by Blog Staff | Jun 28, 2013 | Industry Intel, Threat Lab
On their way to acquire the latest and coolest Android game or application, end users with outdated situational awareness on the latest threats facing them often not only undermine the confidentiality and integrity of their devices, but also, can unknowingly expose critical business data to the cybercriminals who managed to infect their devices.
How are cybercriminals achieving this in times when Google is automatically scanning all submissions to the Google Play store, and is also verifying the applications to prevent the abuse of potential installations from untrusted third-party stores/application download locations?
Easier than you to think, especially with the recent commercial availability of a DIY Android application decompiler/injector developed to work exclusively with a publicly obtainable Android-based trojan horse.
More details:
(more…)

by Blog Staff | Jun 27, 2013 | Industry Intel, Threat Lab
Like every ecosystem, the cybercrime ecosystem has its own set of market disrupting forces whose applicability and relevance truly shape the big picture at the end of the day. For years, cybercriminals have been porting, localizing (MPack/IcePack, FirePack) and further contributing to the the development of malware/crimeware/Web malware exploitation kits, either through direct cooperation with the original author of a particular release, or on the basis of leaked or commercially available source code.
With more high profile malware source code leaks continuing to take place, more cybercrime-friendly coders now have access to sophisticated antivirus detection bypassing techniques. Access to these techniques will definitely spark the introduction of “new” features within the coders’ own set of underground market releases in an attempt to catch up with the market leading competition.
Two weeks ago, we began monitoring a cybercrime ecosystem advertisement offering access to self-propagating ZeuS-based source code. It sparked several important questions in the overall context of today’s underground market – is coding custom malware for hire still a relevant monetization tactic? Do low/high profile leaks of malware source code actually allow virtually anyone with less sophisticated coding capabilities to re-purpose, brand and start selling their own malware? Or is the underground system still largely dominated by vendors ‘pushing’ their product/service strategies to meet the demand for these kinds of assets?
Let’s find out.
(more…)

by Tyler Moffitt | Jun 27, 2013 | Industry Intel, Threat Lab
By Tyler Moffitt
We see users on the internet getting infected with Rogue Security Malware all the time. In fact, it’s one of the most common and obvious type of infections we see. The Rogues lock-down your computer and prevent you from opening any applications so you’re forced to read their scam. Although they use various tactics and convincing GUIs to get onto your computer, they all share a common goal: To get your money. (more…)

by Blog Staff | Jun 26, 2013 | Industry Intel, Threat Lab
Following last week’s profile of yet another InstallCore Potentially Unwanted Application (PUA) campaign, we detected another rogue ad campaign this week. This time enticing E.U based users into downloading and installing a fake “Free Codec Pack”, with the users sacrificing their privacy in the process due to the additional toolbars that will be installed on their PCs.
More details:
(more…)

by Blog Staff | Jun 25, 2013 | Industry Intel, Threat Lab

The workplace technology landscape has changed dramatically over the past five years, and the security threats have changes along with it. Here are the growing factors that IT professionals can’t afford to ignore, all in a beautiful infographic. (more…)

by Blog Staff | Jun 25, 2013 | Industry Intel, Threat Lab
One of the most common myths regarding the emerging TDoS (Telephony Denial of Service) market segment, portrays a RBN (Russian Business Network) type of bulletproof infrastructure used to launch these attacks. The infrastructure’s speculated resilience is supposed to be acting as a foundation for the increase of TDoS services and products. Fact or fiction? Keep reading.
In this post, we’ll profile a SIP-based, API-supporting fake caller ID/SMS number supporting DIY service, and discuss its relevance in the overall increase in TDoS underground market propositions.
More details:
(more…)

by Blog Staff | Jun 24, 2013 | Industry Intel, Threat Lab
Our sensors continue detecting rogue ads that expose users to bogus propositions in an attempt to install privacy-invading Potentially Unwanted Applications (PUAs) on their PCs. The most recent campaign consists of a successful brand-jacking abuse of Mozilla’s Firefox browser, supposedly offered for free, while in reality, the rogue download manager entices users into installing multiple rogue toolbars, most commonly known as InstallCore.
More details:
(more…)

