Recently we’ve seen a big change in the encrypting ransomware family and we’re going to shed light on some of the newest variants and the stages of evolution that have led the high profile malware to where it is today. For those that aren’t aware of what encrypting ransomware is, its a crypto virus that encrypts all your data from local hard drives, network shared drives, removable hard drives and USB. The encryption is done using an RSA -2048 asymmetric public key which makes decryption without the key impossible. Paying the ransom will net you the key which in turn leads to getting your data back.
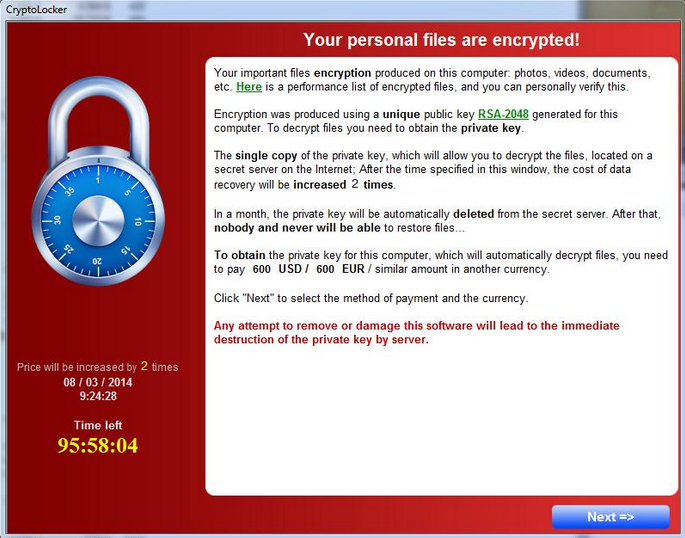
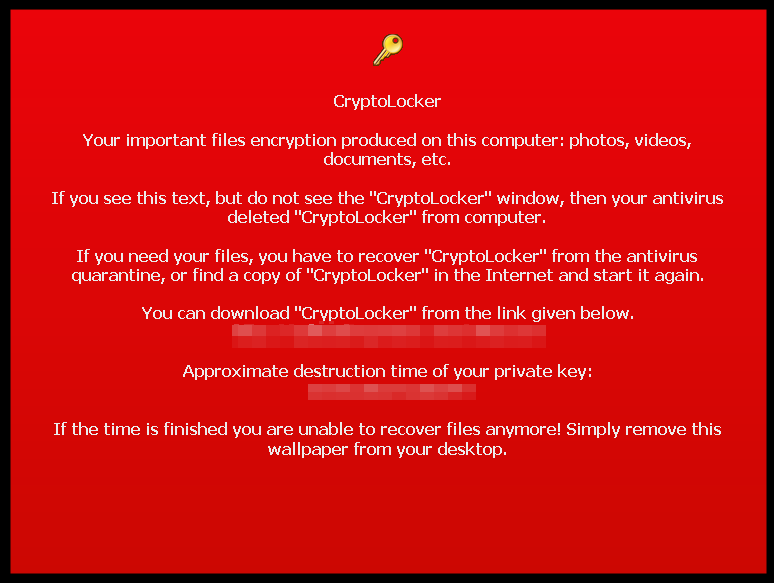
Cryptolocker
In it’s first evolution of what we know as “Cryptolocker” the encryption key was actually stored on the computer and the victim, with enough effort could retrieve said key. Then you could use tools submitted on forums to put in your key and decrypt all your data without paying the ransom. In future improvements malware authors made sure that the only place the key was stored was on a secure server so that you were forced to pay. However, more often than not the malicious dropper didn’t delete the VSS (Volume Shadow Service) and victims still had the option to manually restore files from a previous date using programs like Shadow explorer (OS drive only). For those that don’t know what the VSS is it’s a restorative feature that is included in XP sp2 and later versions of windows. Essentially it is a technology that allows taking manual or automatic backup copies of data and is related to system restore. In newer variants of Cryptolocker the VSS is almost always deleted at deployment. Malware authors also give the victim a special extended period of time to get their files they waited past the deadline, but the price usually doubles of triples.
