Driven by popular demand, the underground market segment for TDoS (Telephony Denial of Service) attacks continues flourishing with established vendors continuing to actively develop and release new DIY (do-it-yourself) type of tools. Next to successfully empowering potential customers with the necessary ‘know-how’ needed to execute such type of attacks, vendors are also directly contributing to the development of the market segment with new market entrants setting up the foundations for their business models, using these very same tools, largely relying on the lack of situational awareness/understanding of the underground market transparency of prospective customers. Positioned in a situation as ‘price takers’, they’d be often willing to pay a premium to gain access to TDoS type of attack capabilities, with the intermediary in a perfect position to command a high profit margin, further improving the market segment’s capitalization.
A well known (Russian) vendor of TDoS products continues ‘innovating’ and utilizing basic customer-ization concepts, thereby introducing new features into well known TDoS ‘releases’, bug fixes, and overly-continuing to actively maintain a decent portfolio of multiple TDoS applications. Let’s take a peek at the most recently updated, 3G USB Modem/GSM/SIM card based of TDoS attack application, dubbed by the vendor as the most effective and cost-effective form of TDoS attack.
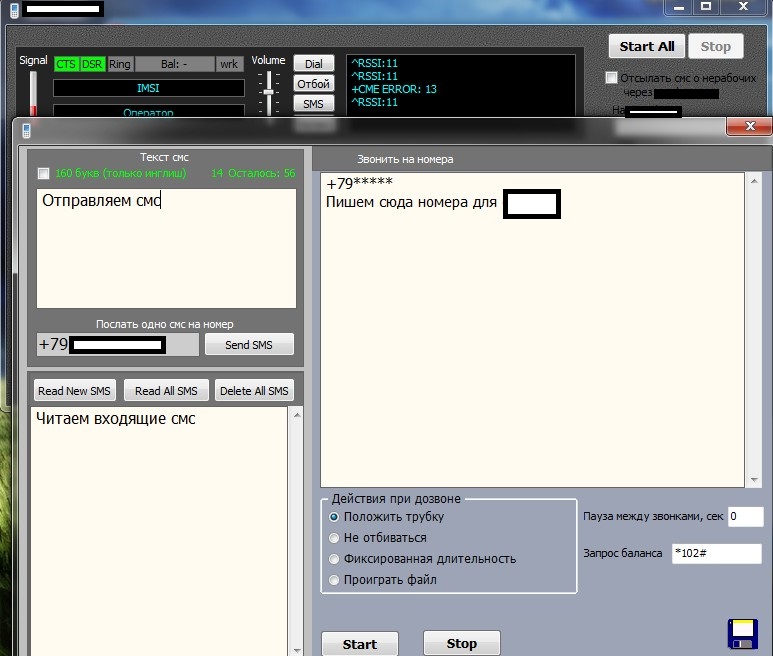
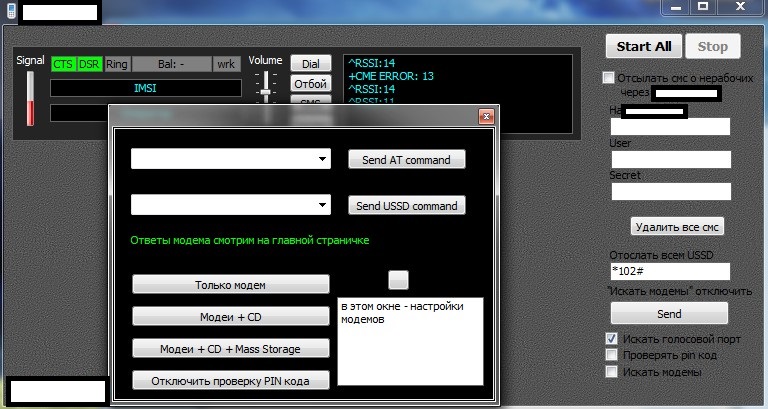
Sample screenshots of the 3G USB Modem/GSM/SIM card based TDoS tool:
Sample screenshot of a sample inventory of 3G USB Modems utilized for launching TDoS attacks:
In combination with the commercial availability of non-attributable SIM cards, both TDoS vendors, and customers utilizing the technique in a DIY fashion, would continue taking advantage of the concept, successfully undermining the availability of a victim’s phone/corporate phone system. Moreover, in our “Cybercrime Trends 2013 – Year in Review” analysis, we indicated that the TDoS market segment is gaining the necessary market traction, thanks to, for instance, proven DDoS (Distributed Denial of Service) attacks vendors, ‘vertically integration’ by starting to offer TDoS services next to their portfolio of DDoS type of attacks.
We’ll continue monitoring the TDoS market segment and post updates as soon as new developments emerge.