by Tyler Moffitt | Jun 21, 2013 | Threat Lab
By Tyler Moffitt
We’ve seen quite a few audio ads infecting users recently. We think it’s a good idea to go over an in-depth look at how they infect your computer and how to remediation them.
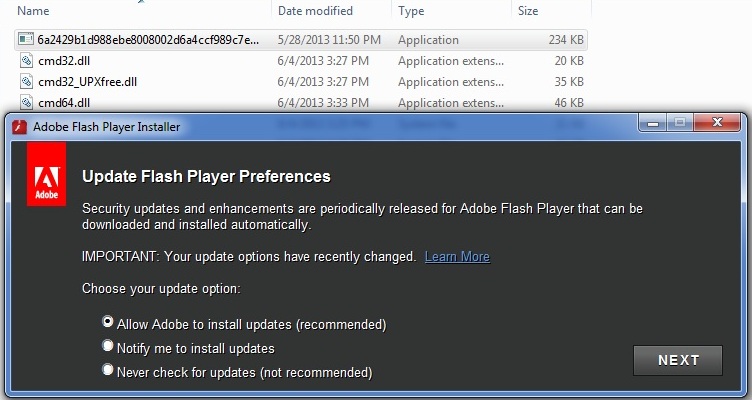
As you can see in this first picture, this is another Adobe Flash spoof that launches its signature update window.
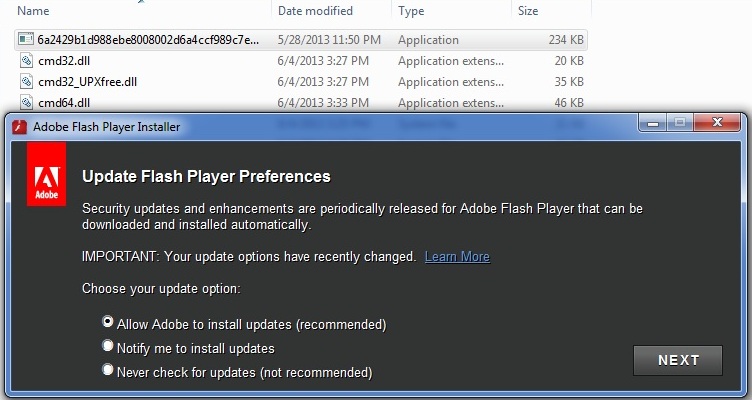
You might not be able to see, but the “f” is a little off on the tiny icon at the top left. Either way it looks quite legitimate. It doesn’t matter what option you check; once you click “NEXT” you’ll get this next window.
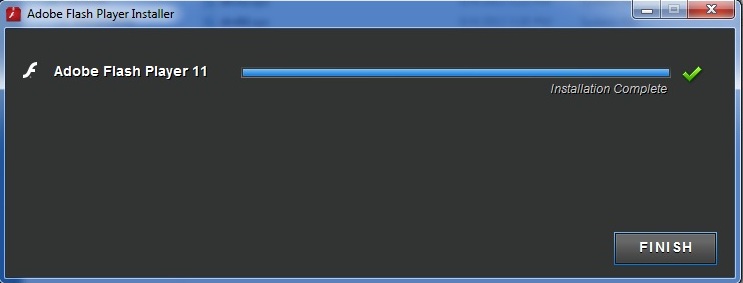
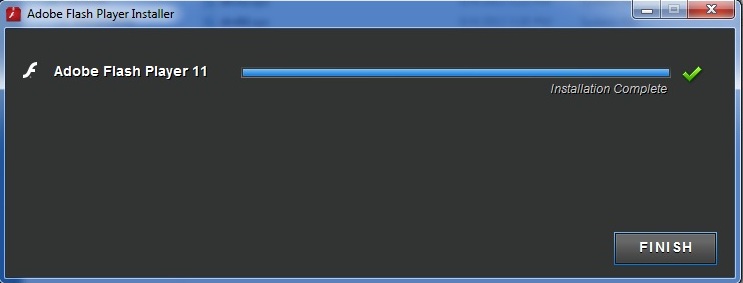
So far this seems completely official and harmless. It even takes it’s time progressing the loading bar. However, once you click “Finish” everything closes down and the computer reboots. The command force quits all applications so you won’t have time to save anything or cancel the shutdown. Once the computer reboots there is no final closing message from “Adobe”, but everything seems normal for a few minutes. After about three to five minutes the