Palo Alto Networks recently discovered ransomware hidden inside of the torrenting app ‘Transmission’. While this may come as a shock to those that still believe the Mac is a fortress that can’t be broken, the rest of us are not shocked at all. In fact, a few months back I wrote a blog warning Mac users not to dismiss Mac malware. It is time to take Mac security seriously. Apple does a great job for the most part, but in order to secure your information and your devices, you need a good Antivirus product.
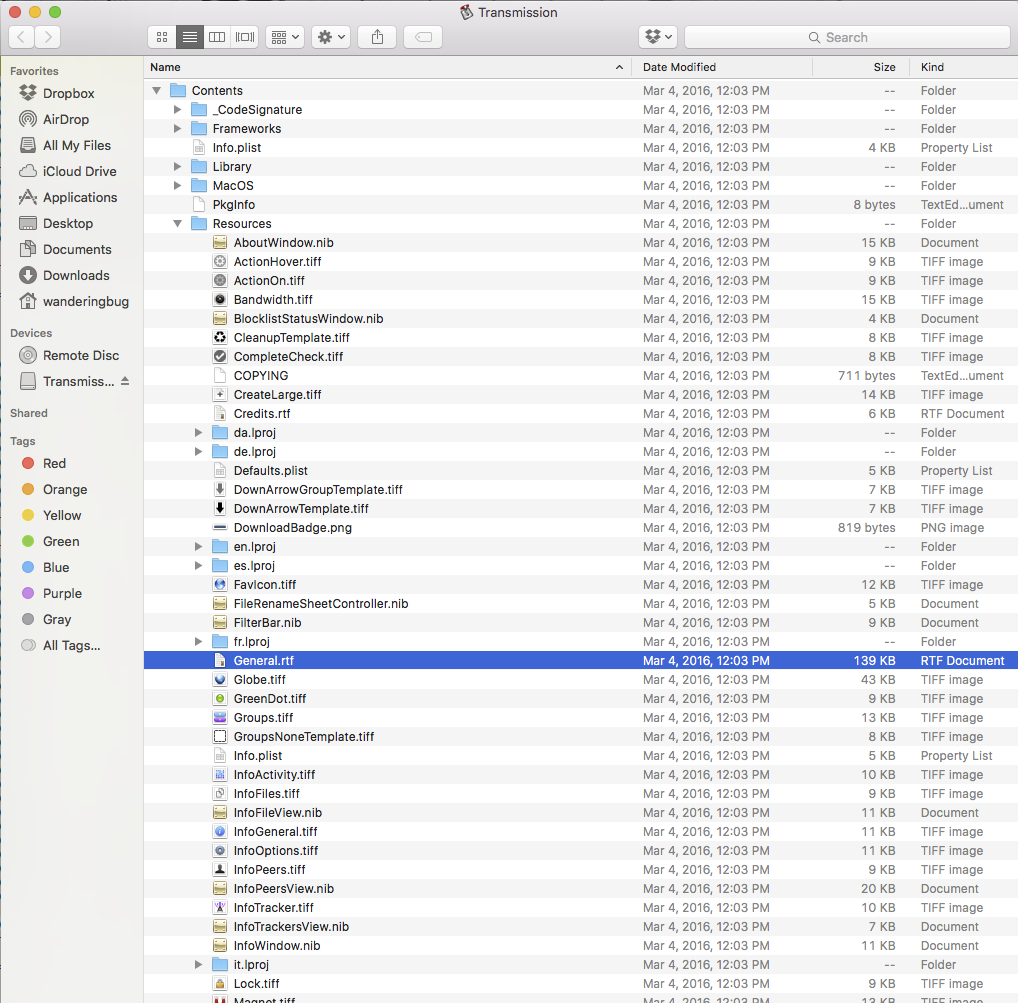
Back to the threat at hand. This ransomware is bundled in with the Transmission Bittorrent client as a file called “General.rtf”. For most, this file looks like a simple real text file. However, it is actually a Mach-O 64-bit executable file that will execute three days after you run Transmission. This helps keep the ransomware hidden so that users wouldn’t suspect the app they are using for torrenting, but rather the torrents that they are pulling down as the source of infection.
