by Blog Staff | Dec 22, 2009 | Industry Intel, Threat Lab












 Here’s a mind-bender for you to ponder over the holidays: What do diva musician Beyonce, the massively-multiplayer game World of Warcraft, the anime series Naruto, and Libertarian politician (and failed presidential candidate) Ron Paul have in common?
Here’s a mind-bender for you to ponder over the holidays: What do diva musician Beyonce, the massively-multiplayer game World of Warcraft, the anime series Naruto, and Libertarian politician (and failed presidential candidate) Ron Paul have in common?
I couldn’t guess what you might come up with, but we’ve found a drive-by download attack that delivers malware, using these disparate icons as a hook to convince Web surfers to click malicious links. The hack attempt was discovered by a Threat Research Analyst who also happens to be a Ron Paul fanatic (and I do mean fanatic — that’s a photo of his truck parked out back). While doing his daily search for Ron’s latest words of wisdom, he encountered a cleverly crafted campaign to manipulate search results which originated with Twitter feeds suddenly lighting up with links supposedly pointing to YouTube videos.
A large number of Twitter accounts tweeted messages like “YOUTUBE RON PAUL – BEST NEW VIDEO – WATCH NOW” or “YOUTUBE NARUTO CHAT ROOM 1 | BEST NEW VIDEO | WATCH NOW” — you get the idea — all within a short amount of time. Each of those screaming teasers was accompanied by a URL shortened using the bit.ly (and to a lesser extent, TinyURL.com) service; The bit.ly URLs pointed to a (now deleted) hidden subdirectory on the website of Stage Time magazine, an online only, stand-up-comedy industry publication (neither YouTube nor Stage Time was, knowingly, involved in the hack — they were victims as well). And the many first-time visitors to that site found their computers in a world of hurt shortly after following one or another of those links.
 The malicious pages on Stage Time hosted PHP scripts that pushed down several new malware samples; The scripts exploited security vulnerabilities in older versions of Adobe Flash and Adobe Reader, loading maliciously crafted SWF and PDF files in order to force the browser to pull down and run malicious executables which had virtually no detection across the spectrum of antivirus vendors. Some of these samples were droppers, others were downloaders; In either case, the drive-by payloads left the PC in a very bad state.
The malicious pages on Stage Time hosted PHP scripts that pushed down several new malware samples; The scripts exploited security vulnerabilities in older versions of Adobe Flash and Adobe Reader, loading maliciously crafted SWF and PDF files in order to force the browser to pull down and run malicious executables which had virtually no detection across the spectrum of antivirus vendors. Some of these samples were droppers, others were downloaders; In either case, the drive-by payloads left the PC in a very bad state.
Drive-by downloads such as these serve to illustrate a point I can’t emphasize enough: No matter how careful you might think you are, one wrong click can lead to an infection. In the case of this drive-by, the malicious website attempted to load first an Adobe Flash video, then a PDF file, which tricked the browser into downloading more malware. Now more than ever, browser plug-ins like Flash and Adobe Reader need to be kept up to date. For additional protection, you can disable Javascript in Adobe Reader; in this case, it would have stopped the initial infection in its tracks.
(more…)

