By Dancho Danchev
Kindle users, watch what you click on!
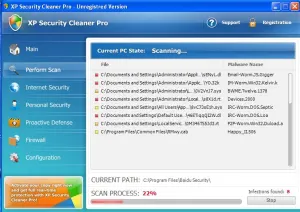
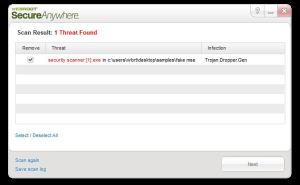
Cybercriminals are currently mass mailing tens of thousands of fake Amazon “You Kindle E-Book Order” themed emails in an attempt to trick Kindle users into clicking on the malicious links found in these messages. Once they do so, they’ll be automatically exposed to the client-side exploits served by the Black Hole Exploit Kit, ultimately joining the botnet operated by the cybercriminal/cybercriminals that launched the campaign.
More details: