective cybercriminals as a turn-key conversion solution for their fraudulently obtained assets. In this case, the ability to efficiently sell access to compromised accounts. Not only has this E-shop script have the potential to empower virtually anyone with the ability to sell their goods, but in this particular case, the vendor is promising to donate some of the revenue for philanthropic purposes.
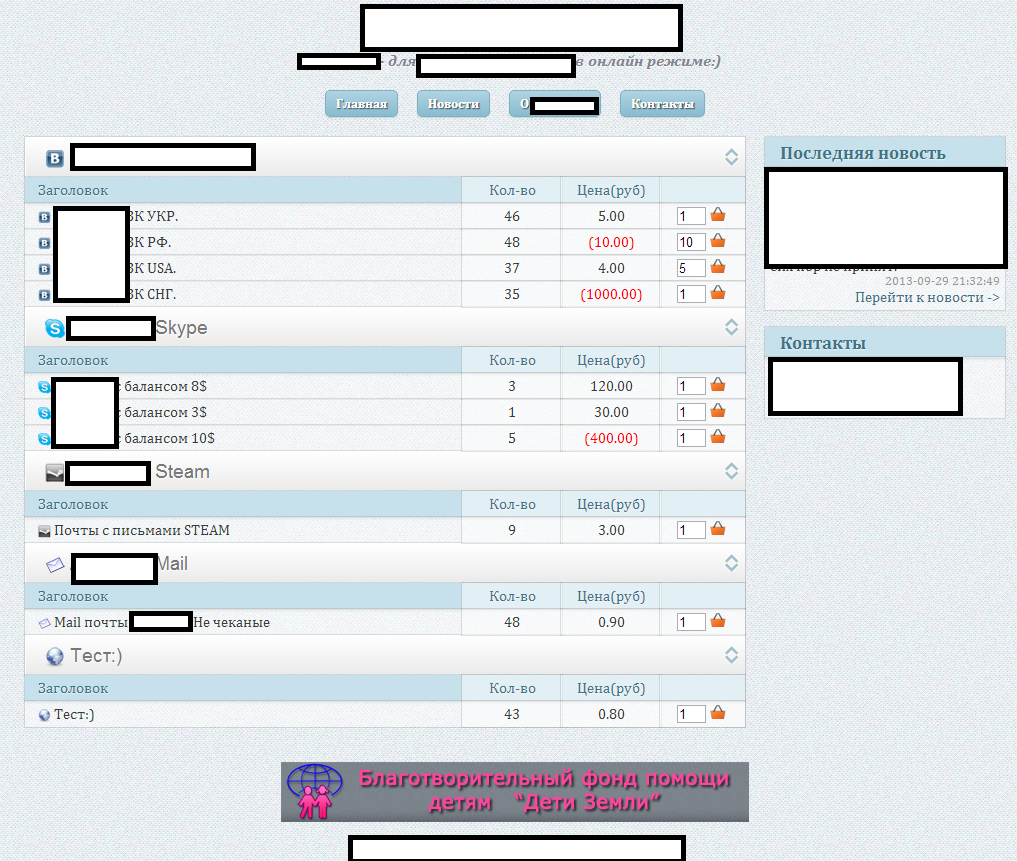
Sample screenshot of an E-Shop for compromised accounts, as created by the E-Shop script offered for sale:
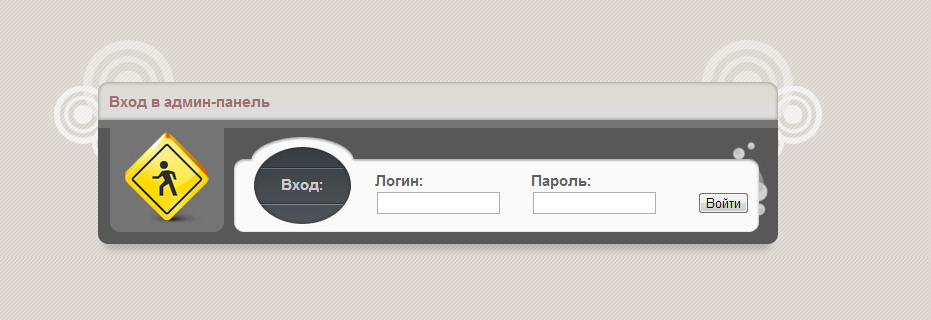
Sample screenshot of the login page for the administration panel:
Sample screenshots of the actual administration panel:
Despite the fact that we’ve seen scareware ‘going green’ — at least to convince the user into thinking that it’s a legitimate antivirus offer – the author of this E-shop script is also promising that 10% of the revenue coming from this project will be donated to a charitable project with the project’s banner clearly visible at the bottom of the demo E-Shop. Such efficiency-oriented underground market propositions have the potential to streamline the entire supply chain of fraudulently obtained assets, similar to the standardization of money mule recruitment processes, or the template-ization of malware-serving sites, which were taking place a couple of years ago.
We’ll continue to monitor and update the development of this standardizaed E-shop for fraudulently obtained assets that could potentially have an even bigger impact on the cybercrime ecosystem.