Data Privacy Week (Jan. 27-31) is an excellent opportunity to reflect on the importance of protecting one of your most valuable assets: your personal information. Whether you’re browsing online as a consumer or running a business, data privacy is paramount in an environment where cyber threats can lurk around every corner.
In the spirit of Data Privacy Week, here are six ideas to help you protect yourself—and your data:
1. Understand your level of risk
Get acquainted with the phrase personally identifiable information. This includes any data that can be used to identify you, and it ranges from your name and address to more sensitive information like health and financial records. Here are some common examples:
- Health data: Information stored in a patient portal, online pharmacy, or health insurance website.
- Financial data: Details of your bank account, 401K fund, or IRA.
- Apps: Data collected by various applications you use. This information can range from your current location to previous purchasing habits.
- Social media: Information you share on platforms like Facebook, Twitter, and Instagram.
Knowing what kinds of personal data you have out there is the first step toward protecting it.
2. Learn the basics of data privacy self-defense
Protecting your data doesn’t have to be complicated. Here are some basic steps you can take to safeguard your privacy:
- Create secure passwords: Use a combination of letters, numbers, and special characters.
- Use multifactor identification: Add an extra layer of security to your accounts by using a password combined with a code sent to their phone or a fingerprint.
- Limit the number of cookies you accept: Be selective about which websites can track your activity.
- Beware of public Wi-Fi: Avoid accessing sensitive information on unsecured networks.
- Use a virtual private network, or VPN: Encrypt your internet connection to protect your data.
- Keep software up to date: Regular updates can protect you from security vulnerabilities.
3. Update your privacy settings
Take some time to review the privacy settings on the apps, devices, or websites you use most often. You might be surprised at what you find. The nonprofit National Cybersecurity Alliance has compiled a comprehensive list of popular sites’ privacy pages to get you started.
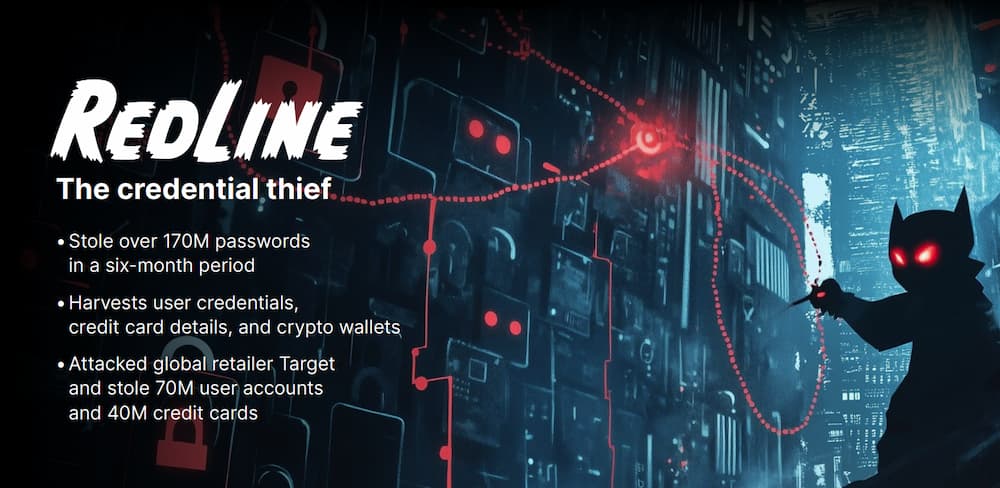
4. Arm yourself with antivirus protection
An effective antivirus program is essential for protecting your devices from malware and other threats. Look for features such as real-time scanning, automatic updates, and comprehensive protection against various types of malware. A product like Webroot offers a variety of antivirus solutions to keep your data safe. Webroot even offers a product selection tool that can help you find a solution tailored to your unique needs.
5. Find an encrypted data backup product
Backing up your data is crucial, but it’s equally important to ensure that those backups are secure. An encrypted data backup solution like Carbonite can protect your data from unauthorized access. Carbonite’s secure, always-on backup ensures that you won’t lose important, irreplaceable files due to accidental deletion or device malfunction.
6. Take in a movie
After all that hard work learning about data privacy, it’s time to reward yourself by doing something fun. Hop on the couch and watch a movie that delves into the topic. Here are some suggestions from the nonprofit group Educause:
- Terms and Conditions May Apply
- Citizen Four
- Code 2600
- Gattaca
- Minority Report
- 1984
- The Lives of Others