by Blog Staff | Dec 15, 2009 | Industry Intel, Threat Lab












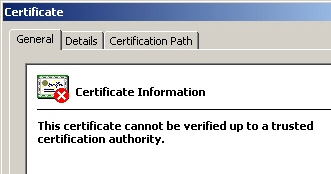
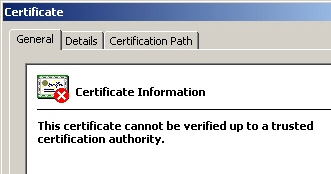 Security Websites are buzzing with news that a new zero-day exploit against Adobe Reader and Acrobat is circulating today, causing computers to become infected with malware simply by visiting certain Web pages. While the exploit itself is worthy of note, nobody is talking about the payload it downloads: It installs a trio of files dressed up to look like Windows system files which have been digitally signed with a security certificate supposedly issued by Microsoft. The digital signature gives the casual user the impression that the two signed files — an executable and a DLL both named “LNETCPL” — are legitimate Microsoft components.
Security Websites are buzzing with news that a new zero-day exploit against Adobe Reader and Acrobat is circulating today, causing computers to become infected with malware simply by visiting certain Web pages. While the exploit itself is worthy of note, nobody is talking about the payload it downloads: It installs a trio of files dressed up to look like Windows system files which have been digitally signed with a security certificate supposedly issued by Microsoft. The digital signature gives the casual user the impression that the two signed files — an executable and a DLL both named “LNETCPL” — are legitimate Microsoft components.
The fake certificates appear in the properties sheets of both the installer and two of the three executable payloads dropped by the installer. One giveaway is that the sheet identifies the signer as Microsoft but lacks both an email address and a time stamp. Legitimate system files digitally signed by Microsoft identify the signer as Microsoft Corporation and always have a time stamp. The bogus signatures are identified as invalid, but only when you click the Details button on the Properties Sheet’s Digital Signatures tab.
A legitimate Microsoft-signed file is issued by the “Microsoft Code Signing PCA” certificate authority, and will also display a countersignature from Verisign; The fakes have no countersignature, and appear to have been issued by “Root Agency” — a made up name for a nonexistent certificate authority the malware creators are using to generate these files. In fact, the malware creators may actually be using Microsoft’s own Certificate Creation Tool (which is supposed to be used for testing) to facilitate generating these signed files.
While we’ve seen a number of digitally signed files come through our research queue over the years, authors of Trojan horse apps rarely go to the trouble of digitally signing files in this way. It’s not clear why they would be digitally signing files, but clearly the person or people behind this are up to no good. We’ve published a new definition to remove both the installer and these payload files; Trojan-Certispaz will be available to help our customers clean up infections in our next definitions update.
(more…)

by Blog Staff | Dec 15, 2009 | Industry Intel, Threat Lab
By Jeff Horne












 On December 11, 2009, users of Twitter submitted questions to Webroot’s Director of Threat Research, Jeff Horne, as part of a live Q&A session. Webroot’s Twitter followers asked questions about connecting safely to the Internet while traveling during the holidays. A variety of questions came in live, with some others through direct messages in advance, and one non-twitter user asked a question via Webroot’s Facebook page. The interview was tracked using the #webroot hashtag, which has been omitted from the tweets to make them easier to read. We’ve posted a transcript of the Q&A on the following page.
On December 11, 2009, users of Twitter submitted questions to Webroot’s Director of Threat Research, Jeff Horne, as part of a live Q&A session. Webroot’s Twitter followers asked questions about connecting safely to the Internet while traveling during the holidays. A variety of questions came in live, with some others through direct messages in advance, and one non-twitter user asked a question via Webroot’s Facebook page. The interview was tracked using the #webroot hashtag, which has been omitted from the tweets to make them easier to read. We’ve posted a transcript of the Q&A on the following page.
(more…)

by Blog Staff | Dec 11, 2009 | Industry Intel, Threat Lab












 The gang of malware distributors who are currently flooding the Internet with bogus Facebook “Update Tool,” CDC “H1N1 Flu Vaccination Profile,” and IRS “Tax Statement” emails and Web pages are at it again — this time, targeting Visa with a fake email alert that leads to a page hosting not only a Trojan-Backdoor-Zbot installer, but that performs a drive-by download as well. This is the second time in less than a month that malware distributors have targeted Visa; Just before Thanksgiving, we saw a similar scam involving links to bunk Verified By Visa Web pages.
The gang of malware distributors who are currently flooding the Internet with bogus Facebook “Update Tool,” CDC “H1N1 Flu Vaccination Profile,” and IRS “Tax Statement” emails and Web pages are at it again — this time, targeting Visa with a fake email alert that leads to a page hosting not only a Trojan-Backdoor-Zbot installer, but that performs a drive-by download as well. This is the second time in less than a month that malware distributors have targeted Visa; Just before Thanksgiving, we saw a similar scam involving links to bunk Verified By Visa Web pages.
I’d say it’s ironic that malware distributors are using fraudulent transaction warnings as a method to infect users with a keylogger capable of stealing their credit card information when the victim enters it into a shopping Web site, but Visa doesn’t issue these kinds of warnings—the Visa-card-issuing bank warns customers of suspected fraud themselves, and they never do anything with that level of urgency via email.
Once you click through to the Web page, you end up on a page dressed up in its holiday best to look like an official Visa Web site. The top of the page even has your credit card number printed on it! Well, not the whole credit card number. It just prints the number “4XXX XXXX XXXX XXXX” (then goes on to say “to protect your private information, part of the card number is hidden with X’s“). How considerate.
Of course, all bank-issued Visa card numbers in the US are sixteen digits long and begin with a “4” so it’s actually a pretty good guess that the Visa in your wallet right now looks just like that.
The bogus Web page even sports a URL that begins with “reports.visa.com,” followed by a random six- to eight-character domain name, but there the similarities end. The servers hosting the fraudulent pages are based in foreign countries where you wouldn’t expect a major company like Visa to operate its Web presence from, such as Morocco, on networks known to harbor both Koobface and Zbot Trojans. The text on the page claims to have a downloadable transaction report for your card. If you haven’t already guessed, the “statement” is just an installer for the Trojan.
(more…)