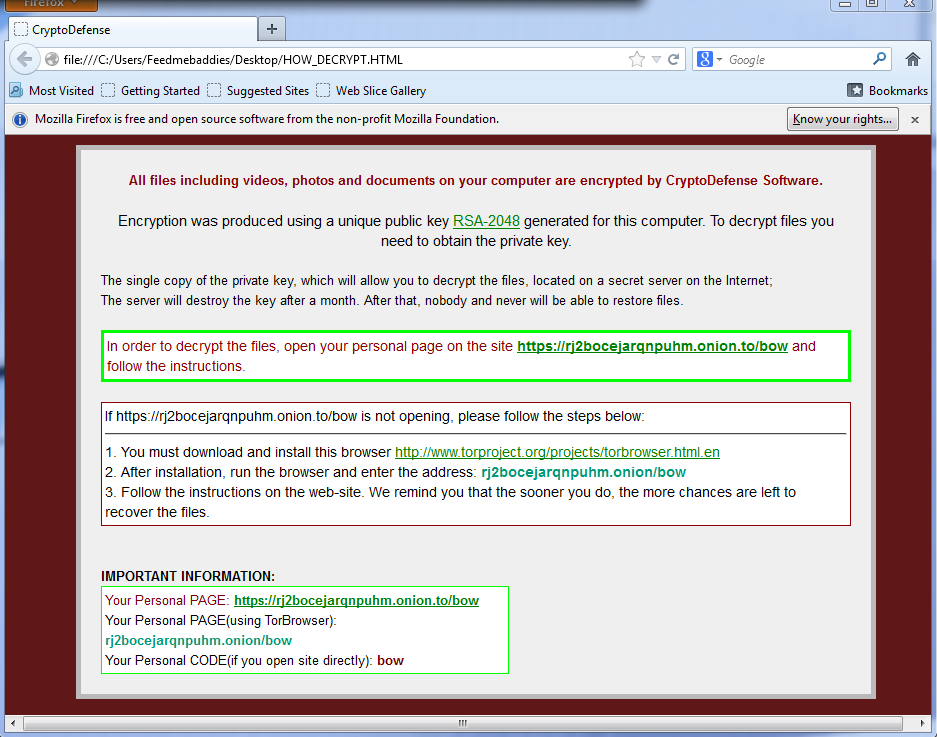
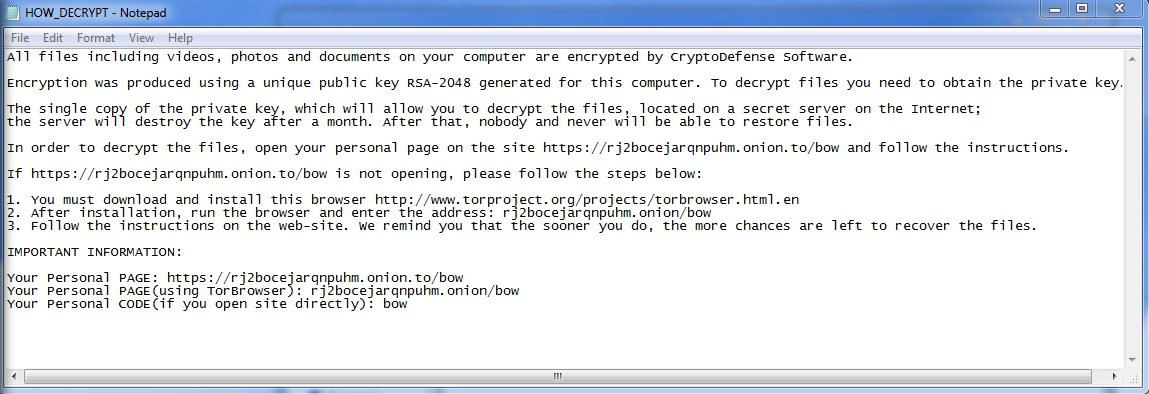
CryptoDefense
In one of the more recent variants of encryption ransomware dubbed “CryptoDefense” it no longer has a graphical user interface (GUI). Instead the malware will just open a webpage after encryption and leave a text file at every directory that was encrypted. The instructions to get the key to decrypt your files have you install anonymous tor or other layered encryption browsers so you can pay them directly and securely. this enables malware authors to circumvent a portion of the Zeus fraud avoid the need for money mules (middle man) and increasing the percentage of profit.
DirCrypt
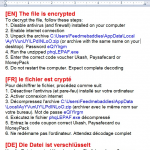
In this most recent change in encrypting ransomware. Instead of going after various file extensions, all files are encrypted into RTF documents with a *.enc.rtf extension. This one really blind sides the victim as you’ll get no pop up GUI or web page once encryption completes; you have to open one of your documents to find that it was encrypted. All documents will have the same content similar to what is shown. One big improvement that is quite nasty for victims is the encryption is no longer a static one time deal. This variant will actively seek out and encrypt any new or modified files written to drives. We noticed while testing a collected sample that when we attempted to save screenshots, that it immediately encrypted them. We expect future encrypting ransomware variants to include these tactics as the evolution continues.
Webroot SecureAnywhere users are proactively protected from the variants shown. We are constantly working with the evolving threat landscape to protect against the newest variants as they progress.
Webroot support is always more than happy to help with removal and any questions regarding infections.











Fantastic article!