computer slows down to a crawl and Audio ads start playing in the background. By now users start to worry about foul play with their computer so here’s a look at what’s going on at this point.
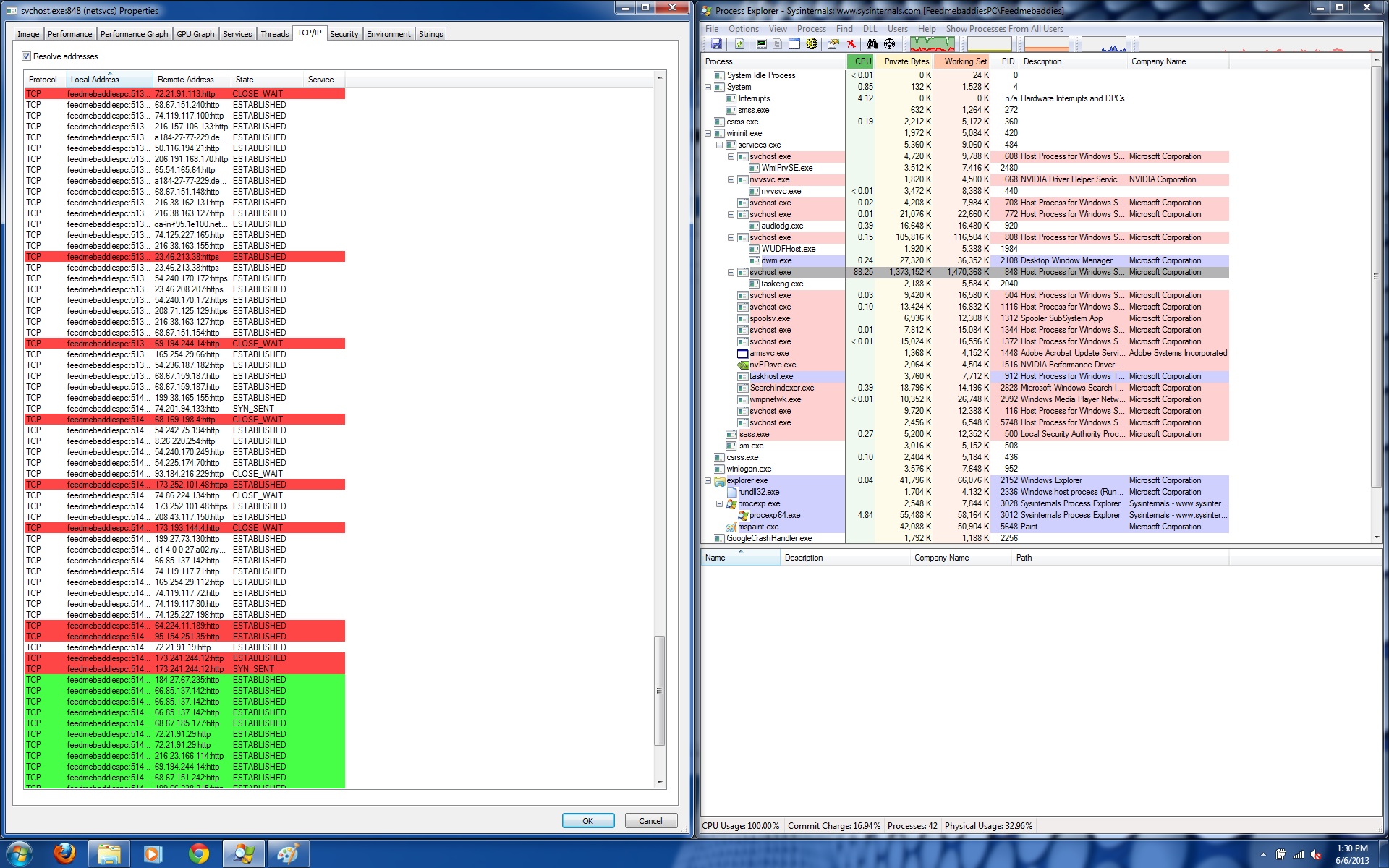
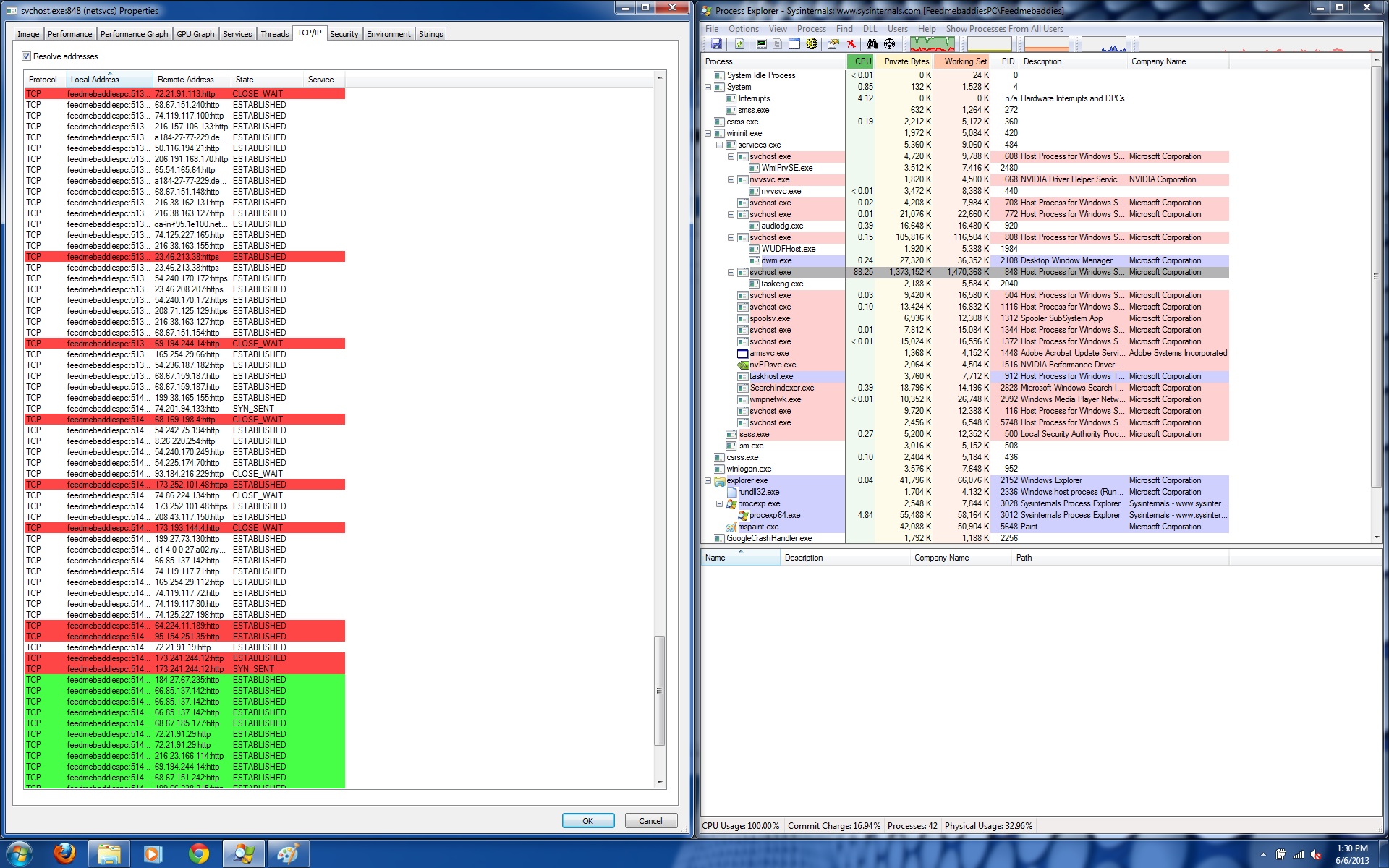
The audio streams are not being run by an audio application or an internet browser session, but instead a hijacked “svchost.exe” that’s using 88.25% CPU. If we take a look at its network communication we find that it’s establishing and closing over a hundred different connections at once. This is why the audio ads aren’t coherent and are basically just multiple advertisement streams all at once which makes for quite an annoying sound. You can give it a listen by clicking below.
[soundcloud url=”http://api.soundcloud.com/playlists/6977174″ params=”” width=” 100%” height=”300″ iframe=”true” /]
The motivation is for this virus, other than being very obnoxious, is that the hundreds of IP addresses being resolved from the PC will generate a tick on the visit counter and generate ad revenue.
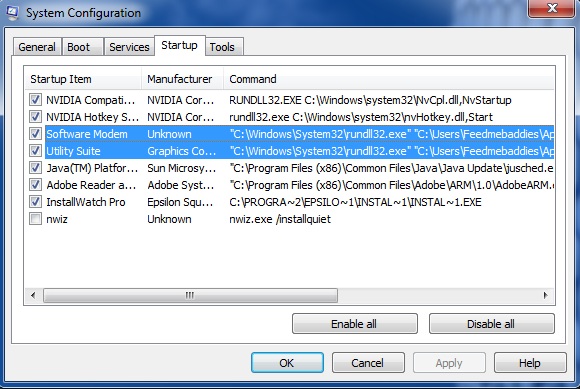
