Over the last two months, we’ve been closely monitoring — and proactively protecting from — the malicious campaigns launched by cybercriminals who are no strangers to the concept of social engineering topic rotation. Their purpose is to extend a campaign’s life cycle, or to generally increase a botnet’s infected population by spamming out tens of thousands of fake emails, exposing users to malicious software. The most recent campaign launched by the same cybercriminal(s), is once again impersonating T-Mobile U.K in an attempt to trick mobile users into thinking that they’ve received a legitimate MMS Gallery notification. In reality though, once the attachment is executed, the victim’s PC will automatically join the botnet operated by the cybercriminal(s) behind the campaign, ultimately undermining the confidentiality and integrity of the host.
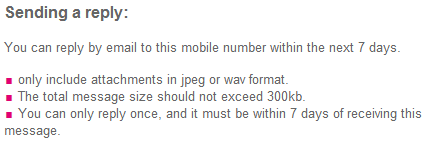
Sample screenshot of the spamvertised email:
Detection rate for the spamvertised attachment: MD5: bff8af7432ced6e574e85d9241794f80 – detected by 8 out of 47 antivirus scanners as Trojan.Zbot; W32/Trojan2.OADJ.
Once executed, the sample phones back to networksecurityx.hopto.org. Go through related assessments of campaigns known to have been launched by the same cybercriminal(s), also phoning back to the same C&C server:
- ‘T-Mobile MMS message has arrived’ themed emails lead to malware
- Spamvertised T-Mobile ‘Picture ID Type:MMS” themed emails lead to malware
- U.K users targeted with fake ‘Confirming your Sky offer’ malware serving emails
- Cybercriminals spamvertise tens of thousands of fake ‘Sent from my iPhone’ themed emails, expose users to malware
- Fake WhatsApp ‘Voice Message Notification/1 New Voicemail’ themed emails lead to malware
Related malicious MD5s that are known to have phoned back to the same C&C server over the last 24 hours:
MD5: 334caadd87414cec33aeed2cd5660047
MD5: 758427f8dbca63c5996732d53af9d437
MD5: 3c2c403e4e13634e5ff16ff0d5958f4a
MD5: 8d8cdb8e019f6512ec577b65aacd8811
MD5: 292b15c5c38812d99ee5b71488d4da84
MD5: e53efd2f8cf233ebdaff75547a7afe2a
MD5: d20943554561953f5f495f2497fb6ec7
MD5: 9c26ccbd415da8c9eaf99e347ffd46bf
MD5: 32d86dcf3dae6ccf298745293992c776
MD5: 6a1d9111dde1c54e06937594642d1c96
MD5: 555aba5436e4b7c197b705803063528f
MD5: f5257fa2d6948f14ec92c77f45b0bff9
MD5: f3aa65b13c7d6552bf6e5c40f502194e
MD5: ef1d8ff8ea198e4e601e90f645acbfdb
MD5: ee9f046ff9cce896faf3cd9094a14100
MD5: f1b3ab7ecc9268d8ed2e2afeafaa34ab
MD5: ed43d198b52ff644c0a38e45def54ce6
MD5: ea1a91d504c8ccffcd2a22ea9a8e9f82
MD5: e9a5b9e3d0b69248dd3f2e769ce6f9eb
MD5: deac0b055af271d8f30bba759a18bae4
We’ve also observed two newly introduced C&C servers within these samples, namely, dnshosting1.ws – 185.26.120.124 and 178.32.173.85.
Webroot SecureAnywhere users are proactively protected from these threats.