by Blog Staff | Dec 10, 2009 | Industry Intel, Threat Lab












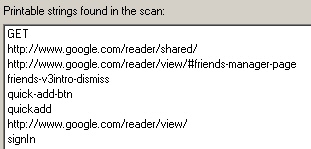
 Over the past several months, we’ve seen Koobface steadily progress in its ability to infect systems with malware. In our latest tests, we’ve found that the most recent version of this social-networm has a few new holiday-themed tricks up its sleeve. Among those tricks are a new, improved “captcha breaker” utility; A tool to check whether you have a Google and/or a Blogspot account (and, if not, it creates a new Google account); And a tool designed to create Google Reader pages on the fly, which the worm then uses to post malicious code. Those Google Reader accounts then end up linked in private messages and wall-to-wall posts on a variety of social network sites.
Over the past several months, we’ve seen Koobface steadily progress in its ability to infect systems with malware. In our latest tests, we’ve found that the most recent version of this social-networm has a few new holiday-themed tricks up its sleeve. Among those tricks are a new, improved “captcha breaker” utility; A tool to check whether you have a Google and/or a Blogspot account (and, if not, it creates a new Google account); And a tool designed to create Google Reader pages on the fly, which the worm then uses to post malicious code. Those Google Reader accounts then end up linked in private messages and wall-to-wall posts on a variety of social network sites.
The Koobface-generated Google Reader pages have been floating around for a little while now, but I’d never seen the worm in action. What I found fascinating was that I could observe the process of the worm creating a new Google account on my testbed.
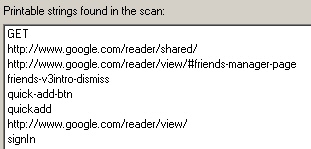 In order to create the Google account, it downloaded and ran four new applications: “v2googlecheck” simply looks at your browser cookies to determine whether you already have a Google account; “v2newblogger” creates a new account if one doesn’t already exist; “v2captcha” prompts the user of the infected machine to enter a captcha into a dialog box that looks like a Windows login dialog (in order to complete the account creation); and “v2reader,” which creates the new page, and passes that information to the worm.
In order to create the Google account, it downloaded and ran four new applications: “v2googlecheck” simply looks at your browser cookies to determine whether you already have a Google account; “v2newblogger” creates a new account if one doesn’t already exist; “v2captcha” prompts the user of the infected machine to enter a captcha into a dialog box that looks like a Windows login dialog (in order to complete the account creation); and “v2reader,” which creates the new page, and passes that information to the worm.
Once the Google account is created, it then uses that account to generate a new, malicious Google Reader page.
(more…)

