by Blog Staff | May 15, 2013 | Threat Lab
By Cameron Palan and Nathan Collier
Recently, we discovered a new malicious Android application called Android.MouaBot. This malicious software is a bot contained within another basic app; in this case, a Chinese calculator application. Behind the scenes, it automatically sends an SMS message to an auto-reply number which replies back to the phone with a set of commands/keywords. This message is then parsed and the various plugins within the malicious packages are run or enabled.
(more…)
by Blog Staff | May 15, 2013 | Threat Lab
Our sensors just picked up a rogue advertisement served through the Yieldmanager ad network, which exposes users to fake Adobe Flash Player HD ads, ultimately dropping a copy of the potentially unwanted application (PUA)/adware, known as Somoto Better Installer.
More details:
(more…)

by Blog Staff | May 14, 2013 | Threat Lab
By Dancho Danchev
Bitcoin, the digital peer-to-peer based currency, is an attractive target for cybercriminals, who persistently look for new monetization tactics to apply to their massive, but easily generated botnets. Not surprisingly, thanks to the buzz surrounding it, fraudulent Internet actors have begun to look for efficient ways to take advantage of the momentum. A logical question emerges – how are market oriented cybercriminals capitalizing on the digital currency?
Instead of having to personally infect tens of thousands of hosts, some take advantage of basic pricing schemes such subscription-based pricing, and have others do all the infecting, with them securing a decent revenue stream based on a monthly subscription model.
Let’s profile the international underground market proposition, detailing the commercial availability of a stealth Bitcoin miner, feature screenshots of the actual DIY miner generating tool, screenshots provided by happy customers, and perhaps most importantly, MD5s of known miner modifications ‘pushed’ since its first commercial release.
More details:
(more…)

by Blog Staff | May 13, 2013 | Threat Lab
By Dancho Danchev
On the majority of occasions, Cybercrime-as-a-Service vendors will sell access to malware-infected hosts to virtually anyone who pays for them, without bothering to know what happens once the transaction takes place.
A newly launched E-shop for malware-infected hosts, however, has introduced a novel approach for calculating the going rate for the hacked PCs. Basically, they’re selling actual malicious binary “executions” on the hosts that the vendor is managing, instead of just selling access to them.
A diversified international underground market proposition? Check. A novel approach to monetize malware-infected hosts? Not at all. Let’s profile the actual market proposition, and discuss in-depth why its model is flawed by design.
More details:
(more…)

by Blog Staff | May 10, 2013 | Threat Lab
By Dancho Danchev
In 2013, Liberty Reserve and Web Money remain the payment method of choice for the majority of Russian/Eastern European cybercriminals. Cybercrime-as-a-Service underground market propositions, malware crypters, R.A.Ts (Remote Access Trojans), brute-forcing tools etc. virtually every underground market product/service is available for purchase through the use of these ubiquitous virtual currencies.
What’s the situation on the international underground market? Next to accepting PayPal and consequently all major credit cards, we’ve been observing an increase in market propositions starting to accept Bitcoins. Is this a trend or a fad, and does the currency’s P2P model about to be embraced ecosystem-wide due to its (current) pseudo-anonymous model?
Let’s find out.
More details:
(more…)

by Blog Staff | May 10, 2013 | Threat Lab
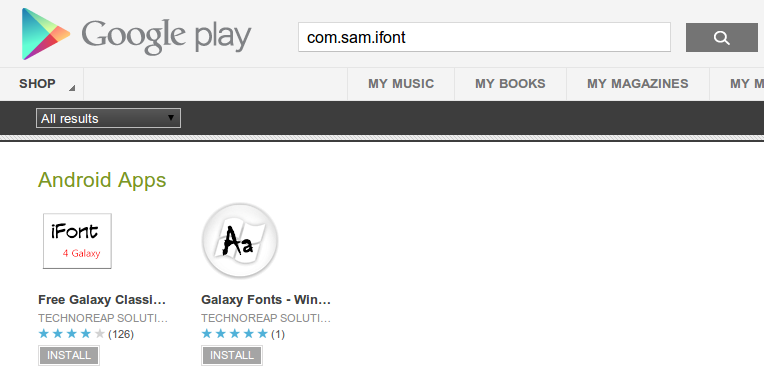
We have found a new threat we are calling Android.TechnoReaper. This malware has two parts: a downloader available on the Google Play Market and the spyware app it downloads. The downloaders are disguised as font installing apps, as seen below:
 (more…)
(more…)

by Blog Staff | May 9, 2013 | Threat Lab
By Dancho Danchev
Cybercriminals are currently spamvertising tens of thousands of bogus emails impersonating New York State’s Department of Motor Vehicles (DMV) in an attempt to trick users into thinking they’ve received an uniform traffic ticket, that they should open, print and send to their town’s court.
In reality, once users open and execute the malicious attachment, their PCs will automatically join the botnet operated by the cybercriminal/cybercriminals behind the campaign.
More details:
(more…)

by Blog Staff | May 8, 2013 | Threat Lab
By Dancho Danchev
Kindle users, watch what you click on!
Cybercriminals are currently mass mailing tens of thousands of fake Amazon “You Kindle E-Book Order” themed emails in an attempt to trick Kindle users into clicking on the malicious links found in these messages. Once they do so, they’ll be automatically exposed to the client-side exploits served by the Black Hole Exploit Kit, ultimately joining the botnet operated by the cybercriminal/cybercriminals that launched the campaign.
More details:
(more…)

by Blog Staff | May 7, 2013 | Threat Lab
Over the past 24 hours, we’ve intercepted yet another spam campaign impersonating Citibank in an attempt to socially engineer Citibank customers into thinking that they’ve received a Merchant Billing Statement. Once users execute the malicious attachment found in the fake emails, their PCs automatically join the botnet operated by the cybercriminal/cybercriminals.
More details:
(more…)

by Blog Staff | May 6, 2013 | Threat Lab
Need a compelling reason to perform search engine reconnaissance on your website, for the purpose of securing it against eventual compromise? We’re about to give you a good one.
A new version of a well known mass website hacking tool has been recently released, empowering virtually anyone who buys it with the capability to efficiently build “hit lists” of remotely exploitable websites for the purpose of abusing them in a malicious or fraudulent fashion. Relying on Google Dorks for performing search engine reconnaissance, the tool has built-in SQL injecting options, the ability to add custom exploits, a proxy aggregation function so that no CAPTCHA challenge is ever displayed to the attacker, and other related features currently under development.
More details:
(more…)