Top Predictions for 2014
- FBI/ICE MoneyPak
- Cryptolocker
- Rogues
As this year comes to a close we’ve seen some measurable progress on the infiltration techniques for malware. We’re going to give you some insight into some of the top threats of 2013 and what it could mean for 2014.
FBI/ICE MoneyPak

We saw some frightening improvements with Ransomware this year. FBI/ICE MoneyPak or Win32.Reveton was a huge hit to the PC community. Although first seen in 2012 it wasn’t until 2013 that it was tweaked to be one of the most annoying and difficult Ransomware to remove. Once dropped on your computer and executed, either by email attachment, “video codec” (or the like), it eliminates all the safemodes, taskmanager and shows nothing but this screen. You have no options to launch any applications like system restore, regedit as the explorer shell hijacked. Most of these also start themselves in new user accounts so the only removal is to be blocked at dropped by your Anti-Virus or boot to a linux disc and remove it there. Since this is still super effective (especially zero day variants) against most anti-virus I would expect to see more of this. I foresee naming changing and the typical scare tactics text of “violations” to change as once more and more people become educated on these threats its really easy to just slap on a new image and text and fool you again.
Cryptolocker
This new Cryptolocker that’s got everyone in a scare is no joke. Once on your machine this Ransomware will use about 10% CPU power to encrypt all your documents unnoticed (*.odt, *.ods, *.odp, *.odm, *.odc, *.odb, *.doc, *.docx, *.docm, *.wps, *.xls, *.xlsx, *.xlsm, *.xlsb, *.xlk, *.ppt, *.pptx, *.pptm, *.mdb, *.accdb, *.pst, *.dwg, *.dxf, *.dxg, *.wpd, *.rtf, *.wb2, *.mdf, *.dbf, *.psd, *.pdd, *.pdf, *.eps, *.ai, *.indd, *.cdr, *.jpe, *.jpg, *.avi, *.mp3, *.wma, *.wmv, *.wav, *.divx, *.mp4, *.dng, *.3fr, *.arw, *.srf, *.sr2, *.bay, *.crw, *.cr2, *.dcr, *.kdc, *.erf, *.mef, *.mrw, *.nef, *.nrw, *.orf, *.raf, *.raw, *.rwl, *.rw2, *.r3d, *.ptx, *.pef, *.srw, *.x3f, *.der, *.cer, *.crt, *.pem, *.pfx, *.p12, *.p7b, *.p7c).
Once it’s encrypted all files found on your local drives as well as mapped network drives it will then show you the above screen. This isn’t like previous versions that stored the decryption key in the initial drop, but instead has the key created and stored on a remote server and the key is different with every unique infection. This leaves you with little to no recourse unless you have a back up or a system restore point saved. Shadow Explorer is a lovely tool that will allow you to restore all files that you had at any given restore point using the windows built-in Volume Shadow Service (Vista/7/8 only). Be warned however, this only works on files stored on the same hard drive the operating system is on so if you lost files on other slave drives in your box or network drives then you have no option but to pay. Also a growing percentage of the Cryptolockers we’ve seen are now executing this command off the bat:
“C:\Windows\SYsWOW64\cmd.exe” /C “C:\Windows\Sysnative\vssadmin.exe” Delete Shadows /All /Quiet
This completely removes all hope of using tools like Shadow Explorer. Expect to see plenty more Cryptolocker in the future, and expect them to pack more tricks to prevent you from using tools to restore files and prevent Anti-virus from detecting them.
Rogues
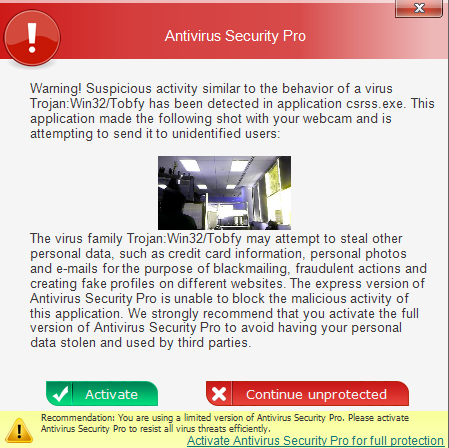
We saw some impressive improvements in Rogues over the year 2013. Not only are the malware authors putting more effort into the interface to make it more realistic, but they’re even taking pictures of you! Specifically we came across some samples that if you didn’t pay in 10 minutes or so it would actually capture pictures using the built-in webcam. It claimed that “detected viruses took these pictures and would send them to unauthorized users.” However, we saw no network traffic other than the initial drop of components. What I expect to see in the future is a merge of this and cryptolocker techniques. Given the extreme violation of privacy that taking unauthorized pictures with the webcam poses I can definitely see variants actually threatening to distribute this data as leverage to win over the ransom.
If you have any questions or comments please let us know!