by Blog Staff | Dec 4, 2009 | Industry Intel, Threat Lab












 A week since the file-sharing clearinghouse Mininova changed its business model and deleted links to copyrighted material being shared over the peer-to-peer Bittorrent network, malware distributors continue to exploit the confusion as people who download movies, TV shows, and other shared files seek out new sources for those files.
A week since the file-sharing clearinghouse Mininova changed its business model and deleted links to copyrighted material being shared over the peer-to-peer Bittorrent network, malware distributors continue to exploit the confusion as people who download movies, TV shows, and other shared files seek out new sources for those files.
As a torrent search engine, Mininova had to deal with a significant number of malicious torrents posted to their site each day. The service had a reputation for rapidly deleting torrents which led to Trojaned applications, or maliciously crafted media files that lead file-sharing enthusiasts into infections. But in the ensuing frenzy to find a new home, torrent downloaders may encounter more than they bargained for.
 In a desperately unscientific test of torrents retrieved from several of the sites that have popped up to replace Mininova, we retrieved a significant number of malicious Windows Media Video files, as well as torrents that contain a password-protected archive (supposedly containing the video file) and malicious HTML file which the malware distributor claims contains the password, but actually leads the viewer into a morass of advertisements. The WMV videos spawn a “License Acquisition” window in Windows Media Player that prompts potential viewers to download a video codec installer; The file is, in fact, a dangerous Trojan.
In a desperately unscientific test of torrents retrieved from several of the sites that have popped up to replace Mininova, we retrieved a significant number of malicious Windows Media Video files, as well as torrents that contain a password-protected archive (supposedly containing the video file) and malicious HTML file which the malware distributor claims contains the password, but actually leads the viewer into a morass of advertisements. The WMV videos spawn a “License Acquisition” window in Windows Media Player that prompts potential viewers to download a video codec installer; The file is, in fact, a dangerous Trojan.
We used the torrent search engines’ own lists of “most popular” search terms to pull down the malicious files. Top among the popular searches on many sites was the phrase “new moon” or “Twilight” — a reference to the recently released teen-vampire-heartthrob cinematic sparklefest. The people who posted these malicious torrents claimed that they contain a video of the movie, ripped from a DVD screener — the discs that film studios distribute to members of the Academy, who need to watch the movies prior to casting their Oscar ballots. Screeners typically pop up on torrent sites around the end of the year.
(more…)

by Blog Staff | Dec 1, 2009 | Industry Intel, Threat Lab












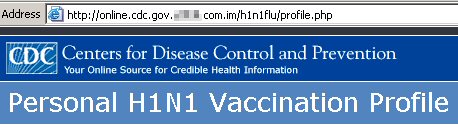
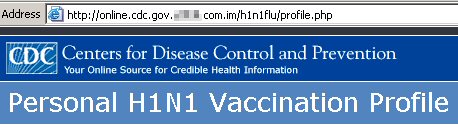 The newest victim of the faux–Web–sites-posing-as-government-pages scam is the Centers for Disease Control and Prevention. In the same vein as fake pages supposedly hosted on the Web servers of the IRS, FDIC, and other organizations, we’re seeing a new scam to infect computers with Trojan-Phisher-Zbot that pretends to be a “Personal H1N1 Vaccination Profile.”
The newest victim of the faux–Web–sites-posing-as-government-pages scam is the Centers for Disease Control and Prevention. In the same vein as fake pages supposedly hosted on the Web servers of the IRS, FDIC, and other organizations, we’re seeing a new scam to infect computers with Trojan-Phisher-Zbot that pretends to be a “Personal H1N1 Vaccination Profile.”
As with the previous scams, dozens of Web servers are involved. The URLs involved in the scheme all begin with the “http://online.cdc.gov” — the “online.” subdomain is not used by the CDC — followed by a six- to seven-character random domain name and a non-.gov top-level domain.
The text of the page reads
Your Personal H1N1 Vaccinating Profile is an electronic document, which contains your name, your contact details and your medical data (what kind of illnesses you have sustained in your childhood or what kind of allergy you have to some certain drug). All instructions you need are included in the archive below
There’s a link labeled “Download Archive (130Kb)” that, when you click it, pulls down the Zbot installer from the malicious server. The file name is vacc_profile.exe. Please don’t execute this file if you happen to download it.
This particularly pernicious program appears to have a perspicacity for FTP passwords. It appears to target several popular Windows FTP and SCP client applications, including SmartFTP, WSFTP, FlashFXP, CoreFTP, FTP Commander, Total Commander, WinSCP, FileZilla, and FAR Manager. If you typically save your FTP credentials in these applications, Zbot will seek them out.
Webroot has implemented procedures to warn you when you visit one of these sites. Anyone using our software who has their File System Shield active will see a warning if you follow a malicious link. If you get this warning message, close the browser window, perform a full sweep of your computer — and change the passwords to any FTP accounts that have been saved in any of the client apps listed above.


by Blog Staff | Nov 27, 2009 | Industry Intel, Threat Lab












 Now that the turkey and pumpkin pie has settled, and everyone’s gotten a good night’s sleep, shoppers are busily hustling the Web for the best deals. I’ve been doing the same thing, and wanted to share some of my tips that may help you avoid becoming snared in the most prolific cyberscam of the moment: fake virus alert messages (otherwise known as fakealerts).
Now that the turkey and pumpkin pie has settled, and everyone’s gotten a good night’s sleep, shoppers are busily hustling the Web for the best deals. I’ve been doing the same thing, and wanted to share some of my tips that may help you avoid becoming snared in the most prolific cyberscam of the moment: fake virus alert messages (otherwise known as fakealerts).
For months, the perpetrators of this fraud have been honing their skills at targeting malicious web pages to rise in search results for whatever is in the popular zeitgeist-of-the-moment. Victims experience a computer that appears to be out of control, seemingly unable to do anything but download whatever application the fakealert forces upon them.

