WhatsApp users, watch what you click on! A currently circulating fraudulent spam campaign is brand-jacking WhatsApp in an attempt to trick its users into clicking on links found in the email. Once socially engineered users fall victim to the scam, they’re automatically exposed to a fraudulent pharmaceutical site, offering them pseudo bargain deals. Let’s assess the fraudulent campaign, and expose the fraudulent infrastructure supporting it.
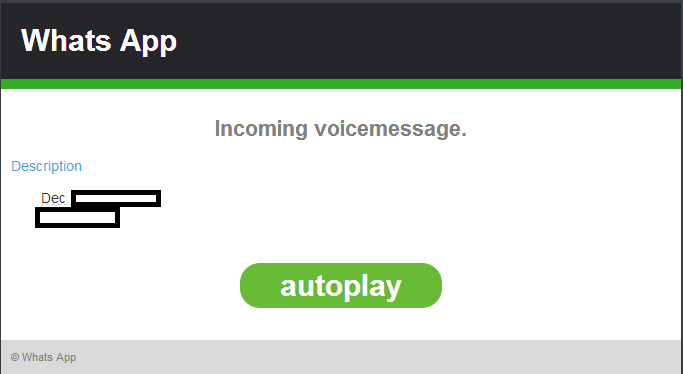
Sample screenshot of the spamvertised email:
Sample screenshot of the landing pharmaceutical scam page:
Redirection chain: hxxp://203.78.110.20/horizontally.html -> hxxp://viagraphysician.com (109.201.133.58)
We’re also aware of the following fraudulent domains that are known to have phoned back to the same IP (109.201.133.58):
67157d.pharmahimoft.pl
albertacanadatab.in
asaletabla.at
baruchelmedicine.in
bioportfoliotablet.com
biotechviagrahealthcare.com
buygenericspills.com
canadascanadarx.com
canadatab.in
canadaviagras.com
canadawelnesstoronto.com
carehealthtabletspills.ru
careteachers.com
cialismed.com
cialispharmdrone.com
contabdiet.com
dietpharmediterranean.com
dietviagraweight.com
docherbal.in
drugrxmedicine.be
Name servers:
ns1.viagraphysician.com – 178.88.64.149
ns2.viagraphysician.com – 200.185.230.32
The following fraudulent name servers are also known to have participated in the campaign’s infrastructure at 178.88.64.149:
ns1.wpdsasya.com
ns1.bioportfoliohealthcaretab.com
ns1.viagraphysician.com
ns1.androidherbaltablet.com
ns1.viagracialalec.in
ns2.viagracialalec.in
ns1.kgvghatm.eu
ns2.kgvghatm.eu
ns1.zwsxfwqn.eu
ns1.worgad.ru
ns1.iald.ru
ns2.iald.ru
ns1.fivere.ru
ns1.gabrue.ru
ns1.nagh.ru
ns1.lonoci.ru
ns1.menono.ru
ns1.xior.ru
ns1.uptras.ru
ns2.uptras.ru
ns1.qatt.ru
ns1.aprpharmacyrx.ru
ns2.aprpharmacyrx.ru
ns1.swoltz.ru
The following fraudulent name servers are also known to have participated in the campaign’s infrastructure at 200.185.230.32:
ns2.medicarepillmedicaid.com
ns1.tabdietmediterranean.com
ns2.viagraphysician.com
ns2.pharmacylevitrapharmacist.com
ns2.viagracialalec.in
ns2.kgvghatm.eu
ns1.zwsxfwqn.eu
ns2.worgad.ru
ns2.fivere.ru
ns1.gabrue.ru
ns2.nagh.ru
ns1.tabletsmedshealth.ru
ns2.menono.ru
ns2.xior.ru
ns2.uptras.ru
ns2.swoltz.ru
We expect that more legitimate brands will continue getting targeted in such a way, with the fraudsters behind the campaign continuing to earn revenue through pharmaceutical affiliate programs.
Webroot SecureAnywhere users are protected from these scams.








I accidentally clicked on this and now it is sending lots of emails from my email address to my contacts, I have changed my password is there anything I can do?
StephenJames2 me too its really annoying:S how do i get it to stop
This alert does NOT mention hijacking contacts, the 2 previous posters must have contracted a different virus etc.
This one is doing the rounds again – I had one today but do not hve Whatsapp enabled.
Beware everyone