Password predictability is one of the most significant challenges to overall online security. Well aware of this trend, hackers often seek to exploit what they assume are the weak passwords of the average computer user. With a little bit of background information, “brute forcing” a simple password is a straightforward undertaking.
How are passwords cracked?
Cybercriminals use computing power to crack passwords with a method known as a brute force attack. With this method, an attacker guesses at the password repeatedly with the help of computer software/scripts. This makes the process automated and essentially effortless for the attacker.
The weaker the password (meaning the easier it is to guess), the quicker an attacker can crack with computing power.
So, how do we combat this?
The problem is password predictability
Passwords can be very easy to guess. Ironically, one factor that contributes to this is one that’s supposed to make passwords safer; the uniform standard most websites impose on users when creating a new password. Typically, sites require a single capital letter, at least 6 charters, numbers and one special character.
Attackers can use this information to guess when and where each character may be using only the predictable tendencies of human users. And because many users create a single password that meets these requirements and use them on multiple sites like Netflix, Facebook and Instagram, getting lucky once can lead to a bonanza for cybercriminals.
Here is an example of a password that would meets the requirements of most websites:
Example1234!
This would be considered “secure” in most cases because it meets the most common internet standard for password creation. Now swap “Example” out for the name of a child or pet, and the easily remembered combination is very likely to be someone’s actual, real-life password. It’s easy for the user to remember, and therefore convenient to use across multiple sites.
Let’s assume a user has a pet named Toby and plug it into the above example format.
Toby1234!
This is not a strong password. Pet’s names, children’s names and birthdays are often easily discoverable, especially by mining social media accounts. An attacker may just need to do a little recon on Facebook to scrounge up a handful of likely options.
Passwords vs. Passphrases
A password is a short character set of mixed digits. A passphrase is a longer string of text making up a phrase or sentence. The important thing to know about passphrases is that, when allowed, they’re far more secure than passwords. The idea that a password should be one word is outdated and retiring it would benefit user security greatly.
A method for devising a passphrase is to simply pick a line from your favorite movie, book or song and mix it with capitals and numbers. If we take Arnold’s famous line “I’ll be back,” we can easily make it into a secure passphrase.
Original: “I’ll be back”
Remove quate marks and spaces, since they can’t be used as password inputs.
Illbeback
Add some capitals: iLLbeBack
Add Numbers: iLL3beBack
And finally, a special character: iLL3beBack$
As a fun test, you can use this password-checking tool to see how long it would take a computer to crack your new creation. How long would it take to crack yours?
For comparison, let’s take one of our simple password examples from above and see how long it would take to crack. We can use Toby1234! (and yes, some people do use such simple passwords).
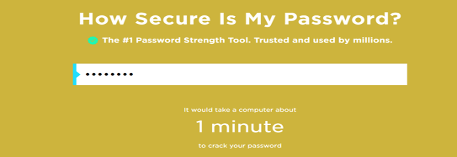
As you can see, it wouldn’t take long at all.
What about our new passphrase iLL3beBack$

I think we’ll be secure for now.
More tips and tricks for password safety
Using a password manger is the most practical way for making passwords more secure. Users tend to gravitate toward the most convenient solution to a given problem, and password managers keep them from having to memorize a series of complex passwords for different sites. The user can automatically save passwords with an internet browser plugin and let autofill features handle the rest.
Here are some other good rules of thumb for password safety:
- Use a password generator
- Use two-factor authentication (2FA) as much as possible
- Don’t reuse passwords
- Be unpredictable in password formatting
Don’t let a predictable password come back to bite you. When made up of easily guessable public information, a weak password can be cracked in minutes. Instead, choose a passphrase or rely on one of the many secure password management tools available on the web today.