A typical “warning” from a malicious fakealert
Take a look at this video. Earlier in the week I tried searching for news about Black Friday or deals on the toy that appears to be the Tickle Me Elmo of 2009, the hard to find Zhu Zhu Pets. What I found were a flood of fakealert sites mixed in with the legitimate search results.
[vimeo 7825517]
The good news is, it’s not hard to avoid these fakealert sites, but you have to be an alert Web surfer, and carefully scrutinize the results before you click a link. Read on for my top six tips to shop online safely this Black Friday, Cyber Monday, or anytime this holiday season.
(more…)

by Blog Staff | Nov 25, 2009 | Industry Intel, Threat Lab












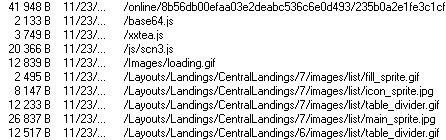
 In general, the use of fakealerts — those bogus warnings that look like your PC has started some sort of antivirus scan on its own, then predict imminent doom if you don’t buy some snake oil product right this minute — is on the rise. Fakealerts constitute a particularly effective social engineering trick, earning the makers of bogus, ineffective “antivirus” programs millions of dollars (and the scorn of victims) in the process. So it should come as no surprise that the fakealerts themselves have gone through some technological advances in the past year.
In general, the use of fakealerts — those bogus warnings that look like your PC has started some sort of antivirus scan on its own, then predict imminent doom if you don’t buy some snake oil product right this minute — is on the rise. Fakealerts constitute a particularly effective social engineering trick, earning the makers of bogus, ineffective “antivirus” programs millions of dollars (and the scorn of victims) in the process. So it should come as no surprise that the fakealerts themselves have gone through some technological advances in the past year.
In the past few months, the fakealert-makers have slowly been migrating their techniques to a new platform: The browser. As recently as six months ago, the majority of fakealerts we saw were generated by small Trojan Horse applications running on a victim’s PC. Today, most fakealerts we see simply reshape the browser to mimic the appearance of a generic antivirus application.
It makes good economic sense for the creators of fakealerts to do this. The Windows application fakealerts only run on Windows (obviously). Like all Windows software, fakealert apps subject to being blocked by both the operating system (which, like the fakealerts themselves, prompts users with warnings in dialog boxes), by real-time detection mechanisms in legitimate antivirus software, and/or by savvy users themselves.
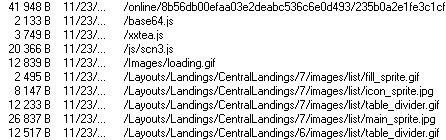
One typical load-sequence for the components of a scripted fakealert
Using a scripting technology such as Javascript to reproduce the “fakealert experience” is a natural extension of the success of fraudulent, rogue antivirus products. After all, a fakealert is no more than an elaborate performance for the targeted victim — the goal of the fakealert is simply to convince the victim to download and run a file, typically a rogue antivirus product. Javascript can run in virtually every browser and operating system (save for special cases, like the Firefox browser with the NoScript Add-On installed).
Scripts such as these bypass most traditional malware protection because, in essence, there is no malware installed until the victim installs it his- or herself. Unlike a static binary executable, the contents of a script can be tweaked, on the fly, to maximize effectiveness (or just to change the name of the fraudulent product). And the scripts themselves which make up the Web fakealert experience are highly obfuscated, which makes them more challenging for automated systems to block.
In the course of researching a new malware sample unrelated to fakealerts — an installer of Trojan-Downloader-Dermo on a page purportedly offering an update to Windows Media Player — I observed one common fakealert script as it ran soon after the testbed PC was infected. I was able to reconstruct its modus operandi.
(more…)

