In a clear demonstration of low QA (Quality Assurance) applied to an ongoing malicious spam campaign, the cybercriminals behind the recently profiled ‘Cybercriminals spamvertise tens of thousands of fake ‘Your Booking Reservation at Westminster Hotel’ themed emails, serve malware‘ campaign, have launched yet another spam campaign.
Despite the newly introduced themed attempting to trick users into thinking that they’ve received a ‘iGO4 Private Car Insurance Policy Amendment Certificate‘, the cybercriminals behind it didn’t change the malicious binary from the previous campaign.
More details:
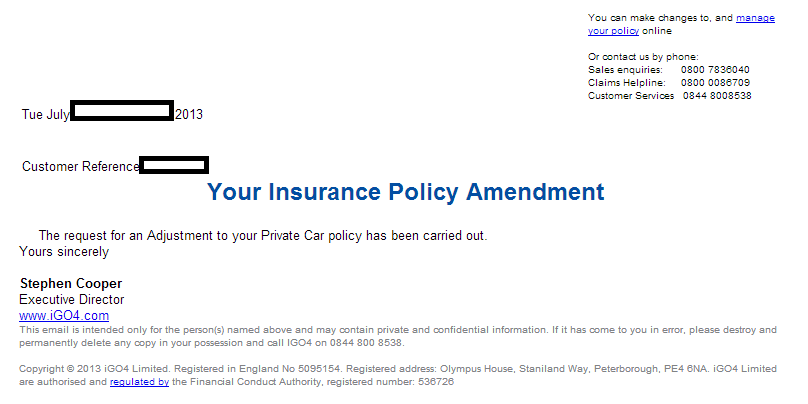
Sample screenshot of the spamvertised email:
Detection rate for the malicious attachment, which has naturally improved over the past 24 hours: MD5: 7eed403cfd09ea301c4e10ba5ed5148a – detected by 27 out of 47 antivirus scanners as Trojan-PSW.Win32.Tepfer.nprd; TrojanDownloader:Win32/Dofoil.R.
The sample continues phoning back to hxxp://62.76.178.178/fexco/com/index.php (62-76-178-178.clodo.ru), AS48172.
Webroot SecureAnywhere users are proactively protected from this threat.
You can find more about Dancho Danchev at his LinkedIn Profile. You can also follow him on Twitter.