To remove this sample is actually quite simple. Since this starts as soon as the computer starts if you take a look at the startup entries you should find something similar to this.
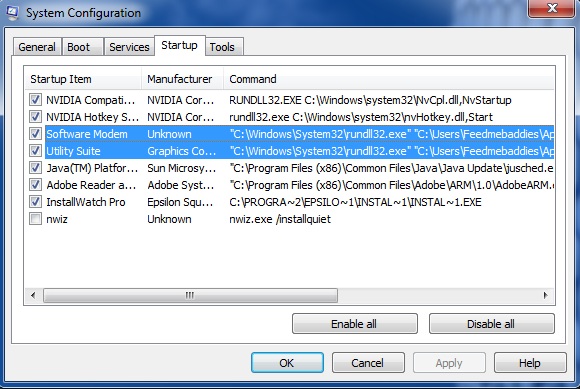
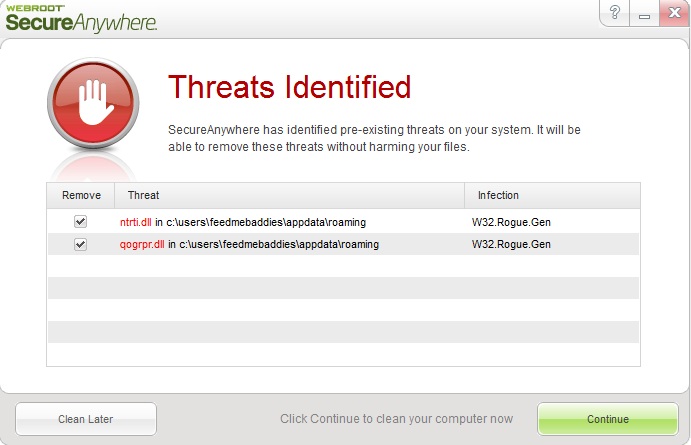
Software Modem and Utility Suite are the culprit. If you read the full command they are located in appdata and point to two randomly named DLLs called “qogrpr.dll” and “ntrti.dll” This is extremely suspicious.
All you need to do is delete the files in appdata and then remove the run keys from startup. The full registry key and directory location from are below.
[HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun]
“qogrpr”=””C:\Windows\System32\rundll32.exe” “C:\Users\”youruserfolder”\AppData\Roaming\qogrpr.dll”,GetGlobals”
“ntrti”=””C:\Windows\System32\rundll32.exe” “C:\Users\”youruserfolder”\AppData\Roaming\ntrti.dll”,NewMember”
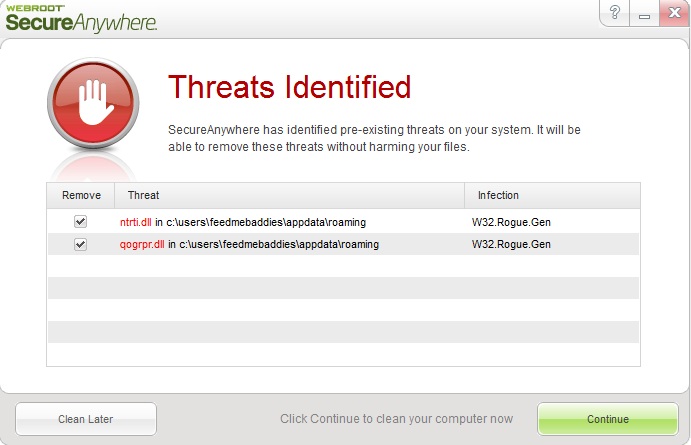
As always, you can install Webroot SecureAnywhere and we’ll remove it with ease.
That’s it for this variant of the Audio ads. There are also other variants that use rootkits to infect the MBR. Please contact Webroot Support if additional assistance is needed in remediating this infection.

by Blog Staff | Jun 21, 2013 | Industry Intel, Threat Lab
A recently released subscription-based SHA256/Scrypt supporting stealth DIY Bitcoin mining tool is poised to empower cybercriminals with advanced Bitcoin mining capabilities to be used on the malware-infected hosts that they have direct access to, or have purchased through a boutique cybercrime-friendly E-shop selling access to hacked PCs.
Let’s take a peek at the DIY Bitcoin mining tool, and discuss some of its core features.
(more…)

by Blog Staff | Jun 20, 2013 | Industry Intel, Threat Lab
Thanks to the buzz generated over the widespread adoption of the decentralized P2P based E-currency, Bitcoin, we continue to observe an overall increase in international underground market propositions that accept it as means for fellow cybercriminals to pay for the goods/services that they want to acquire.
In this post, I’ll profile yet another recently launched E-shop selling access to thousands of malware-infected hosts, which compared to the previous E-shops that we’ve profiled, is directly promoting the use of ransomware, click fraud facilitating bots and bitcoin mining tools on the malware-infected hosts purchased through the service.
More details:
(more…)