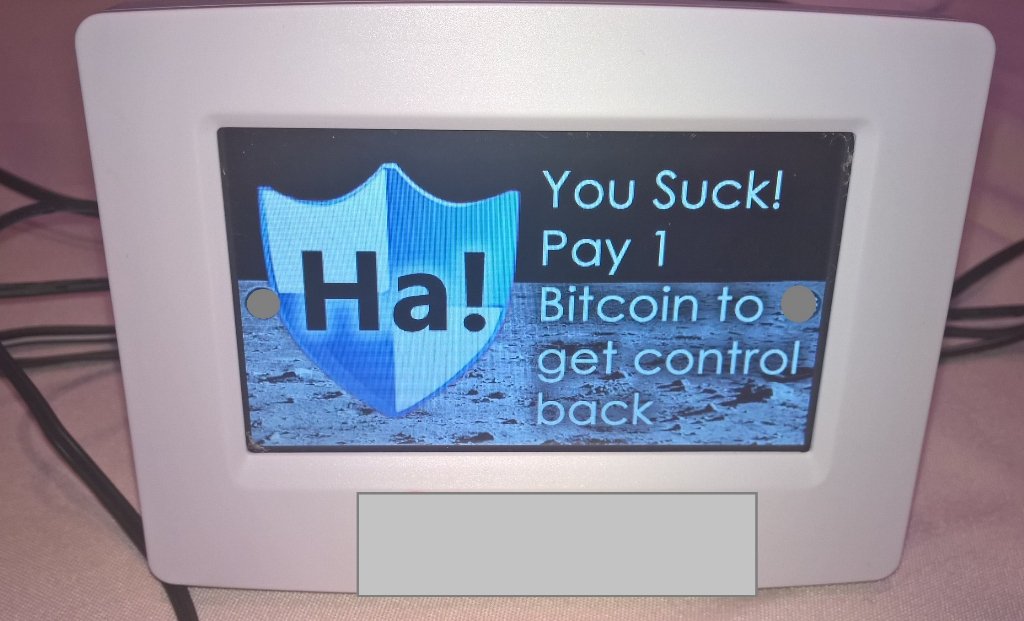
We all know that Internet of Things (IoT) is the future and that everything from your refrigerator to your toaster may eventually connect to the internet. With that being the case, it’s important to remember that these connected devices need to be designed with security in mind. On Saturday at the Def Con hacking conference in Las Vegas, Andrew Tierney and Ken Munro showcased a ‘smart’ thermostat hack, in which they were able to install encrypting ransomware onto the device, fortunately just as a proof of concept. Check it out:
The hacked thermostat (displayed in the screenshot above) runs a Linux operating system and has an SD card slot for owners to load custom settings and wallpapers. The researchers found that the thermostat didn’t check what files were being loaded or executed. Theoretically, this would allow hackers to hide malware into an application that looks just like a picture and fool users into transferring it onto their thermostat, which would then allow it to run automatically. At that point, hackers would have full control of the device and could lock the owner out. “It actually works, it locks the thermostat,” Munro said. This achieves the predictions of others in the security industry.
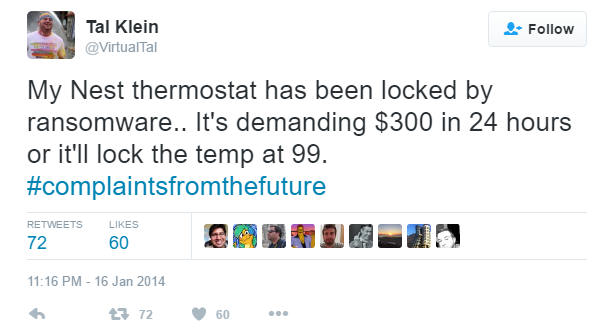
Despite the above tweet, Tierney and Munro declined to confirm the brand of this particular thermostat that they hacked. Because this test was so new, despite the vulnerability being showcased, the reserachers haven’t yet disclosed the vulnerability to the manufacturer, but the plan is to disclose the bug today. They also said that the fix should be easy to deploy. While this ransomware isn’t an immediate threat to anyone using smart devices in their homes today, the point has been proven that it’s very possible to create ransomware for these new and emerging IoT devices. “You’re not just buying [Internet of Things] gear,” Tierney warned, “You’re inviting people on your network and you have no idea what these things do.”






Another thermostat security issue is whether outsiders can view your heat settings, perhaps by hacking the network side of the infrastructure? If someone could see your thermostat was locked at 65F for a few days, they could safely assume you were gone on vacation and rob your house.
A good point. However, houses do not get robbed. Houses get buglarized, people get robbed.
Very few IoT devices have decent security. Worse, many are designed so they “need the cloud” to function, so if you block their internet access at the router, they won’t work. (Think about what that means when the industry shakes out and most of them go belly up.) Bottom line is that IoT devices should function when isolated.
The Register has a great article just on IoT wireless locks that are trivial to defeat. (The Kwikset Kevo lock can be taken apart by a burglar with a screw driver. Duh…)
http://www.theregister.co.uk/2016/08/25/iot_manufacturer_caught_fixing_security_holes/
IS ANY OF THIS GOOD FOR MAC COMPUTERS
Why not just take off the nest and have a backup dumb thermostat available?
so easy to fix.
So what happens if you simply cut the wires, remove the thermostat and install a new one?
I thought Webroot was working on a Ransomeware update for our products?
Hello Richard,
Our Threat Team is constantly tracking new Ransomware infections every day to ensure that your files are protected.
https://community.webroot.com/t5/Webroot-SecureAnywhere-Antivirus/How-does-Webroot-stop-ransomware/td-p/256844
I will say the absolute #1 way you can prevent any damage from these types is Backups, Backups, Backups.
http://www.pcworld.com/article/3056907/security/how-to-stop-ransomware-backup-can-protect-you-but-only-if-you-do-it-right.html
Warm Regards,
Josh P.
Webroot Community Support
They need to work harder faster, and longer, if that Is what they are working on. I have that program and have been ransomwared twice in the last 3 months. I have gotten an anti ransomware program, and anti exploit program, and another malware program since the last hack. Maybe I won’t be such a sitting duck. But one never knows
This article is in regards to thermostats but my concern is wireless printers. Several times this past month I have turned my printer off only to find it turned back on. So finally I had my husband turn the printer off and then unplug it from the wall. That cured the turning off and back on until he plugged the printer back in. Then this past week, while uploading documents and graphics to my website, ftp, I had no control over the scroll bar. It was going haywire. So I turned my computer off and let it set off for a few minutes and turned it back on, changed the passwords and things worked fine. Feedback please. Thanks for these articles. I read all of them.
Some really good reasons why we should never computerize our homes, thermostats, ovens, a/c units, or refrigerators. We think ransomware./hacking/cybercrime is bad now? Wait until criminals can lock us out of our own homes. Just what America needs!
Rip the dam thing off the wall! There are plenty of thermostats around that are no on line> and you have to ask DO I REALY NEED IT? For whay so i can set it on my phone :Sirously!
Get a new thermostat preferably of a different make.
wow, So glad we have sweaters and a fireplace when it is cold; we open windows when it is hot, we are lucky the way. With all this automation it won’t be long before someone steals a car remotely. Thanks, everyone, for thee posts.