Whenever a user gets socially engineered, they unknowingly undermine the confidentiality and integrity of their system, as well as any proactive protection they have in place, in exchange for quick gratification or whatever it is they are seeking. This is exactly how unethical companies entice unsuspecting victims to download their new “unheard of” applications. They promise users the moon, and only ask in return that users install a basic free application. Case in point, our sensors picked up yet another deceptive ad campaign that entices users into installing privacy violating applications, most commonly known as PUAs or Potentially Unwanted Applications.
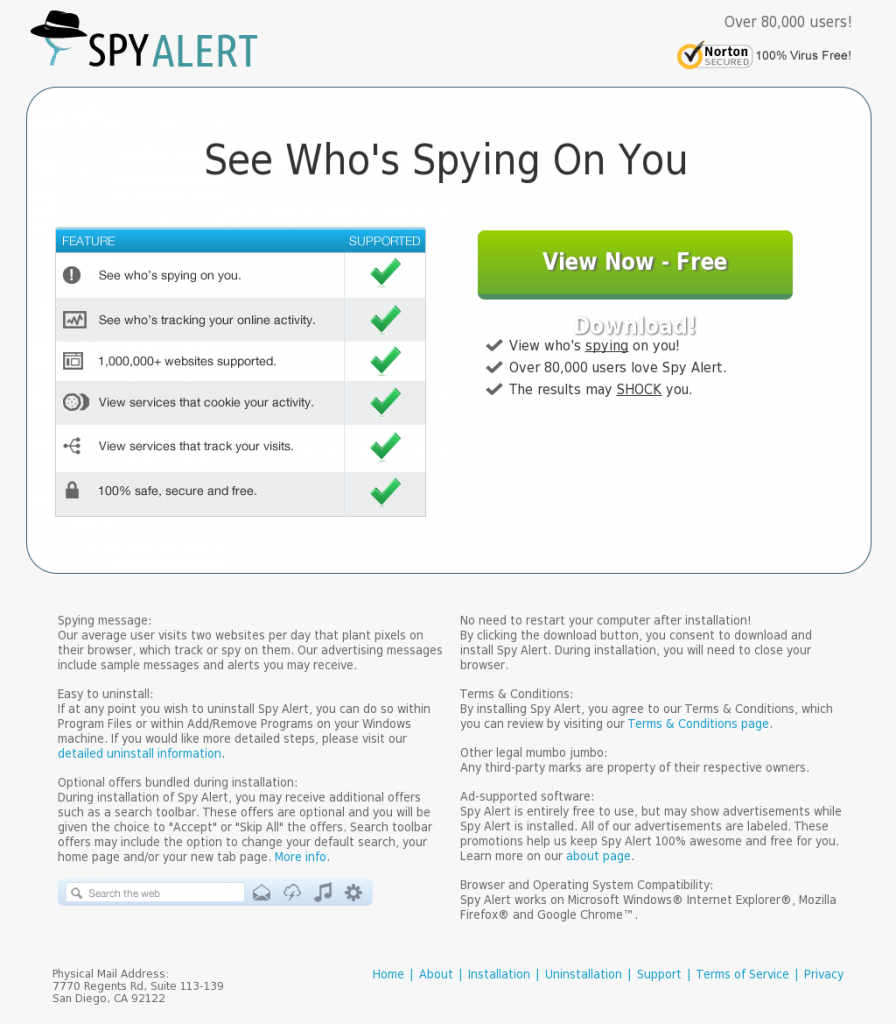
Sample screenshots of the landing page:
Landing URL: spyalertapp.com
Detection rate for the SpyAlertApp PUA: MD5: 183cf05e8846a18dab9850ce696c3bf3 – detected by 4 out of 47 antivirus scanners as Win32/ExFriendAlert.B; SearchDonkey (fs)
Once executed, it phones back to 66.135.34.182 and 66.135.34.181
The following PUA domains are also known to have responded to the same IPs:
l.cloud-canvas.com
l.getsecureweb.com
l.hitthelightsapp.com
l.infoseekerapp.com
l.moviemodeapp.com
l.provideodownloader.com
l.recordcheckerapp.com
l.searchdonkeyapp.com
l.spyalertapp.com
l.spyguardapp.com
l.spylookoutapp.com
l.tubedimmerapp.com
l.unfriendapp.com
l.webshieldonline.com
The following PUA MD5s are known to have phoned back to these IPs:
MD5: 5a4202e570997e6740169baac0d231cb
MD5: d461ced9efbba91fc9f672b4283ec9ce
MD5: 739974dc2cba93e265b8a4e3015f389d
MD5: a2abbbafbc74c0ee26b2d7cc57050033
MD5: 0c4b84ef70ea55fbadcd20c85e5df888
MD5: 1821d0ff30a9840db1a1be3133cee77f
MD5: 71a8639f45706cc034c37e39443774da
MD5: 9f08e58f38744753921090ee28eb3277
MD5: 8e2a368e139e81ae779e39304d03fb79
MD5: 2a65db19303587722aad675485f33ab4
MD5: 5a7751c7fb62bed7fafebbae36b29d8f
MD5: b1598ddaa466ae8c5ed7727fe8bf9bba
MD5: b960fcc346da8a64d969932fe993ed76
MD5: 32c0863bcb2543a55436ecd5bc1df462
MD5: 0f358896ee2bf4507a07ff971b7bc749
MD5: 82aad768bf3609f700947c689f024d9a
MD5: 2f1101cc2c834b4e404389fb14b43fd2
MD5: 0e76ffda3480511dbc9dda95b18d1c1b
MD5: ed6d97129f713a174d60eb10d5db0992
MD5: 126cf0cfe5f1da0106dfff9ce9cb7041
MD5: 84d31aaf279c57a0d2886639d7468ec5
MD5: 6b4e76e4655592d06828e0a932f260d5
MD5: e86c7ae3bae035e9cdd2a71db1c0fbea
Want to known who’s tracking your online activities? We advise you to give Mozilla’s Lightbeam, a try.
Webroot SecureAnywhere users are proactively protected from these PUAs.