by Blog Staff | Nov 20, 2009 | Industry Intel, Threat Lab
By Gerhard Eschelbeck












It’s been a busy year in Internet security — cybercriminals were crafty and creative while we security vendors worked hard to stay a step ahead. Let’s take a look back at the biggest security trends of 2009, and at predictions for what’s ahead in 2010.
2009 — The Year in Review
Conficker. Targeted at enterprise networks but also crossing over to individuals who could bring it home on a USB stick, Conficker generated a lot of media discussion which drove confusion among consumers and concern among IT admins. Conficker renewed the public’s focus on Internet security, at a time when the threat landscape was growing more complex.
Consolidation. In 2009, we saw Symantec acquire MessageLabs, McAfee acquire MX Logic, Cisco acquire ScanSafe, M86 acquire Finjan, and Barracuda acquire Purewire. Many large vendors have track records of poorly integrating smaller companies after acquiring them for a key piece of technology. At the endof this year, we’re left asking, will true innovation now only be possible among the few independent vendors remaining?
Social Media. Concerned about productivity and infection, enterprises struggled with corporate usage policies of social networks — media that is now ubiquitous, and also integral to communicating with and understanding customers. Meanwhile, consumers adopted social networks en masse, providing cybercriminals with a huge target for harvesting personal data via Koobface and various spam campaigns.
The Cloud. While the definition of “cloud computing” and “in the cloud” held different meanings in 2009, enterprises continued to adopt security as a service for its easier, faster, more efficient and cost-effective distribution of security updates. Vendors extended their SaaS-based technology into their consumer solutions after proven success in the enterprise market — an exciting convergence of technologies.
Malware Trends. We saw a changing Internet user who is highly mobile, presenting a new set of attack vectors for malware authors. We also saw increasingly sophisticated malware — cybercriminals using email to distribute malicious Web links and manipulating SEO by programming malicious links near the top of search results for popular news stories — and an explosion of social engineering tactics employing fake security alerts and rogue AV products with new variants launched seemingly in real-time.
2010 — The Year Ahead
Threat Landscape. The malware attacks of today are different than in recent years. Hybrid malware, combining the use of Web and email to carry out sophisticated attacks, will become even more prevalent in 2010. Narrowly targeted malware, which requires the presence of specific applications or data to engage in malicious activity, will also be on the rise. Finally, the increasing “real-feel” of phishing sites and emails — as evidenced by a recent Verified by Visa scam — are keeping security vendors, IT directors and consumers on their toes.
Social Media. Attacks on social networks will continue to increase in volume and scope, targeting communities such as Facebook and Twitter as well as those we’ll see emerge in the coming year. Social networks present a very good ROI for cybercriminals using them as a platform for perpetrating URL-based attacks. This trend will intensify — through shortened links, user-generated content, videos, and so forth. Friend, Follower, Tweeter, beware.
The Cloud Grows. We predict cloud computing as the computing platform, such as the Amazon data center model, will be the next generation of the Internet. Computing will become like a utility, similar to how we use electricity today. We will pay for what we use; the PC will become the visualization tool we look into for applications in the cloud. More cloud computing platforms will become available as we capitalize on this economical, scalable model.
While this may seem like a daunting list of threats and predictions, the good news is, the security industry has never been stronger: The level of innovation, the raised awareness, the healthy competition among vendors — together make for an optimistic outlook. We at Webroot wil continue to work hard to create effective technologies to make the Internet and the cloud a safe place for consumers and businesses alike.


 Here’s a mind-bender for you to ponder over the holidays: What do diva musician Beyonce, the massively-multiplayer game World of Warcraft, the anime series Naruto, and Libertarian politician (and failed presidential candidate) Ron Paul have in common?
Here’s a mind-bender for you to ponder over the holidays: What do diva musician Beyonce, the massively-multiplayer game World of Warcraft, the anime series Naruto, and Libertarian politician (and failed presidential candidate) Ron Paul have in common? The malicious pages on Stage Time hosted PHP scripts that pushed down several new malware samples; The scripts exploited security vulnerabilities in older versions of Adobe Flash and Adobe Reader, loading maliciously crafted SWF and PDF files in order to force the browser to pull down and run malicious executables which had virtually no detection across the spectrum of antivirus vendors. Some of these samples were droppers, others were downloaders; In either case, the drive-by payloads left the PC in a very bad state.
The malicious pages on Stage Time hosted PHP scripts that pushed down several new malware samples; The scripts exploited security vulnerabilities in older versions of Adobe Flash and Adobe Reader, loading maliciously crafted SWF and PDF files in order to force the browser to pull down and run malicious executables which had virtually no detection across the spectrum of antivirus vendors. Some of these samples were droppers, others were downloaders; In either case, the drive-by payloads left the PC in a very bad state.