The convenience of having some kind of internet connection on more and more of the devices we use each day is undeniable. However, without proper security vetting, this convenience may come at a hefty price. In the past year alone, we’ve seen millions of routers, DVRs, IP cameras, cars, and more get hacked and either ransomed or hijacked for illegal purposes. This is mostly because the vendors of these devices only focus on functionality and the “set it and forget it” mentality. The next big IoT device type on the high-risk radar might not be what you expect… It’s toys.
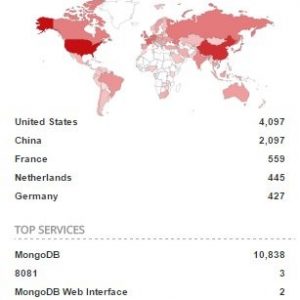
Just last month, almost a million CloudPets.com accounts were compromised which contained 2 million voice recordings of kids and their families. This data—which is currently being ransomed—was taken from an unsecured MongoDB installation. There was no password or authentication required to access the widely available MongoDB on port 2701 at 45.79.147.159. Anyone who tried to connect had access and could access as much data as they wanted. It was only a matter of time before threat actors decided to take the data and delete the original copies from the server. In fact, the MongoDB currently has over ten thousand unsecured servers from which data has been stolen and held for ransom.
The CloudPets breach is yet another in a long list of poorly secured connected devices. Germany has already banned My Friend Cayla dolls, having classified them as espionage devices. Anyone selling the toy may be subject to a fine of up to 25,000 € for anyone who sells the toy. Barbie dolls are also on radar, since the Hello Barbie doll made headlines a couple of years ago. The doll was easily hackable and would reveal users’ system information, Wi-Fi network names, internal MAC addresses, account IDs, and even MP3 files. Aside from the sheer creepiness of hacking a children’s toy, this type of sensitive information can be used by cybercriminals to gain entry into a user’s more high-value accounts. The ease with which an attacker can access users’ details, including passwords, can give them a starting point to infiltrate other accounts, and sensitive family information can be used to guess passwords and secret questions.
Are hackers toying with your data?
We continue to witness a growing number of attacks with extortion as their goal. They begin with a simple but effective brute force assault from RDP to MongoDB and are now on to MySQL, and it won’t stop there. As long as such protocols, tools, and software are installed without adequate security measures, new breach stories will continue to make the news. Vendors of all IoT devices must ensure that they properly secure their devices and the information they collect.
Beyond the vulnerabilities the backend databases that support these IoT devices comprise, we have also been seeing remote exploitation of the actual toy device via Bluetooth Web API. Any user with a computer or a phone can connect to the CloudPets plushie without any authentication, and can then control the toy. Using the built-in microphone, an attacker can send and receive recorded messages to and from the toy, and they don’t even have to be inside the house. Experts in the field are already issuing warnings as to the privacy risks associated with allowing websites to connect to devices via Bluetooth. The CloudPets situation is a prime example of connected device manufacturers being grossly negligent towards the security of their products, and only focused on functionality (and, therefore, saleability.)
There’s a smarter way to play
To mitigate these types of risks, vendors need to conduct regular risk assessments and security vetting. They need to understand what does and does not need to be internet-facing within the organization. The items that do need to connect to the internet should be protected accordingly, starting with checking and improving on default settings. Authentication levels for each product need to be investigated and possibly enhanced to require two-factor, given that default options aren’t always the most secure. Where possible, access should be restricted based on policy, and vendors must investigate whether VPN and tunneling protocols would work for a particular use case. It’s essential to keep installations up to date. Additionally, vendors need to regularly review the setup configurations, look for unexpected or undocumented changes, and review the listed administrator accounts as a standard routine. In addition, consumers must be educated on the potential for these devices to generate and store sensitive data, as well as how to use good security practices to ensure their information stays safe. Although we can never make ourselves 100% secure, we should give ourselves a fighting chance.
Once a vendor or organization has set up what it believes to be the best defense, it cannot simply forget about it. Plans need to be in place for when a breach does occur so data can be recovered as quickly and efficiently as possible. This means creating and executing a well-divided, regularly-tested, air-gapped backup strategy. It could mean the difference between a breach being little more than a learning experience, versus resulting in devastating losses from which the business may not recover. It’s also important to make sure all employees are aware of what to do when things go wrong, as time will be of the essence. Each employee must know who needs to do what, when, where and how, from the incident responders to PR. Because the modern threat landscape continually changes, the only way to achieve remotely effective protection is not to sit back and relax, but to continue examining, refining, and improving upon security practices.






It’s terrifying how many sites like this get hacked every day! And who would have thought that toy sites will be on the radar? Website owners need to pay more attention to this and how important it’s to secure their online presence. For all of us!
Thanks for your comment, Ines 🙂
I completely agree!
Warm Regards,
Josh P.
Digital Care Coordinator