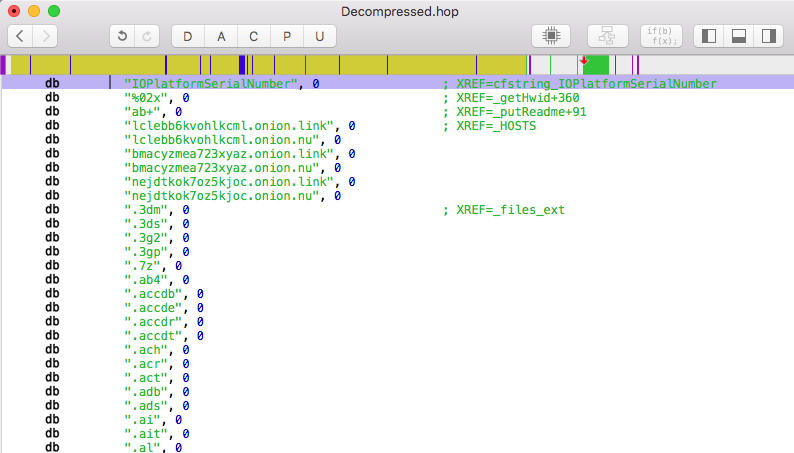
After the three days, the app executes and drops a file called “kernel_service” into the user’s library directory. This process is named in such a way so as to confuse anyone that looks in Activity Monitor into believing that it is a system process. It then drops three more files in the user’s library: “.kernel_pid”, “.kernel_time” and “.kernel_complete”. It will collect the infected Mac’s model name and UUID then upload the information to one of its Command and Control servers.
These servers will respond with a file named “README_FOR_DECRYPT.txt”, in which it explains how to get the key for decryption and the price for the key in bitcoins. The ransomware is able encrypt around 300 different types of file extensions that it finds in the “/Users/” directory and changes the file extension to end in “.encrypted”. This means that the family pictures that you keep on your Mac will now be labeled “GrandCanyon2010.jpg.encrypted” and cannot be opened.
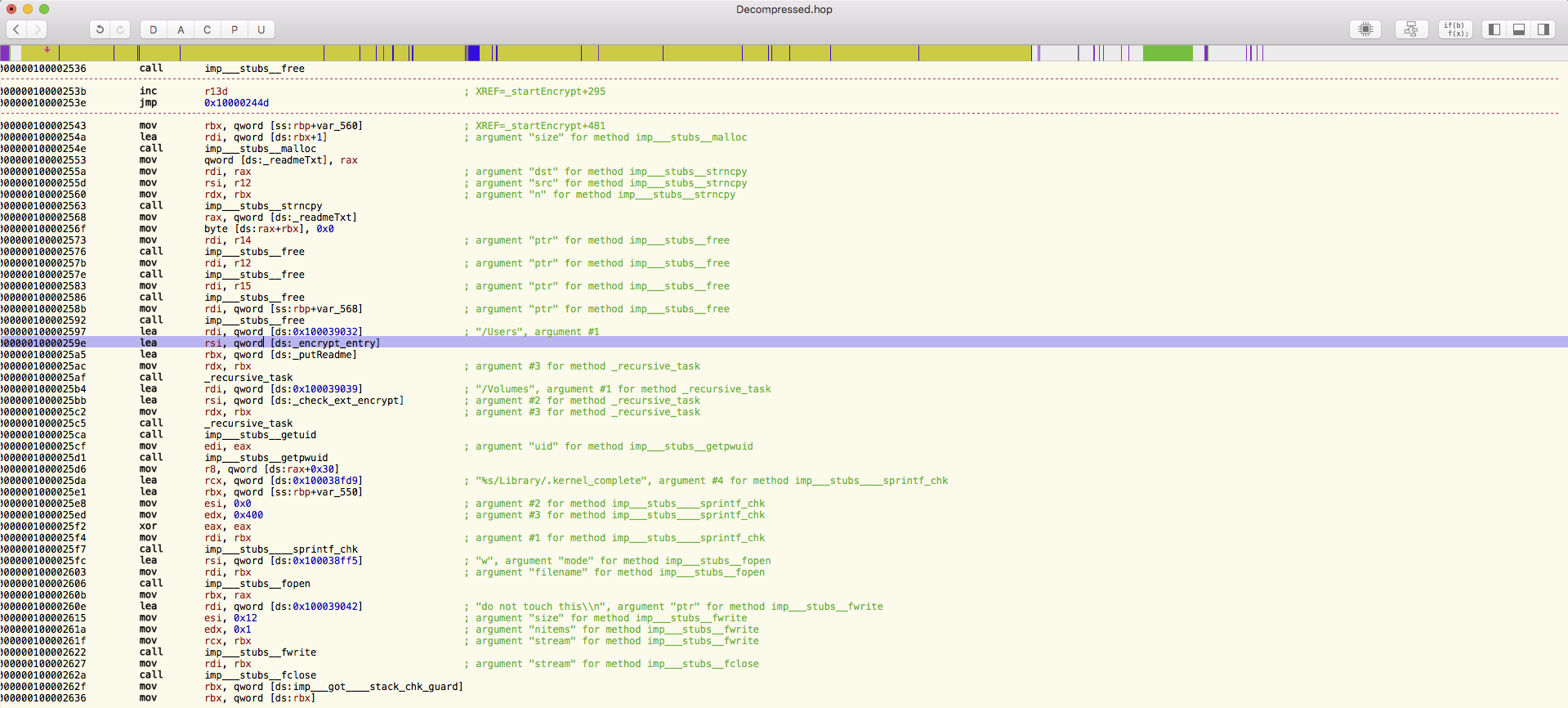
One of the most important things to note is that the program is still a work in progress. There are many functions that have been found in the code that are not currently being used, like the ability to encrypt your Time Machine backup as well. This of course is the second wall of defense for many people, who believe that because they have a Time Machine backup, they can always just roll back their Mac if something happens.
To add some more context into the expansion of ransomware into the Mac OS, our David Kennerley recently commented in Global Security Mag:
“Given the potential gains for attackers, it’s no surprise that they are now diversifying and targeting OS X – a popular system with a large target base. Add to this the fact that many people believe they are safe from such malware when running OS X, this ransomware has the potential to impact a huge number of people.”
