The general availability of DIY malware generating tools continues to contribute to the growth of the ‘malware-infected hosts as anonymization stepping stones‘ Socks4/Socks5/HTTP type of services, with new market entrants entering this largely commoditized market segment on a daily basis. Thanks to the virtually non-attributable campaigns that could be launched through the use of malware-infected hosts, the cybercrime underground continues to seek innovative and efficient ways to integrate the inventories of these services within the market leading fraudulent/malicious campaigns managing/launching tools and platforms.
Let’s take a peek at one of the most recently launched services offering automatic access to hundreds of malware-infected hosts to be used as anonymization stepping stones.
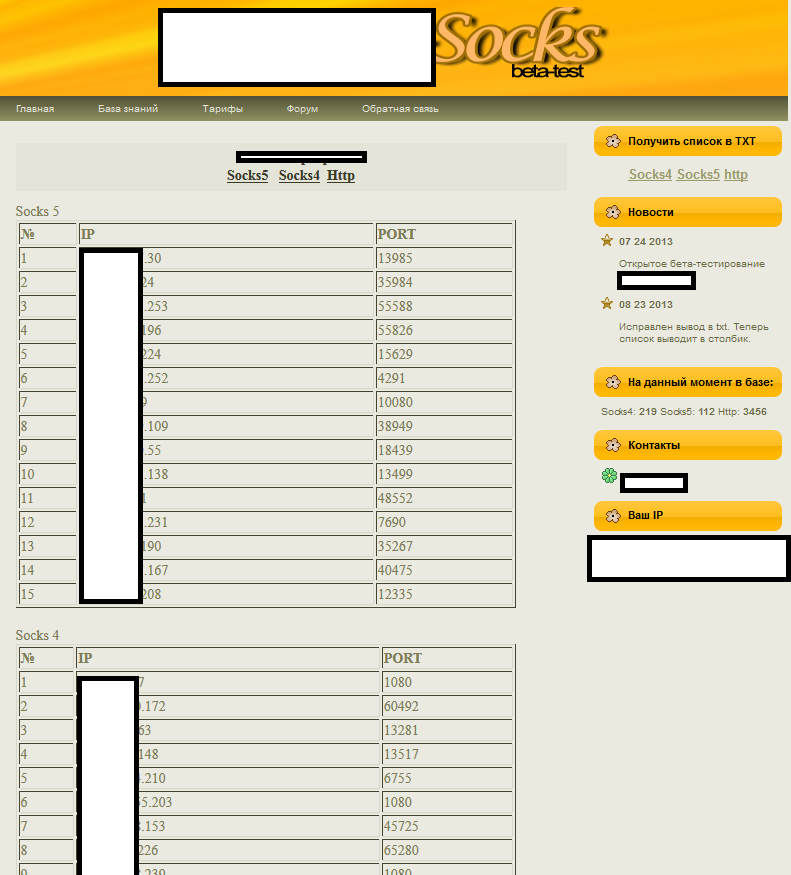
Sample screenshot of the “malware-infected hosts as anonymization stepping stones” service:
One of the main differentiation factors for this type of services is whether or not they’d continue re-supplying new customers with access to the same set of available compromised and converted to Socks4/Socks5/HTTP servers, or offer exclusively access to a specific set of servers, on a per customer basis only. The lack of QA (Quality Assurance) in this particular service is prone to lower the quality of the campaigns launched using these servers as multiple cybercriminals will now have access to the same pool of compromised hosts, which will inevitably increase the probability that they will be quickly labeled as IPs with extremely bad reputation.
Catch up with this previous research on the topic of “Anonymizing a cybercriminal’s Internet activities”:
Naturally, there are vendors whose sole objective is to ‘innovate’, in this particular case, reboot the life cycle of a popular anonymization concept known as ‘proxy-chaining’, that is, the process of simultaneously connecting through multiple compromised hosts in an attempt to decrease the chances for a successful identification for a particular attack. Due to the persistent demand for Socks4/Socks5/HTTP based compromised hosts, we expect to continue observing a steady supply of new hosts, with the vendors differentiating their propositions, naturally trying to occupying a market leading share of this in-demand market segment.