You can locate the full article here.
I’ve said it before and I will say it again: Mac malware is real. Don’t be an Apple user that finds this out the hard way.







New mac usr. Comp less than a year old, I put Web root on when I bought it and have been battling an attack for over a month now.
So… the Webroot I have now will not protect me from this? And is this something I can avoid by simply not opening suspicious emails?
Yes, the program will. However, new variants can emerge! Our team will constantly be watching emerging threats to ensure you stay protected.
Jerry,
Yes, we will offer protection from this. Usually we have already set rules in place for something such as this before a blog article is posted about it. Don’t hesitate to let us know if you need anything!
After reading this article I can see why Apple had such an extensive update to El Captain OS X today. You are always one step ahead of everything and I remember back when I first got my iMac the Apple techs told me to take your software off of my computer. I said no to that and you have an excellent product. I have not heard any of their Apple techs say lately to take an anti-virus software off. Nothing much is safe and secure these days but trying to stay ahead of inventive cybercriminals is great. Keep on helping your customers like me stay as safe as possible.
I was recently informed that my Webroot which is the only security I have had on my computer from day one, is no longer able to protect my computer. This was a message from the place I was purchasing it from. After I checked further with others, I was told Webroot is having an “issue” concerning this and is working on taking care of the problem. Soooo for the time being, is it protecting my computer each day when it automatically scans it as it always had done? Just wondering if anyone knows what is going on with Webroot. Thanks.